Download PDF
GlobalProtect
Remote Access VPN with Two-Factor Authentication
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
-
-
-
- 6.3
- 6.2
- 6.1
- 6.0
-
- 6.3
- 6.2
- 6.1
- 6.0
Remote Access VPN with Two-Factor Authentication
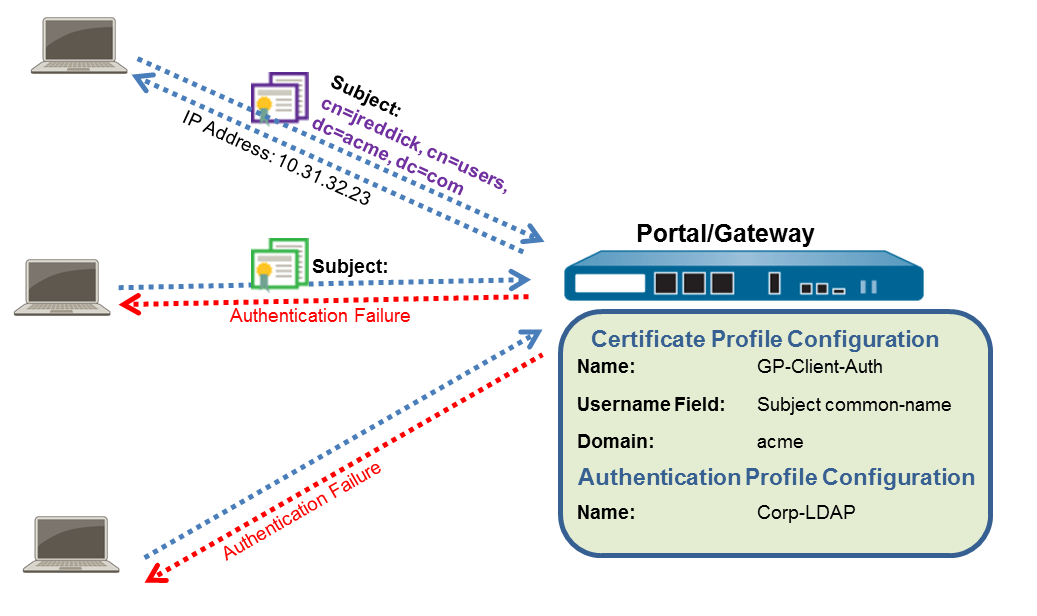
If you configure a GlobalProtect portal or
gateway with an authentication profile and a certificate profile
(which together can provide two-factor authentication), the end
user must authentication through both profiles successfully before
gaining access. For portal authentication, this means that certificates
must be pre-deployed on the endpoints before their initial portal
connection. Additionally, the client certificate presented by a
user must match what is defined in the certificate profile.
- If the certificate profile does not specify a username field (Username Field is set to None), the client certificate does not require a username. In this case, the user must provide the username when authenticating against the authentication profile.
- If the certificate profile specifies a username field, the certificate that the user presents must contain a username in the corresponding field. For example, if the certificate profile specifies that the username field is Subject, the certificate presented by the user must contain a value in the common-name field, or else authentication fails. In addition, when the username field is required, the value from the username field of the certificate is automatically populated as the username when the user attempts to enter credentials for authenticating to the authentication profile. If you do not want force users to authenticate with a username from the certificate, do not specify a username field in the certificate profile.
This quick
configuration uses the same topology as GlobalProtect
VPN for Remote Access. However, in this configuration, users
must authenticate against a certificate profile and an authentication
profile. For more details on a specific type of two-factor authentication,
see the following topics:
Use
the following procedure to configure remote VPN access with two-factor authentication.
- (Required only on NGFW managed by Panorama or Strata Cloud Manager)Create Interfaces and Zones for GlobalProtect.Use the default virtual router for all interface configurations to avoid having to create inter-zone routing.
