Prisma Access
Security Policy for Apps Enabled with ZTNA Connector (Panorama)
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
-
-
- 4.0 & Later
- Prisma Access China
-
-
Security Policy for Apps Enabled with ZTNA Connector (Panorama)
Set up a Security policy rule that enables users to access apps behind ZTNA Connector
for Panorama Managed Prisma Access deployments.
After you onboard apps to ZTNA Connector, you should set up policy rules to allow and
control access for those apps. The procedure to create and apply policy differs on
whether your apps are defined by wildcards, IP Subnets, or FQDNs.
Security Policy for Wildcard-Based Apps
Wilcard-based apps ( (SettingsZTNA ConnectorApplication TargetsWildcard Targets) require that you create a custom URL category; however, that
type of category only enforces policy for HTTP and HTTPS traffic, and other
traffic (such as SSH) isn't allowed. For this reason, you need to temporarily
allow access to all apps by allowing traffic to the ZTNA Connector Application
IP blocks.
After ZTNA Connector learns the FQDNs that are based on the wildcards, you can
disable the policy that allows Application IP Block traffic and apply policy
enforcement based on the learned FQDNs.
- Create a policy to allow the IP addresses for the ZTNA Connector Application IP Blocks.
- From the ZTNA Connector UI, go to ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessPrisma Access Infrastructure SetupPrisma Access Infrastructure and make a note of the Application IP Blocks under ZTNA Connector IPs.
![]() Go to ObjectsAddresses and Add address objects based on the IP addresses you retrieved.Go To ObjectsAddress Groups and Add the address objects you created to an address group.
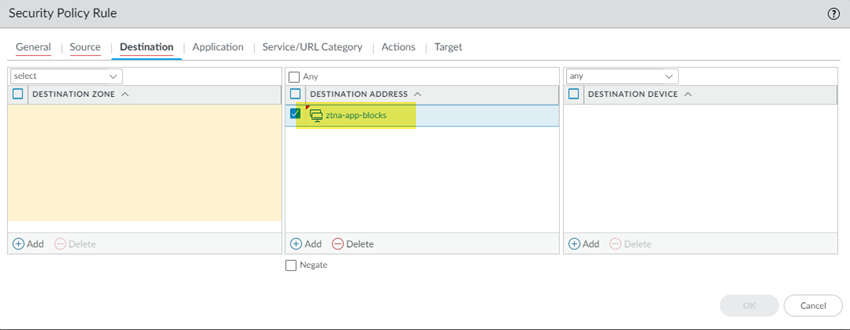
Go to ObjectsAddresses and Add address objects based on the IP addresses you retrieved.Go To ObjectsAddress Groups and Add the address objects you created to an address group.![]() Go to PoliciesSecurity Pre Rules and Add a Security policy to allow access to all application IP address blocks, specifying the Address Group you created in an earlier step.Adding this Security policy allows all traffic from wildcard-based app traffic to be passed while ZTNA Connector discovers the apps based on wildcards. Without the rule to allow the Application IP Blocks, users can't access wildcard-based apps.You can leave this policy in place until ZTNA Connector discovers the wildcard-based apps. Then, you can choose to disable this policy and add Security policy rules for each of the discovered apps.
Go to PoliciesSecurity Pre Rules and Add a Security policy to allow access to all application IP address blocks, specifying the Address Group you created in an earlier step.Adding this Security policy allows all traffic from wildcard-based app traffic to be passed while ZTNA Connector discovers the apps based on wildcards. Without the rule to allow the Application IP Blocks, users can't access wildcard-based apps.You can leave this policy in place until ZTNA Connector discovers the wildcard-based apps. Then, you can choose to disable this policy and add Security policy rules for each of the discovered apps.![]() After ZTNA Connector has discovered the apps based on wildcards, configure a Security policy for the apps that you added using FQDNs.
After ZTNA Connector has discovered the apps based on wildcards, configure a Security policy for the apps that you added using FQDNs.- Go to ConfigurationZtna ConnectorFQDN Targets and make a note of the FQDNs used by the apps.Create an Address object for the FQDN (ObjectsAddresses).Select either the Mobile_User_Device_Group or the Remote_Network_Device_Group, depending on whether mobile users or users at branch sites will be accessing the private apps behind ZTNA Connector.Add an address object with the Type of FQDN and enter the FQDN of the discovered application.Enter the FQDNs for the FQDN targets.
![]() Go to PoliciesSecurityPre Rules and Add a Security policy to allow access to the discovered apps.
Go to PoliciesSecurityPre Rules and Add a Security policy to allow access to the discovered apps.![]() Commit and Push your changes.(Optional) After you have created the Security policy based on FQDNs, remove the policy based on the IP application blocks.
