SaaS Security
Onboard a Microsoft Power BI App to SSPM
Table of Contents
Expand All
|
Collapse All
SaaS Security Docs
Onboard a Microsoft Power BI App to SSPM
Connect a Microsoft Power BI instance to SSPM to detect posture risks.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Data Security license:
|
Previously, you could onboard Microsoft Power BI by supplying account
credentials to SSPM. This enabled SSPM to access the account directly or through the
Okta or Microsoft Azure identity providers. Once connected, SSPM would use data
extraction techniques to scan your Microsoft Power BI instance. In April 2026, we
discontinued this earlier connector in favor of a new connector that accesses the
Microsoft Power BI API through a service principal.
For SSPM to detect posture risks in your Microsoft Power BI instance, you must
onboard your Microsoft Power BI instance to SSPM. Through the onboarding process,
SSPM connects to the Power BI Service API and, through this API, scans your
Microsoft Power BI instance at regular intervals.
SSPM gets access to your Microsoft Power BI instance through a service principal,
which represents a Microsoft Entra application that you create. You will configure
this application's permissions to enable SSPM to access only the API scopes that
SSPM requires to complete its scans. When you register this application, Microsoft
Entra creates the associated service principal that SSPM will use to connect to the
Power BI Service API.
The supported Microsoft account plan for SSPM scans is the Microsoft Business Premium
plan.
To access your Microsoft Power BI instance, SSPM requires the following information,
which you will specify during the onboarding process.
| Item | Description |
|---|---|
| Tenant ID | A globally unique identifier (GUID) for your Microsoft Entra tenant. |
| Client ID | SSPM will access a Microsoft API through a Microsoft Entra service principal that represents an application that you create. Microsoft Entra generates the client ID to uniquely identify the application and its associated service principal. |
| Client Secret | SSPM will access a Microsoft API through a Microsoft Entra service principal that represents an application that you create. Microsoft Entra generates the client secret, which SSPM uses to authenticate to the service principal. |
To onboard your Microsoft Power BI instance, you complete the following actions:
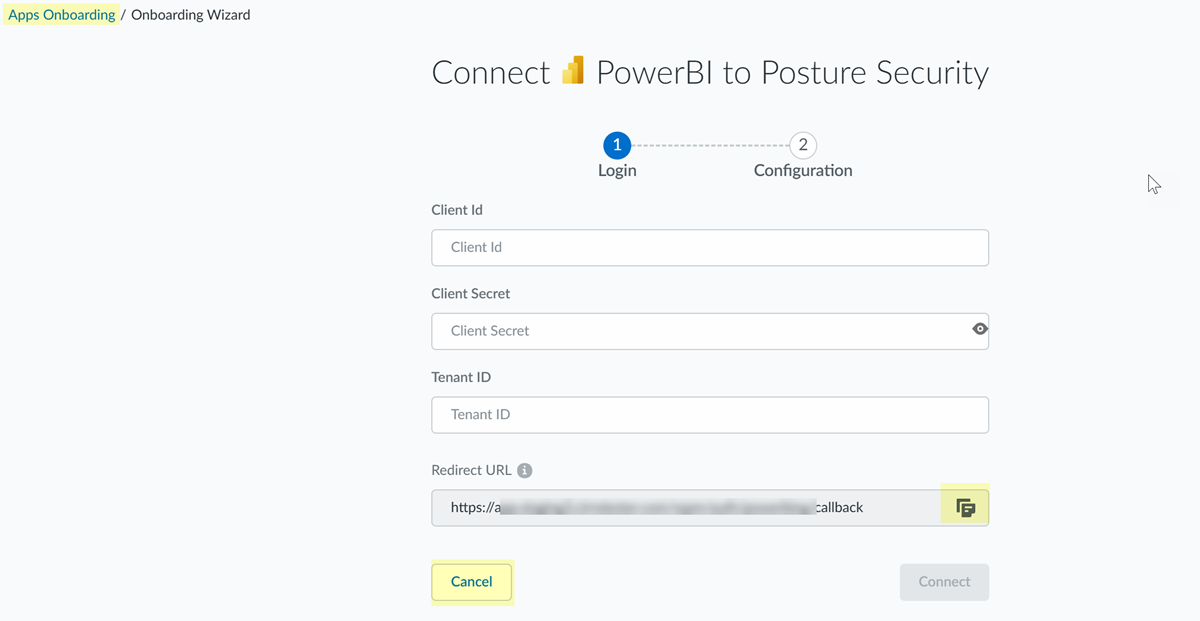
- From SSPM, get the redirect URL that you will need when you configure the Web platform settings for your Microsoft Entra application. To get this information, you will begin the onboarding process in SSPM, but you will not complete the process.
- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecurityPosture SecurityApplicationsAdd Application and click the Power BI tile. tile.On the Posture Security tab, Add New instance.Log in with CredentialsSSPM displays a page for onboarding a Power BI instance. The Redirect URL field displays the redirect URL value.Copy the URL and paste it into a text file.
![]() Do not continue to the next step unless you have copied the redirect URL. You will need to specify this URL later when you are configuring the Web platform settings for your Microsoft Entra application.Because you won't be completing the onboarding process until after you have gathered the necessary configuration information, Cancel the onboarding process and return to the Apps Onboarding page.Open a web browser to the Microsoft Entra admin center and log in as a Global Administrator or a Privileged Role Administrator.To create the Microsoft Entra application and its associated service principal, and to grant access to required API scopes, you must use an account that is assigned to the Global Administrator or Privileged Role Administrator role.Create and register your Microsoft Entra application.
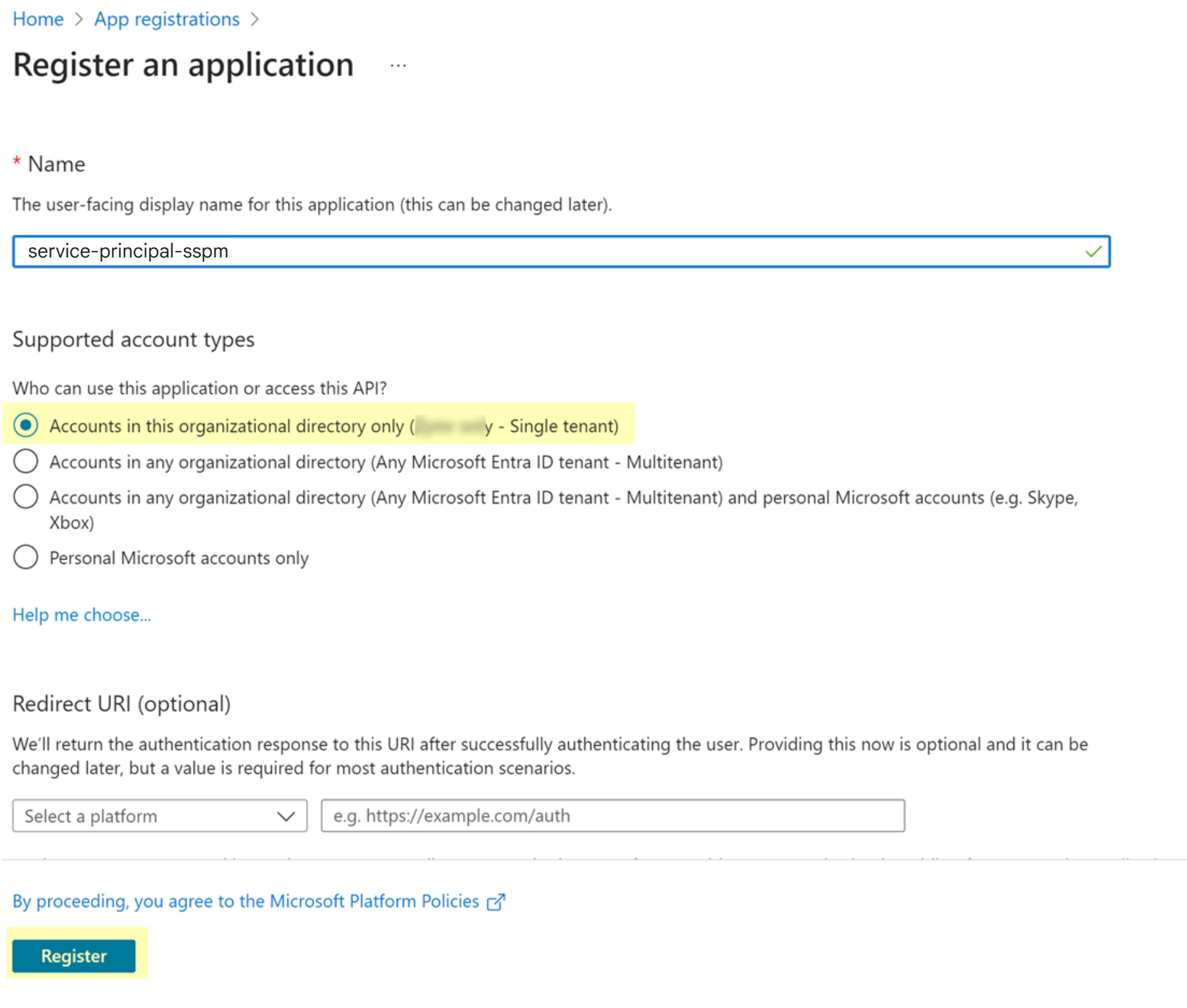
