Strata Cloud Manager
New Features in September 2023
Table of Contents
Expand All
|
Collapse All
Strata Cloud Manager Docs
New Features in September 2023
Here are the new features available in Strata Cloud Manager in September
2023.
Here are the latest new features introduced on Strata Cloud Manager. Features listed here
include some feature highlights for the products supported with Strata Cloud Manager.
For the full list of new features supported for a product you're using with Strata Cloud
Manager, see the release notes for that product.
Prisma Access: Traffic Mirroring and PCAP Support
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Prisma® Access secures your traffic in real time based on traffic inspection, threat
analysis, and security policies. While you can view Prisma Access logs to view
security events, your organization might have a requirement to save packet capture (PCAP) files for forensic and
analytical purposes, for example:
- You need to examine your traffic using industry-specific or privately-developed monitoring and threat tools in your organization and those tools require PCAPs for additional content inspection, threat monitoring, and troubleshooting.
- After an intrusion attempt or the detection of a new zero-day threat, you need to preserve and collect PCAPs for forensic analysis both before and after the attempt. After you analyze the PCAPs and determine the root cause of the intrusion event, you could then create a new policy or implement a new security posture.
- Your organization needs to download and archive PCAPs for a specific period of time and retrieve as needed for legal or compliance requirements.
- Your organization requires PCAPs for network-level troubleshooting (for example, your networking team requires data at a packet level to debug application performance or other network issues).
To accomplish these objectives, you can enable traffic replication which uses the
Prisma Access cloud to replicate traffic and encrypt PCAP files using your
organization's encryption certificates.
Prisma Access: New Local Zones
|
September 29, 2023
New local zones:
Now supported on Strata Cloud Manager for:
|
Local zones place compute, storage,
database, and other services close to large population and industry centers. These
locations have their own compute locations.
Keep in mind the following guidelines when deploying local zones:
- Local zone locations do not support IPv6.
- Local zone locations do not use Palo Alto Networks registered IP addresses.
- 1 Gbps support for remote networks is not supported.
- Remote network and service connection node redundancy across availability zones is not available if you deploy them in the same local zone, as both nodes are provisioned in a single zone.
- These local zones do not use Palo Alto Networks registered IPs. If you have problems accessing URLs, report the website issue using https://reportasite.gpcloudservice.com/ or reach out to Palo Alto Networks support.
- Some SaaS applications might experience a higher latency in local zones when compared with non-local zone locations.
Prisma Access: Microsoft Defender for Cloud Apps Integration
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Unmanaged cloud services and shadow IT applications can introduce significant
security risks to your network. To address this issue, you can now integrate Prisma®
Access with Microsoft Defender for Cloud Apps. This
integration automatically syncs and blocks the list of unsanctioned applications
inline, providing crucial closed-loop remediation. This integration enables you to
gain visibility and to discover all cloud applications and shadow IT applications
being used. The automated syncing and blocking provide crucial closed-loop
remediation for unsanctioned applications.
Microsoft Defender is one of many Microsoft products that Prisma Access integrates
with so that you can protect your applications and data on Azure, in Office 365, on
the network, and the endpoint.
Cloud Management for NGFWs: New Predefined BGP Distribution Profile (Auto VPN & SD-WAN)
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Configuring full mesh connectivity and ensuring dynamic branch-to-branch
communication in complex SD-WAN environments often requires manual intervention and
intricate Border Gateway Protocol (BGP) setup. This process is time-consuming and
can lead to configuration errors, potentially limiting the seamless flow of traffic
across autonomous systems (AS).
Auto VPN simplifies network reachability
management across your managed NGFW connections using SD-WAN. When
you add NGFW to a VPN cluster, Strata Cloud Manager automatically
assigns the predefined All-Connected-Routes BGP
Redistribution profile by default. This BGP Redistribution profile determines
network reachability based on IP prefixes available within autonomous systems
(AS).