- Select NetworkInterfacesEthernet. Configure ethernet1/2 as a Layer3 Ethernet interface with IP address 203.0.113.1 and assign it to the l3-untrust Security Zone and the default Virtual Router.
- Create a DNS “A” record that maps IP address 203.0.113.1 to gp.acme.com.
- Select NetworkInterfacesTunnel and Add the tunnel.2 interface. Add the tunnel interface to a new Security Zone called corp-vpn, and then assign it to the default Virtual Router.
- Enable User Identification on the corp-vpn zone.
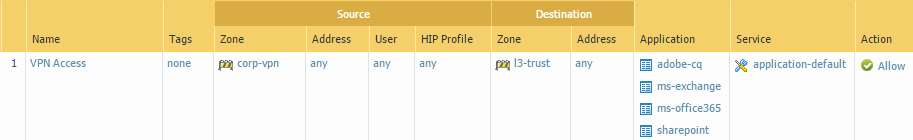
Create security policies to enable traffic flow between the corp-vpn zone and the l3-trustzone, which enables access to your internal resources.- Do one of the following:
- On Panorama, select PoliciesSecurity, and then Add a new rule.
- On Strata Cloud Manager, select ManageConfigurationNGFW and Prisma AccessSecurity Services and then Add a new rule.
For this example, you would define the rule with the following settings:- Name (General tab)—VPN Access
- Source Zone (Source tab)—corp-vpn
- Destination Zone (Destination tab)—l3-trust
![]() Use one of the following methods to obtain a server certificate for the interface hosting the GlobalProtect portal and gateway:Manage certificates as follows:
Use one of the following methods to obtain a server certificate for the interface hosting the GlobalProtect portal and gateway:Manage certificates as follows:- Obtain a server certificate. Because the portal and gateway are on the same interface, the same server certificate can be used for both components.
- The CN of the certificate must match the FQDN, gp.acme.com.
- To enable users to connect to the portal without receiving certificate errors, use a server certificate from a public CA.
Issue client certificates to GlobalProtect clients and endpoints.- Use your enterprise PKI or a public CA to issue a unique client certificate to each GlobalProtect user.Install certificates in the personal certificate store on the endpoints.Create a client certificate profile.
- Do one of the following:
- On Panorama, select DeviceCertificate ManagementCertificate Profile. Add a new certificate profile, and then enter a profile Name such as GP-client-cert.
- On Strata Cloud Manager, select ManageConfigurationNGFW and Prisma AccessObjectsCertificate ManagementCertificate Profile. Add a new certificate profile, and then enter a profile Name such as GP-client-cert.
Select DeviceCertificate ManagementCertificate Profile. Add a new certificate profile, and then enter a profile Name such as GP-client-cert.Specify where to obtain the username that will be used to authenticate the end user:- From user—If you want the end user to supply a username when authenticating to the service specified in the authentication profile, select None as the Username Field.
- From certificate—If you want to extract the username from the certificate, select Subject as the Username Field. If you use this option, the CN contained in the certificate automatically populates the username field when the user is prompted to log in to the portal/gateway. The user is required to log in using that username.