Do not continue to the next step unless you have copied the redirect URL. You will need to specify this URL later when you are configuring the Web platform settings for your Microsoft Entra application.Because you won't be completing the onboarding process until after you have gathered the necessary configuration information, Cancel the onboarding process and return to the Apps Onboarding page.Open a web browser to the Microsoft Entra admin center and log in as a Global Administrator or a Privileged Role Administrator.To create the Microsoft Entra application and its associated service principal, and to grant access to required API scopes, you must use an account that is assigned to the Global Administrator or Privileged Role Administrator role.Create and register your Microsoft Entra application.- From the left navigation pane in the Microsoft Entra admin center, select App registrations.On the App registrations page, select the action to create a New registration.On the Register an Application page, complete the following actions:
- Specify a name for the application.
- Select Accounts in this organizational directory only.
- Register.Microsoft Entra registers your application and displays the details page for your application. Registering the application automatically creates its associated service principal.
![]()
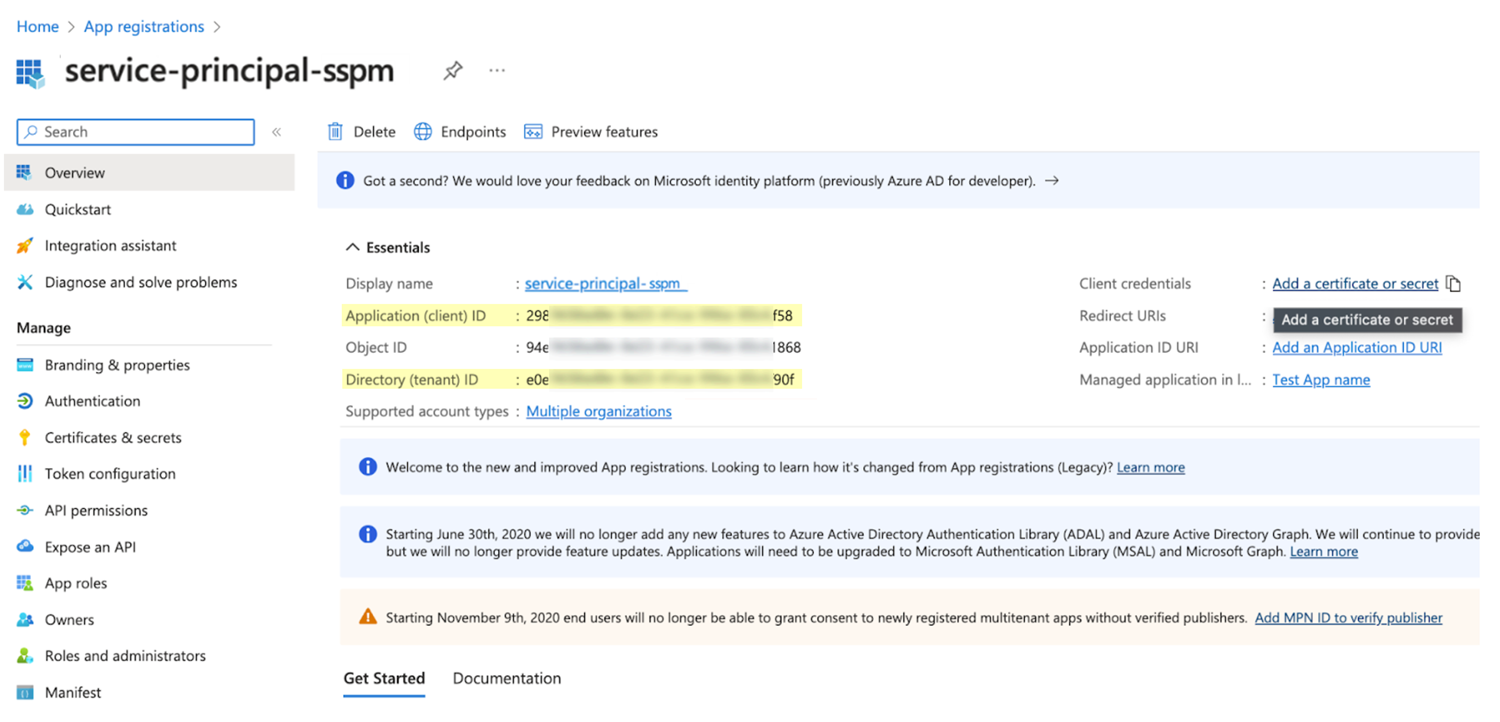
Copy the tenant ID and application credentials (client ID and client secret) for your application.- Copy the tenant ID and client ID.
- From the details page for your application, select Overview.
