AI Access Security
Create Custom Policy Rules to Control GenAI App Usage (Strata Cloud Manager)
Table of Contents
Expand All
|
Collapse All
AI Access Security Docs
Create Custom Policy Rules to Control GenAI App Usage (Strata Cloud Manager)
Create custom policy rules in Strata Cloud Manager to control GenAI App usage in
your organization.
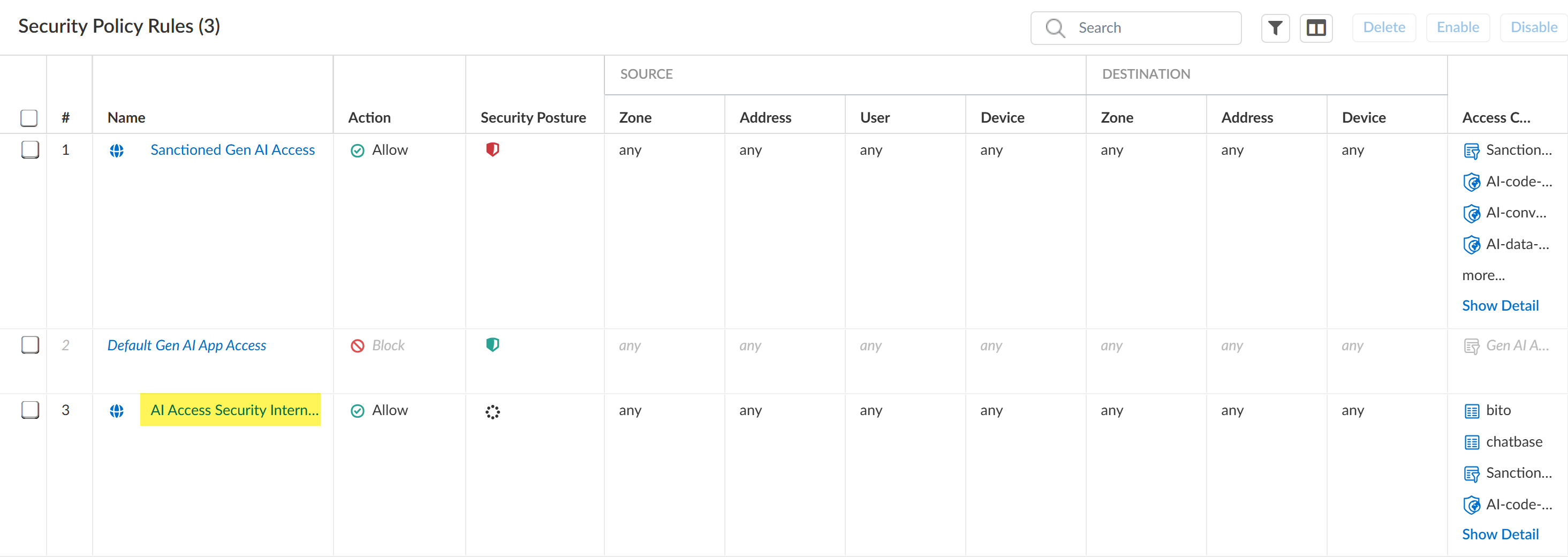
Your Internet Access Security policy rules
are evaluated and enforced ahead of your Security policy rules. In the event a
Internet Access and Security policy rule both apply to the same traffic, the
Internet Access policy rule Action and Enterprise DLP inspection
configuration take precedence over the Security policy rule. After a successful
match to a Internet Access policy rule, no further policy rule evaluation is
performed.
For example, you create Internet Access policy rule and Security policy rule that
apply to User Group A and multiple GenAI apps.
- Internet Access Policy Rule A allows User Group A access to the specified GenAI apps and has an Enterprise DLP Data Profile A associated with the GenAI apps to prevent exfiltration of sensitive data.
- Security Policy Rule B blocks User Group A's access to the same specified GenAI apps.
In this case, when any user in User Group A accesses
a GenAI app specified in the Internet Access and Security policy rules they are
allowed and Enterprise DLP inspection and verdict rendering is performed
because Internet Access Policy Rule A is higher in
the policy rulebase evaluation order.
