Cloud NGFW for AWS
Cloud NGFW Integration with AWS Cloud WAN
Table of Contents
Expand All
|
Collapse All
Cloud NGFW for AWS Docs
Cloud NGFW Integration with AWS Cloud WAN
Integrate Cloud NGFW with AWS Cloud WAN.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
AWS Cloud WAN is a managed wide area networking (WAN) service that enables you
to build a unified network that interconnects cloud and on-premises environments. It
provides a centralized dashboard to connect on-premises, branch offices, data centers,
and Amazon Virtual Private Clouds (VPCs) across the AWS global network and even other
cloud providers.
Cloud WAN helps with connectivity within AWS through the AWS Network Manager, an
interface which centrally manages your global network. A global network is a single
private network that acts as the root-level container for your network objects and can
contain both transit gateways and a core network. The core network consists of network
policies, attachments such as VPCs, and transit gateway route tables.
You can map these VPCs to segments in the core network. These segments are connected
using attachments such as VPC attachment or transit gateway route table attachments. The
built-in segmentation helps you to
maintain network isolation across AWS and on-premises environments. Each segment creates
a dedicated routing domain. You can create multiple network segments within your global
network. Cloud WAN restricts AWS resources to communicate within the segment. In
nutshell, Cloud WAN allows you to route traffic between:
- VPCs in the same segment and in the same region (isolated attachments).
- VPCs in different segments of the same region.
- VPCs in the same segment across different regions (isolated attachments).
- VPCs in different segments across different regions.
Considerations before deploying the AWS Cloud WAN:
- Peering between transit gateways and Cloud WAN is supported in the same region, and not across regions.
- For use cases that require AWS site-to-site VPN connections over Direct Connect using private IP addresses, ensure that you connect Cloud WAN with a transit gateway.
- While deploying Cloud WAN along with transit gateways, ensure that the transit gateway ASN is different from the ASN used for Cloud WAN’s core network edges.
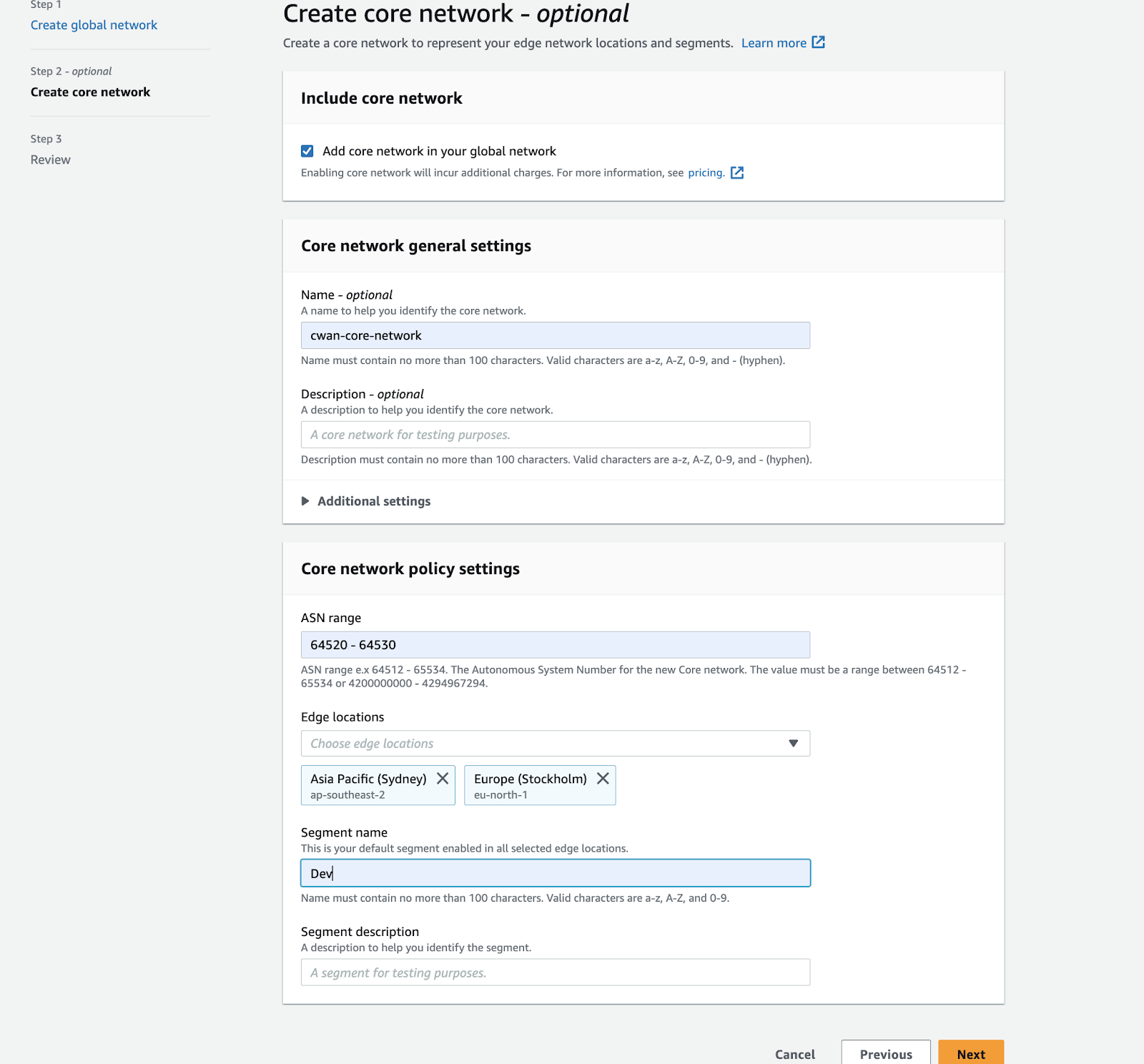
- While creating the core network, ensure that you add all the regions your VPCs are configured to, in the edge locations section under core network policy settings. You also need to create segments and add the type of segment (dev, prod, management, or security) that these regions belong to, under the segment name.
