Prisma Access
Proxy Mode on Remote Networks (Strata Cloud Manager)
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
-
-
- 4.0 & Later
- Prisma Access China
-
-
Proxy Mode on Remote Networks (Strata Cloud Manager)
Learn how to use multicast and unicast IP address to
secure mobile users and devices at Remote Networks with an Explicit
Proxy.
To secure users at remote networks using explicit proxy in Prisma Access (Managed by Strata Cloud Manager),
complete the following steps.
- Configure your explicit proxy setup and onboard the explicit proxy locations you want to add.Onboard your remote networks if you have not done so already.You must enable Prisma Access remote networks in the locations that are supported with explicit proxy.Push Config, being sure that Mobile Users—Remote Workforce and Remote Networks are selected in the Push scope.The push operation retrieves and anycast addresses you need to integrated explicit proxy with the remote network.Get the anycast IP addresses you use for your explicit proxy or remote network deployment.For Remote Network—High Performance deployments, select any one of the retrieved anycast addresses. You cannot use multiple addresses in a single deployment.
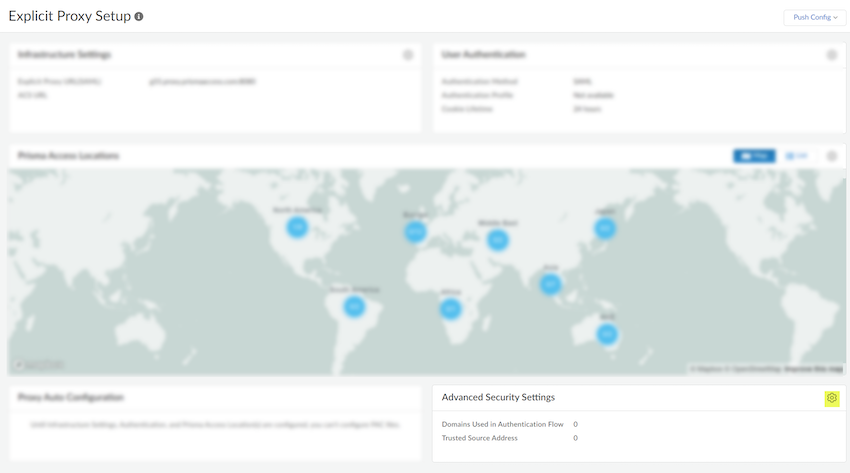
- Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessExplicit ProxyAdvanced Security Settings.
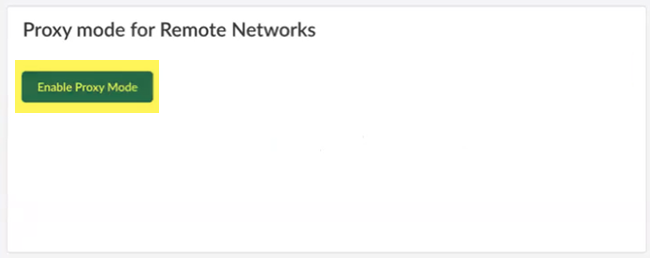
![]() If you want to forward traffic to explicit proxy from your branches through a secure IPSec tunnel, Enable Proxy Mode.
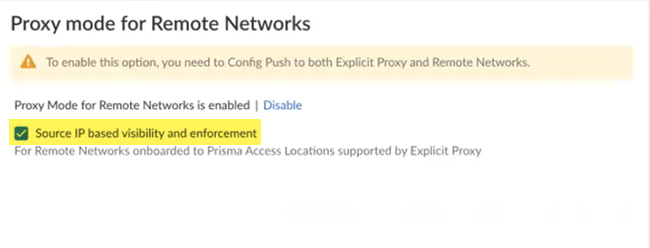
If you want to forward traffic to explicit proxy from your branches through a secure IPSec tunnel, Enable Proxy Mode.![]() To leverage the source IP addresses of the systems in your branch locations that are forwarding traffic to explicit proxy, select Source IP based visibility and enforcement.This functionality has these requirements:
To leverage the source IP addresses of the systems in your branch locations that are forwarding traffic to explicit proxy, select Source IP based visibility and enforcement.This functionality has these requirements:- A minimum Prisma Access dataplane of 10.2.4 is required.
- You must use only remote network locations supported with Explicit Proxy.
