Strata Cloud Manager
On-Demand BPA Report
Table of Contents
Expand All
|
Collapse All
Strata Cloud Manager Docs
On-Demand BPA Report
Provides an overview about On-Demand BPA report.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
One of these:
|
You can now run the Best Practice Assessment (BPA) and Feature Adoption
summary directly from Strata Cloud Manager. Just upload a Tech Support File (TSF).
You can generate the on-demand BPA report for devices that are not sending telemetry
data or onboarded to AIOps for NGFW.
The BPA evaluates your security posture against Palo Alto Networks best practices and
prioritizes improvements for devices. Security best practices prevent known and unknown
threats, reduce the attack surface, and provide visibility into traffic, so you can know
and control which applications, users, and content are on your network. Additionally,
best practices include checks for the Center for Internet Security’s Critical Security
Controls (CSC). See the best practices guidance to bolster security
posture and implement improvements.
Can I Still Generate BPA Reports from the Customer Support Portal?
Transition to the new method of generating Best Practice Assessment
reports.
Before AIOps existed, you went to the Customer Support Portal to access and run the
BPA. Today, the preferred way to generate and download Best Practice
Assessment report for NGFW/Panorama Managed Prisma Access is from AIOps.
After July 17, 2023 you'll no longer be able to access and run the BPA from the
Customer Support Portal.
- Go to the Hub and activate AIOps for NGFW. It’s free. You can activate without Strata Logging Service if you don’t want to onboard devices with telemetry enabled at this time.The best practices dashboard, security alerts, and adoption summary features are not available for devices onboarded without Strata Logging Service or telemetry enabled.Log in to your activated instance AIOps for NGFW. You’ll see the following tabs, even without Strata Logging Service:
- Posture
- Activity
- Settings
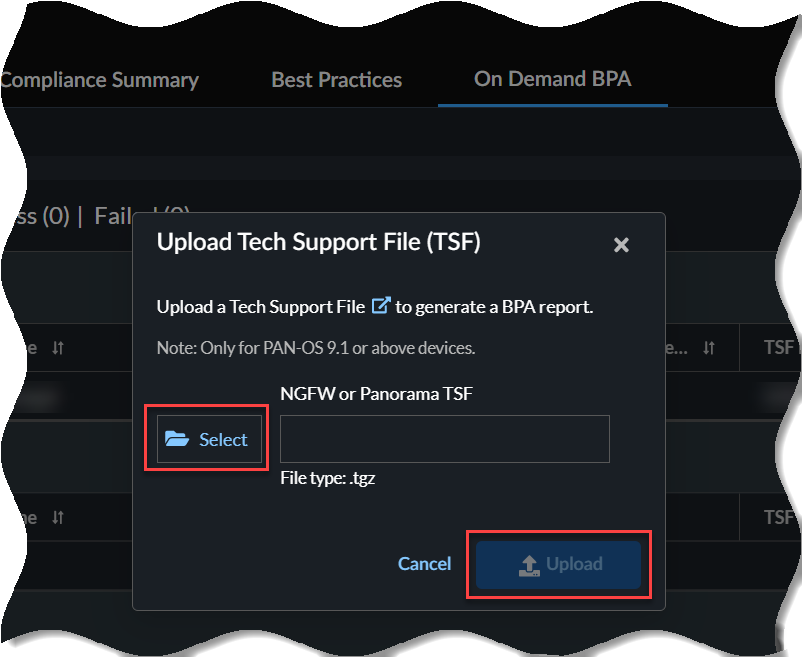
Go to InsightsPOSTUREOn Demand BPA.Generate New BPA Report.Select TSF and Upload TSF file.![]() The upload time is dependent on the size of your .tgz file and your Internet speed. Uploading the file could take a few minutes for larger files. Expand In-Progress to view the status of the TSF files.
The upload time is dependent on the size of your .tgz file and your Internet speed. Uploading the file could take a few minutes for larger files. Expand In-Progress to view the status of the TSF files.- On-demand BPA supports only the Tech Support Files (TSF) in the .tgz file format.
- On-demand BPA supports TSFs from devices with the PAN-OS version 9.1 or above for report generation.
Select View Report below Completed after the TSF is processed to view the generated BPA report from your device.