Enterprise DLP
Set Up Cloud Storage on AWS to Save Evidence
Table of Contents
Expand All
|
Collapse All
Enterprise DLP Docs
Set Up Cloud Storage on AWS to Save Evidence
Create an S3 storage bucket on AWS to store files that match your Enterprise Data Loss Prevention (E-DLP) data profiles.
On May 7, 2025, Palo Alto Networks is introducing new Evidence Storage and Syslog Forwarding service IP
addresses to improve performance and expand availability for these services
globally.
You must allow these new service IP addresses on your network
to avoid disruptions for these services. Review the Enterprise DLP
Release Notes for more
information.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Enterprise DLP license
|
Amazon Web Services (AWS) users can configure an S3 storage bucket to automatically
upload all files that match an Enterprise Data Loss Prevention (E-DLP) data profile for Enterprise DLP.
To store your files scanned by Enterprise DLP, you must create an S3 storage
bucket and Identity and Access Management (IAM) role that allows Enterprise DLP
access to automatically store files. Enterprise DLP provides you with a JSON
data containing the required policy permissions to create the IAM role. Files
uploaded to your S3 storage bucket are automatically named using a unique Report ID
for each file. The Report ID is used to search and download specific files for more
in-depth investigation.
Enterprise DLP automatically sends email alerts to the data security
administrator who originally connected Enterprise DLP to the S3 storage bucket
and to the data security admin who last modified the storage bucket settings in case
of connection issues. Enterprise DLP sends the email alert every 48 hours until
you restore the connection between Enterprise DLP and the storage bucket.
Files not scanned while Enterprise DLP is disconnected from your storage
bucket can’t be stored and are lost. This means that all impacted files are not
available for download. However, your data security administrator can still view
all snippet data associated with the DLP incident.
Enterprise DLP automatically resumes forwarding files to your storage bucket
after you restore the connection.
Set up Evidence Storage on Strata Cloud Manager Using AWS
Create an S3 storage bucket on AWS to store files that match your Enterprise Data Loss Prevention (E-DLP) data profiles.
