SaaS Security
Onboard a Kustomer App to SSPM
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Onboard a Kustomer App to SSPM
Connect a Kustomer instance to SSPM to detect posture risks.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
For SSPM to detect posture risks in your Kustomer instance, you must onboard your
Kustomer instance to SSPM. Through the onboarding process, SSPM connects to a
Kustomer API and, through the API, scans your Kustomer instance for misconfigured
settings. If there are misconfigured settings, SSPM suggests a remediation action
based on best practices.
SSPM gets access to your Kustomer instance through an API access key. During the
onboarding process, SSPM prompts you for the API access key and related information
for your Kustomer instance.
To onboard your Kustomer instance, you complete the following actions:
Collect Information for Accessing Your Kustomer Instance
To access your Kustomer instance, SSPM requires the following information, which
you will specify during the onboarding process.
| Item | Description |
|---|---|
| API Key |
A generated character string that uniquely identifies your
organization to the Kustomer API. SSPM requires this API key
to authenticate to the Kustomer API.
Required permissions: The API key must be generated
by an administrator. The administrator must configure the
key to have the org.permission role.
|
| Region |
The region (US or EU) where your organization deployed the
Kustomer.
|
As you complete the following steps, make note of the values of the items
described in the preceding table. You will need to enter these values during
onboarding to access your Kustomer instance from SSPM.
- Log in to Kustomer as an administrator.
- Open a web browser and go to the Kustomer login page at www.kustomerapp.com/domain. Enter your organization name and Continue.
- Log in using administrator credentials.
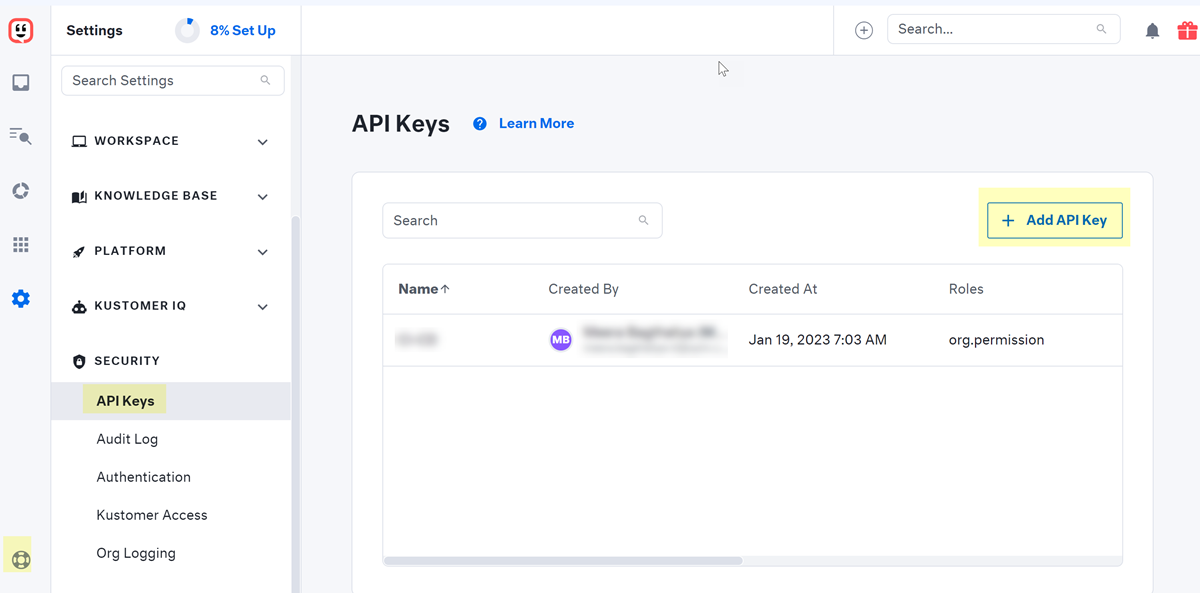
Generate an API key for your organization.- Click the settings icon (gear icon) in the lower-left corner of the window, and select SECURITYAPI Keys.
- + Add API Key.
![]()
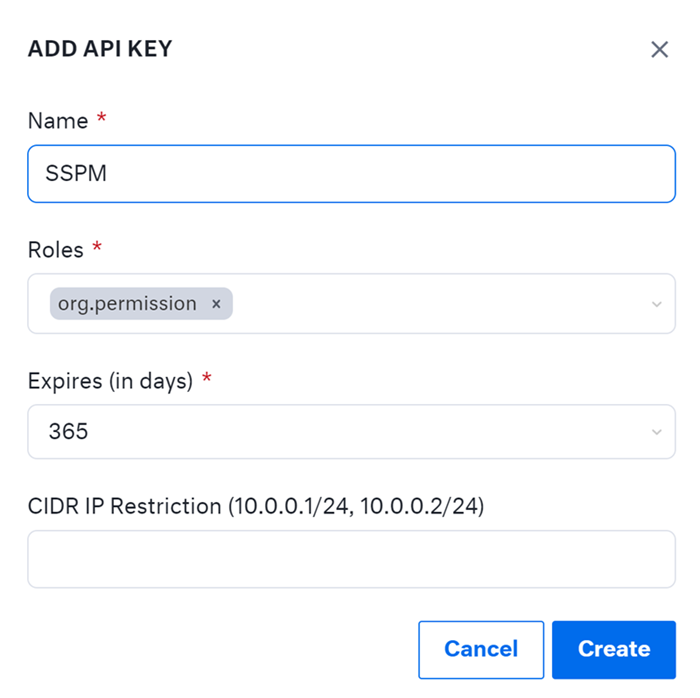
- Fill in the fields of the ADD API KEY dialog.
- Enter a name for the new API key.
- In the Roles field, specify
org.permissionRequired permissions: The key must be configured with the org.permission role.
- Specify an expiration date for the key.
![]()
- Create the key.Kustomer generates and displays your new key.
- Copy the API key and paste it into a text file.Do not continue to the next step unless you have copied the API Key. You must provide this key to SSPM during the onboarding process.
Identify the region (United States or European Union) where your organization instance was deployed. Because API calls are region specific, you must provide this information to SSPM during the onboarding process.Connect SSPM to Your Kustomer Instance
By adding a Kustomer app in SSPM, you enable SSPM to connect to your Kustomer instance. - From the Add Application Page (Posture SecurityApplicationsAdd Application), click the Kustomer tile.Under posture security instances, Add Instance or, if there is already an instance configured, Add New instance.Enter the API Key, and Connect.