- Use the AI Access Security Insights dashboard to discover risks posed by GenAI apps.The AI Access Security Insights dashboard provides detailed and comprehensive visibility into GenAI app usage across your organization. You can discover risky GenAI app use cases, individual risky GenAI apps, as well as risky users accessing GenAI apps.If you want to use the existing policies in snippets, perform the initial AI Access Security configuration.On Strata Cloud Manager, This includes creating an Enterprise Data Loss Prevention (E-DLP) data profile to define the sensitive data match criteria, associating the predefined Gen-AI-Best-Practice and Application-Tagging snippets, and the Vulnerability Protection profile used to stop attempts to exploit system flaws or gain unauthorized access to systems.For NGFW, this also includes creating an internal trust zone and an outbound untrusted zone.If you want to build your own custom policies, log in to Strata Cloud Manager.Create a custom Internet Access policy rule.
- In Strata Cloud Manager, even though you can create custom policy rules through Security Policies for GenAI Apps, it's recommended that you use Internet Access policy rules to create policy rules efficiently.
- It's not recommended to have both GenAI and non-GenAI apps in the same policy if the Enterprise Data Loss Prevention (E-DLP) license isn't active.
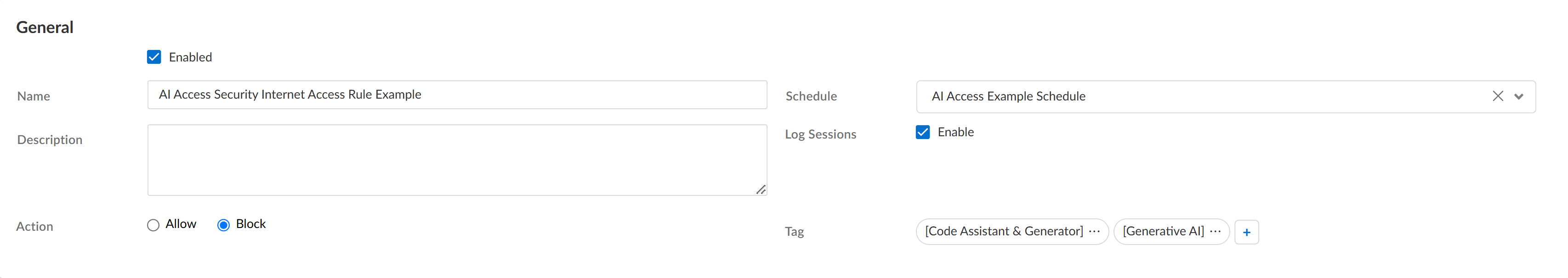
- Select Add RuleInternet Access Rule.Enable the Internet Access policy rule.Enter a descriptive Name.(Optional) Add a Description for the Internet Access policy rule, and add a predefined Tag or create a new one.Configure the Action (Block or Allow).(Optional) Configure a Schedule to specify the times the Internet Access policy rule is active.
![]() In the Match Criteria section, define traffic to enforce based on the traffic Source (where it originates).For example, based on your risk discovery investigation you determine unauthorized users associated with User Group A access a GenAI app sanctioned for use by User Group B. In this case you can create a Internet Access policy rule to block access to the GenAI and add User Group A as the user group Source.In the Web Application section, configure the Application or URL Category to define which GenAI apps or GenAI app URLS you want to block or allow access to.(Allowed GenAI Apps) Only add supported GenAI apps to the list of allowed apps.