- Review the setup prerequisites for Enterprise DLP and enable the required ports, full qualified domain names (FQDN), and IP addresses on your network.Create a public S3 storage bucket to store files scanned by Enterprise DLP.
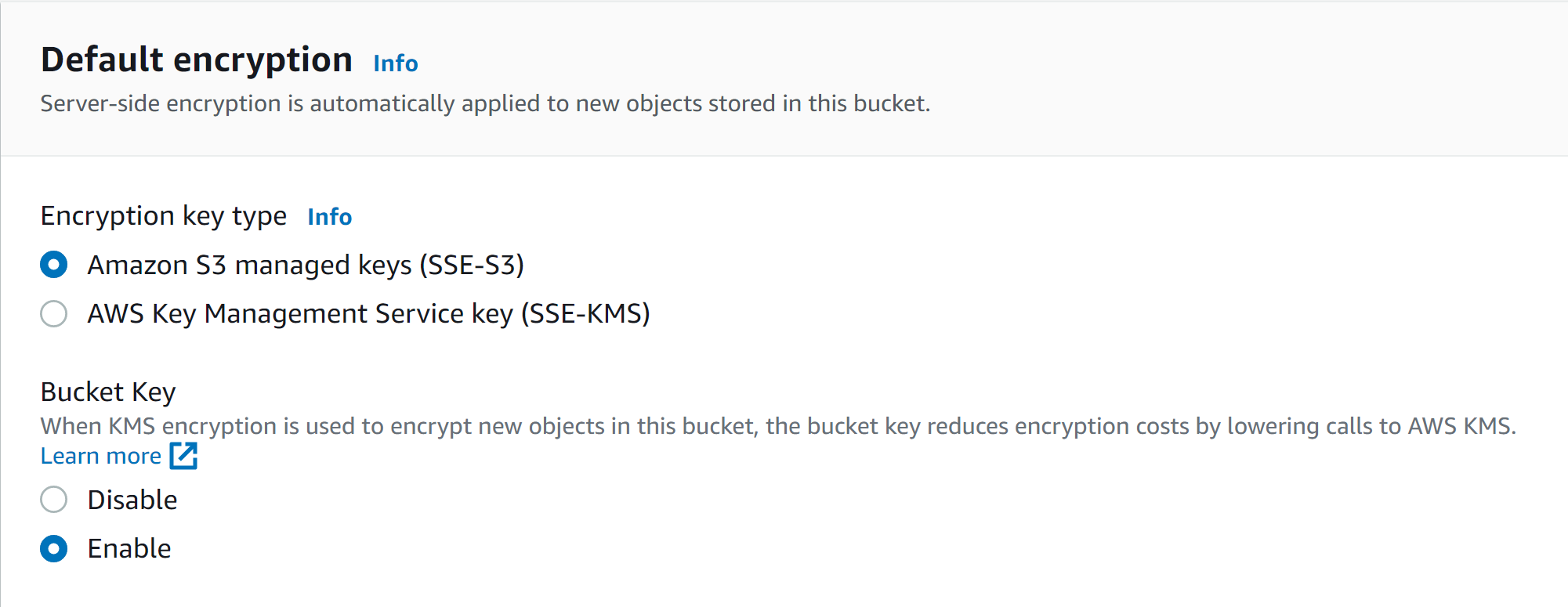
- Log in to the Amazon AWS console.Select ServicesStorageS3Buckets and Create bucket.Enter a descriptive Bucket name.Select the AWS Region for the S3 storage bucket.In the Default encryption section, select Amazon S3 managed keys (SSE-S3) as the Encryption key type.
![]() Create bucket.Obtain the ARN for the S3 storage bucket.After creating the S3 storage bucket, you're redirected back to the Buckets page. Search for and click the storage bucket you created.Click Properties. The storage bucket ARN is displayed in the Bucket overview.Enable the AWS KMS setting for the storage bucket and locate the trust relationship and access policy JSONs provided by Palo Alto Networks.
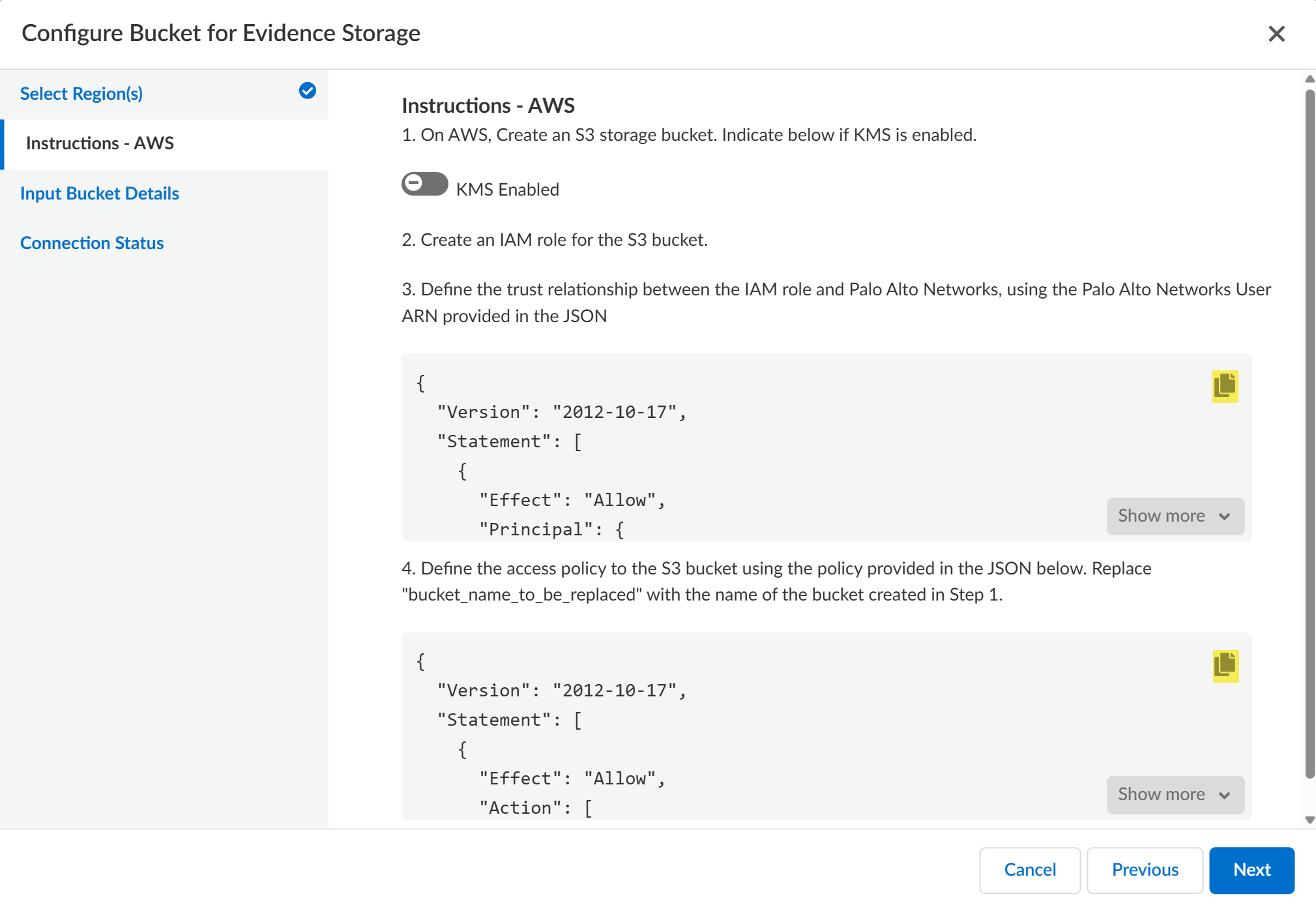
Create bucket.Obtain the ARN for the S3 storage bucket.After creating the S3 storage bucket, you're redirected back to the Buckets page. Search for and click the storage bucket you created.Click Properties. The storage bucket ARN is displayed in the Bucket overview.Enable the AWS KMS setting for the storage bucket and locate the trust relationship and access policy JSONs provided by Palo Alto Networks.