Perform Initial Configuration
Table of Contents
Expand All
|
Collapse All
Next-Generation Firewall Docs
-
-
- Cloud Management of NGFWs
- PAN-OS 10.0 (EoL)
- PAN-OS 10.1
- PAN-OS 10.2
- PAN-OS 11.0 (EoL)
- PAN-OS 11.1 & Later
- PAN-OS 9.1 (EoL)
-
- PAN-OS 10.1
- PAN-OS 10.2
- PAN-OS 11.0 (EoL)
- PAN-OS 11.1 & Later
-
-
- Cloud Management and AIOps for NGFW
- PAN-OS 10.0 (EoL)
- PAN-OS 10.1
- PAN-OS 10.2
- PAN-OS 11.0 (EoL)
- PAN-OS 11.1
- PAN-OS 11.2
- PAN-OS 8.1 (EoL)
- PAN-OS 9.0 (EoL)
- PAN-OS 9.1 (EoL)
Perform Initial Configuration
By default, the PA-Series firewall has an
IP address of 192.168.1.1 and a username/password of admin/admin.
For security reasons, you must change these settings before continuing
with other firewall configuration tasks. You must perform these
initial configuration tasks either from the MGT interface, even
if you do not plan to use this interface for your firewall management,
or using a direct serial connection to the console port on the firewall.
- Install your firewall and connect power to it.If your firewall model has dual power supplies, connect the second power supply for redundancy. Refer to the hardware reference guide for your model for details.Gather the required information from your network administrator.
- IP address and netmask (if the MGT port will have a static address)
- Default gateway (if the MGT port will have a static default gateway address)
- DNS server address
Connect your computer to the firewall.You can connect to the firewall in one of the following ways:- Connect a serial cable from your computer to the Console port and connect to the firewall using terminal emulation software (9600-8-N-1). Wait a few minutes for the boot-up sequence to complete; when the firewall is ready, the prompt changes to the name of the firewall, for example PA-220 login.
- Connect an RJ-45 Ethernet cable from your computer to the MGT port on the firewall. From a browser, go to https://192.168.1.1.
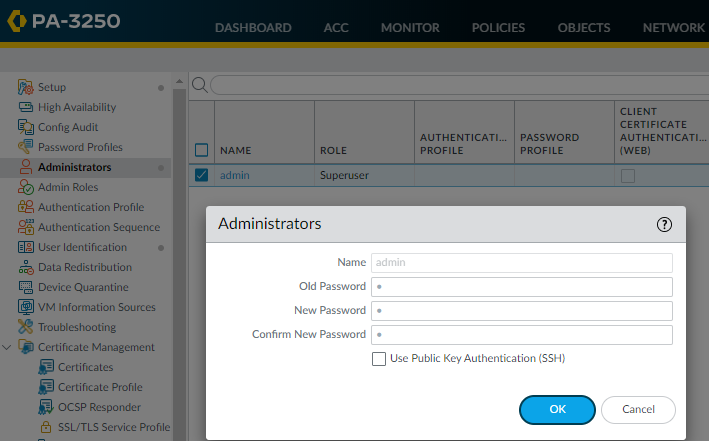
You may need to change the IP address on your computer to an address in the 192.168.1.0/24 network, such as 192.168.1.2, to access this URL.When prompted, log in to the firewall.You must log in using the default username and password (admin/admin). The firewall will begin to initialize.Set a secure username and password for the admin account.The predefined, default administrator password (admin) must be changed on the first login on a device. The new password must be a minimum of eight characters and include a minimum of one lowercase and one uppercase character, as well as one number or special character. Although you don’t have to configure a new username, it is a best practice to do so and to use unique usernames and passwords for each administrator. The login must include at least one alphabetical character or symbol (underscore, period, or hyphen, although a hyphen cannot be the first character in the username) and cannot be numbers only.Be sure to use the best practices for password strength to ensure a strict password and review the minimum password complexity.- Select DeviceAdministrators.Select the admin role.Enter the current default password and the new password.
![]() Click OK to save your settings.Configure the MGT interface.
