SD-WAN Features
Table of Contents
Expand All
|
Collapse All
Next-Generation Firewall Docs
-
-
-
-
-
-
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 11.0 (EoL)
- PAN-OS 10.2
- PAN-OS 10.1
- PAN-OS 10.0 (EoL)
- PAN-OS 9.1 (EoL)
- PAN-OS 9.0 (EoL)
- PAN-OS 8.1 (EoL)
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 10.2
- PAN-OS 10.1
SD-WAN Features
What new SD-WAN features are in PAN-OS 11.2?
The following section describes new SD-WAN features introduced in PAN-OS 11.2.
Post-Quantum IKEv2 VPNs Support
|
April 2025
|
Cryptographically relevant quantum computers (CRQCs) threaten traditional
cryptographic systems by dramatically reducing the time needed to break encryption
algorithms. VPN communications secured by IKEv2 are vulnerable to the threats posed by CRQCs because IKEv2 uses
Diffie-Hellman (DH) and Elliptic Curve Diffie-Hellman (ECDH) for key exchange.
Delays in implementing post-quantum cryptography (PQC) increase the risk of Harvest
Now, Decrypt Later attacks. In these attacks, adversaries capture and store
encrypted data today for future decryption when CRQCs become available. If you
handle sensitive data requiring long-term storage, you are especially
susceptible.
To future-proof VPN communications against this emerging threat, PAN-OS® 11.1
implements quantum-resistant IKEv2 VPNs based on
RFC
8784. RFC 8784 specifies the mixing of post-quantum pre-shared keys (PQ
PPKs) with DH keys to create quantum-resistant connections. The implementation
involves a PQ PPK and a public key ID associated with the secret. You must share the
secret with both VPN peers out-of-band. After the peers perform a standard DH key
exchange, one peer sends the key ID to the other in-band. Both peers use that key ID
to identify the PQ PPK to mix with the DH key material. This method creates a new,
quantum-resistant key that provides multiple layers of protection. CRQCs can't
compromise the resulting key because it isn't based on prime number factorization
that Shor's algorithm exploits. Harvesting attacks fail because the PPK itself never
leaves your IKEv2 peers; adversaries can't capture the key material required for
future decryption, even if they compromise the DH key.
Palo Alto Networks implementation of RFC 8784 ensures a seamless transition to PQC.
The standard doesn't require cryptography upgrades, so you can introduce PPKs into
existing IPsec VPN deployments without network disruption. It also supports falling
back to classical cryptography if a peer doesn't support RFC 8784. Further, the
standard is interoperable with multiple vendors and works with other standards such
as RFC 9370.
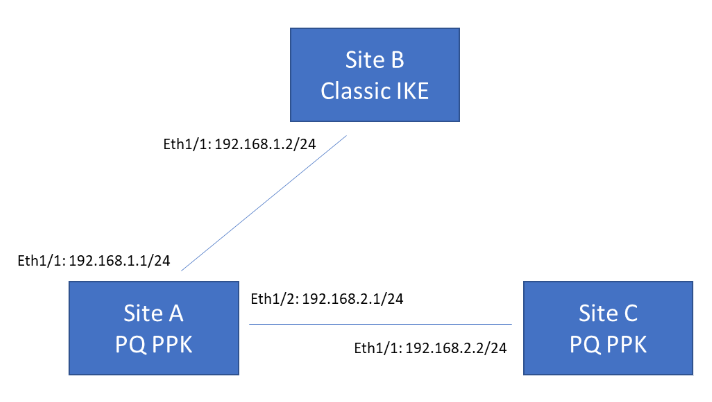
The following example topology shows three VPN termination sites. Sites A and C
support post-quantum VPNs based on RFC 8784, while Site B supports classical VPNs
only. Site A must be able to communicate with both Site B and Site C. When
communicating with Site B, Site A can either fall back to classical negotiation or
abort the connection, depending on your configured preference. When communicating
with Site C, Site A uses a PQ PPK because Site C supports this.
Add SD-WAN Capability to your Cellular Interfaces (4G/5G)
|
September 2024
|
As 5G becomes increasingly prominent, more organizations use or are
considering wireless WAN links as the primary or secondary WAN transport to share
the load. With wireless WAN 5G connectivity, you can achieve a reliable connection
on 5G-capable firewalls.
On the cellular interface, you can enable SD-WAN support on your 5G-capable
firewalls. When you enable SD-WAN on the 5G cellular interface, you are adding
support for automatic traffic steering based on the collected metrics within
qualified paths and links (which includes cellular and wireless WAN connections).
