Network Security
Quantum-Safe Security App
Table of Contents
Expand All
|
Collapse All
Network Security Docs
Quantum-Safe Security App
The Quantum-Safe Security application eases your organization's PQC transition
through a live cryptographic inventory, continuous risk assessment, and risk remediation
guidance.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
The Quantum-Safe Security app helps you plan, prepare for, and manage the migration to
post-quantum cryptography (PQC). It provides comprehensive visibility into your
cryptographic posture through a real-time inventory of your applications, user devices,
infrastructure, and IoT devices and their cryptographic materials, including protocols,
keys, algorithms, and certificates. By analyzing telemetry from SSL/TLS sessions, SSH
sessions, and VPN tunnels, the app identifies where and how cryptography is used,
determines asset vulnerabilities, and evaluates quantum readiness. A central dashboard provides an overview of cryptographic
risk and quantum readiness across all assets. Actionable insights and remediation
guidance help you mitigate data exposure and Harvest Now, Decrypt Later risks and
prepare assets for migration.
To get started, review app prerequisites and follow the steps in Enable Comprehensive Cryptographic
Visibility.
To launch the application, log in to Strata Cloud Manager, and then select InsightsQuantum-Safe Security. You can also select Quantum Resilience from the
Strata Visions switcher.
How It Works
Your Next-Generation Firewalls (NGFW) and Prisma Access tenants act as distributed,
agentless sensors across your network. They inspect traffic, extract relevant
cryptographic attributes and context, and forward this data to the Strata Logging Service. The primary
sources of this data are SSL/TLS and SSH decryption logs, Traffic logs, and Tunnel
Inspection logs. The Quantum-Safe Security app continuously processes telemetry
captured by your devices to discover assets, identify
cryptographic dependencies, and assess quantum readiness and risk. This data enables
the app to build a cryptographic inventory and an overview dashboard.
Components
The Quantum-Safe Security app consists of two interactive components that help you
monitor and manage your cryptographic posture and PQC
migration.
Overview
This dashboard summarizes the cryptographic health of your network for the
selected time range, enabling you to assess and monitor quantum readiness and
resilience at a glance. It provides a consolidated view of discovered assets and the
volume of data in transit, segmented by cryptographic risk and quantum readiness
status (quantum-ready or quantum-safe).
- Central Pie Chart—Shows the breakdown of the total volume of data in motion by risk category. You can also View Details, such as the top algorithms and protocols contributing to that risk.
- Left Arc— Shows the total number of assets detected in the specified time range and the breakdown by asset type.
- Right Arc—Shows the number of quantum-ready and quantum-safe assets and the number of recommendations targeted to moving an asset to a quantum-safe or quantum-ready state. The right arc provides a shortcut to the specific recommendations in the inventory's recommendation panel.
- Weekly Impact Summary—Tracks progress toward quantum readiness by displaying week-over-week trends for key metrics, such as the number of quantum-ready browsers, sessions using deprecated algorithms, and cipher translation usage. For some metrics, the summary shows the percent change. For example, a 5% week-over-week decrease in sessions using deprecated algorithms may indicate reduced data exposure risk.
Inventory
The inventory is your dynamic cryptographic bill of materials (CBOM). It catalogs
applications, user devices, infrastructure, and IoT devices across your network
alongside their cryptographic dependencies. It shows each asset's cryptographic
risk, quantum readiness, and identifying details. The app enriches assets with
context such as hardware models, operating system, cryptographic library versions,
and browser versions. Additionally, the Show Recommendations
panel provides targeted recommendations (for example, upgrade pathways) for specific
asset types, risks, and readiness. Each recommendation shows the number of assets
impacted by current cryptography use and that the fix targets.
How To Use the Overview
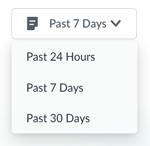
Set the Time Range
Adjust the time range to identify newly discovered assets or analyze trends and
your cryptographic posture at different time periods. Available options include:
Past 24 Hours, Past 7 Days, or
Past 30 Days.
Filter the Overview by Asset Type
By default, the dashboard displays data for all assets. To view data, insights,
and recommendations tailored to a specific asset type, select
Applications, User Devices,
Infrastructure, or IoT
Devices from the left arc.
Investigate Cryptographic Risk
In the All Assets view, click View
Details on a specific risk category. The pie chart updates to
reveal deeper insights, such as the number of impacted sessions, certificates,
and tunnels or the top contributors to that risk. For example, you can learn the
number of assets impacted by the use of the top deprecated algorithm. If you
select a different asset type, then the cryptographic risk details and other
data focus only on the asset type you selected.
If you select a specific asset type (for example, IoT
Devices) and there is only one risk category represented, the dashboard shows
details such as number of tunnels detected.
