Advanced URL Filtering
Set Up Credential Phishing Prevention (Strata Cloud Manager)
Table of Contents
Set Up Credential Phishing Prevention (Strata Cloud Manager)
Follow these steps to configure credential phishing prevention for Cloud Managed Prisma
Access.
If you’re using Panorama to manage Prisma Access:
Toggle over to the PAN-OS & Panorama tab and follow the guidance there.
If you’re using Strata Cloud Manager, continue here.
- Configure the user credential detection method you want to use.Review Methods to Check for Corporate Credential Submissions for details about each method.
- For IP User Mapping, set up local users and groups, Identity Redistribution, or Authentication with Prisma Access.
- To use Domain Credential Filter, set up Identity Redistribution and local users and groups or Authentication.
- To use Group Mapping, set up local users and groups or Authentication.
- Create a Decryption policy rule that decrypts the traffic you want to monitor for user credential submissions.
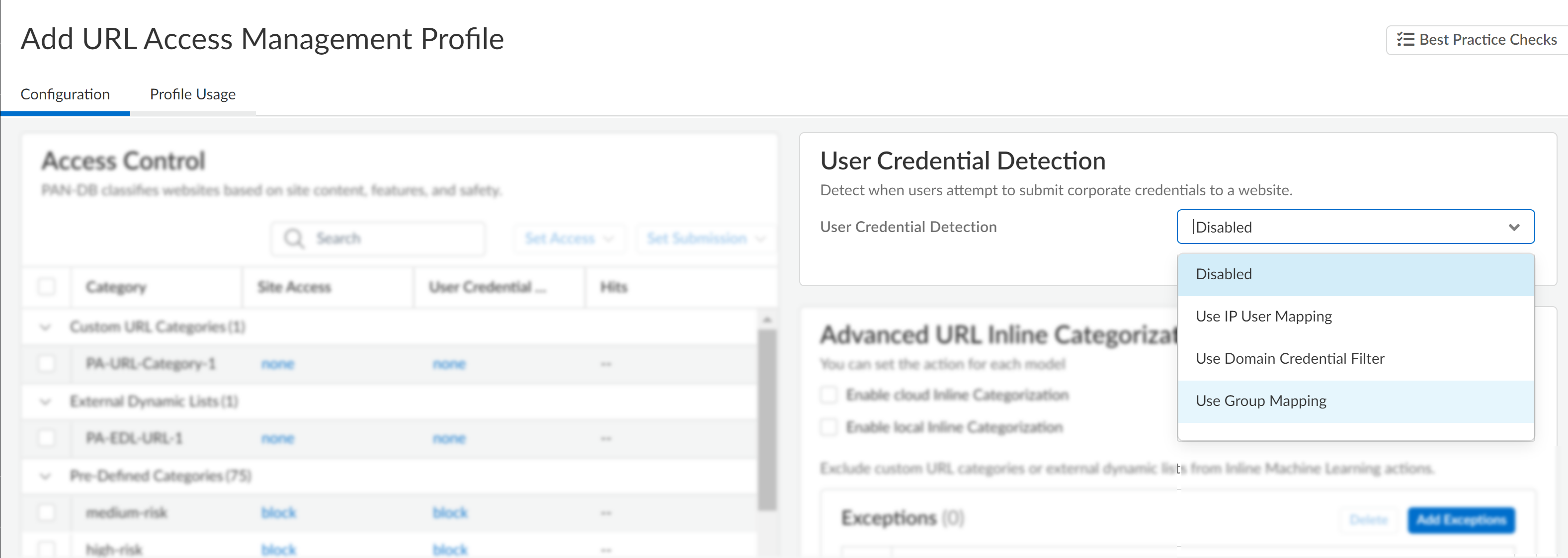
- Create or modify a URL Access Management Profile.
- Select ManageConfigurationNGFW and Prisma AccessSecurity ServicesURL Access Management.
- Under URL Access Management Profiles, click Add Profile or select an existing profile.
- Configure the User Credential Detection settings.
- Under User Credential Detection, select a User Credential
Detection method.
- Use IP User Mapping—Checks for valid corporate username submissions and verifies that the login username maps to the source IP address of the session. To do this, Prisma Access matches the submitted username and source IP address of the session against its IP-address-to-username mapping table.
- Use Domain Credential Filter—Checks for valid corporate username and password submissions and verifies that the username maps to the IP address of the logged-in user.
- Use Group Mapping—Checks for valid
username submissions based on the user-to-group mapping table
populated when you map users to groups. You can apply credential
detection to any part of the directory or for specific groups
that have access to your most sensitive applications, such as
IT.This method is prone to false positives in environments that do not have uniquely structured usernames. Because of this, you should only use this method to protect your high-value user accounts.
![]()
- For Valid Username Detected Log Severity, select
the severity level that the firewall records in log when it detects
corporate credential submissions:
- high
- (default) medium
- low
- Under User Credential Detection, select a User Credential
Detection method.
- Configure the action taken when the firewall detects corporate credential
submissions.
- Under Access Control, select an action for User Credential
Submission for each URL category with its
Site Access set to allow or alert.You can select from the following actions:
- (Recommended) alert—Lets users submit credentials to websites in the given URL category but generates a URL Filtering log each time this happens.
- (Default) allow–Lets users submit credentials to the website.
- (Recommended) block—Prevents users from submitting credentials to websites in the given URL category. When a user tries to submit credentials, the firewall displays the anti-phishing block page.
- continue—Presents the anti-phishing continue page to users when they attempt to submit credentials. Users must select Continue on the response page to proceed to the website.
- Save the profile.
- Under Access Control, select an action for User Credential
Submission for each URL category with its
Site Access set to allow or alert.
- Apply the URL Access Management profile to your Security policy rules.
- Select ManageConfigurationNGFW and Prisma AccessSecurity ServicesSecurity Policy.
- Under Security Policy Rules, create or select a Security policy rule.
- Select ActionsProfile Group, and then select a URL Access Management profile group.
- Save the rule.
- Click Push Config.