When you enable SD-WAN on a 5G cellular interface, you gain support for:
- IPv4 SD-WAN cellular traffic
- SD-WAN interface profile and upstream NAT
Multiple Virtual Routers Support on SD-WAN Branches
|
September 2024
|
SD-WAN deployments require strict routing separation and support for overlapping IP
subnets to meet regulatory requirements and accommodate complex network
architectures. Enabling multiple virtual routers (VRs) in your SD-WAN deployment
logically separates the routing infrastructure over SD-WAN overlays, which helps you
to comply with regulations and maintain network segregation while utilizing
overlapping IP subnets.
With this new functionality, you can run multiple instances of routing protocols on
your multiple VRs when connecting to neighboring routers. Those VRs can now use
overlapping address spaces and still successfully route traffic to the appropriate
destination based on the virtual router ID (VR-ID) associated with each virtual
router. This provides you with the flexibility to maintain multiple segregated VRs
for each connection.
To enable multiple virtual routers on an SD-WAN branch, you must first configure multiple virtual routers on the SD-WAN
hub to which these branches connect. You can configure a maximum of 20
virtual routers on an SD-WAN branch. However, the maximum number of virtual routers varies
based on the Palo Alto Networks Next-Generation Firewalls you use in your
deployment.
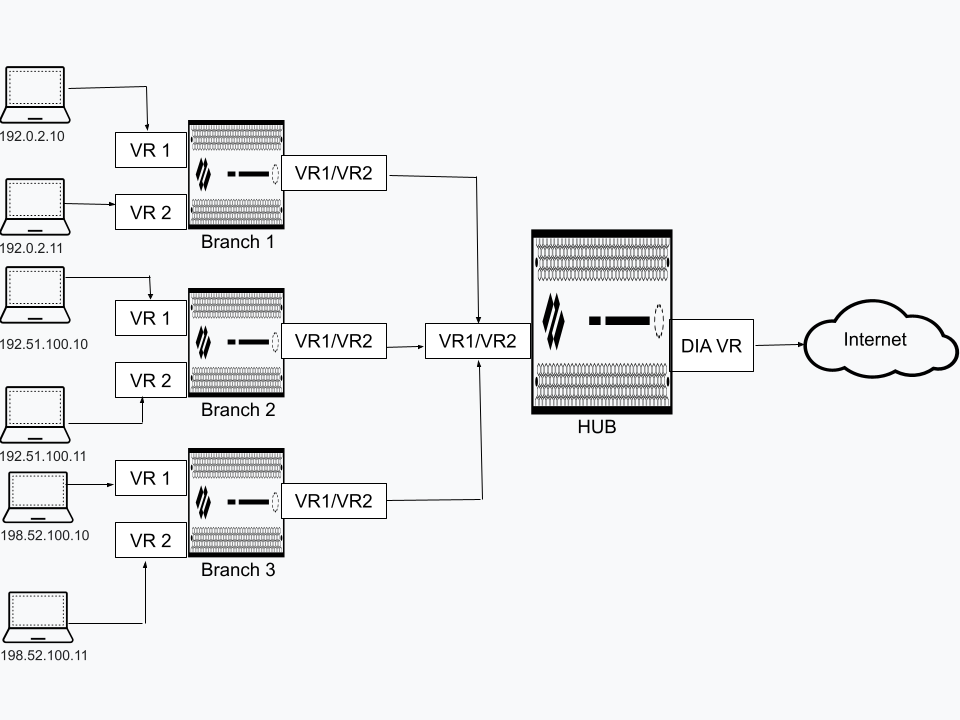
This illustration contains three SD-WAN branches, each configured with two virtual
routers. When you enable support for multiple VRs on the SD-WAN branches, those
three branches connected to the same SD-WAN hub can use overlapping IP subnets or
belong to different devices. In this configuration, these SD-WAN branches can
function independently because the branch traffic goes to different virtual
routers.
Monitor Bandwidth on SD-WAN Devices
|
May 2024
|
Currently it's difficult for the network administrators to quickly identify the cause
for an application’s poor performance in an SD-WAN device. It's because there isn't
enough information available to identify the issue and the available limited
information (such as VPN statistics, Panorama's device health statistics, and link
health statistics) are located between Panorama® and firewalls. It becomes a time
consuming activity for the administrators to correlate this information and locate
the performance issues on an SD-WAN device.
For a VPN cluster, you will now be able to view the bandwidth of a tunnel and a
physical interface for a selected site by default. Bandwidth is a primary measure of
a link performance in addition to existing
jitter, latency, and packet loss performance measures. There is no configuration
required to view the bandwidth of a tunnel.
