IoT Security
IoT Security Solution
Table of Contents
Expand All
|
Collapse All
IoT Security Docs
-
-
- Firewall Deployment Options for IoT Security
- Use a Tap Interface for DHCP Visibility
- Use a Virtual Wire Interface for DHCP Visibility
- Use SNMP Network Discovery to Learn about Devices from Switches
- Use Network Discovery Polling to Discover Devices
- Use ERSPAN to Send Mirrored Traffic through GRE Tunnels
- Use DHCP Server Logs to Increase Device Visibility
- Control Allowed Traffic for Onboarding Devices
- Support Isolated Network Segments
-
IoT Security Solution
Learn about the structure and setup of the IoT Security solution and the technical
product information available about IoT Security.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
IoT Security is an on-demand cloud subscription
service designed to discover and protect the growing number of connected
“things” on your network. Unlike IT devices such as laptop computers
that perform a wide variety of tasks, IoT devices tend to be purpose-built
with a narrowly defined set of functions. As a result, IoT devices
generate unique, identifiable patterns of network behavior. Using
machine learning and AI, IoT Security recognizes these behaviors
and identifies every device on the network, creating a rich, context-aware
inventory that’s dynamically maintained and always up to date.
After IoT Security identifies a device and establishes a baseline
of its normal network activities, it continues monitoring its network activity
so it can detect any unusual behavior indicative of an attack or
breach. If it detects such behavior, IoT Security notifies administrators
through security alerts in the portal and, depending on each administrator’s
notification settings, through email and SMS notifications.
IoT Security also uses those behaviors and device identities
to automatically generate security policy rule recommendations that
allow IoT devices to continue doing normal network activities and
block them from doing anything unusual. Panorama or next-generation
firewalls can then import these policy rules and enforce them.
For Panorama-managed firewalls that have an IoT Security
subscription requiring Strata Logging Service – Panorama can only import
policy rule recommendations if it was used to onboard its managed firewalls
to Strata Logging Service.
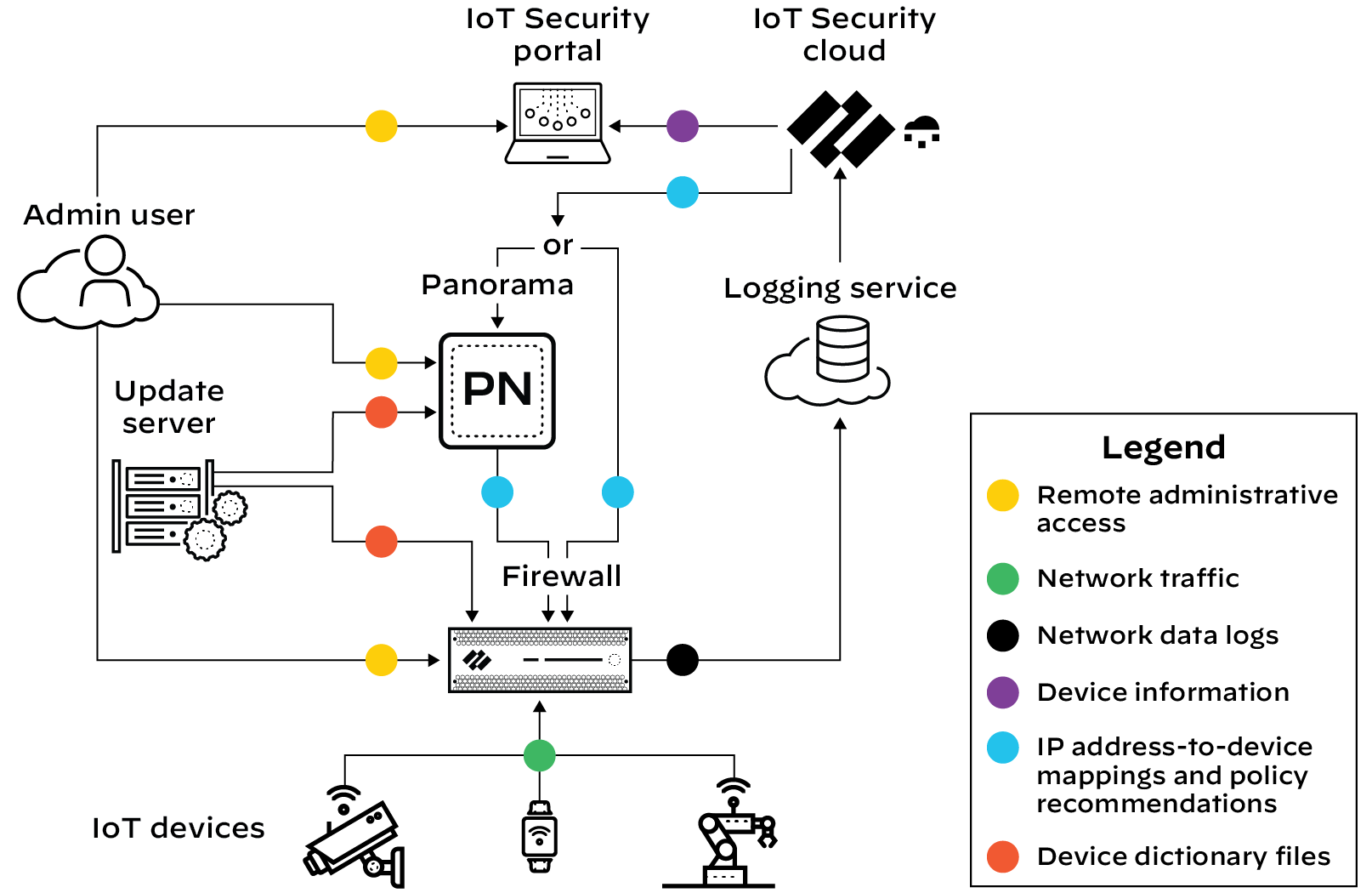
The firewall collects metadata from the network traffic of IoT
devices, generates Enhanced Application logs (EALs), and forwards
them to the logging service. The IoT Security cloud then extracts
metadata from these logs for analysis and employs AI and machine-learning