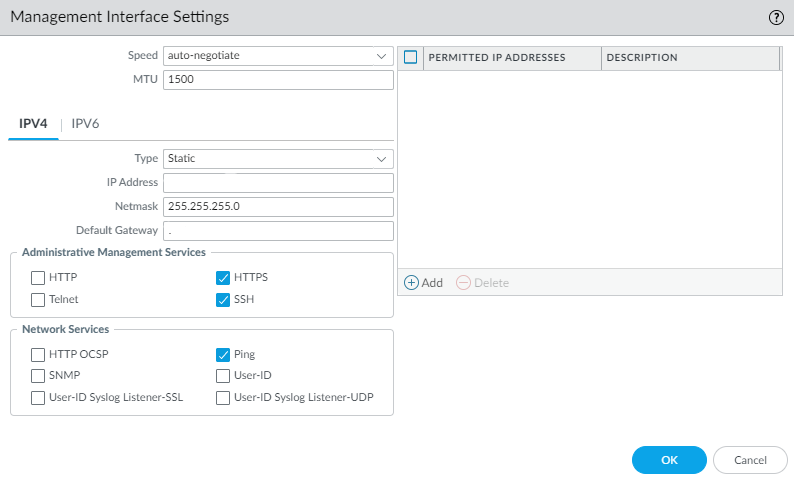
Click OK to save your settings.Configure the MGT interface.- Select DeviceSetupInterfaces and edit the Management interface.Set the Speed to auto-negotiate.Specify the MTU in bytes for packets sent on this interface.Select IPv4 or IPv6.To configure IPv4 address settings for the MGT interface, select an address Type:
- Static— Enter the IP Address, Netmask, and Default Gateway.
- DHCP Client—To configure dynamic address settings, you must Configure the Management Interface as a DHCP Client.
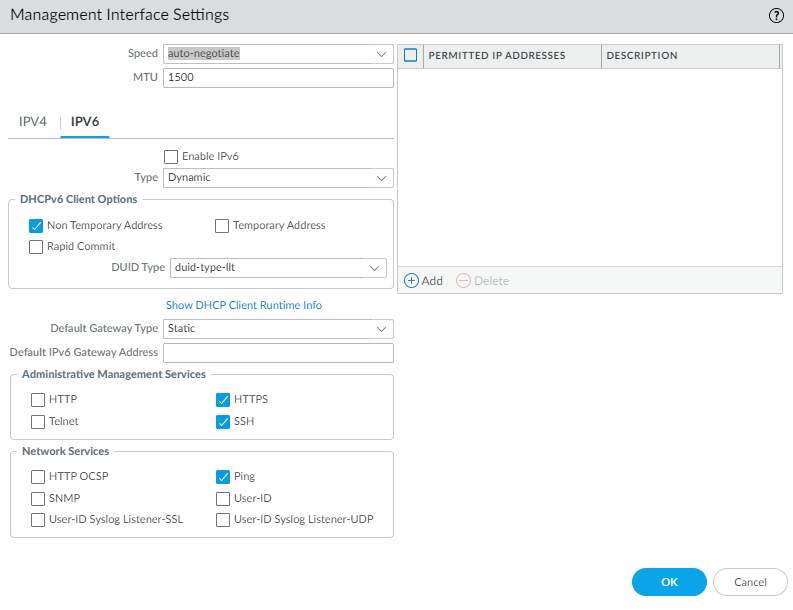
![]() To configure IPv6 address settings for the MGT interface, Enable IPv6 and select an address Type:
To configure IPv6 address settings for the MGT interface, Enable IPv6 and select an address Type:- Static— Enter the IPv6 Address/Prefix Length. Additionally, select a Default Gateway Type: Static (enter the Default IPv6 Gateway Address) or Dynamic (the firewall learns the default gateway address from the Router Advertisement message that the router sent).
- DHCP Client—To configure dynamic IPv6 address settings, you must Configure the Management Interface for Dynamic IPv6 Address Assignment.