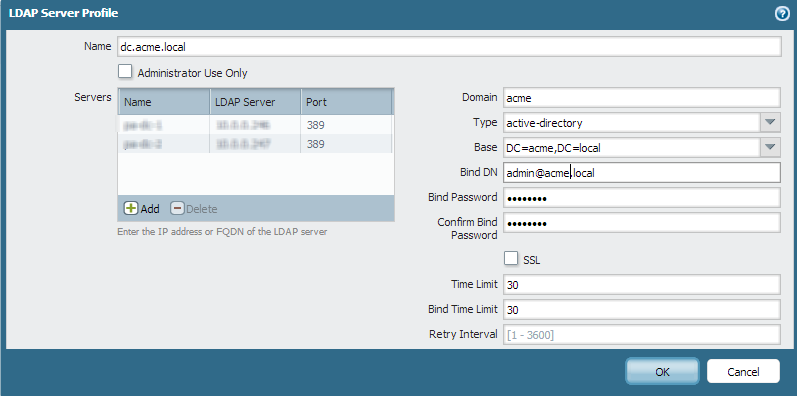
In the CA Certificates area, Add the CA certificate that issued the client certificates. Click OK twice.Create a server profile.The server profile instructs the firewall on how to connect to the authentication service. Local, RADIUS, Kerberos, SAML, and LDAP authentication methods are supported. This example shows an LDAP authentication profile for authenticating users against the Active Directory.Create the server profile for connecting to the LDAP server (DeviceServer ProfilesLDAP).![]() (Optional) Create an authentication profile.Attach the server profile to an authentication profile:
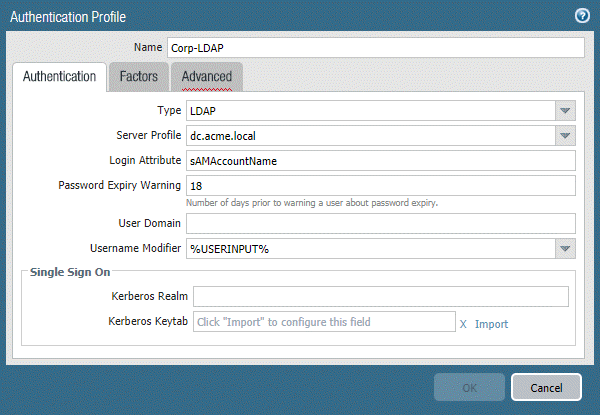
(Optional) Create an authentication profile.Attach the server profile to an authentication profile:- On Panorama, select DeviceAuthentication Profile.
- On Strata Cloud Manager, select ManageConfigurationNGFW and Prisma AccessIdentity ServicesAuthentication Profiles.
![]() Configure a GlobalProtect Gateway the following configuration.See the topology diagram shown in GlobalProtect VPN for Remote Access.Interface—ethernet1/2IP Address—203.0.113.1Server Certificate—GP-server-cert.pem issued by GoDaddyCertificate Profile—GP-client-certAuthentication Profile—Corp-LDAPTunnel Interface—tunnel.2IP Pool—10.31.32.3 - 10.31.32.118Configure a GlobalProtect Portals with the following configuration:Select NetworkGlobalProtectPortals, and then Add the following configuration:
Configure a GlobalProtect Gateway the following configuration.See the topology diagram shown in GlobalProtect VPN for Remote Access.Interface—ethernet1/2IP Address—203.0.113.1Server Certificate—GP-server-cert.pem issued by GoDaddyCertificate Profile—GP-client-certAuthentication Profile—Corp-LDAPTunnel Interface—tunnel.2IP Pool—10.31.32.3 - 10.31.32.118Configure a GlobalProtect Portals with the following configuration:Select NetworkGlobalProtectPortals, and then Add the following configuration:- Set Up Access to the GlobalProtect Portal:Interface—ethernet1/2IP Address—203.0.113.1Server Certificate—GP-server-cert.pem issued by GoDaddyCertificate Profile—GP-client-certAuthentication Profile—Corp-LDAPDefine the GlobalProtect Agent Configurations:Connect Method—On-demand (Manual user initiated connection)External Gateway Address—gp.acme.comDeploy the GlobalProtect App Software.Follow the procedure to Host App Updates on the Portal.(Optional) Deploy App Settings Transparently.As an alternative to deploying app settings from the portal configuration, you can define settings directly from the Windows registry or global macOS plist. Examples of settings that you can deploy include specifying the portal IP address or enabling GlobalProtect to initiate a VPN tunnel before a user logs in to the endpoint and connects to the GlobalProtect portal. On Windows endpoints only, you can also configure settings using the MSIEXEC installer.(Optional) Enable use of the GlobalProtect mobile app.Purchase and install a GlobalProtect subscription to enable use of the app.Save the GlobalProtect configuration.Click Commit.