Multiple Virtual Routers Support on SD-WAN Hubs
|
February 2024
May 2024
|
With earlier SD-WAN plugin versions, you can't have SD-WAN configurations on multiple
virtual routers. By default, a sdwan-default virtual router is created and it
enables Panorama to automatically push the router configurations. Due to this
restriction, customers faces difficulty and spends additional effort in some of the
SD-WAN deployments:
- User Scenario: Overlapping IP addresses from different branches connecting to the same hub.
- Single Virtual Router Configuration on SD-WAN Hub: Customers may need to reconfigure the overlapping subnets to unique address spaces.
- Multiple Virtual Routers Configuration on SD-WAN Hub: Enable Multi-VR Support on the SD-WAN hub device. The traffic from different branches is directed to different virtual routers on a single hub to keep the traffic separate.
- User Scenario: Government regulations that disallow different entities to function on the same virtual router.
- Single Virtual Router Configuration on SD-WAN Hub: Customers won’t be able to separate routing of different entities with a single virtual router.
- Multiple Virtual Routers Configuration on SD-WAN Hub: Enable Multi-VR Support on the SD-WAN hub device to keep the traffic of different entities separate. Multiple virtual routers on the SD-WAN hub maps the branches to different virtual routers on the hub that provides logical separation between the branches.
SD-WAN plugin now supports multiple virtual routers on the SD-WAN
hubs that enable you to have overlapping IP subnet addresses on branch
devices connecting to the same SD-WAN hub. Multiple virtual routers can run multiple
instances of routing protocols with a neighboring router with overlapping address
spaces configured on different virtual router instances. Multiple virtual router
deployments provide the flexibility to maintain multiple virtual routers, which are
segregated for each virtual router instance.
However, the number of virtual routers supported on the PAN-OS SD-WAN hub
varies by platform.
Benefits:
- A hub with multiple virtual router configuration logically separates the routing for each branch office that it is connected with.
- Branches sharing the same SD-WAN hub can reuse the same IP subnet address.
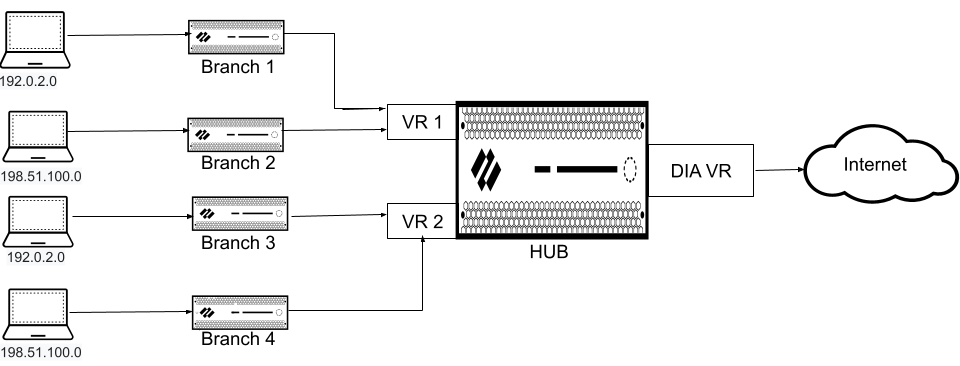
The following figure illustrates an SD-WAN hub with two virtual routers. By enabling
multiple virtual routers support on the SD-WAN hub, the four branches
connecting to the same SD-WAN hub (but different virtual routers) can have
overlapping IP subnets or belong to different entities and function independently
because their traffic goes to different virtual routers.
Additional Private Link Types Support on SD-WAN Device
|
April 2024
May 2024
|
The PAN-OS® SD-WAN plugin previously supported a limited number of private
link types, which complicated configurations for organizations using more than three
distinct private link providers. This limitation required administrators to
implement configuration workarounds, preventing the SD-WAN plugin from correctly
establishing one-to-one device peering based on the link type.
To address this, four additional link types are now
available: Private 1, Private 2, Private 3, and Private 4. These function
identically to the existing MPLS link type and inherit its aggressive path
monitoring characteristics. By allowing each distinct private link to be assigned a
unique type, this feature enables the SD-WAN plugin to correctly determine
one-to-one device peering for the overlay network, eliminating the need for
configuration workarounds.
Additional SD-WAN Hubs in VPN Cluster
|
April 2024
May 2024
|
The number of hubs to configure in a VPN cluster has been
increased from 4 to 16. Only four of the 16 hubs can have the same hub priority
within a VPN cluster due to ECMP.
