IoT Security
IoT Security Integration with Prisma Access
Table of Contents
Expand All
|
Collapse All
IoT Security Docs
-
-
- Firewall Deployment Options for IoT Security
- Use a Tap Interface for DHCP Visibility
- Use a Virtual Wire Interface for DHCP Visibility
- Use SNMP Network Discovery to Learn about Devices from Switches
- Use Network Discovery Polling to Discover Devices
- Use ERSPAN to Send Mirrored Traffic through GRE Tunnels
- Use DHCP Server Logs to Increase Device Visibility
- Control Allowed Traffic for Onboarding Devices
- Support Isolated Network Segments
-
IoT Security Integration with Prisma Access
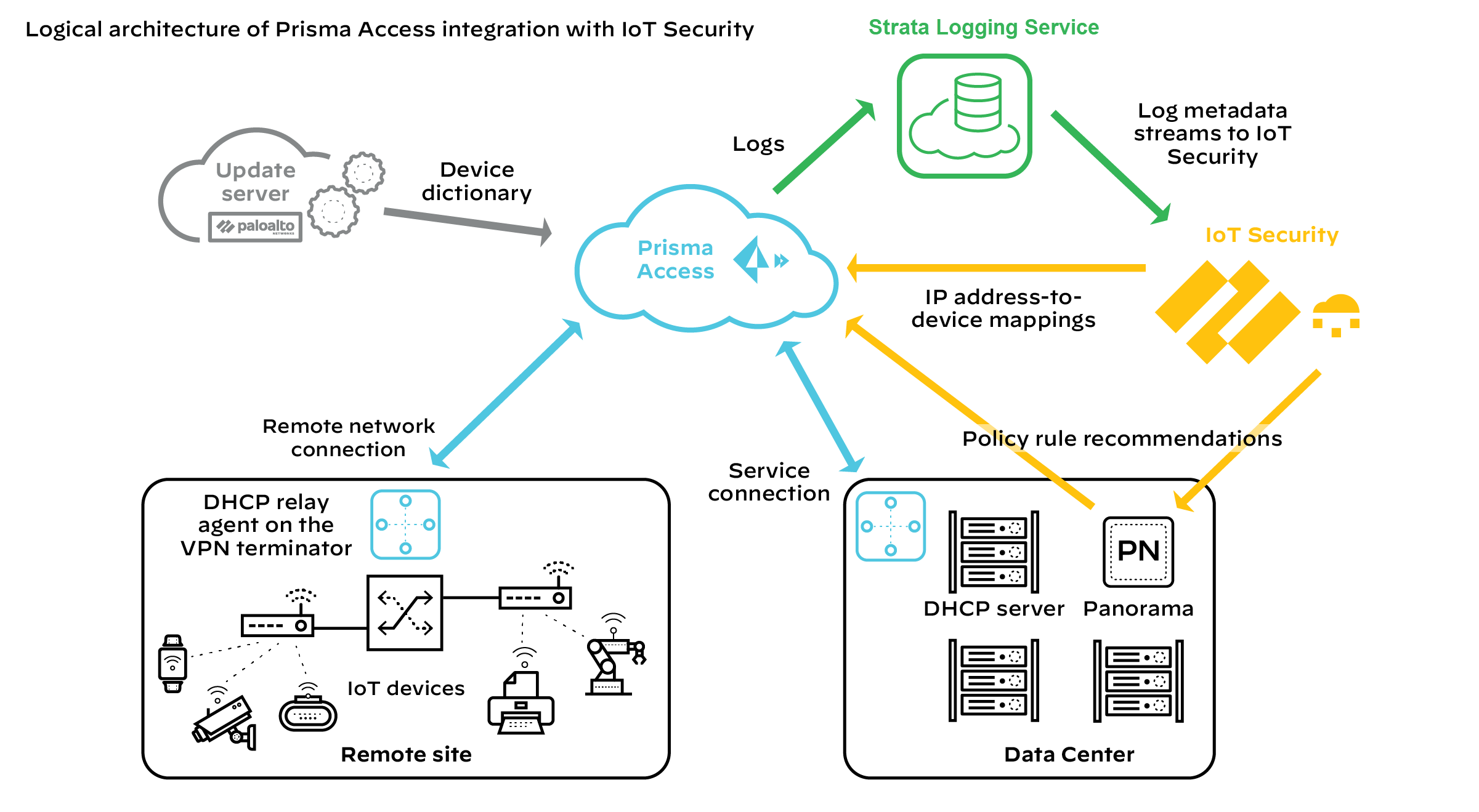
Use IoT Security with Prisma Access to gain visibility and protection of IoT
devices in your remote networks.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
Prisma Access
uses a cloud-based infrastructure that
lets you avoid the challenges of sizing firewalls and computing resource allocation
while securing remote networks and mobile users. To identify IT and IoT devices at your
remote sites, detect IoT device vulnerabilities, and discover threats posed to these
devices and the network, Prisma Access can integrate with IoT Security through
a purchased add-on. In addition, IoT Security also provides Prisma Access with
policy rule recommendations through Panorama to permit only acceptable network behavior
and block anomalous behavior from your IoT devices.
For IoT Security to identify IT and IoT devices, and analyze risk levels and detect
security alerts on IoT devices, it must be able to access network traffic metadata. The
more data it has to work with, the more accurate and faster it can be. Therefore, it's
critical to do two things to collect as much traffic metadata as possible. First, design
your network strategically so that Prisma Access sees all traffic from your remote
sites, including DHCP traffic. Then apply policy rules to as much traffic as you can and
enable logging and log forwarding on these rules to
send traffic metadata to Strata Logging Service.
