SaaS Security
View the Health Status of Application Scans
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
View the Health Status of Application Scans
After you onboard a SaaS app to SaaS Security Posture Management, you should periodically verify
that app scans are working.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
After you onboard a SaaS app to SaaS Security Posture Management, SSPM will scan the app at
regular intervals. Depending on the app and the administrator permissions that were
given to SSPM during onboarding, SSPM performs one or more scans. The basic scan,
which is supported for all apps, is the Config Scan. During a Config
Scan, SSPM determines if the app's security settings conform to SSPM's
recommendations for best practices.
Additional scans are supported for only a subset of apps. If a Risky Account
Scan is supported for the app, SSPM scans the app for accounts that
weren’t provisioned by using your organization's identity provider. If a 3rd
Party Plugins Scan is supported, SSPM scans the app for information about
third-party functionality that is hosted in the app.
Because changes in the connected app and temporary conditions might cause a scan to
fail, you should periodically verify that app scans are working. For example,
changes in a service account that was used to onboard the app to SSPM might cause
scans to fail. Some changes that can cause scans to fail include changed login
credentials, changed permissions, and deleted or expired tokens or API keys. Scans
might also fail due to temporary connectivity issues or internal SSPM errors.
SSPM sends a daily digest to app owners, which includes the health status of app
scans. You can also view the overall health status of app scans from the
Applications page. From there, you can navigate to the app's details page to view
the status of individual scans.
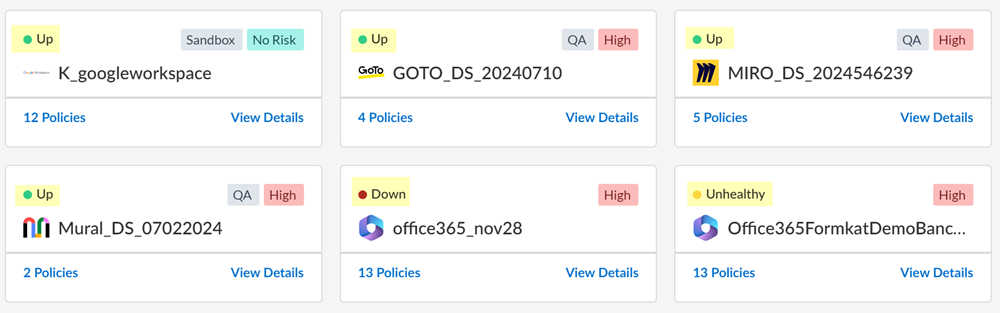
- Log in to Strata Cloud Manager.Navigate to SaaS Security Posture Management.Select Posture SecurityApplications.View the overall scan status for each app that was onboarded to SSPM.The Applications page displays a tile for each app instance that was onboarded to SSPM. The overall scan status for each app appears in the upper-left corner of the tile. If an app supports additional scans beyond the standard Config Scan, this overall status is based on the status of all the scans.
Status Meaning UpThe most recent scan of each supported scan type ran successfully, or the scan is currently running.UnhealthyThe most recent scan of one or some of the supported scan types did not run successfully.DownThe most recent scan for all of the supported scan types did not run successfully.![]() If an app has an overall scan status that is not Up, investigate further.
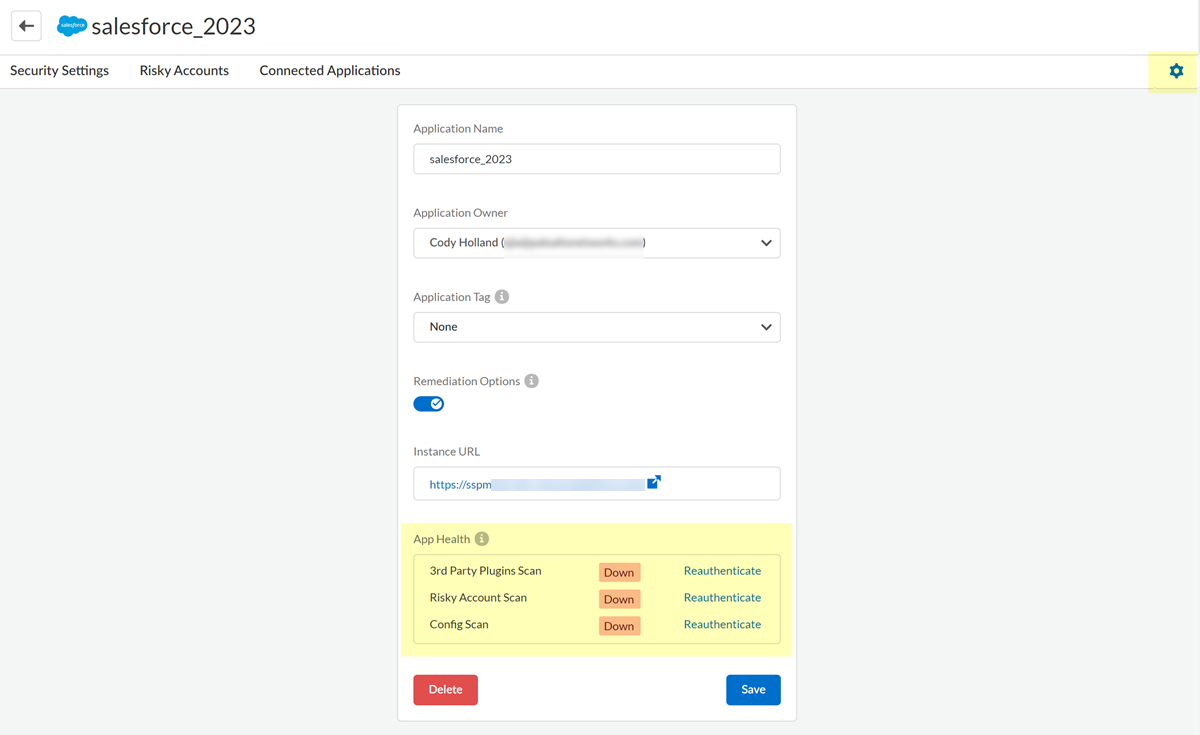
If an app has an overall scan status that is not Up, investigate further.- View Details of the app.On the details page, click the settings icon (gear icon) in the upper-right corner of the page.The settings page shows the scan status for the scans that are supported by the app.
![]() Examine the status of each scan, and take action as needed. The following table describes the meaning of each status value.
Examine the status of each scan, and take action as needed. The following table describes the meaning of each status value.Status Meaning UpThe scan is working correctly. No action is needed.UnhealthyRecent attempts to connect to the SaaS app and complete the scan were unsuccessful, but SSPM will continue trying. If further attempts to connect to the SaaS app fail, SSPM will set the App Health status to Down.Common reasons for connection failures include 401 and 403 HTTP responses from the SaaS app, and temporary connectivity issues. Verify that the credentials that were supplied to SSPM during onboarding are still valid, and that SSPM has the necessary permissions. Continue to check the App Health to see if it returns to the Up status or is changed to the Down status.DownMultiple consecutive attempts to connect to the SaaS app to complete the scan were all unsuccessful. Common reasons for connection failures include 401 and 403 HTTP responses from the SaaS app. If the Config Scan status is Up, but other scans are failing, then the likely cause is that SSPM does not have the necessary permissions for the advanced scan.Reauthenticate to the SaaS app instance to enable the scan. Make sure you supply SSPM with valid credentials and the necessary permissions.ScanningThe scan is currently running.