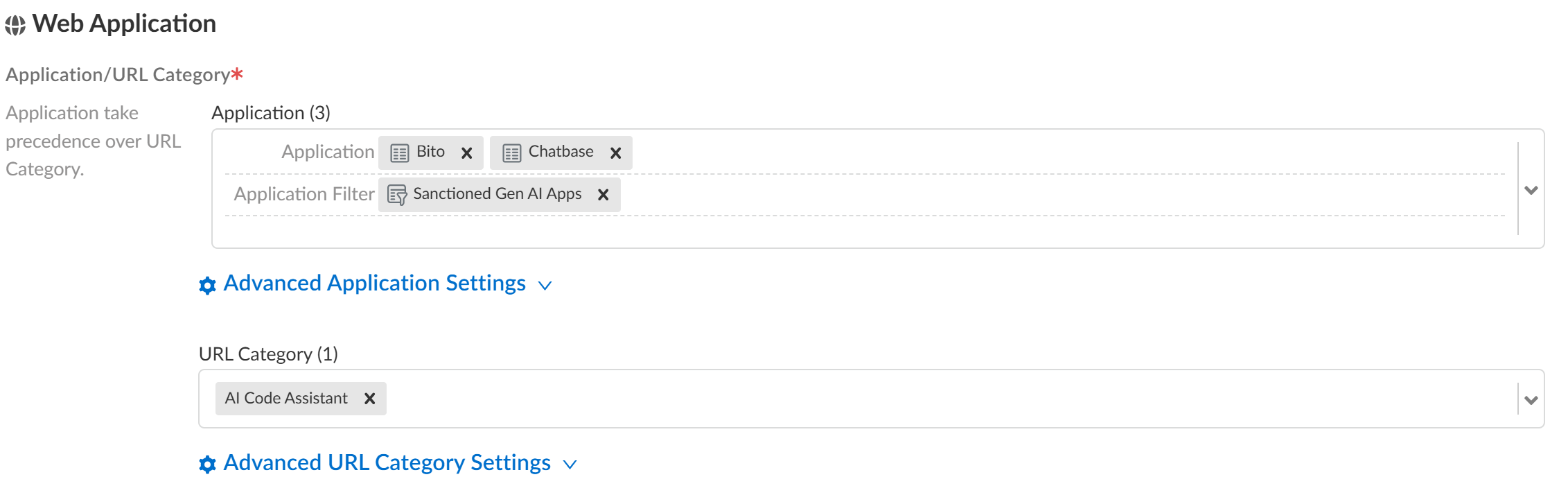
In the Match Criteria section, define traffic to enforce based on the traffic Source (where it originates).For example, based on your risk discovery investigation you determine unauthorized users associated with User Group A access a GenAI app sanctioned for use by User Group B. In this case you can create a Internet Access policy rule to block access to the GenAI and add User Group A as the user group Source.In the Web Application section, configure the Application or URL Category to define which GenAI apps or GenAI app URLS you want to block or allow access to.(Allowed GenAI Apps) Only add supported GenAI apps to the list of allowed apps.- Application—Add one or more GenAI apps.
- Application Group—An application group is a static grouping of individual apps that you create.
- Application Filter—An application filter dynamically groups applications based on app filters you define.For example, you can use a predefined or custom GenAI app filter to dynamically control access to GenAI apps in your organization rather than adding individual GenAI apps or creating an application group that must be updated manually each time a change is required.
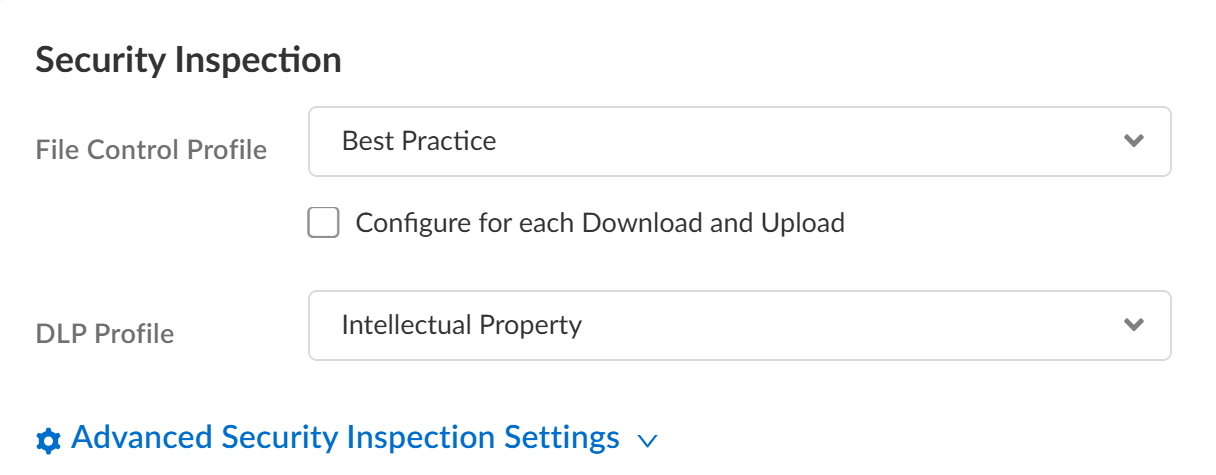
![]() (Allowed GenAI Apps) In the Security Inspection section, select a file blocking and Enterprise DLP profile to prevent exfiltration of sensitive data.
(Allowed GenAI Apps) In the Security Inspection section, select a file blocking and Enterprise DLP profile to prevent exfiltration of sensitive data.- File Control Profile—A File Blocking profile allows you to identify specific file types that you want to block or monitor. You can create a custom File Blocking profile or use the default Best Practice File Blocking profile.
- DLP Profile—An Enterprise DLP data profile allows you to define the match criteria for sensitive data that you want to inspect for and block to prevent exfiltration of sensitive data. You must assign a data profile to generate Sensitive Assets data when discovering risks posed by GenAI apps.
![]()