DHCP traffic is particularly important to IoT Security. It provides IoT Security with
useful data, including a mapping of the IP address to MAC address of each DHCP client,
which is a critical element of the
IP address-to-device mappings used
for device identification. To obtain this data, ensure that a DHCP server is in your
data center or in a similar centralized site and a DHCP relay agent is on the customer
premises equipment (CPE) where the remote network connection terminates at each site.
Each relay agent forwards the DHCP messages it receives from DHCP clients through the
Prisma Access to
the IP address of the DHCP server. On the policy rule allowing DHCP traffic from the
remote sites to the DHCP server, be sure logging and log forwarding are enabled so that
Prisma Access sends DHCP traffic logs to Strata Logging Service. In fact,
if you have not already done so, enable logging and log forwarding on all policy rules.
With log forwarding enabled, Prisma Access sends its logs through Strata Logging Service, which then streams metadata to IoT Security for
analysis.
Prisma Access cannot forward logs to IoT Security for Layer 2 traffic or Layer 3
traffic where both the source and destination are in the same site because such
traffic never reaches it. Without ARP and DHCP traffic metadata in particular,
identifying devices might take IoT Security longer and its confidence might be
lower than it otherwise would be. To counter this, consider deploying SD-WAN ION
devices at remote sites where they can log these types of traffic and forward their
logs to Strata Logging Service for IoT Security to access. By
integrating IoT Security with both Prisma Access
and SD-WAN, IoT Security can gain visibility into traffic that
flows between sites and the Internet as well as traffic that stays within a
site.
After IoT Security has sufficient information to identify devices from their network
behavior, it provides Prisma Access with IP address-to-device mappings and Panorama
with policy recommendations that the
Panorama administrator can import and then push to Prisma Access to enforce policy
on IoT device traffic. In addition, Prisma Access downloads device dictionary files
from the update server. The device dictionary lists various device attributes with which
the Panorama administrator can construct Security policy rules. The combination of IP
address-to-device mappings, policy recommendations, and device dictionary files comprise
the elements of the
Device-ID feature introduced in
PAN-OS 10.0.
Required Panorama Configuration
Check that you have enabled Enhanced Application Logs on
your log forwarding profiles.
- Log in to Panorama and select ObjectsLog Forwarding under the Remote_Network_Device_Group device group or a parent device group.
- Open your log forwarding profiles and make sure that Enable enhanced application logging to Strata Logging Service is selected.
Requirements for using IoT Security with Prisma Access
To use the IoT Security add-on with Prisma Access, check that your deployment meets the
following requirements:
- Prisma Access is running the Prisma Access 2.0-Innovation release or later.
- You have purchased and activated licenses for Strata Logging Service and the IoT Security add-on for Prisma Access.If you are a new Panorama-managed Prisma Access customer as of August 2022, activate new licenses for Prisma Access through the Prisma SASE platform.If you are an existing Panorama-managed Prisma Access customer from before August 2022, your Prisma Access tenant will be transitioned from the hub to the Prisma SASE platform. After the transition, you will no longer see a Prisma Access app title on the hub. However, there will be a button on the hub to navigate to sase.paloaltonetworks.com where you can activate new licenses for Prisma Access through the Prisma SASE platform. Until then, continue to manage your deployment as you’ve been doing.
- The deployment of Prisma Access in a particular region requires that the Strata Logging Service instance and IoT Security application it works with to be in a particular location as well. The following table shows the relationship of Prisma Access deployments in different regions to the locations of Strata Logging Service and IoT Security.
Prisma Access Strata Logging Service IoT Security Americas Canada Canada Canada United States United States United States European Union France France Germany Germany Germany Germany Italy Italy Germany Poland Poland Germany Spain Spain Germany Netherlands Netherlands Germany Switzerland Switzerland Switzerland United Kingdom United Kingdom United Kingdom Asia-Pacific Australia Australia Australia China China Singapore India India Singapore Indonesia Indonesia Singapore Japan Japan Japan Singapore Singapore Singapore - You’re using Panorama 10.0 or later to manage Prisma Access.With a mixed deployment of Prisma Access and on-premises next-generation firewalls, you must use the same Panorama management system to manage them and the same IoT Security tenant for both.
- DHCP is being served from a data center or from some other central site.
- The Prisma Access infrastructure provides routing from remote sites to data center resources, which include the DHCP server.
- A DHCP relay agent on the VPN terminator at all remote sites points to the IP address of the DHCP server in the data center.
- Security policy rules in Prisma Access control traffic to the Internet, the data center, and other remote sites. Logging is enabled on these policies and Prisma Access forwards logging data to Strata Logging Service, which streams it to IoT Security.IoT Security uses Enhanced Application logs (EALs), traffic logs (which include DHCP traffic), threat logs, and wildfire logs. Make sure that your policy rules have logging enabled and are forwarding EALs and traffic logs to Strata Logging Service. Although the last two log types are not required for IoT Security to function, we recommend getting licenses for threat prevention and Wildfire and forwarding their logs as well because they help improve risk assessment and malware detection.
Once these requirements are met, use IoT Security to monitor traffic metadata, identify IoT
devices, detect vulnerabilities, discover threats, and prepare policy rule
recommendations. Import policy rule recommendations from IoT Security into
Panorama or configure Device-ID policy rules directly in Panorama and then push them to
Prisma Access for policy enforcement on IoT device traffic.