algorithms to detect and identify IoT devices using its patented
three-tier deep-learning engine:
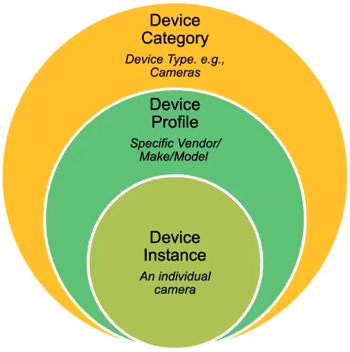
Tier 1: Device category—IoT Security first identifies
the category to which an IoT device belongs. For example, it might
identify network behaviors common to all security cameras.
Tier 2: Device profile—IoT Security next constructs a
profile of the device, learning its vendor, make, and model. For
example, it might discover that the camera behaves in ways that
uniquely identify it, such as checking a particular server for software
updates for example.
Tier 3: Device instance—IoT Security continues its analysis
until it discerns behaviors unique to a specific instance of the
identified security camera.
IoT Security looks at over 200 parameters in network traffic
metadata, including DHCP option 55 parameter lists, HTTP user agent
IDs, protocols, protocol headers, and a host of others. It matches
the network traffic patterns of new devices with those of previously
identified devices to identify the same types or similar types of
devices, even those it is encountering for the first time.
Depending on various factors such as how much network traffic
IoT devices generate and how varied their behavior patterns are,
IoT Security typically identifies most IoT devices with a high level
of confidence during the first day it starts accessing metadata
from the logging service. After that, IoT Security continues to
increase the number of confidently identified devices until it identifies
all or nearly all of them. During this time, you can log in to the
IoT Security portal to check that the device inventory is being
populated and monitor its progress.
A confidence score indicates the level of confidence IoT Security has in its identification
of a device. IoT Security has three confidence levels based on calculated
confidence scores: high (90-100%), medium (70-89%), and low (0-69%).
In addition to using machine learning (ML) to observe network
traffic and extract various attributes to identify devices and detect
anomalous behaviors, IoT Security employs an ML-based model to check
for SQL content injected into HTTP URLs, a technique commonly used
in SQL vulnerability exploits. By using an ML-based model instead
of a model based on rules, IoT Security can find certain patterns
of injected SQL content even without specific signatures.
The architectural components that constitute the IoT Security solution are introduced
here. Learn about the various components, how they work together, and how to set them up.
Also learn about all the educational resources available for IoT Security.