- Log in to Strata Cloud Manager.Select ConfigurationData Loss PreventionSettingsSensitive Data.In Evidence Storage, select Configure Regional BucketAWS as the Public Storage Bucket.In Instructions - AWS, locate the trust relationship and access policy JSON provided to define the trust relationship and access policy between the IAM role and Enterprise DLP.The first JSON provided is the trust relationship and the second is the access policy. Highlighted are the copy buttons that you will use later on to create the IAM role for the S3 storage bucket.Leave the Configure Bucket for Evidence Storage display open and continue to create the IAM role for the S3 storage bucket in a separate browser window.
![]() Create the IAM role for the S3 storage bucket.This role is required to allow Enterprise DLP to write to the S3 storage bucket.
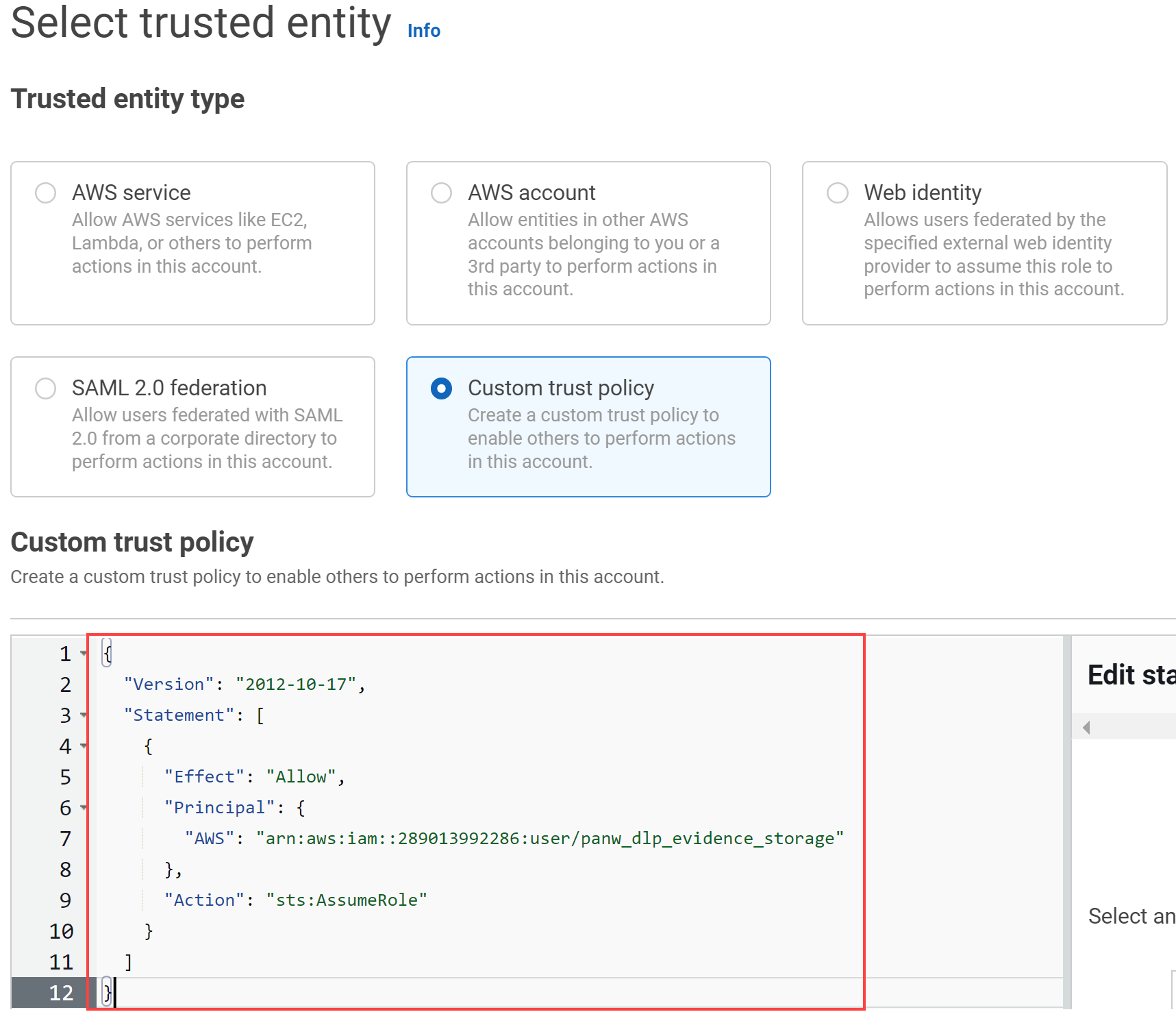
Create the IAM role for the S3 storage bucket.This role is required to allow Enterprise DLP to write to the S3 storage bucket.