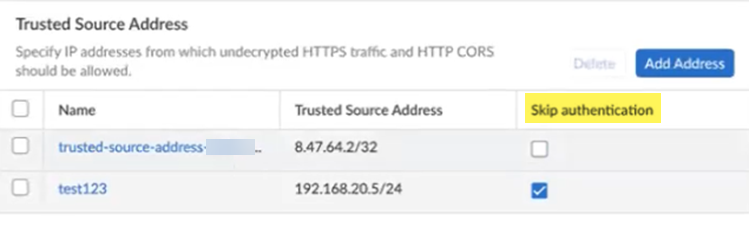
![]() Add a policy to allow traffic bound to anycast and unicast IP on remote networks. If you have enabled Source IP visibility and enforcement, use the Source IP field in Security policies in explicit proxy to secure the traffic. You need additional policies in the remote networks.(Optional) To bypass authentication of any trusted source addresses you entered, specify IP addresses that should have authentication skipped in the Trusted Source Address area and select Skip authentication.You can use Skip authentication with Source IP based visibility and enforcement to Skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma Access Explicit Proxy.You can add either IP addresses or subnets. A maximum of 100,000 IP addresses are supported after expanding the subnets.
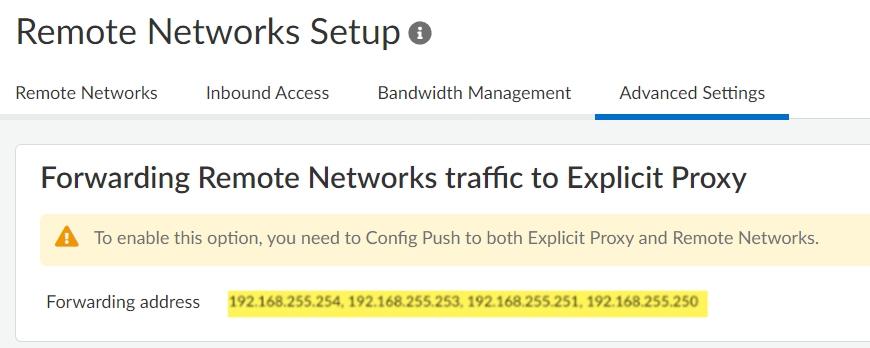
Add a policy to allow traffic bound to anycast and unicast IP on remote networks. If you have enabled Source IP visibility and enforcement, use the Source IP field in Security policies in explicit proxy to secure the traffic. You need additional policies in the remote networks.(Optional) To bypass authentication of any trusted source addresses you entered, specify IP addresses that should have authentication skipped in the Trusted Source Address area and select Skip authentication.You can use Skip authentication with Source IP based visibility and enforcement to Skip authentication of headless systems that can't authenticate, set up security policies, and get visibility of the traffic on Prisma Access Explicit Proxy.You can add either IP addresses or subnets. A maximum of 100,000 IP addresses are supported after expanding the subnets.![]() Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessRemote Networks.Push Config, being sure that Mobile Users—Remote Workforce and Remote Networks are selected in the Push scope.Go to Advanced Settings in your Remote Networks Setup and find the anycast IP addresses used to forward traffic to explicit proxy.
Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessRemote Networks.Push Config, being sure that Mobile Users—Remote Workforce and Remote Networks are selected in the Push scope.Go to Advanced Settings in your Remote Networks Setup and find the anycast IP addresses used to forward traffic to explicit proxy.![]() (Optional, Non-Remote Network—High Performance Deployments only) Find the unicast address to use for your explicit proxy or remote network deployment.Use the unicast IP address in the PAC file only if you want to target a specific remote network to forward traffic to explicit proxy. If you want to use all deployed remote networks to forward traffic to explicit proxy, use the anycast addresses.You cannot use unicast addresses with Remote Network—High Performance networks; however, you can use any one of the anycast addresses.
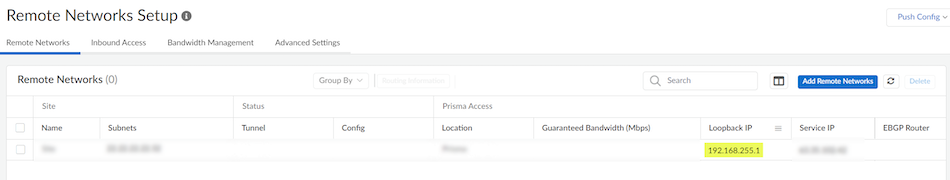
(Optional, Non-Remote Network—High Performance Deployments only) Find the unicast address to use for your explicit proxy or remote network deployment.Use the unicast IP address in the PAC file only if you want to target a specific remote network to forward traffic to explicit proxy. If you want to use all deployed remote networks to forward traffic to explicit proxy, use the anycast addresses.You cannot use unicast addresses with Remote Network—High Performance networks; however, you can use any one of the anycast addresses.- Go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessRemote Networks.Make a note of the Loopback IP address.If you have IPv4 and IPv6 addresses, make a note of the IPv4 address.
![]()