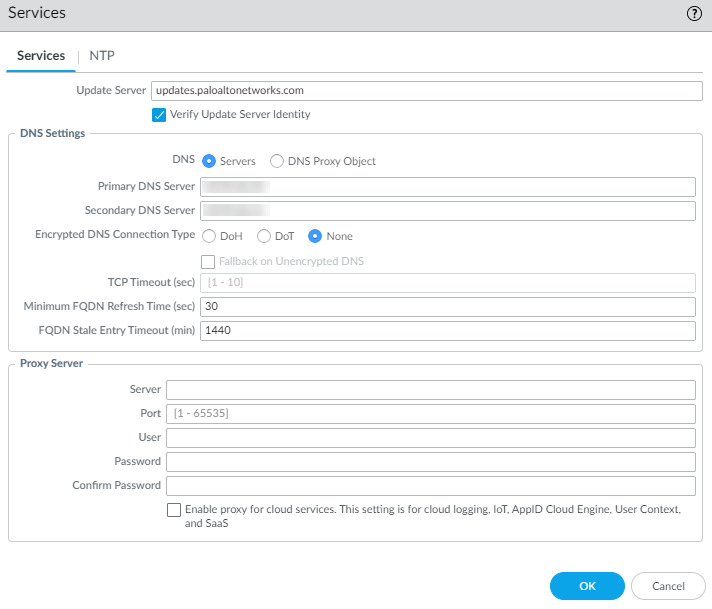
![]() To prevent unauthorized access to the management interface, it is a an administrative best practice to Add the Permitted IP Addresses from which an administrator can access the MGT interface.Select which management services to allow on the interface.Make sure Telnet and HTTP aren't selected because these services use plaintext and aren't as secure as the other services; they could compromise administrator credentials.Click OK.Specify the update server, and configure DNS settings and proxy server settings.You must manually configure at least one DNS server on the firewall or it won't be able to resolve hostnames; it won't use DNS server settings from another source, such as an ISP.
To prevent unauthorized access to the management interface, it is a an administrative best practice to Add the Permitted IP Addresses from which an administrator can access the MGT interface.Select which management services to allow on the interface.Make sure Telnet and HTTP aren't selected because these services use plaintext and aren't as secure as the other services; they could compromise administrator credentials.Click OK.Specify the update server, and configure DNS settings and proxy server settings.You must manually configure at least one DNS server on the firewall or it won't be able to resolve hostnames; it won't use DNS server settings from another source, such as an ISP.- Select DeviceSetupServices.
- For multi-virtual system platforms, select Global and edit the Services section.
- For single virtual system platforms, edit the Services section.
On the Services tab, Update Server represents the IP address or host name of the server from which to download updates from Palo Alto Networks. The current value is updates.paloaltonetworks.com. Don't change this setting unless instructed by technical support.Select Verify Update Server Identity.It's a best practice to enable this option, which causes the firewall or Panorama to verify that the server from which the software or content package is downloaded has an SSL certificate signed by a trusted authority.For DNS, select the way for the MGT interface to get DNS services:- Servers—Enter the Primary DNS Server address and Secondary DNS Server address.
- DNS Proxy Object—From the drop-down, select the DNS Proxy that you want to use to configure global DNS services, or click DNS Proxy to configure a new DNS proxy object.Beginning with PAN-OS 11.2.1 and later releases, you can enable encrypted DNS on the MGT interface (whether the interface uses a DNS server or DNS proxy) by configuring DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT).
- To configure encrypted DNS when the MGT interface uses DNS servers, refer to the Networking Administrator's Guide, Use Case 1: Firewall Requires DNS Resolution..
- To configure encrypted DNS when the MGT interface uses DNS proxy, refer to the Networking Administrator's Guide, Configure a DNS Proxy Object.
![]() Click OK.Configure date and time (NTP) settings.
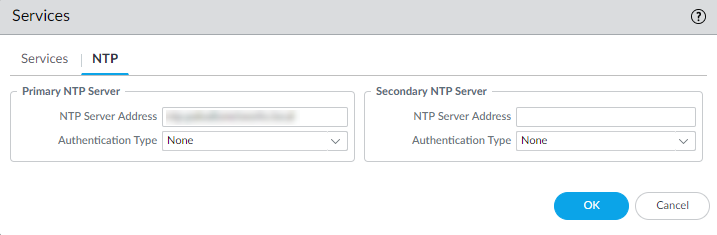
Click OK.Configure date and time (NTP) settings.- Select DeviceSetupServices.
- For multi-virtual system platforms, select Global and edit the Services section.
- For single virtual system platforms, edit the Services section.