- Log in to the Amazon AWS console.Select ServicesSecurity, Identity, and ComplianceIAMAccess managementRoles and Create role.Select Custom trust policy.For the Trusted entity type, select Custom trust policy.Return to Strata Cloud Manager and copy the trust relationship JSON.In the Amazon AWS console, paste the trust relationship JSON into the Custom trust policy to configure the trust policy.
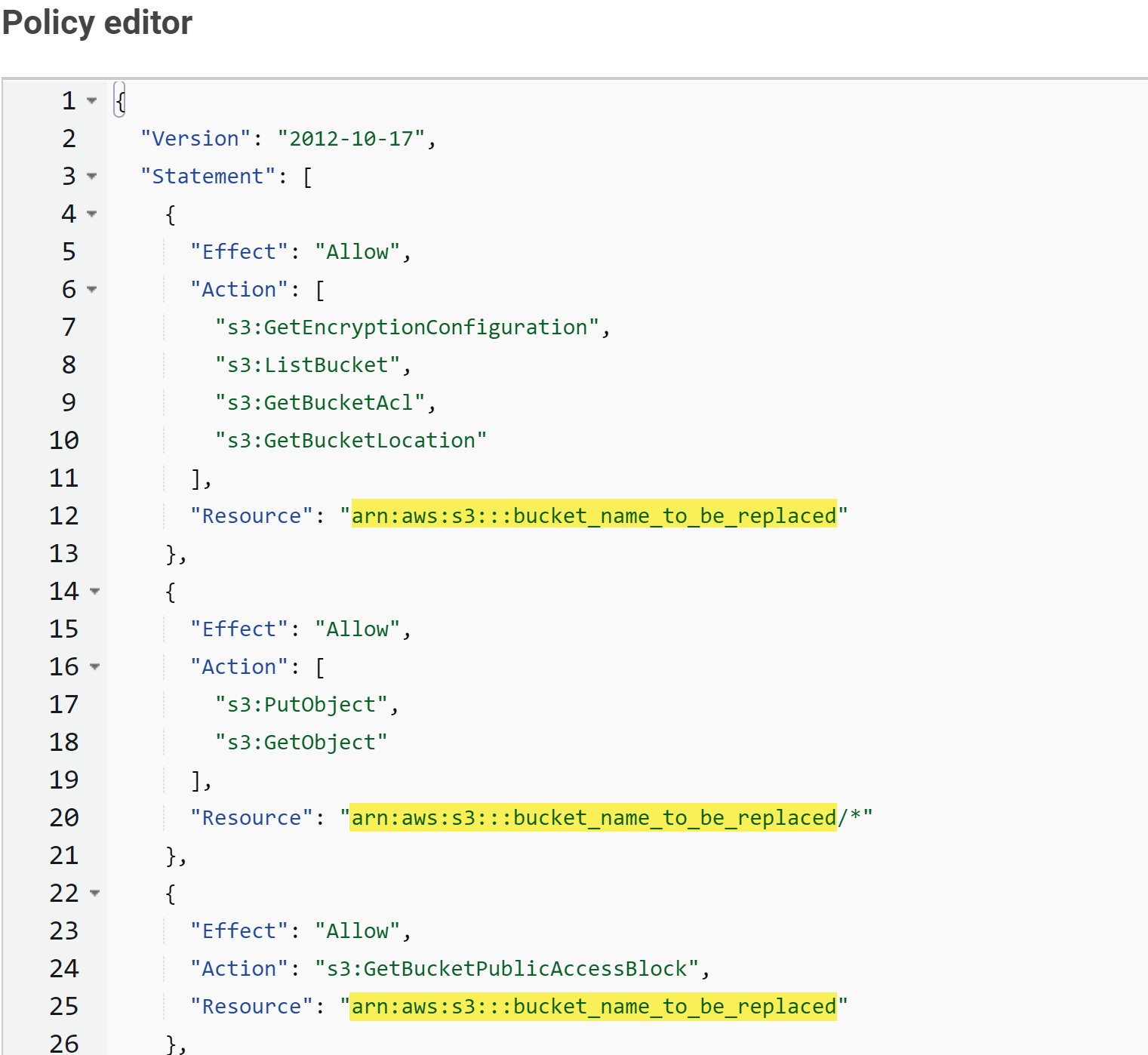
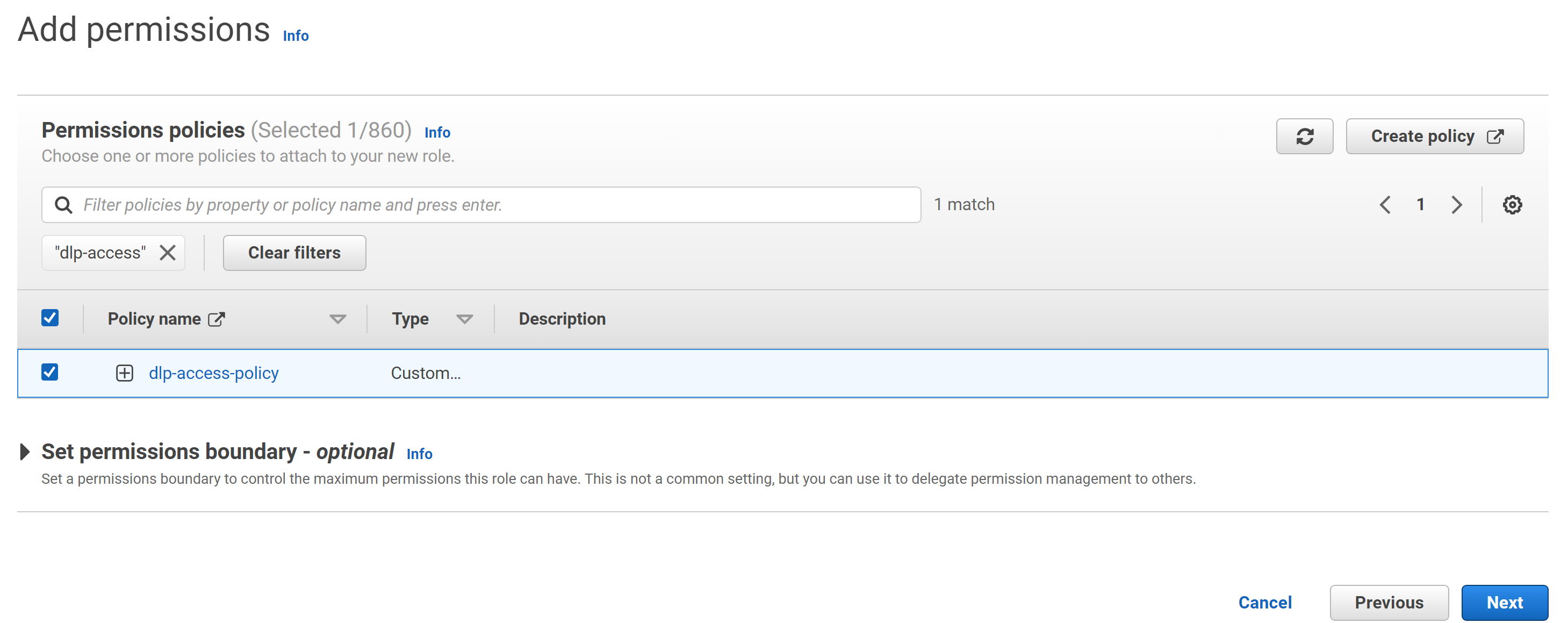
![]() Click Next.In Add permissions, select Create policyJSON.A new window is automatically opened in your browser to create the new access policy.Return to Strata Cloud Manager and copy the access policy JSON.In the Amazon AWS console, paste the access policy JSON into the Policy editor.Add the bucket ARN for the S3 storage bucket you created.Throughout the JSON, you must replace all instances of bucket_name_to_be_replaced with the S3 storage bucket ARN you created.
Click Next.In Add permissions, select Create policyJSON.A new window is automatically opened in your browser to create the new access policy.Return to Strata Cloud Manager and copy the access policy JSON.In the Amazon AWS console, paste the access policy JSON into the Policy editor.Add the bucket ARN for the S3 storage bucket you created.Throughout the JSON, you must replace all instances of bucket_name_to_be_replaced with the S3 storage bucket ARN you created.![]() Click Next.Enter a Policy name and Create policy.Return to the browser window where you're creating the IAM role,Search for and select the access policy you created.
Click Next.Enter a Policy name and Create policy.Return to the browser window where you're creating the IAM role,Search for and select the access policy you created.![]() Click Next.Enter a descriptive Role name for the IAM role.Review the IAM role trust relationship and access policy.Create role.Log in to Strata Cloud Manager.Access to evidence storage settings and files on Strata Cloud Manager is allowed only for an account administrator or app administrator role with Enterprise DLP read and write privileges. This ensures that only the appropriate users have access to report data and evidence.(Email DLP only) Select ConfigurationSaaS SecuritySettingsEmail DLP Settings and enable Evidence Storage for Email DLP.You must enable the evidence storage service for Email DLP so Enterprise DLP can forward evidence files to your storage buckets. Enterprise DLP won't forward evidence files for Email DLP traffic matches if you don't enable this setting.Configure the S3 storage bucket for evidence file storage.