By setting the All-Connected-Routes profile as the
default, you ensure SD-WAN broadcasts all connected routes to every VPN peer in the
cluster. This profile handles both the necessary tunnel and route peering
configuration, completing all route advertisements required for secure, dynamic
branch-to-branch communication without administrative overhead. This automation
immediately enables full network visibility, saving significant configuration time
and ensuring a consistent routing policy across your entire VPN cluster.
Cloud Management for NGFWs: Custom Path Quality Profile (SD-WAN)
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Managing the performance of business-critical and latency-sensitive applications
across multiple SD-WAN paths requires strict, real-time
quality control. Network deterioration,even brief spikes in latency, jitter, or
packet loss, can severely impact user experience and service continuity. Security
administrators can now create custom path quality profiles for SD-WAN to define
unique network quality requirements for applications, services, and groups.
Create a custom path quality profile on Strata Cloud Manager to establish maximum
thresholds for key performance indicators: latency, jitter, and packet loss
percentage. Security administrators specify the maximum limit for each parameter,
above which the firewall considers the path unreliable. The firewall treats these
criteria as OR conditions, meaning if the network quality exceeds any one of
the defined thresholds (latency OR jitter OR packet loss), the firewall immediately
selects the new best path. Any path that has latency, jitter, and packet loss
metrics less than or equal to all three defined thresholds is considered qualified,
and the firewall selects the final path based on the associated Traffic Distribution
profile, ensuring consistent, high-quality network resources for your most demanding
applications.
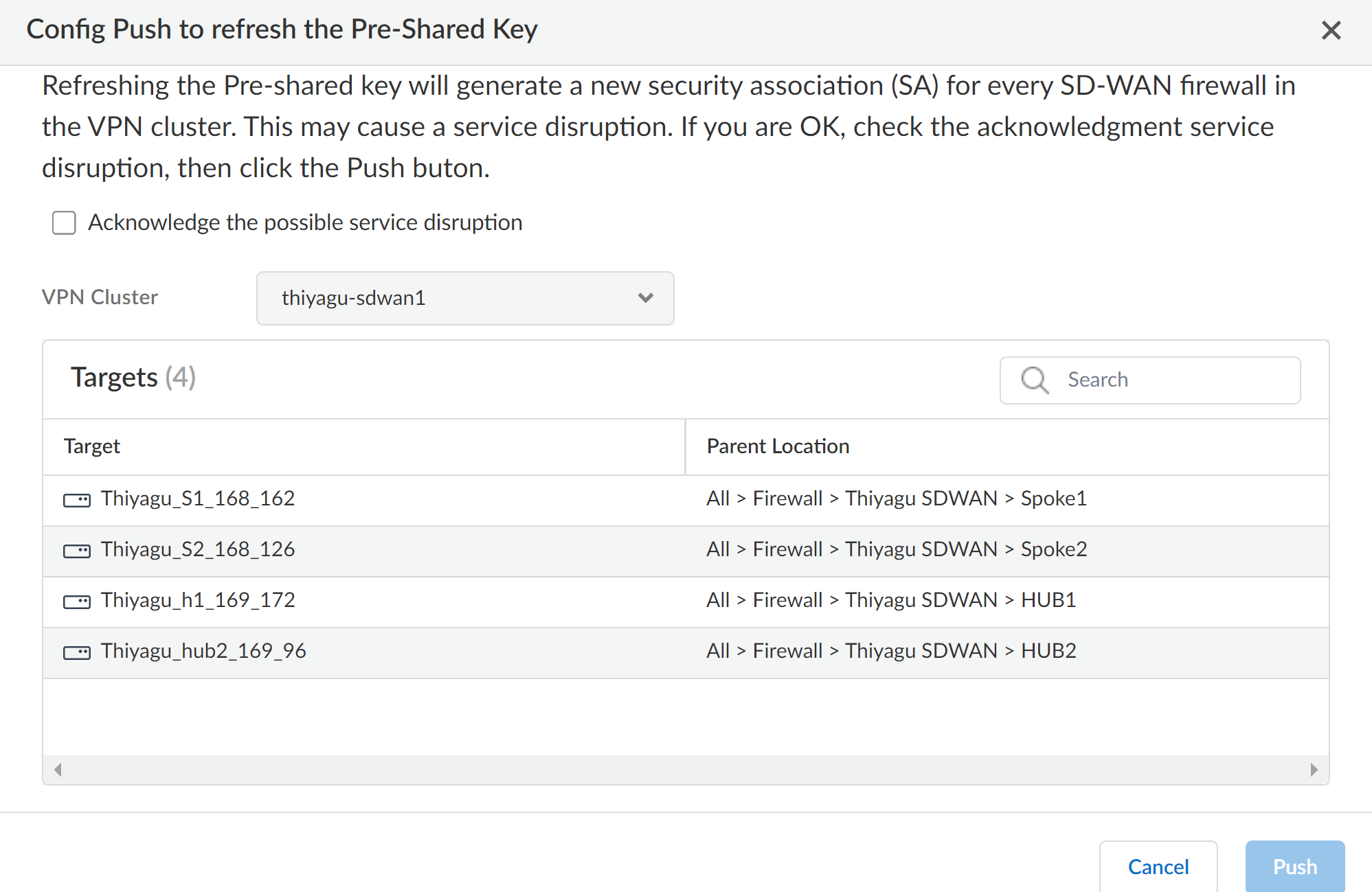
Cloud Management for NGFWs: Pre-Shared Keys Refresh (Auto VPN & SD-WAN)
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Auto VPN allows you to configure secure
connectivity between Strata Cloud Manager and your managed firewalls using SD-WAN. Peers in the VPN cluster use a
pre-shared key to mutually authenticate each other. Strata Cloud Manager now allows
you to refresh the pre shared keys used for authenticating VPN tunnels for existing
VPN clusters (ManageConfigurationNGFW and Prisma AccessGlobal SettingsAuto VPN).
Cloud Management for NGFWs: Cloud IP Tag Collection (with the Cloud Identity Engine)