Access Recommendations
In the right arc, under the Quantum Ready or Quantum Safe headers, select a
recommendation category (for example, Hardware
Recommendations). This directs you to the specific
recommendations in the recommendations panel in the inventory.
How To Use the Inventory
Set the
Time Range
Adjust the time range of the inventory to identify
newly discovered assets or analyze trends and your cryptographic posture at
different time periods. Available options include: Past 24
Hours, Past 7 Days, or Past 30
Days.
Filter Assets in the Inventory
Filter the inventory for a
specific asset type by Type (for example, SaaS
application), Quantum Readiness, Cryptography
Risk, Cipher Translation, or a
combination of filters. Available filters differ between asset types. For
example, to identify web applications ready for migration, apply both the
Type (select Internet) and
Quantum Readiness (select
Ready) filters when in the
Applications tab.
- To apply filters:
- Click Add Filter.
- Select a filter, such as Quantum Readiness.
- Select filter values, such as Ready or Not Ready.
- (Optional) Add more filters.
- To clear filters, click Reset Filters.
- To find assets more readily, you can use the Search.
Customize your view and navigate
between pages of the inventory using the following pagination and navigation
settings:
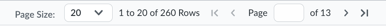
- Assets per Page—To adjust the number of assets displayed on a single page of the inventory, select a Page Size. Available options are: 10, 20, 50, 100.
- Navigation—To jump to a specific page in the inventory, enter a Page number in the given range or use the directional arrows.
Drill-down into Individual Assets
To open a detailed view of a
specific asset, click its Asset Name. This provides a
more digestible, easy-to-read layout of the asset's information compared to the
main inventory view.
Explore
Recommendations
- To view recommendations, click Show Recommendations, and then click Quantum Ready or Quantum Safe. Recommendations targeted to the goals of quantum readiness or quantum safety display.
- To close the recommendations panel, click Hide Recommendations.
- Search within recommendations using terms like "hardware" or "software".
Key Concepts
Cryptographic Risk Classification
Quantum-Safe Security performs a risk assessment for each asset it discovers. Based
on cryptography observed in sessions, tunnels, and certificates, the app classifies
each asset into one of three Cryptography Risk categories:
- Data Exposure Risk—Identifies sessions using algorithms or protocols deprecated by the National Institute of Standards and Technology (NIST).
- Harvest Now, Decrypt Later (HNDL) Risk—Identifies assets using classical algorithms that are currently secure but vulnerable to a cryptographically relevant quantum computer (CRQC). Attackers could steal data encrypted by these algorithms today to decrypt in the future. For more information on this threat, see The Quantum Computing Threat and Harvest Now, Decrypt Later (HNDL): The Quantum-Era Threat.
- Quantum-Secure—Identifies assets already using NIST-approved PQC algorithms or hybrid PQC algorithms.
The Quantum-Safe Security app continuously monitors cryptographic usage across the
enterprise to ensure the accuracy of cryptographic risk and help you track the
effectiveness of mitigation actions.
The following table lists the specific data sources and cryptographic
attributes used to evaluate cryptographic risk exposure. This list is not
exhaustive.
| Data Source | Metadata Inspected |
|---|---|
| Sessions |
|
| Certificates |
|
| Tunnels |
|
Quantum Readiness
Quantum Readiness reflects the capability of an asset to support PQC, which depends
on its specific hardware and software attributes. An asset is Quantum Ready when its
underlying hardware or software supports quantum-resistant algorithms, even if they
are not in use. An asset is Quantum Safe if its hardware or software actively uses
PQC or hybrid PQC that complies with NIST or other PQC standards.
While Quantum Readiness is a fixed attribute—an asset either has PQC capability or
not—your configuration can determine what state the asset is in. For example,
enabling PQC for SSL/TLS sessions ensures that quantum-ready assets negotiate
quantum-safe sessions. The app provides recommendations for modernizing assets that
are Not Ready and migrating Ready assets to PQC.
When asset context is lacking, the app cannot provide a
definitive status of Quantum Readiness. In this case, if a single PQC key exchange
is observed for the asset over the selected time period, the app infers that the
asset is Quantum Ready.
Cipher Translation Proxy
To secure legacy systems or IoT devices that cannot be upgraded, the app recommends
that you enable cipher translation. Cipher translation is
the process of intercepting network traffic secured with classical encryption (like
RSA or ECDHE) and re-encrypting it in real-time using quantum-safe algorithms (like
ML-KEM) at the network edge. Hybrid post-quantum (PQ) key exchange enables this
process.
NGFWs running PAN-OS 12.1 or later versions act as the inline proxy, upgrading the
security of sessions. Communications between the parties is secure as long as at
least one of the two mechanisms—classical or PQC—remains uncompromised. Cipher
translation protects against the Harvest Now, Decrypt Later threat, does not require
upgrades or other changes to the endpoint, and facilitates a gradual transition to
PQC without disrupting business operations.