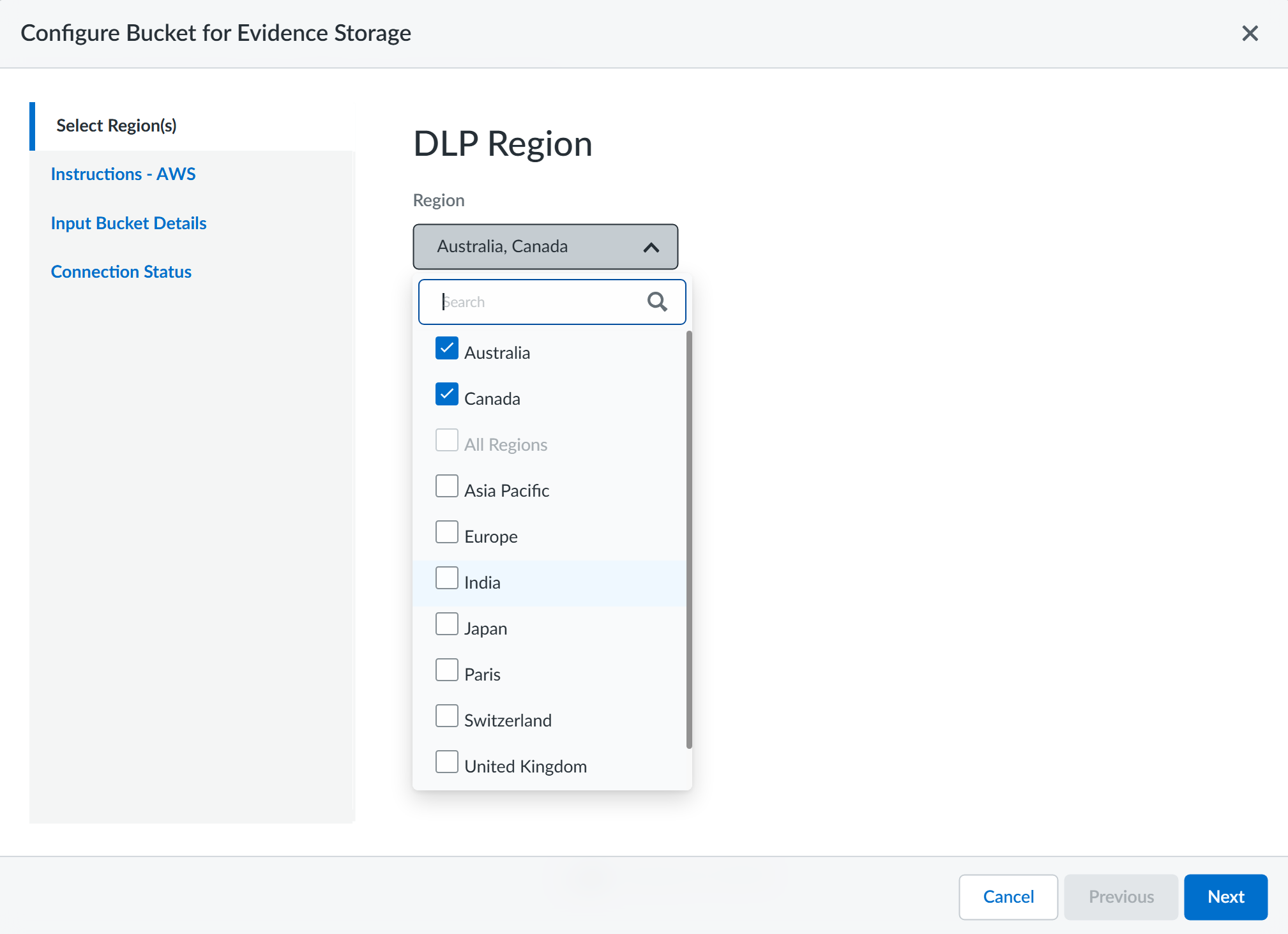
Click Next.Enter a descriptive Role name for the IAM role.Review the IAM role trust relationship and access policy.Create role.Log in to Strata Cloud Manager.Access to evidence storage settings and files on Strata Cloud Manager is allowed only for an account administrator or app administrator role with Enterprise DLP read and write privileges. This ensures that only the appropriate users have access to report data and evidence.(Email DLP only) Select ConfigurationSaaS SecuritySettingsEmail DLP Settings and enable Evidence Storage for Email DLP.You must enable the evidence storage service for Email DLP so Enterprise DLP can forward evidence files to your storage buckets. Enterprise DLP won't forward evidence files for Email DLP traffic matches if you don't enable this setting.Configure the S3 storage bucket for evidence file storage.- Select ConfigurationData Loss PreventionSettingsSensitive Data and select Configure Regional BucketAWS.Select the Region(s) from which you want to forward evidence files to the storage bucket.This setting specifies the regions where DLP incidents are generated. When DLP incidents are generated in the regions you select here, Enterprise DLP forwards the incident evidence to the storage bucket.
