Next-Generation Firewall
Configure OSPFv3 on an Advanced Routing Engine
Table of Contents
Expand All
|
Collapse All
Next-Generation Firewall Docs
-
-
-
-
-
-
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 11.0 (EoL)
- PAN-OS 10.2
- PAN-OS 10.1
- PAN-OS 10.0 (EoL)
- PAN-OS 9.1 (EoL)
- PAN-OS 9.0 (EoL)
- PAN-OS 8.1 (EoL)
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 10.2
- PAN-OS 10.1
Configure OSPFv3 on an Advanced Routing Engine
Configure OSPFv3 on an advanced routing engine.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
The Advanced Routing Engine supports OSPFv3, which supports only IPv6 addressing. Before you
configure OSPFv3, you should understand OSPF concepts.
Consider the OSPFv3 Routing Profiles and filters that you can apply to OSPFv3 and
thereby save configuration time and maintain consistency. You can create profiles
and filters in advance or as you configure OSPFv3.
- configure-a-logical-router.html#tabs-id83b76f3d-1148-43e8-b784-502628a974ab_id83b76f3d-1148-43e8-b784-502628a974ab.Configure general OSPFv3 routing options.
- Select NetworkRoutingLogical Routers and select the logical router.Select OSPFv3 and Enable it.
![]() Assign a Router ID to OPSFv3 for the logical router, which is typically an IPv4 address (even though OSPFv3 is for IPv6 addressing), to ensure the Router ID is unique.If you want to apply BFD to OSPFv3, select a BFD Profile you created, or select the default profile, or create a new BFD Profile to apply to all OSPFv3 interfaces belonging to the logical router. Default is None (Disable BFD).Select a Global General Timer profile or create a new one to set SPF throttle timers and to set the minimum interval between arriving instances of the same link-state advertisement (LSA).Select a Global Interface Timer profile or create a new one to set the hello interval, retransmit interval, and other settings.Select a Redistribution Profile or create a new one to redistribute IPv6 static routes, connected routes, IPv6 BGP routes, or the IPv6 default route to OSPFv3.Click OK.Create an OSPFv3 area and specify characteristics based on the type of area.
Assign a Router ID to OPSFv3 for the logical router, which is typically an IPv4 address (even though OSPFv3 is for IPv6 addressing), to ensure the Router ID is unique.If you want to apply BFD to OSPFv3, select a BFD Profile you created, or select the default profile, or create a new BFD Profile to apply to all OSPFv3 interfaces belonging to the logical router. Default is None (Disable BFD).Select a Global General Timer profile or create a new one to set SPF throttle timers and to set the minimum interval between arriving instances of the same link-state advertisement (LSA).Select a Global Interface Timer profile or create a new one to set the hello interval, retransmit interval, and other settings.Select a Redistribution Profile or create a new one to redistribute IPv6 static routes, connected routes, IPv6 BGP routes, or the IPv6 default route to OSPFv3.Click OK.Create an OSPFv3 area and specify characteristics based on the type of area.- Select NetworkRoutingLogical Routers and select the logical router.Select OSPFv3Area and Add an Area by Area ID (an IPv4 address).On the Type tab, select an Authentication profile for the area or create a new one.Specify the Type of area:
- Normal—There are no restrictions; the area can carry all types of routes.
- Stub—There is no outlet from the area. To reach a destination outside of the area, traffic must go through an Area Border Router (ABR), which connects to other areas and area 0.
- NSSA (Not So Stubby Area)—Traffic can leave the area directly, but only by using non-OSPF routes.
(Stub and NSSA areas only) Select no-summary to prevent the area from receiving Type 3 Summary LSAs and thereby reduce traffic in the area.(NSSA area only) Select Default information originate to cause OSPFv3 to originate a default route.- Enter a Metric for the default route; range is 1 to 16,777,214; default is 10.
- Select the Metric-Type: Type 1 or Type 2. Type E1 cost is the sum of the external cost plus the internal cost to reach that route. Type E2 is only the external cost of that route. This can be useful when you want to load-balance the same external route, for example.
![]() Select ABR if you want to configure filtering options.Select an Import-list or create a new Access List to filter Type-3 LSAs; applies to paths announced into the specified area as Type-3 summary LSAs.Select an Export-list or create a new Access List to filter Type-3 summary LSAs announced to other areas originated from intra-area paths from the specified area.Select an Inbound Filter List or create a new Prefix List to filter Type-3 summary LSAs coming into the area.If you apply an Import access list and Inbound prefix list, firewall uses an AND operation (both lists must be met).Select an Outbound Filter List or create a new Prefix List to filter Type-3 summary LSAs from the area.If you apply an Export access list and Outbound prefix list, firewall uses an AND operation (both lists must be met).If the Type of area is NSSA and ABR is selected, Add an IPv6 Prefix to summarize a group of external subnets into a single Type-7 LSA, which is then translated to a Type-5 LSA and advertised to the backbone when you select Advertise.Specify the network range that a Type-3 Summary LSA announces to the backbone area if the area contains at least one intra-area network (that is, described with router or network LSA) from this range.
