SaaS Security
Onboard a MuleSoft App to SSPM
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Onboard a MuleSoft App to SSPM
Connect a MuleSoft instance to SSPM to detect posture risks.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
For SSPM to detect posture risks in your MuleSoft instance, you must onboard your
MuleSoft instance to SSPM. Through the onboarding process, SSPM logs in to MuleSoft
using administrator account credentials. SSPM uses this account to scan your
MuleSoft instance for misconfigured settings. If there are misconfigured settings,
SSPM suggests a remediation action based on best practices.
SSPM gets access to your MuleSoft instance by using Okta SSO credentials that you provide during
the onboarding process. For this reason, your organization must be using Okta as an
identity provider. The Okta account must be configured for multi-factor
authentication (MFA) using one-time passcodes.
To onboard your MuleSoft instance, you complete the following actions:
Collect Information for Accessing Your MuleSoft Instance
To access your MuleSoft instance, SSPM requires the following information, which
you will specify during the onboarding process.
| Item | Description |
|---|---|
| User | An email address of an Okta user account.
Required Permissions: The user must be an
organization owner or organization administrator for the
MuleSoft Anypoint Platform. |
| Password | The password for the Okta user account. |
| Okta Domain | The Okta subdomain for your organization. The subdomain was included in the login URL that Okta assigned to your organization. |
| MFA Secret Key | A key that is used to generate one-time passcodes for multi-factor authentication. |
| Organization Domain Name | The name of the domain in the MuleSoft Anypoint Platform that is associated with your organization. |
As you complete the following steps, make note of the values of the items
described in the preceding table. You will need to enter these values during
onboarding to access your MuleSoft instance from SSPM.
- Identify the Okta user account that SSPM will use to access your MuleSoft instance. The user must be an organization owner or organization administrator for the MuleSoft Anypoint Platform. SSPM needs this administrator access to monitor your MuleSoft instance.Remember which account you will use to access your MuleSoft instance through Okta SSO authentication from SSPM. You will provide the login credentials to SSPM during the onboarding process.To access the administrator account using Okta credentials:Make note of your organization's domain name in the MuleSoft Anypoint PlatformYou can navigate to your organization information from the Access Management page in the MuleSoft Anypoint Platform.
- Log in to the MuleSoft Anypoint Platform.
- Click the menu icon in the top-left corner of the page and select
Access Management.
![]()
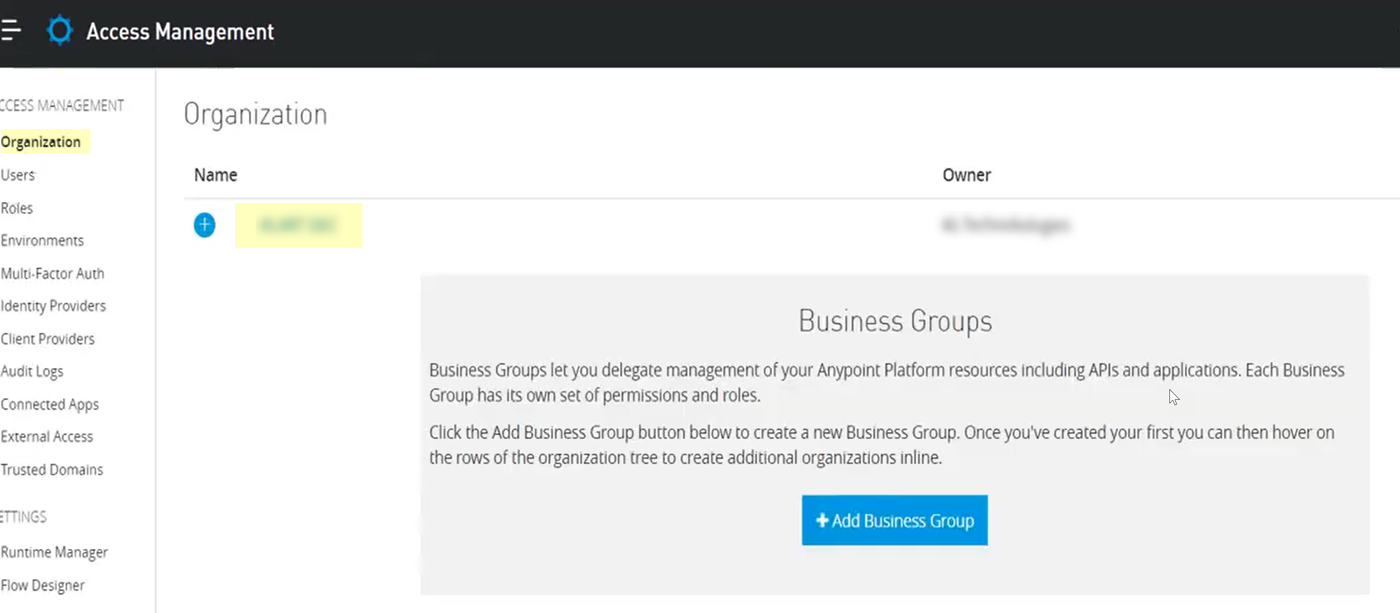
- On the Access Management page, select
Organization and then click on your
organization name.
![]() A dialog opens, displaying information about your organization.
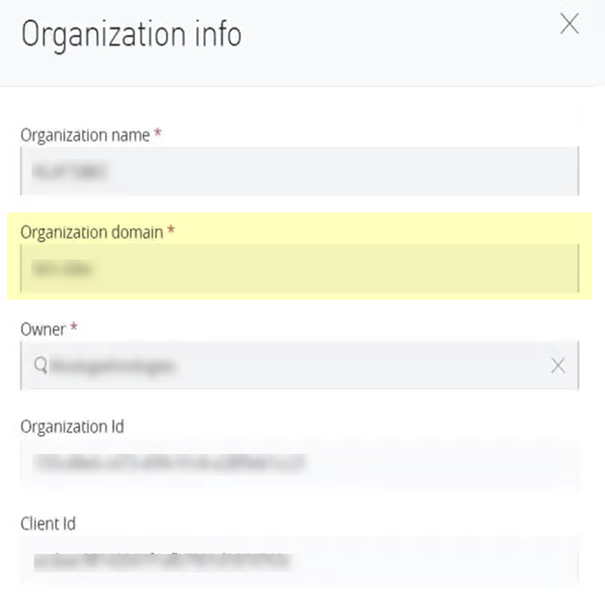
A dialog opens, displaying information about your organization.![]()
- From the Organization info dialog, locate your organization name.
Remember your organization name. You will provide this information to SSPM during the onboarding process.Connect SSPM to Your MuleSoft Instance
By adding a MuleSoft app in SSPM, you enable SSPM to connect to your MuleSoft instance.- From the Add Application page (Posture SecurityApplicationsAdd Application ), click the MuleSoft tile.Under posture security instances, Add Instance or, if there is already an instance configured, Add New instance.Choose the option to Log in with Credentials.Enter the user credentials, Okta domain, MFA secret key, and organization domain name for accessing your MuleSoft instance.Connect.