Network Security
Configure Your Environment to Access an External Dynamic List (Strata Cloud Manager)
Table of Contents
Expand All
|
Collapse All
Network Security Docs
Configure Your Environment to Access an External Dynamic List (Strata Cloud Manager)
Learn about how to configure your environment to access and EDL in Strata Cloud
Manager.
You must establish the connection between your environment and the source that hosts
the external dynamic list before you can Enforce Policy on an External Dynamic
List.
- Find an external dynamic list to use with your configuration.
- Create an external dynamic list and host it on a web server. Enter IP addresses, domains, or URLs in a blank text file. Each list entry must be on a separate line. For example:financialtimes.co.inwww.wallaby.au/joeywww.exyang.com/auto-tutorials/How-to-enter-Data-for-Success.aspxSee the Formatting Guidelines for an External Dynamic List to ensure that your environment doesn't skip list entries. To prevent commit errors and invalid entries, do not prefix http:// or https:// to any of the entries.
- Use an external dynamic list hosted by another source and verify that it follows the Formatting Guidelines for an External Dynamic List.
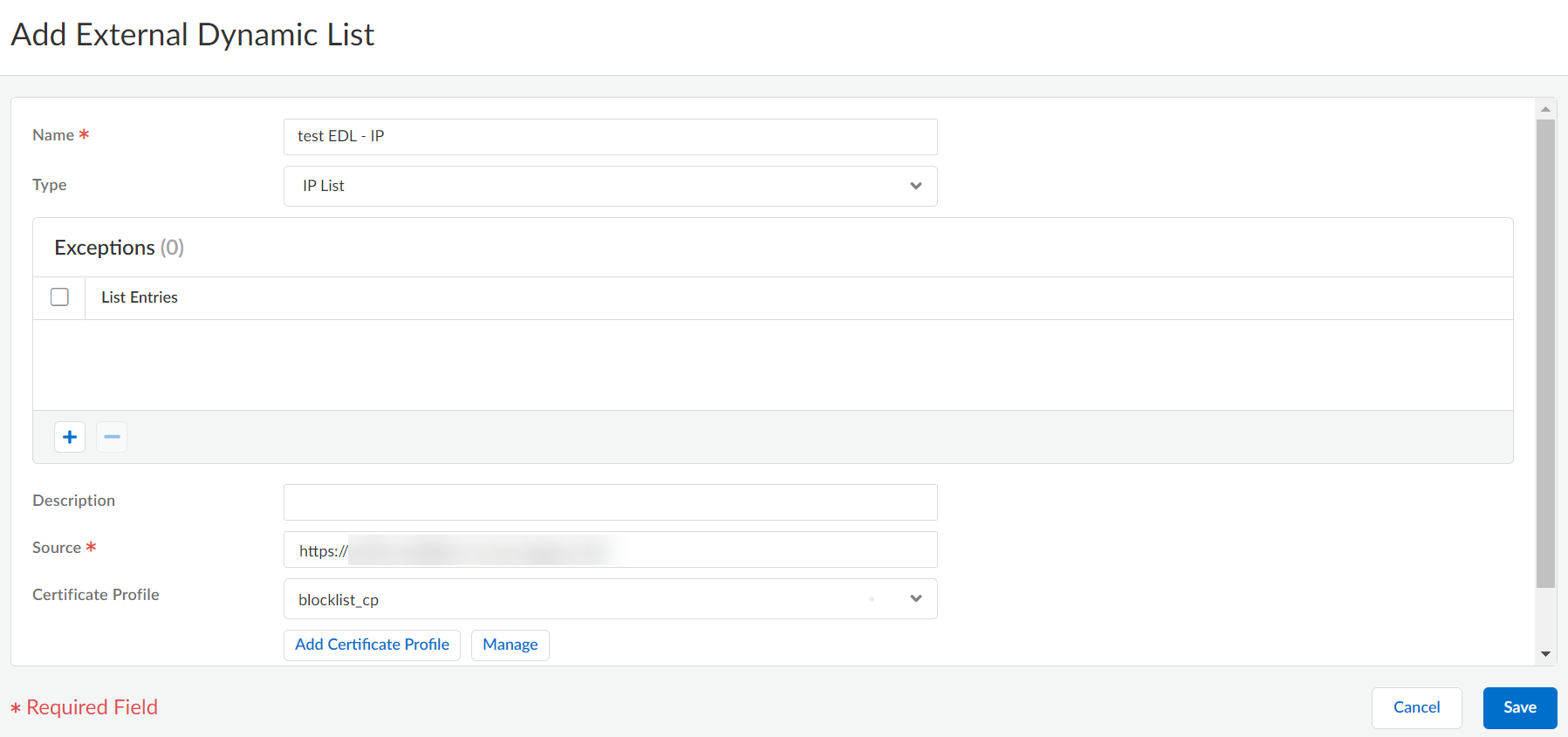
Select ConfigurationNGFW and Prisma AccessObjectsExternal Dynamic Lists.Select Add External Dynamic List and enter a descriptive Name for the list.Select the list Type (for example, URL List).Ensure that the list only includes entries for the list type. See Verify whether entries in the external dynamic list were ignored or skipped.If you using a Domain List, you can optionally enable Automatically expand to include subdomains to also include the subdomains of a specified domain. For example, if your domain list includes paloaltonetworks.com, all lower level components of the domain name (e.g., *.paloaltonetworks.com) will also be included as part of the list. Keep in mind, when this setting is enabled, each domain in a given list requires an additional entry, effectively doubling the number of entries that are consumed.Enter the Source for the list you just created on the web server. The source must include the full path to access the list. For example, https://1.2.3.4/EDL_IP_2015.- If you are creating a Predefined IP external dynamic list, select a Palo Alto Networks malicious IP address feed to use as a source.
- If you are creating a Predefined URL external dynamic list, select panw-auth-portal-exclude-list as a source.