Select ABR if you want to configure filtering options.Select an Import-list or create a new Access List to filter Type-3 LSAs; applies to paths announced into the specified area as Type-3 summary LSAs.Select an Export-list or create a new Access List to filter Type-3 summary LSAs announced to other areas originated from intra-area paths from the specified area.Select an Inbound Filter List or create a new Prefix List to filter Type-3 summary LSAs coming into the area.If you apply an Import access list and Inbound prefix list, firewall uses an AND operation (both lists must be met).Select an Outbound Filter List or create a new Prefix List to filter Type-3 summary LSAs from the area.If you apply an Export access list and Outbound prefix list, firewall uses an AND operation (both lists must be met).If the Type of area is NSSA and ABR is selected, Add an IPv6 Prefix to summarize a group of external subnets into a single Type-7 LSA, which is then translated to a Type-5 LSA and advertised to the backbone when you select Advertise.Specify the network range that a Type-3 Summary LSA announces to the backbone area if the area contains at least one intra-area network (that is, described with router or network LSA) from this range.- Select Range and Add an IPv6 Address/Netmask, which summarizes routes for the area. A Type-3 Summary LSA with routing information that matches the range is announced into the backbone area if the area contains at least one intra-area network from this range.Select Advertise to advertise matching subnets in LSAs to the backbone area. If Advertise is set to No, any matching intra-area prefixes that are present in the area will not be advertised in the backbone area.
![]() Add interfaces to the area.
Add interfaces to the area.- On the Interface tab, Add an Interface by selecting one.Enable the interface.
![]() Select MTU Ignore to ignore maximum transmission unit (MTU) mismatches when trying to establish an adjacency (default is disabled; MTU match checking occurs).Select Passive to prevent sending OSPF Hello packets out this interface and thus prevent the logical router from creating an OSPF adjacency with a neighbor; however, the interface is still included in the link-state database. You can make an interface passive, for example if it connects to a switch, because you don’t want to send Hello packets where there is no router.Keep the Instance ID set to 0 because only one instance of OSPFv3 is allowed.Select the Link Type:
Select MTU Ignore to ignore maximum transmission unit (MTU) mismatches when trying to establish an adjacency (default is disabled; MTU match checking occurs).Select Passive to prevent sending OSPF Hello packets out this interface and thus prevent the logical router from creating an OSPF adjacency with a neighbor; however, the interface is still included in the link-state database. You can make an interface passive, for example if it connects to a switch, because you don’t want to send Hello packets where there is no router.Keep the Instance ID set to 0 because only one instance of OSPFv3 is allowed.Select the Link Type:- Broadcast—All neighbors that are accessible through the interface are discovered automatically by multicasting OSPF Hello messages, such as over an Ethernet interface.
- p2p (point-to-point)—Automatically discover the neighbor.
- p2mp (point-to-multipoint)—Neighbors must be defined manually: Add the Neighbor IPv6 address for all neighbors that are reachable through this interface and the Priority of each neighbor to be elected the designated router (DR) or backup DR; range is 0 to 255; default is 1.
Enter a Priority for the interface—the priority for the router to be elected as a designated router (DR) or backup DR (BDR); range is 0 to 255; default is 1. If zero is configured, the router will not be elected as DR or BDR.Select an OSPFv3 Interface Timer Profile or create a new one to apply to the interface. This OSPFv3 Interface Timer profile overrides the Global Interface Timer applied to OSPFv3.Select an OSPFv3 Interface Authentication profile or create a new one to apply to the interface. This Authentication Profile overrides the Authentication Profile applied to the Area (on the Type tab).By default, the interface will inherit the BFD profile you applied to the logical router for OSPFv3 (Inherit-vr-global-setting). Alternatively, select the default profile, select a BFD Profile you created, create a new one, or select None (Disable BFD) to override the BFD Profile applied at the OSPFv3 level.Enter an OSPFv3 Cost for the interface, which influences route selection; range is 1 to 65,5535; default is 10. During route selection, a route with a lower cumulative cost (the added costs of each interface used) is preferred over a route with a higher cumulative cost.Click OK to save the interface.If the ABR does not have a physical link to the backbone area, configure a virtual link to a neighbor ABR within the same area that has a physical link to the backbone area.The following settings must be defined for area border routers (ABRs) and must be defined within the backbone area (0.0.0.0).- Select Virtual Link.Add a Virtual Link by Name (a maximum of 31 characters).Enable the virtual link.
![]() Select the transit Area where the neighbor ABR that has the physical link to the backbone area is located.Enter the Router ID of the neighbor ABR on the remote end of the virtual link.Select an OSPFv3 Interface Timer Profile or create a new Timer Profile to apply to the virtual link. This OSPFv3 Interface Timer profile overrides the Global Interface Timer applied to OSPFv3 and the OSPFv3 Interface Timer profile applied to the interface.Select an OSPF Interface Authentication profile or create a new Authentication Profile to apply to the virtual link. This Authentication Profile overrides the Authentication Profile applied to the Area (on the Type tab) and the Authentication Profile applied to the interface.Click OK.Click OK to save the area.Configure advanced OSPFv3 features.
