Next-Generation Firewall
Share User-ID Mappings Across Virtual Systems
Table of Contents
Expand All
|
Collapse All
Next-Generation Firewall Docs
-
-
-
-
-
-
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 11.0 (EoL)
- PAN-OS 10.2
- PAN-OS 10.1
- PAN-OS 10.0 (EoL)
- PAN-OS 9.1 (EoL)
- PAN-OS 9.0 (EoL)
- PAN-OS 8.1 (EoL)
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 10.2
- PAN-OS 10.1
Share User-ID Mappings Across Virtual Systems
To share IP address-to-username mappings and username-to-group
mappings across virtual systems, assign a virtual system as a User-ID
hub.
To simplify User-ID™ source configuration
when you have multiple virtual systems, configure the User-ID sources
on a single virtual system to share
IP address-to-username mappings and username-to-group mappings with
all other virtual systems on the firewall.
Configuring a
single virtual system as a User-ID hub simplifies user
mapping by eliminating the need to configure the sources on multiple
virtual systems, especially if traffic will pass through multiple
virtual systems based on the resources the user is trying to access
(for example, in an academic networking environment where a student will
be accessing different departments whose traffic is managed by different
virtual systems).
To map the user or group, the firewall
uses the mapping table on the local virtual system and applies the
policy for that user or group. If the firewall does not find the
mapping for a user or group on the virtual system where that user’s
traffic originated, the firewall queries the hub to fetch the IP
address-to-username information for that user or group mapping information
for that group. If the firewall locates the mapping on both the
User-ID hub and the local virtual system, the firewall uses the
mapping it learns locally. If the mapping on the local firewall
differs from the mapping on the virtual system hub, the firewall
uses the local mapping.
After you configure the User-ID hub,
the virtual system can use the mapping table on the User-ID hub
when it needs to identify a user for user-based policy enforcement
or to display the username in a log or report but the source is
not available locally. When you select a hub, the firewall retains
the mappings on other virtual systems so we recommend consolidating
the User-ID sources on the hub. However, if you don’t want to share
mappings from a specific source, you can configure an individual
virtual system to perform user or group mapping.
- Assign the virtual system as a User-ID hub.
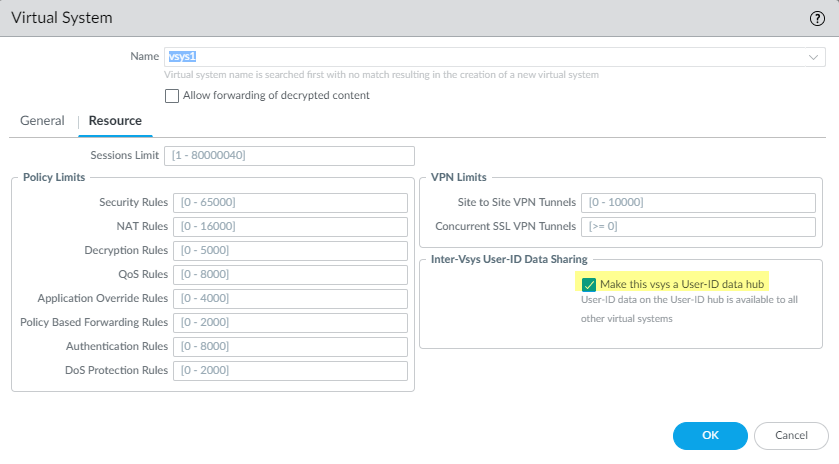
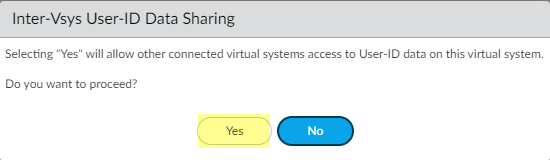
- Select DeviceVirtual Systems and then select the virtual system where you consolidated your User-ID sources.On the Resource tab, Make this vsys a User-ID data hub and click Yes to confirm. Then click OK.
![]() Click Yes to confirm.
Click Yes to confirm.![]() Select the Mapping Type that you want to share then click OK.
Select the Mapping Type that you want to share then click OK.![]()
- IP User Mapping—Share IP address-to-username mapping information with other virtual systems.
- User Group Mapping—Share group mapping information with other virtual systems.
You must select at least one mapping type.Consolidate your User-ID sources and migrate them to the virtual system that you want to use as a User-ID hub.This consolidates the User-ID configuration for operational simplicity. By configuring the hub to monitor servers and connect to agents that were previously monitored by other virtual systems, the hub collects the user mapping information instead of having each virtual system collect it independently. If you don’t want to share mappings from specific virtual systems, configure those mappings on a virtual system that will not be used as the hub.Use the same format for the Primary Username across virtual systems and firewalls.- Remove any sources that are unnecessary or outdated.Identify all configurations for your Windows-based or integrated agents and any sources that send user mappings using the XML API and copy them to the virtual system you want to use as a User-ID hub.On the hub, you can configure any User-ID source that is currently configured on a virtual system. However, IP address-and-port-to-username mapping information from Terminal Server agents are not shared between the User-ID hub and the connected virtual systems.Specify the subnetworks that User-ID should include in or exclude from mapping.Define the Ignore User List.On all other virtual systems, remove any sources that are on the User-ID hub.Commit the changes to enable the User-ID hub and begin collecting mappings for the consolidated sources.Confirm the User-ID hub is mapping the users and groups.
- Use the show user ip-user-mapping all command to show the IP address-to-username mappings and which virtual system provides the mappings.Use the show user user-id-agent statistics command to show which virtual system is serving as the User-ID hub.Confirm the hub is sharing the group mappings by using the following CLI commands:
- show user group-mapping statistics
- show user group-mapping state all
- show user group list
- show user group name <group-name>