AWS Cloud WAN can be deployed using two methods:
- Federating transit gateways with Cloud WAN – In this method you replace statically created transit gateway peering connections with Cloud WAN. While federating transit gateways with Cloud WAN, you will need to register the transit gateways using the AWS Network Manager and create peering between the transit gateways and create attachments to the transit gateways, and then apply the Cloud WAN configuration.
- Cloud WAN only – In this method Cloud WAN is used for all connectivity and transit gateways are removed.
Deploy the AWS Cloud WAN
Cloud WAN is the interconnection of VPCs and on-premises networks. Lets now dive deep
on how to secure traffic interconnected with Cloud WAN using Palo Alto Networks
Cloud NGFWs. Though Cloud WAN is a global construct, Palo Alto Networks recommends
deploying Cloud NGFW in every AWS region it spans, to maintain a security posture
with low latency, and optimized costs.
Cloud NGFW can be deployed in a centralized security VPC in every region.
The security VPC can be directly connected to the cloud WAN security segment via
attachment. The routing associated with the attachments and segments define how the
traffic gets routed toward the Cloud NGFW resource for threat prevention. You can
redirect traffic arriving from cloud attachments to security VPC, before forwarding
to the destination. Cloud NGFW deployed within a region can now protect and
secure.
- East-West traffic with inter-region flows and intra-region flows
- Inspect and secure outbound traffic flow
- Inspect and secure traffic from on-premises and branch environment
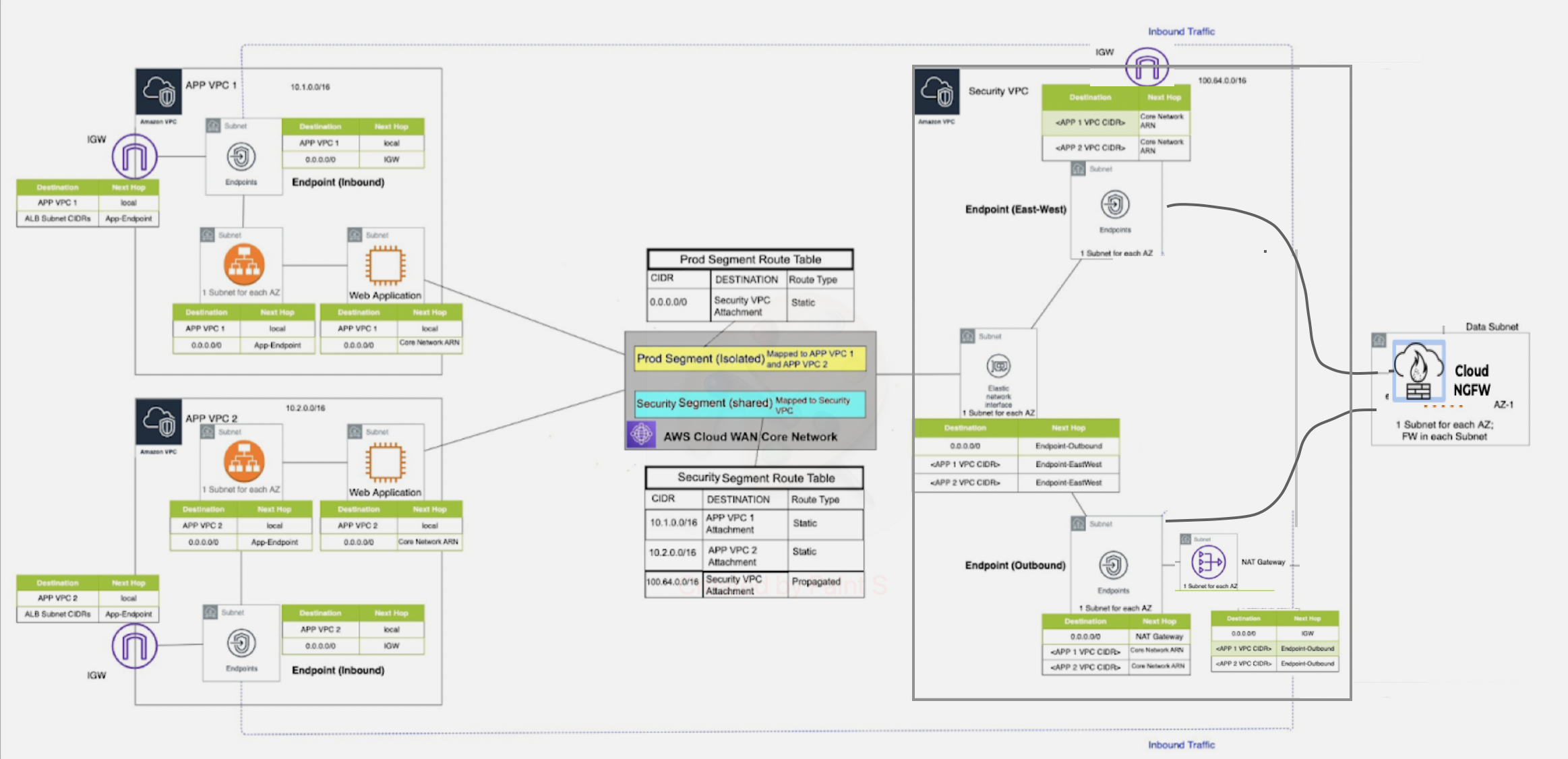
Let us consider a use case where VPCs are in the same region (isolated
attachments). To configure this setup, deploy the Cloud NGFW firewall within the
security VPC. You can deploy the Cloud NGFW firewall in a security VPC, which is
directly connected to a Cloud WAN or through a transit gateway with a Cloud WAN
attachment.
To migrate completely off the transit gateway, you must
connect your VPCs directly to the Cloud WAN.
Egress traffic from the production VPC is routed to the Cloud WAN, which is
then routed to the security VPC for inspection and sent out through NAT gateway and
internal gateway. In the reverse direction, traffic from the security VPC reaches
the security segment and then based on the routing configuration, is sent to the VPC
attachment.