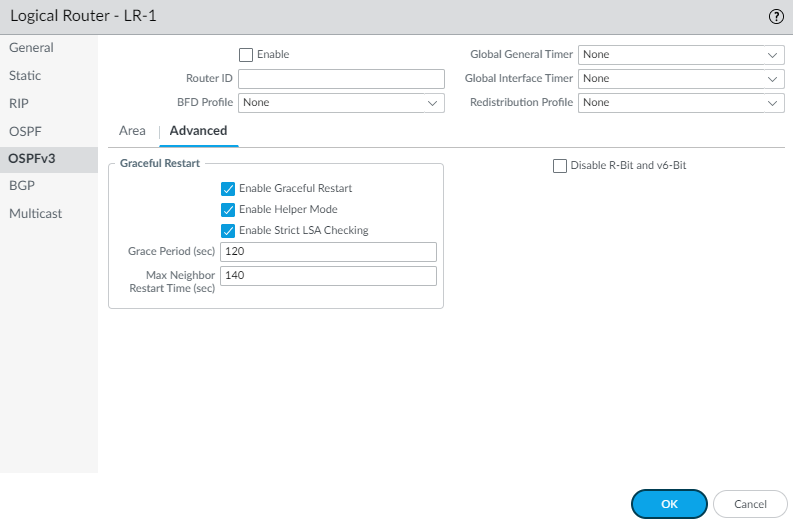
Select the transit Area where the neighbor ABR that has the physical link to the backbone area is located.Enter the Router ID of the neighbor ABR on the remote end of the virtual link.Select an OSPFv3 Interface Timer Profile or create a new Timer Profile to apply to the virtual link. This OSPFv3 Interface Timer profile overrides the Global Interface Timer applied to OSPFv3 and the OSPFv3 Interface Timer profile applied to the interface.Select an OSPF Interface Authentication profile or create a new Authentication Profile to apply to the virtual link. This Authentication Profile overrides the Authentication Profile applied to the Area (on the Type tab) and the Authentication Profile applied to the interface.Click OK.Click OK to save the area.Configure advanced OSPFv3 features.- Select NetworkRoutingLogical Routers and select the logical router.Select OSPFv3Advanced.Enable Graceful Restart to enable Graceful Restart for the logical router. Default is enabled.Enable Helper Mode to enable the logical router to function in Graceful Restart helper mode. Default is enabled.Enable Strict LSA Checking to cause the helper router to stop performing helper mode and to cause the graceful restart process to stop if a link-state advertisement indicates a network topology change. Default is enabled.Enter a Grace Period (sec)—the number of seconds within which the logical router will perform a graceful restart if the firewall goes down or becomes unavailable; range is 5 to 1,800; default is 120.Enter a Max Neighbor Restart Time (sec)—the maximum number of seconds of Grace Period that the logical router accepts from a neighbor when the logical router is in Helper Mode; range is 5 to 1,800; default is 140.Select Disable R-Bit and v6-Bit to clear the R-bit and V6-bit in router LSAs sent from this logical router to indicate that the firewall is not active. When in this state, the firewall participates in OSPFv3 but does not send transit traffic or IPv6 datagrams. In this state, local traffic will still be forwarded to the firewall. This is useful while performing maintenance with a dual-homed network because traffic can be re-routed around the firewall while it can still be reached. See RFC 5340.
![]() Click OK to save advanced settings.Configure intra-area filtering to determine which OSPFv3 routes are placed in the global RIB.You might learn OSPFv3 routes and redistribute them, but not want them in the global RIB; you might want to allow only specific OSPFv3 routes to the global RIB.
Click OK to save advanced settings.Configure intra-area filtering to determine which OSPFv3 routes are placed in the global RIB.You might learn OSPFv3 routes and redistribute them, but not want them in the global RIB; you might want to allow only specific OSPFv3 routes to the global RIB.- Select NetworkRoutingLogical Routers and select a logical router.Select RIB Filter.To filter IPv6 OSPFv3 routes for the global RIB, for OSPFv3 Route-Map, select a Redistribution route map you created or create a new Redistribution Route Map in which the Source Protocol is OSPFv3 and the Destination Protocol is RIB.
![]() Click OK.(Optional) Change the default administrative distances for OSPFv3 Intra Area, OSPFv3 Inter Area, and OSPFv3 External Routes that pertain to the logical router.Commit.View advanced routing information for OSPFv3 and the link-state database (LSDB). The PAN-OS CLI Quick Start lists the commands in the CLI Cheat Sheet: Networking.
Click OK.(Optional) Change the default administrative distances for OSPFv3 Intra Area, OSPFv3 Inter Area, and OSPFv3 External Routes that pertain to the logical router.Commit.View advanced routing information for OSPFv3 and the link-state database (LSDB). The PAN-OS CLI Quick Start lists the commands in the CLI Cheat Sheet: Networking.