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Enforcing your security policy consistently across all the firewalls in your network
relies on those firewalls having the most up-to-date identity information from your
sources, such as cloud-based identity management systems. With the array of
management systems and large numbers of users and devices, it can often be
time-consuming and difficult to correlate identity information with its originating
sources and ensure that it was provided to all necessary devices.
You can now use Strata Cloud Manager with the Cloud Identity Engine to manage IP
address-to-tag (also known as IP-tag) mappings and simplify your security policy by
creating tag-based rules. When you configure a cloud connection in the Cloud
Identity Engine to your cloud-based identity management system (either Azure or
AWS), you can use the Cloud Identity Engine to collect IP-tag mappings.
You can see all of your IP-tag mappings, as well as their associated sources, in the
Cloud Identity Manager. Using filters to highlight the most relevant information,
you can quickly identify issues with your security policy, such as a source that is
currently unavailable. You can then use the Strata Cloud Manager to create tag-based
security policy using dynamic address groupsand distribute it to
the firewalls in your network to ensure they have the latest information needed to
consistently enforce security policy. You can also share the IP-tag mappings with
other firewalls in your network by using User Context segments in the Cloud
Identity Engine.
By leveraging the capabilities of Strata Cloud Manager with the identity information
that the Cloud Identity Engine provides, you can more easily create and manage your
security policy using tags.
Cloud Management for NGFWs: Configuration Version Snapshot
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Managing configuration pushes for cloud managed NGFWs and Prisma® Access
deployments often lacks comprehensive oversight and rapid recovery options. Config Version Snapshots solve this
by providing enhanced visibility and control over your security infrastructure
changes, ensuring you can confidently deploy updates while maintaining the ability
to quickly recover from any unintended consequences.
You can now evaluate configuration pushes with detailed analysis tools,
compare your candidate configuration against previously pushed configurations to
identify specific changes, and rollback recent modifications in the event of any
unintended consequences from a recent push. This comparison functionality helps you
understand exactly what will change before committing updates to production
environments.