To inspect traffic between VPCs in the same segment and the same region with AWS
Cloud WAN(only) deployment, execute the following tasks:
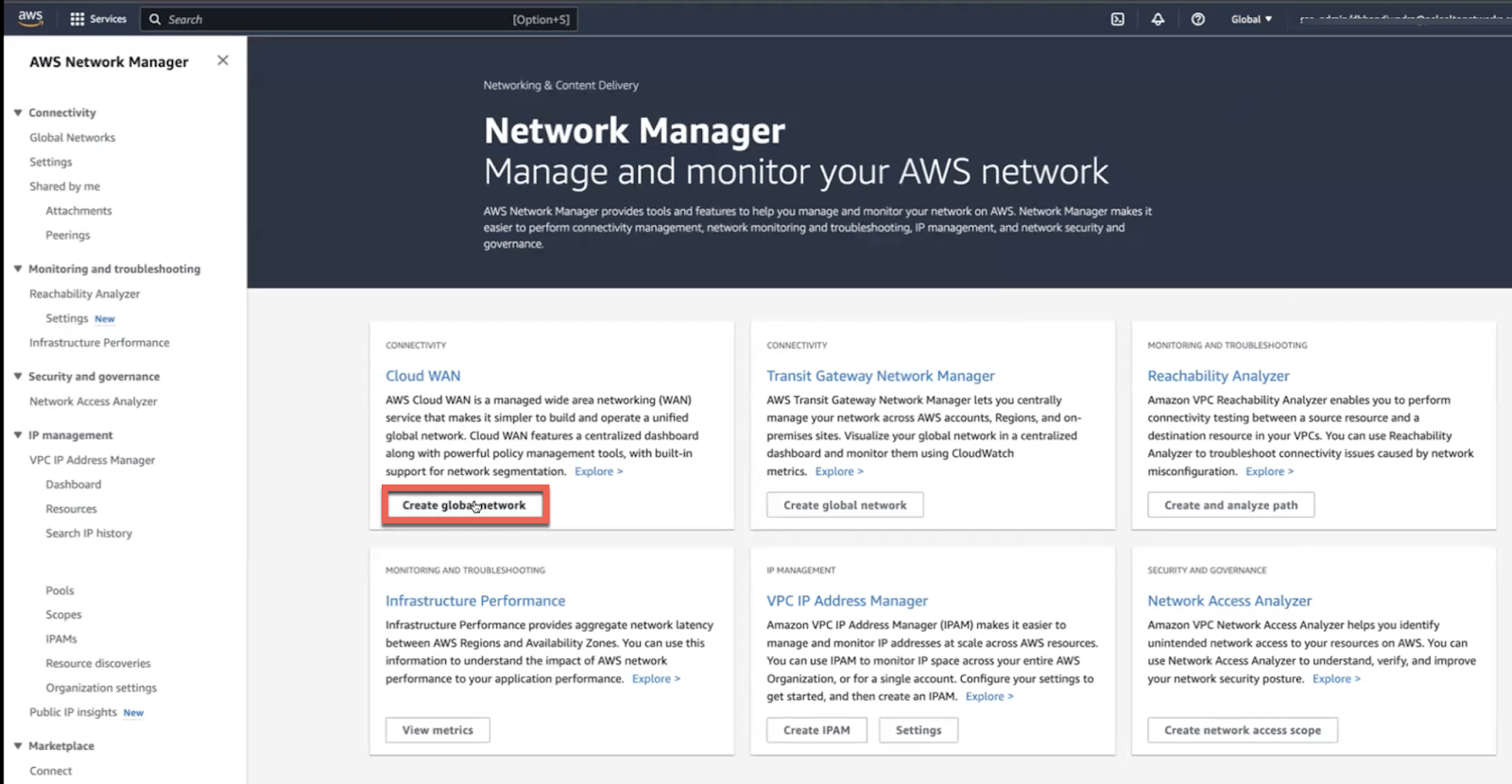
- Login to AWS Network Manager and Create global network.
![]()
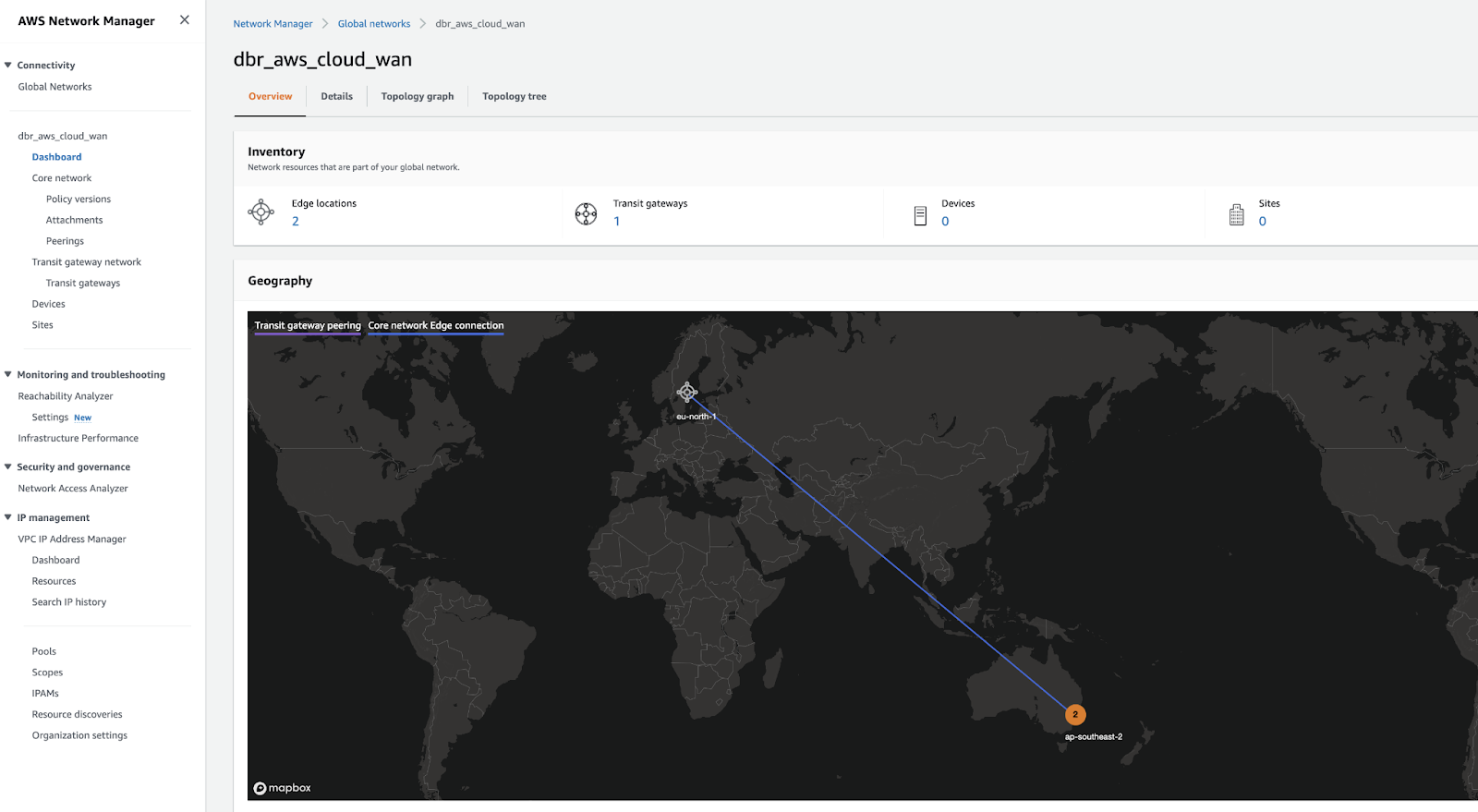
![]()
- Create a core network and core network
policy.Use the AWS Cloud WAN console to create a core network policy version following these tasks:
- Configure the network
settings.