Commit and Push your changes.(Optional) After you have created the Security policy based on FQDNs, remove the policy based on the IP application blocks.Security Policy for IP Subnet-Based Apps
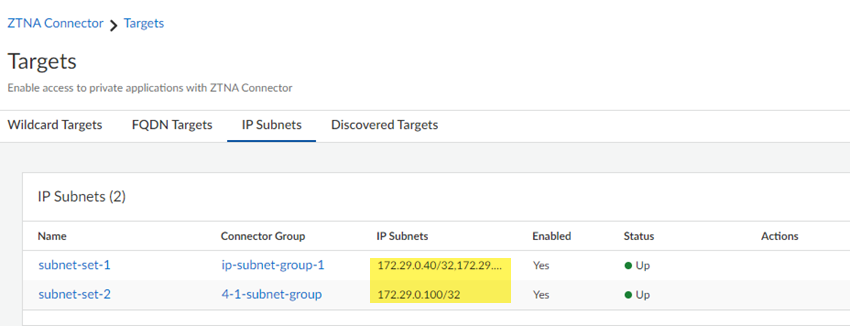
If you created ZTNA Connector application targets based on IP subnets (SettingsZTNA ConnectorConnectorsApplication TargetsIP Subnets), complete the following steps to allow access to the apps. - Go to ConfigurationZTNA ConnectorIP Subnets and make a note of the IP subnets used by the apps.
![]() Create a policy to allow the IP addresses for the IP subnets used for the apps.
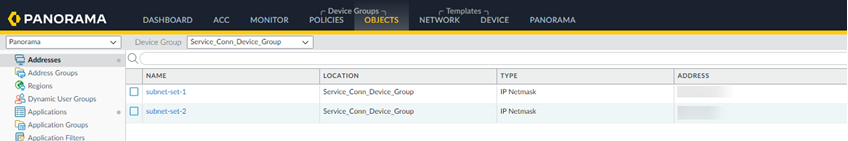
Create a policy to allow the IP addresses for the IP subnets used for the apps.- Go to ConfigurationNGFW and Prisma AccessObjectsAddressAddresses and Add address objects based on the IP addresses you retrieved.
![]() Go To ObjectsAddress Groups and Add the addresses you created to the address groups.
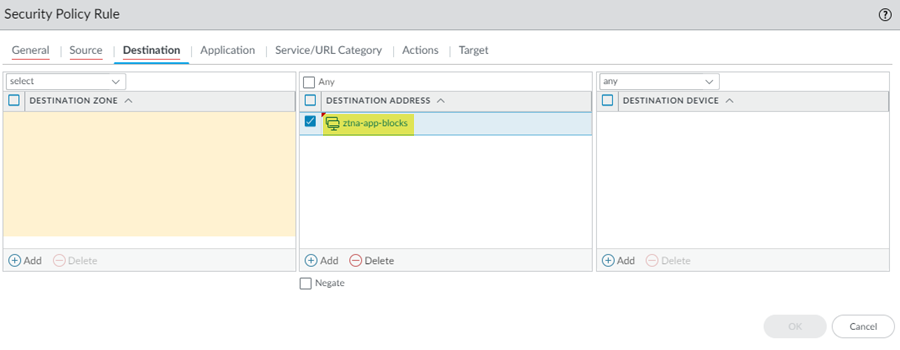
Go To ObjectsAddress Groups and Add the addresses you created to the address groups.![]() Go to PoliciesSecurityPre Rules and Add a Security policy to allow access to the IP subnets for the apps, specifying the Addresses you created in an earlier step.
Go to PoliciesSecurityPre Rules and Add a Security policy to allow access to the IP subnets for the apps, specifying the Addresses you created in an earlier step.![]() Push Config to save and push your configuration changes.
Push Config to save and push your configuration changes.Security Policy for FQDN-Based Apps
If you have added targets based on FQDNs (SettingsZTNA ConnectorConnectorsApplication TargetsFQDN Targets), create an address object and a Security policy to allow access to the apps by completing the following steps. - Configure a Security policy for the apps that you added using FQDNs.
- Go to ConfigurationZTNA ConnectorFQDN Targetsand make a note of the FQDNs used by the apps.Create an Address object for the FQDN (ObjectsAddresses).Select either the Mobile_User_Device_Group or the Remote_Network_Device_Group, depending on whether mobile users or users at branch sites will be accessing the private apps behind ZTNA Connector.Add an address object with the Type of FQDN and enter the FQDN of the discovered application.Enter the FQDNs for all discovered apps.
![]() Optional Go to ConfigurationNGFW and Prisma AccessSecurity ServicesSecurity PolicyPre Rules and Add a Security policy to allow access to the discovered apps.Push Config to save and push your configuration changes.
Optional Go to ConfigurationNGFW and Prisma AccessSecurity ServicesSecurity PolicyPre Rules and Add a Security policy to allow access to the discovered apps.Push Config to save and push your configuration changes.