The system allows you to load previous configurations to use as candidates
for your next configuration push, enabling you to build upon proven stable
configurations and make incremental changes to expand the scope of the original
setup. This iterative approach reduces risk by allowing you to test and validate
changes incrementally rather than implementing large-scale modifications all at
once.
When issues arise, you can restore previous configurations to immediately
rollback the changes from a recent configuration push, minimizing downtime and
quickly returning your security infrastructure to a known good state. This rollback
capability is essential for maintaining business continuity during configuration
troubleshooting scenarios.
Additionally, you can review the specific devices or deployments that are
impacted or targeted by your configuration pushes, providing you with complete
visibility into the full scope of changes across your entire security
infrastructure. This comprehensive view ensures you understand which systems will be
affected before executing any configuration updates.
Cloud Management for NGFWs: Troubleshooting for NGFW Connectivity and Policy Enforcement
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Troubleshoot these
networking and identity features–track down and resolve connectivity issues or
policy enforcement anomalies:
Network Troubleshooting for NAT and DNS Proxy
Troubleshoot your NGFWs from Strata Cloud Manager without having to move
between various firewall interfaces. If you experience connectivity issues after
deploying and configuring your NGFWs, you can get an aggregate view of your routing
and tunnel states, and drill down to specifics to find anomalies and problematic
configurations.
Identity and Policy Troubleshooting
Troubleshoot your identity-based policy rules and dynamically defined
endpoints. Check the status of specific NGFWs and expose possible mismatches between
how you expect a policy to work and its actual enforcement behavior.
Cloud Management for NGFWs: Config Cleanup
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Do dynamic business needs often require you to deal with rapid configuration changes
that result in complex configurations with a number of zero hit rules, zero hit
objects, unused objects, and duplicate objects? Such configurations can lead to a
poor security posture and can inadvertently increase the attack surface of your
network. Config Cleanup has you covered.
Config Cleanup gives you a comprehensive view of all policy rules that have no hits,
objects that aren't referenced directly or indirectly in your configuration, objects
that are referenced in a policy rule but have no hits in the Traffic log during the
specified time frame, and objects of the same type with different names but have the
same values so that you can better:
- Manage attack surface exposure
- Prioritize remediation actions
- Remediate over time
- Respond to audit questions when they arise
Identify and remove unused configuration objects and policy rules from your
configuration. Removing unused configuration objects eases administration by
removing clutter and preserving only the configuration objects that are required for
security enforcement.
Review unused objects and policy rules across your entire Strata Cloud Manager
configuration for the last 6 months, and optimize policy rules that are overly
permissive rules to convert these to be more specific, focused rules that only allow
the applications you’re actually using.
Together with Policy Optimizer, these tools help you
ensure that your policy rules stay fresh and up to date.
Cloud Management for NGFWs: Policy Optimizer
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Overly permissive security rules—such as those allowing "any" application traffic—are
common in large networks, creating security gaps by enabling unused applications and
unnecessarily increasing the attack surface. Manual review and optimization of these
broad rules require extensive log analysis and introduce deployment risk. Strata
Cloud Manager introduces Policy Optimizer that analyzes log data to identify overly
permissive security rules. Policy Optimizer auto-generates specific,
focused rule recommendations based only on the applications actively observed on
your network. This capability eliminates the need for manual log analysis,
strengthens your security posture, and reduces administrative overhead.
Administrators receive actionable, auto-generated optimization recommendations that
can be reviewed and accepted through a guided workflow, ensuring that rule
consolidation and replacement are secure and policy integrity is maintained.
Together with Config Cleanup, these tools help you
ensure that your policy rules stay fresh and up to date.
Cloud Management for NGFWs: Explicit Web Proxy
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Prisma® Access has its own,
separate method of configuring explicit proxy. This
new feature applies only to cloud-managed firewalls.