![]()
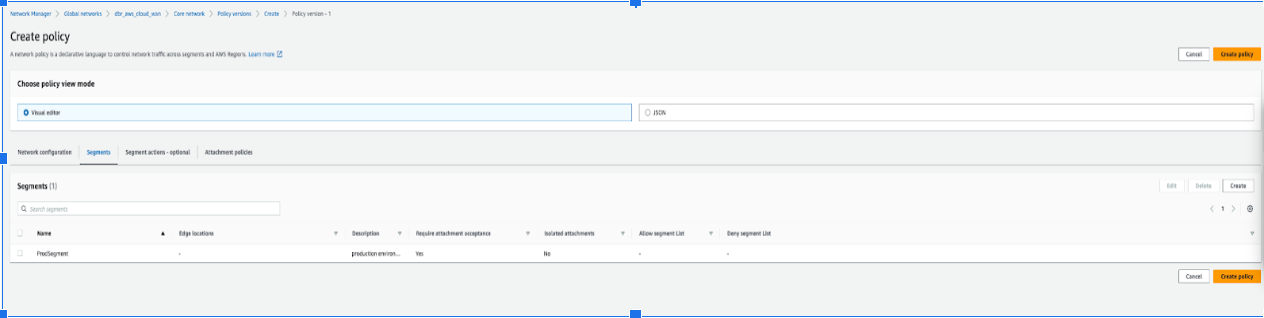
- To edit a policy version, click Policy versions, select
the required policy and click Edit. Make necessary
changes and click Create Policy.
![]()
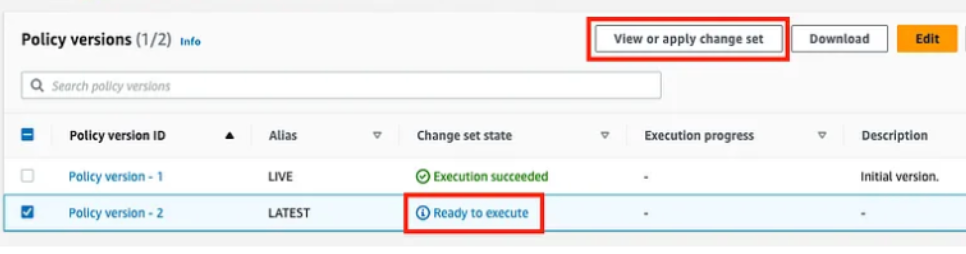
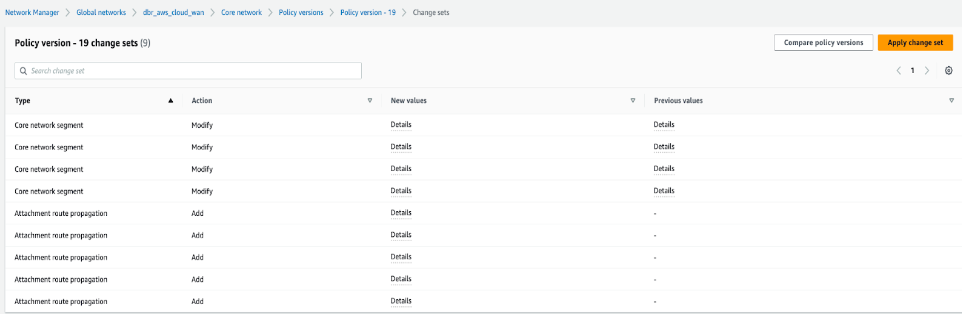
- After the change set the state of the policy version changes to
Ready to execute, execute the policy by clicking
View or apply change set. Alternatively, click
Compare policy version to view the JSON document.
![]()
![]()
- To edit a policy version, click Policy versions, select
the required policy and click Edit. Make necessary
changes and click Create Policy.