On the NTP tab, to use the virtual cluster of time servers on the Internet, enter the hostname pool.ntp.org as the Primary NTP Server or enter the IP address of your primary NTP server.![]() (Optional) Enter a Secondary NTP Server address.(Optional) To authenticate time updates from the NTP server(s), for Authentication Type, select one of the following for each server:
(Optional) Enter a Secondary NTP Server address.(Optional) To authenticate time updates from the NTP server(s), for Authentication Type, select one of the following for each server:- None—(Default) Disables NTP authentication.
- Symmetric Key—Firewall uses symmetric key exchange (shared secrets) to authenticate time updates.
- Key ID—Enter the Key ID (1-65534).
- Algorithm—Select the algorithm to use in NTP authentication (MD5 or SHA1).
- Autokey—Firewall uses autokey (public key cryptography) to authenticate time updates.
Click OK.(Optional) Configure general firewall settings as needed.- Select DeviceSetupManagement and edit the General Settings.Enter a Hostname for the firewall and enter your network Domain name. The domain name is just a label; it will not be used to join the domain.Enter Login Banner text that informs users who are about to log in that they require authorization to access the firewall management functions.As a best practice, avoid using welcoming verbiage. Additionally, you should ask your legal department to review the banner message to ensure it adequately warns that unauthorized access is prohibited.Enter the Latitude and Longitude to enable accurate placement of the firewall on the world map.Click OK.Commit your changes.When the configuration changes are saved, you lose connectivity to the web interface because the IP address has changed.Click Commit at the top right of the web interface. The firewall can take up to 90 seconds to save your changes.Connect the firewall to your network.
- Disconnect the firewall from your computer.(All firewalls except for the PA-5450) Connect the MGT port to a switch port on your management network using an RJ-45 Ethernet cable. Make sure that the switch port you cable the firewall to is configured for auto-negotiation.(PA-5450 only) Connect the MGT port to a switch port on your management network using a Palo Alto Networks certified SFP/SFP+ transceiver and cable.Open an SSH management session to the firewall.Using a terminal emulation software, such as PuTTY, launch an SSH session to the firewall using the new IP address you assigned to it.Verify network access to external services required for firewall management, such as the Palo Alto Networks Update Server.You can do this in one of the following ways:
- If you do not want to allow external network access to the MGT interface, you will need to set up a data port to retrieve required service updates. Continue to Set Up Network Access for External Services.
- If you do plan to allow external network access to the MGT interface, verify that you have connectivity and then proceed to Register the Firewall and Activate Subscription Licenses.
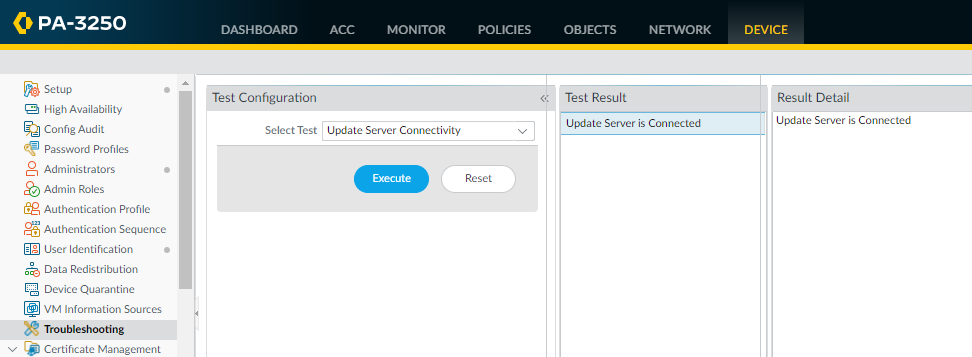
- Use update server connectivity test to verify network connectivity to the Palo Alto Networks Update server as shown in the following example:
- Select DeviceTroubleshooting, and select Update Server Connectivity from the Select Test drop-down.
- Execute the update server connectivity test.
![]() Use the following CLI command to retrieve information on the support entitlement for the firewall from the Palo Alto Networks update server:
Use the following CLI command to retrieve information on the support entitlement for the firewall from the Palo Alto Networks update server:request support checkIf you have connectivity, the update server will respond with the support status for your firewall. If your firewall is not yet registered, the update server returns the following message:Contact Us https://www.paloaltonetworks.com/company/contact-us.html Support Home https://www.paloaltonetworks.com/support/tabs/overview.html Device not found on this update server