To consolidate management, you can now configure a web proxy on the firewalls you're
managing with. This means that if you
use an NGFW as a proxy device to secure your network, you can configure your proxy
settings across your deployment from a single management interface.
This interface includes an in-app Proxy Auto-Configuration (PAC) file
editor so that you can edit your proxy settings and modify your PAC file all in one
place whenever network changes arise.
The web proxy supports two methods for routing traffic:
- Explicit Proxy— The request contains the destination IP address of the configured proxy, and the client browser sends requests to the proxy directly. Authentication methods such as Kerberos and SAML 2.0 are supported, requiring the appropriate web proxy licensing.
- Transparent Proxy—The request contains the destination IP address of the web server and the proxy transparently intercepts the client request (either by being in-line or by traffic steering). This method requires specific networking prerequisites, including a loopback interface, User-ID configuration in the proxy zone, and specific Destination NAT (DNAT) rules defined in Strata Cloud Manager. Transparent proxy does not support X-Authenticated Users (XAU) or Web Cache Communications Protocol (WCCP).
You can push web proxy configurations to the following platforms:
- PA-1400
- PA-3400
- VM-Series (with a minimum of four vCPUs)
Strata Cloud Manager: SaaS Application Endpoint Lists and Enforcement
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
SaaS providers publish lists of the IP addresses and URL endpoints their SaaS
applications use, and frequently update these lists. Strata Cloud Manager now
consumes application endpoint lists from the Palo Alto Networks EDL Hosting Service, so that you can
easily enforce policy for SaaS providers including (but not limited to):
- Microsoft
- Azure
- Amazon Web Services (AWS)
- Google Cloud Platform (GCP)
- Salesforce (SFDC) public endpoints
- Microsoft Defender
- Zoom
- GitHub
In Strata Cloud Manager, you can now subscribe to SaaS application
endpoints lists (both optional and required), and reference the lists in policies
for your cloud-managed NGFWS and Prisma Access.
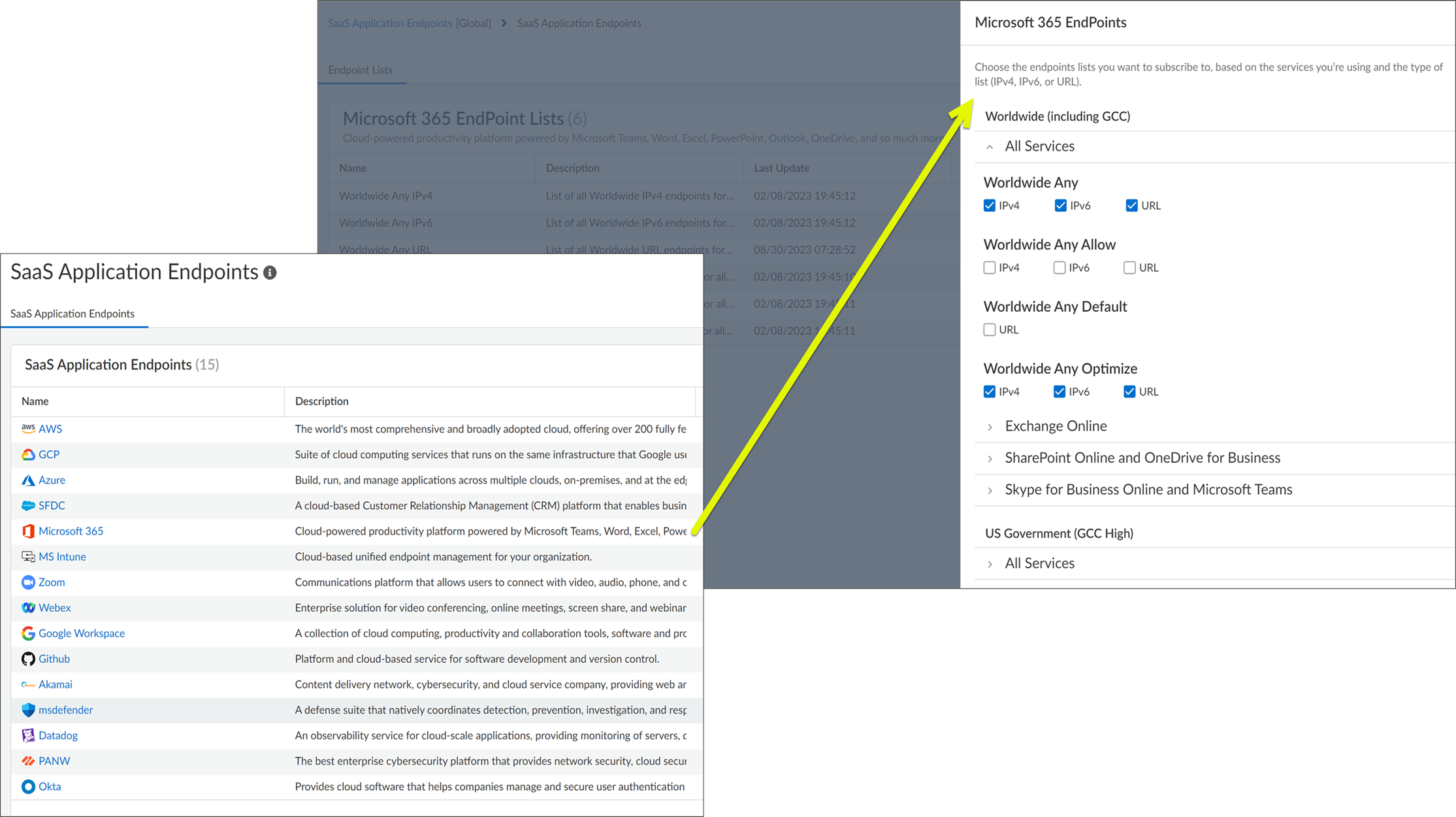
Important to know:
- This feature natively integrates the Palo Alto Networks EDL Hosting Service with Strata Cloud Manager. If you are or were previously using the EDL Hosting Service, the introduction of this feature doesn't impact any of your existing configuration. Any EDLs you've already created that reference a feed URL will continue to work as expected.
- Until now, the O365-Best-Practice snippet enabled you to directly subscribe to M365 endpoint lists in Strata Cloud Manager. With this feature, this snippet is now updated to be an application endpoint list. If you were using this snippet in a policy rule, the update is seamless, and the policy rule will reference the migrated application endpoint list.
- SaaS Tenant Restrictions continue to provide you a way limit SaaS app usage to enterprise accounts (to stop users from accessing their personal accounts on the company network).
- SaaS providers publish lists of the IP addresses and URL endpoints their SaaS applications use, and frequently update these lists. Strata Cloud Manager now hosts these SaaS application endpoint lists directly, so that you can enforce policy for application endpoints from SaaS providers including (but not limited to):
Strata Cloud Manager: Snippet Deletion
|
September 29, 2023
Supported on Strata Cloud Manager for:
|
Administrators often struggle with disorganized configuration scopes due to
unused custom snippets cluttering their management interface. Over time, as network
configurations evolve and deployments change, custom snippets can become obsolete or
redundant, creating confusion during configuration management tasks and increasing
the risk of accidentally applying outdated or inappropriate configurations to
production environments.
You can now delete custom snippets that are no
longer associated with any deployments, firewalls, or folders to keep your
configuration scope organized and prevent unwanted or unused snippets from being
applied by mistake. This cleanup capability helps maintain a streamlined
configuration management experience and reduces the potential for configuration
errors.
Snippets in Strata Cloud Manager are classified into two categories:
Predefined snippets are available to all Strata Cloud Manager users and help you
quickly get your new firewalls and deployments up and running with best practice
configurations. Custom snippets are any snippets that administrators create for
specific organizational needs.