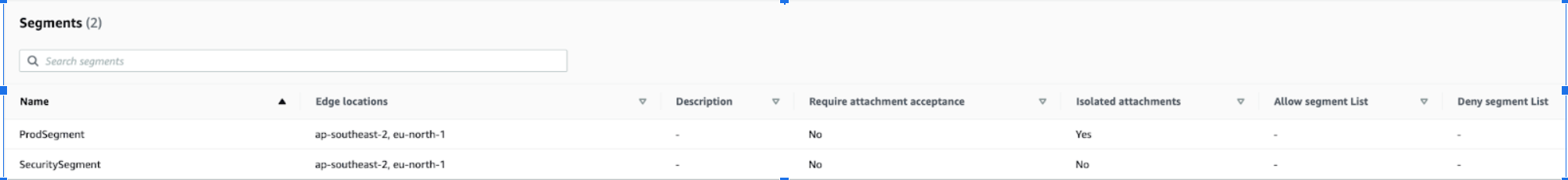
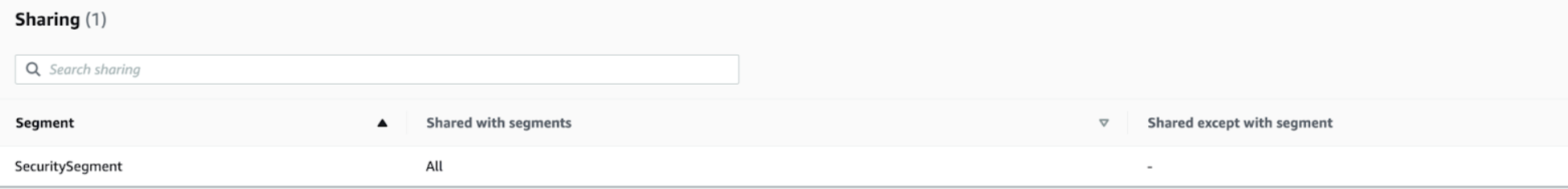
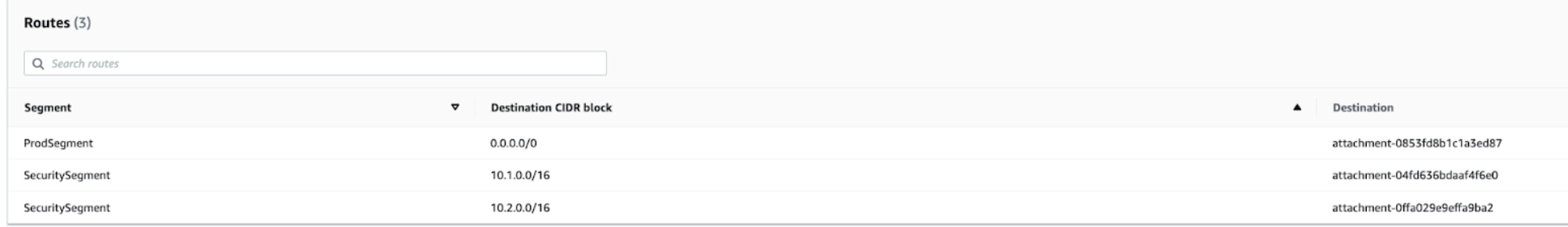
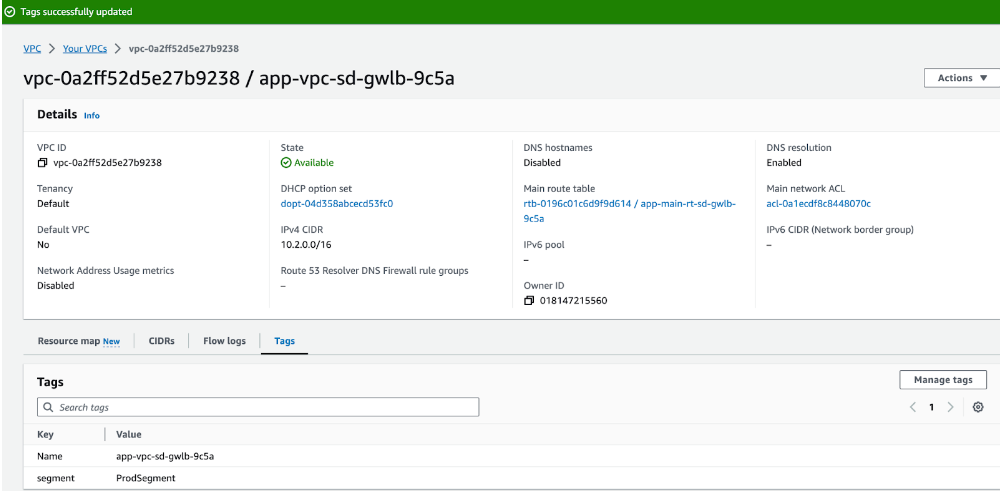
- While configuring policy versions, ensure that you add the applications – APP VPC 1 (10.1.0.0/16) and APP VPC 2(10.2.0.0/16) in the prod segment and the firewall, and security VPC (100.64.0.0/16) in the security segment.
![]()
![]()
![]()
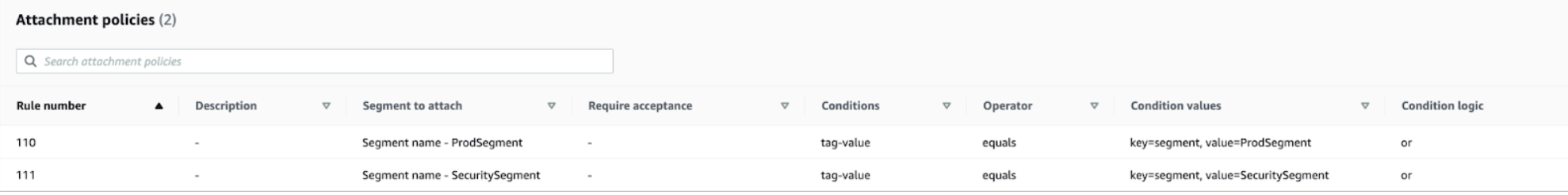
![]() You choose to add tags such as the prod segment (value) to the segment (key). These tags are reflected only after you add the segments in the Cloud WAN.
You choose to add tags such as the prod segment (value) to the segment (key). These tags are reflected only after you add the segments in the Cloud WAN.
- Configure the network
settings.