If the list source is secured with SSL (i.e. lists with an HTTPS URL), enable server authentication. Select a Certificate Profile or create a New Certificate Profile for authenticating the server that hosts the list. The certificate profile you select must have root certificate authority (CA) and intermediate CA certificates that match the certificates installed on the server you are authenticating.Maximize the number of external dynamic lists that you can use to enforce policy. Use the same certificate profile to authenticate external dynamic lists from the same source URL. If you assign different certificate profiles to external dynamic lists from the same source URL, your environment counts each list as a unique external dynamic list.Enable client authentication if the list source has an HTTPS URL and requires basic HTTP authentication for list access.- Select Client Authentication.Enter a valid Username to access the list.Enter the Password and Confirm Password.
![]() (Optional) Specify the frequency at which your environment should Check for updates to the list. By default, the list is retrieved once every hour and commits the changes.The interval is relative to the last commit. So, for the five-minute interval, the commit occurs in 5 minutes if the last commit was an hour ago. To retrieve the list immediately, see Retrieve an External Dynamic List from the Web Server.Click Save and Push Config.(Optional) EDLs are shown top to bottom, in order of evaluation. Use the directional controls at the bottom of the page to change the list order. This allows you to or order the lists to make sure the most important EDLs are committed before capacity limits are reached.Enforce Policy on an External Dynamic List.If the server or client authentication fails, your environment ceases to enforce policy based on the last successfully retrieved external dynamic list. Find External Dynamic Lists That Failed Authentication and view the reasons for authentication failure.
(Optional) Specify the frequency at which your environment should Check for updates to the list. By default, the list is retrieved once every hour and commits the changes.The interval is relative to the last commit. So, for the five-minute interval, the commit occurs in 5 minutes if the last commit was an hour ago. To retrieve the list immediately, see Retrieve an External Dynamic List from the Web Server.Click Save and Push Config.(Optional) EDLs are shown top to bottom, in order of evaluation. Use the directional controls at the bottom of the page to change the list order. This allows you to or order the lists to make sure the most important EDLs are committed before capacity limits are reached.Enforce Policy on an External Dynamic List.If the server or client authentication fails, your environment ceases to enforce policy based on the last successfully retrieved external dynamic list. Find External Dynamic Lists That Failed Authentication and view the reasons for authentication failure.