- From the overview page, copy the client ID from the Application (client) ID field and paste it into a text file.
- From the overview page, copy the tenant ID from the Directory (tenant) ID field and paste it into a text file.
Don’t continue to the next step unless you have copied the client ID and tenant ID. You will provide this information to SSPM during the onboarding process.![]() Create and copy the client secret.
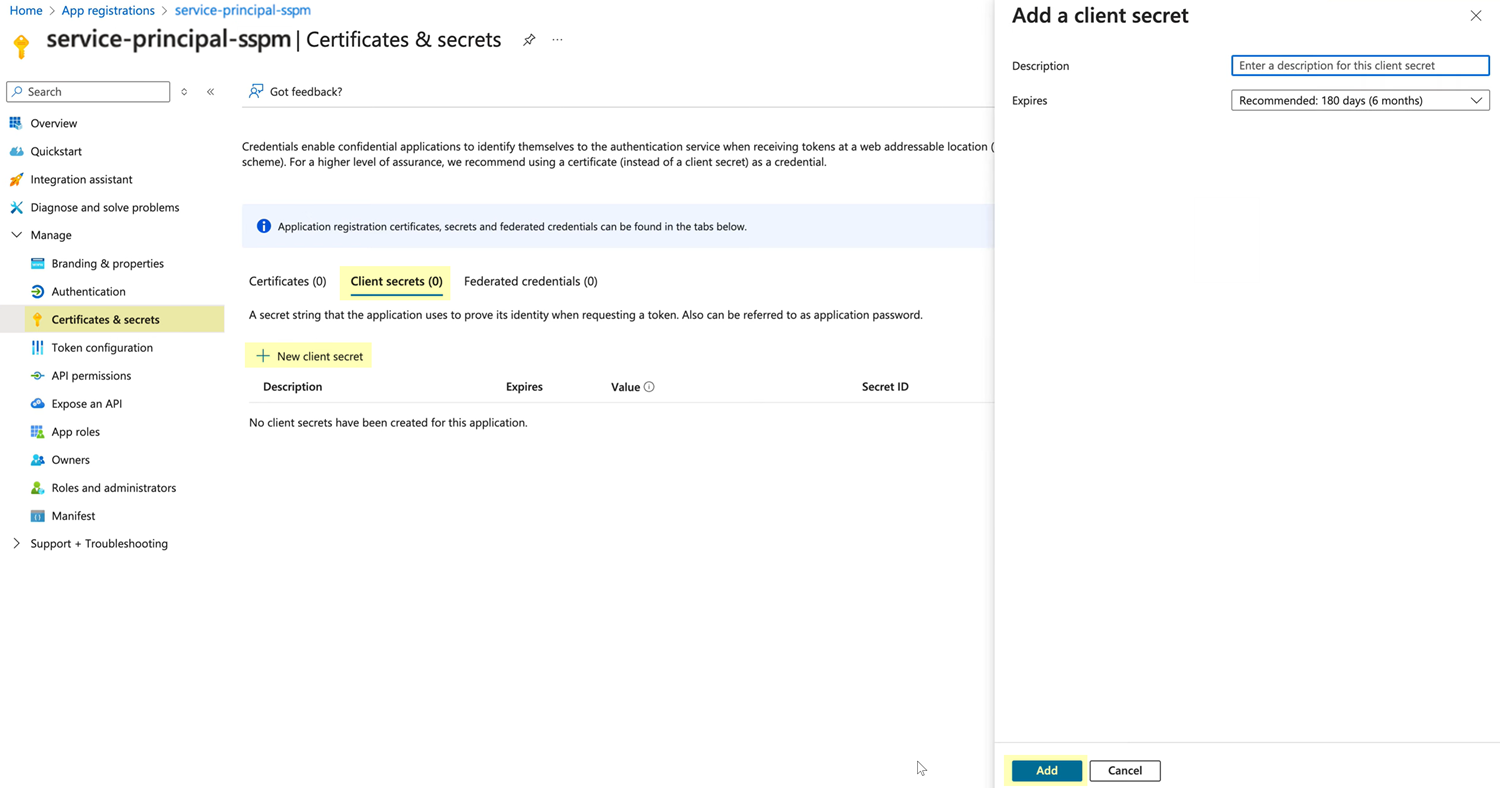
Create and copy the client secret.- From the details page for your application, select Certificates & secretsClient secrets.
- Select New client secret.
- In the Add a client secret flyout dialog, specify an expiration
date for the client secret and Add the
client secret.
![]()
- Copy the Value of the new client secret
and paste it into a text file.Don’t continue to the next step unless you have copied the client secret. You will provide this information to SSPM during the onboarding process.
To ensure a secure handshake between Microsoft Entra ID and SSPM, configure a platform and provide the redirect URL (callback) that will receive the authorization response.- From the details page for your application, select Authentication.In the Platform configurations section, click + Add a platform.In the Configure platforms flyout dialog, select Web.Web is the required platform type for browser-based authorization flows.In the Redirect URIs field, paste the redirect URL that you copied from SSPM.Click Configure to save the platform settings.Configure API permissions for your application.Configure your application to enable access only to the Power BI Service API scopes that SSPM requires. SSPM requires the following permissions:
API Permission Type Permission Microsoft APIs Power BI Service API Delegated permissions Tenant.Read.All To add these permissions, complete the following steps.- From the details page for your application, select API permissions.On the API permissions page, select the action to Add a permission.On the Microsoft APIs tab of the Request API permissions dialog, select Power BI Service.The Power BI Service page prompts you to select the type of permissions your application requires.Select Delegated permissions.Select the following Tenant.Read.All scope and Add permissions.On the API permissions page, verify that the Tenant.Read.All scope was added as a delegated permission.On the API permissions page, select Grant admin consent for your organization.Connect SSPM to your Microsoft Power BI instance.In SSPM, complete the following steps to enable SSPM to connect to your Microsoft Power BI instance.
- Log in to Strata Cloud Manager.Select ConfigurationSaaS SecurityPosture SecurityApplicationsAdd Application and click the Power BI tile.On the Posture Security tab, Add New instance.Log in with Credentials.Enter the application credentials (client ID and client secret) and your tenant ID.Connect.