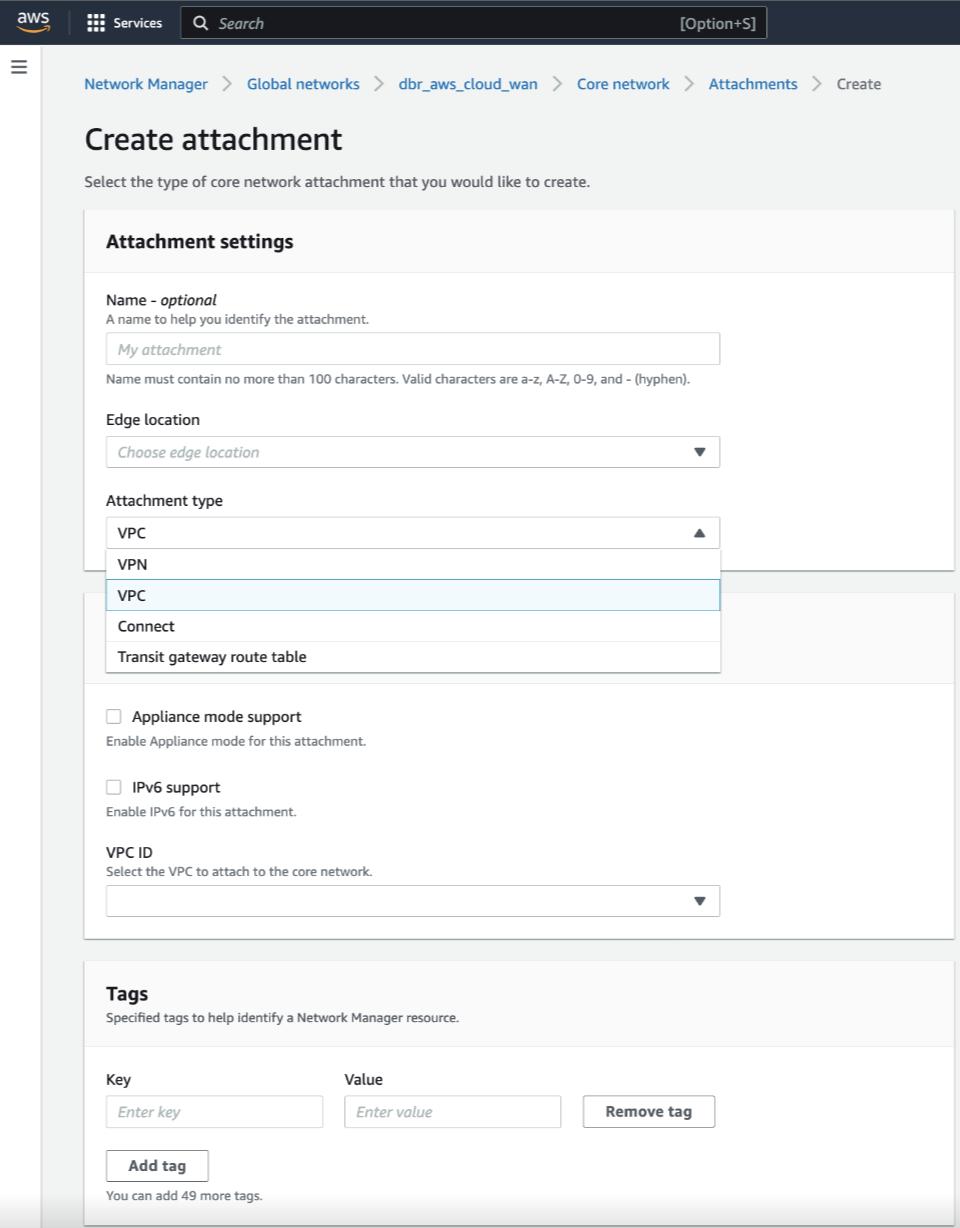
- Create an attachment.
- Use VPC or transit gateway route table as attachment type while creating an attachment.
- To ensure that the Cloud NGFW firewall can inspect traffic that is routed between VPC attachments, you must enable appliance mode on the VPC attachment for the security VPC containing the Cloud NGFW firewall.
![]()
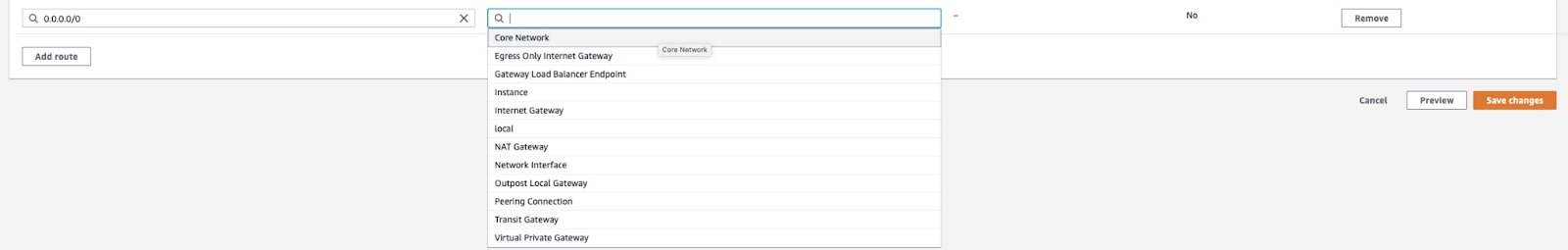
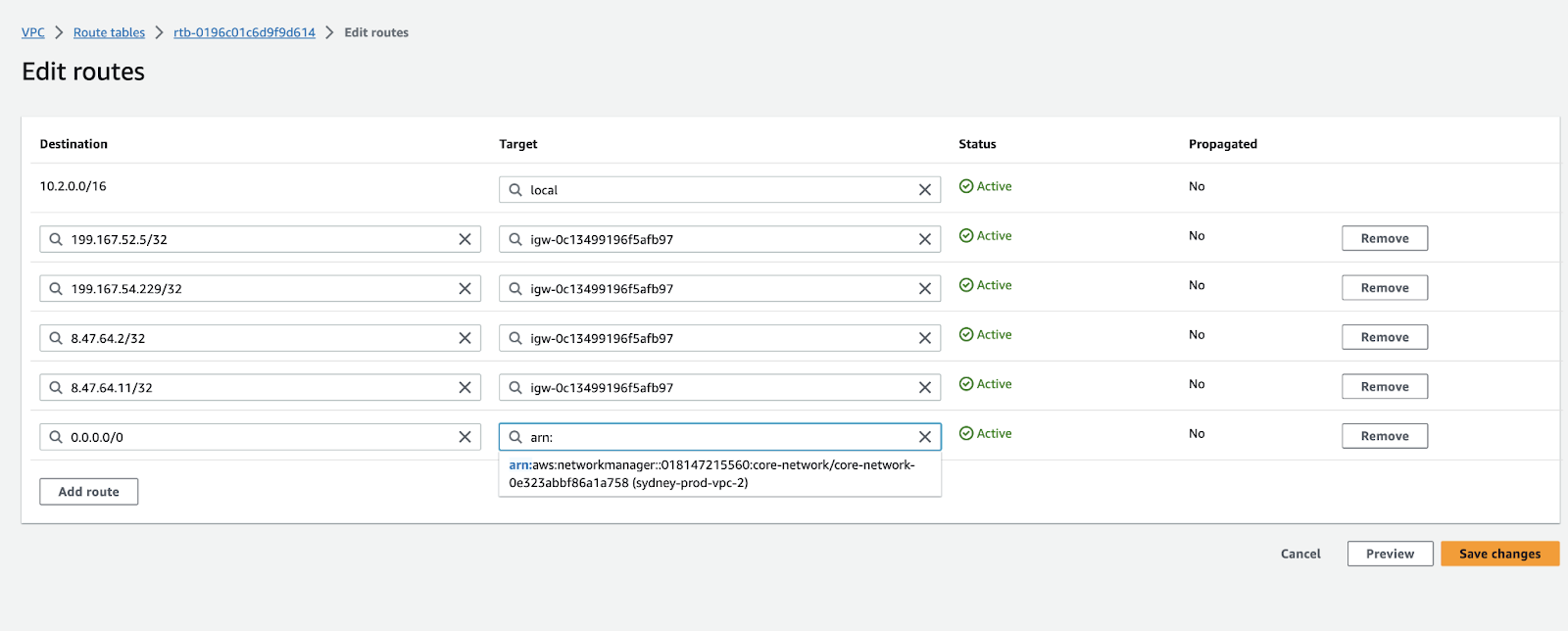
- Update VPC Route tables.Now that the necessary Cloud WAN constructs are in place, the VPCs need to be adjusted to facilitate packet forwarding toward the core network. The application and firewall instances or the respective VPCs need to be tagged similar to that of the segment. Add specific tags to the attachment to match the attachment created during Create policy attachments. of step 2.
To enable communication between attachment VPCs and the Core network, VPC route
tables need to be updated from the existing target transit gateway route to
corresponding Core Network ARN as shown below.