You can delete unused custom snippets directly from the configuration scope
view, providing a convenient way to maintain an organized snippet library. Note that
predefined snippets available in Strata Cloud Manager cannot be deleted, ensuring
that essential best practice configurations remain available to all users.
Strata Cloud Manager: Enhancements to WildFire Dashboard
|
September 27, 2023
Supported on Strata Cloud Manager for:
|
The Advanced WildFire dashboard is now
enhanced to provide a comprehensive view of sample analysis data that you can use to
make informed decisions. The dashboard displays the source of WildFire sample
submissions, insights into unique and new samples by threat type, and context on the
most recent submissions from your network. The dashboard also enables filtering of
data based on a file hash.
Strata Cloud Manager: Advanced WildFire Analysis Data in IoC Search
|
September 15, 2023
Supported on Strata Cloud Manager for:
|
When evasive malware bypasses your defenses, it complicates post-breach analysis. You
can now view Advanced Dynamic WildFire® analysis data directly within Threat Search in Strata Cloud Manager.
This provides the in-depth detail required for a complete and thorough
investigation. This feature integrates detailed results from Advanced WildFire—the
cloud-based engine that detects and prevents highly evasive malware—directly into
your search results.
This new data stream complements existing static and dynamic analysis, giving you a
consolidated view of file behavior. As a result, you can simplify post-attack
analysis, reduce investigation time, and accelerate threat hunting, all from a
single screen.
Strata Cloud Manager: Signature-Based PCAP in Threat Logs
|
September 15, 2023
Supported on Strata Cloud Manager for:
|
You can now view and download signature-based packet captures (PCAPs), along with the
inline detected PCAPs in threat logs. These packet captures provide context around a
threat to help you report false-positives or learn more about the methods used by
the attacker. To download a PCAP, view threat type logs in the Log Viewer and download packet
captures.
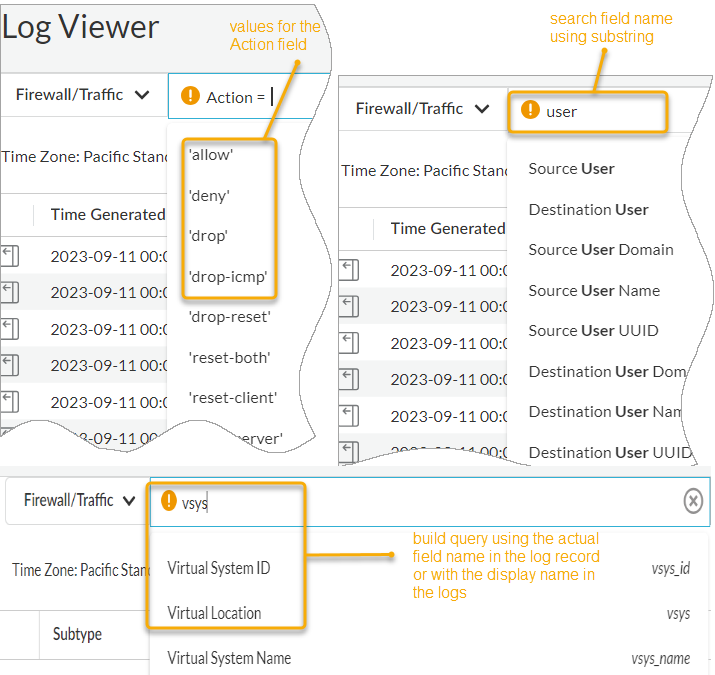
Strata Cloud Manager: Log Viewer Visibility Enhancements
|
September 15, 2023
Supported on Strata Cloud Manager for:
|
Log Viewer is enhanced to search
and view relevant logs easily. The enhancements include:
- Autosuggestions for field values when you select a field in the query builder.
- Search field names using substrings (for example, search with the string ‘user’ returns suggestions such as source_user, destination_user).
- Search for a field based on the displayed field name in the log table and not just the actual field name in the log record. The query builder uses the displayed field name.
- Press Shift + Enter to start a new line in the query builder, and press Enter to submit a query.