Packet Walkthrough
The following steps describe a packet walkthrough when an EC2 instance in
Application VPC 1 communicates with an EC2 instance in Application VPC 2:
- When a client in APP VPC 1(10.1.0.0/16) starts a connection to a server in APP VPC 2 (10.2.0.0/16), it does a VPC (App Subnet) route table lookup. The packet matches the default route entry with the Core Network ARN as the target and the packet gets routed to the core network.
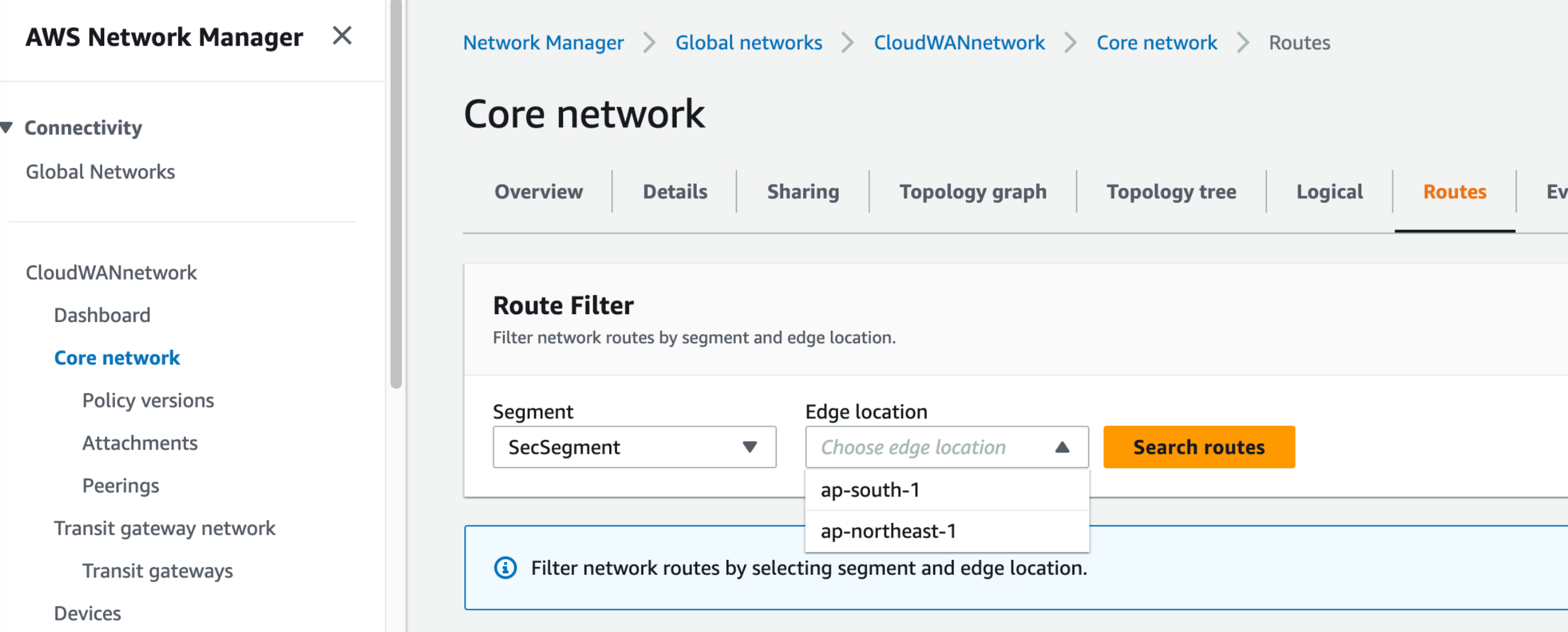
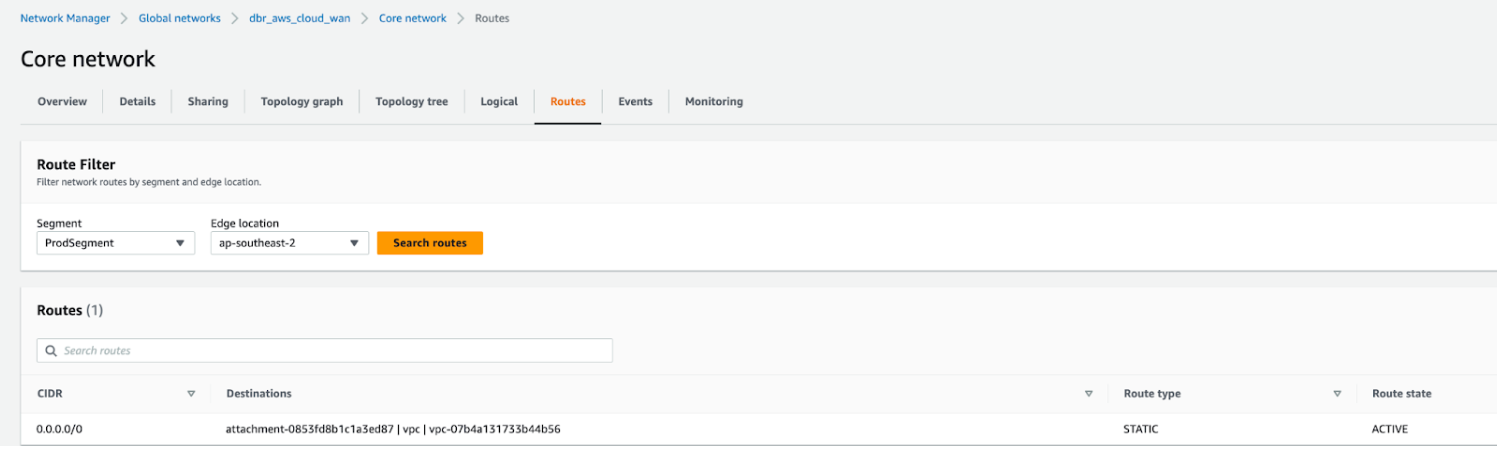
- When the packet arrives at the core network, it does a prod segment
route table lookup because APP VPC 1 is associated with the prod segment. The
packet matches the default entry with security attachment as the target and the
packet gets routed to security VPC.
![]()
![]()
- When the packet arrives at the security VPC(100.64.0.0/16) attachment, it does a VPC (CWAN Subnet) route table lookup. The packet matches the default route with firewall endpoint 1 as the target and the packet gets routed to a firewall, through the firewall’s endpoint, for inspection.
- The firewall inspects the traffic, compares it to its security policy, and allows it through. The firewall routes the packet back to the firewall’s endpoint, where it does a VPC (Firewall Subnet) route table lookup. The packet matches the default route entry with the Core Network ARN as the target, and the packet gets routed to the Core Network.
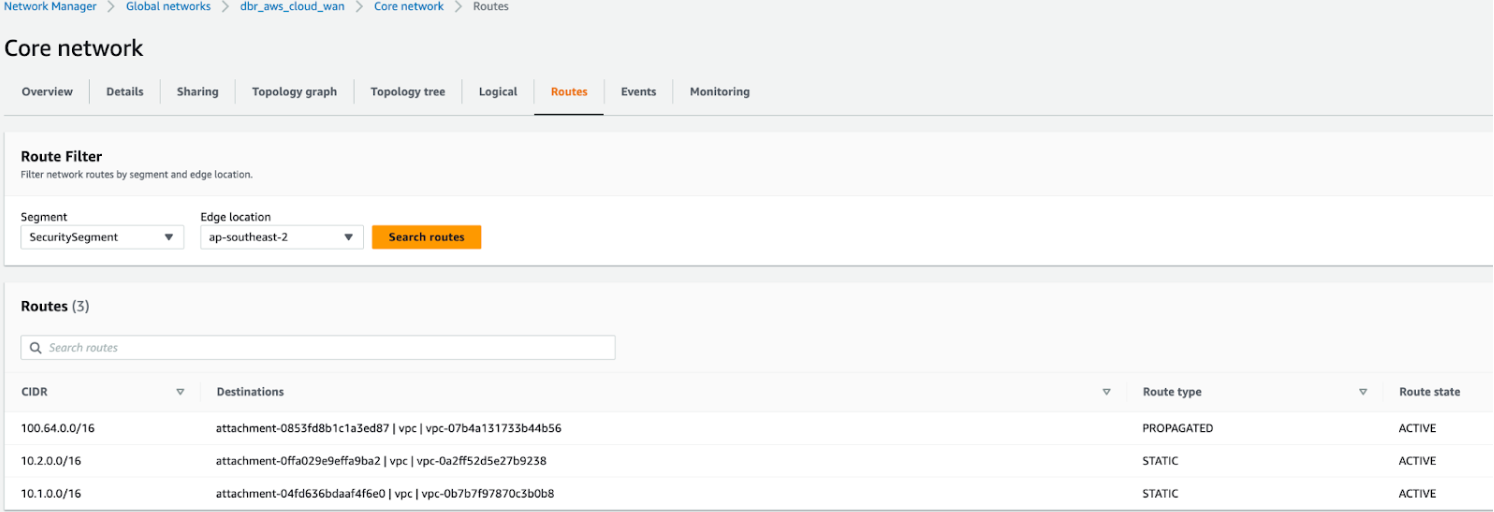
- When the packet arrives at the core network, it does a shared security
route table lookup because the security VPC is associated with the security
segment. The packet matches the APP VPC 2 CIDR(10.2.0.0/16) entry with APP VPC 2
attachment as the target and the packet gets routed to APP VPC 2.
![]()
- When the packet arrives at APP VPC 2, it does a VPC (CWAN Subnet) route table lookup. The packet matches the VPC CIDR entry with local as the target and the packet gets routed to Instance.
Return traffic traces the same path in the opposite direction.