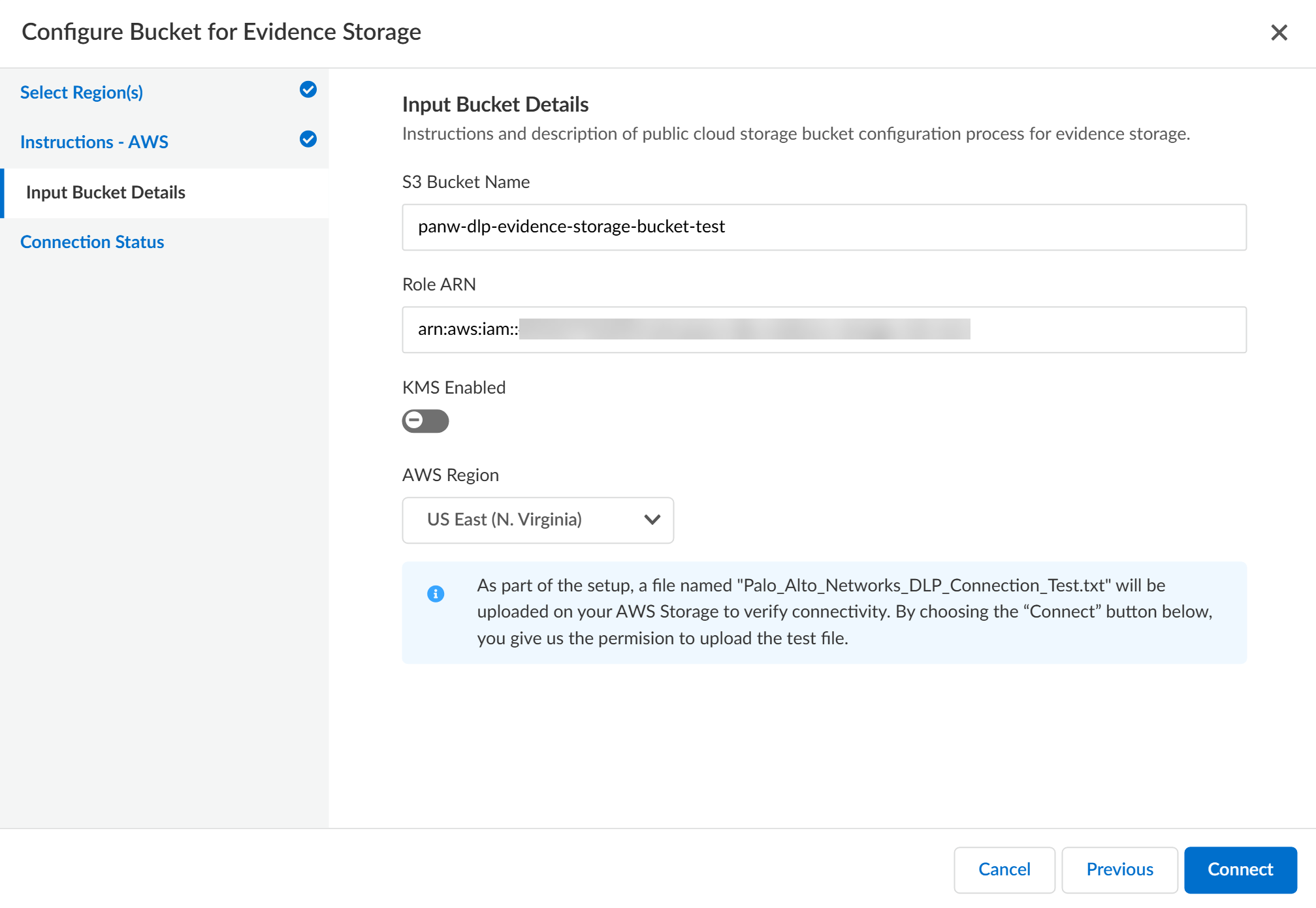
![]() Review the Instructions - AWS and click Next.Select Input Bucket Details.Enter the S3 Bucket Name of the bucket you created.The name you enter here must match the name of the S3 storage bucket on AWS.Enter the Role ARN for the IAM role you created.The IAM Role ARN can be found in the IAM role Permissions. The role ARN is displayed in the Summary.Select the AWS Region where the bucket is located.The region you select here corresponds to the region where you deployed your AWS storage bucket, and not the region where a DLP incident is generated.Connect Enterprise DLP to your S3 storage bucket.
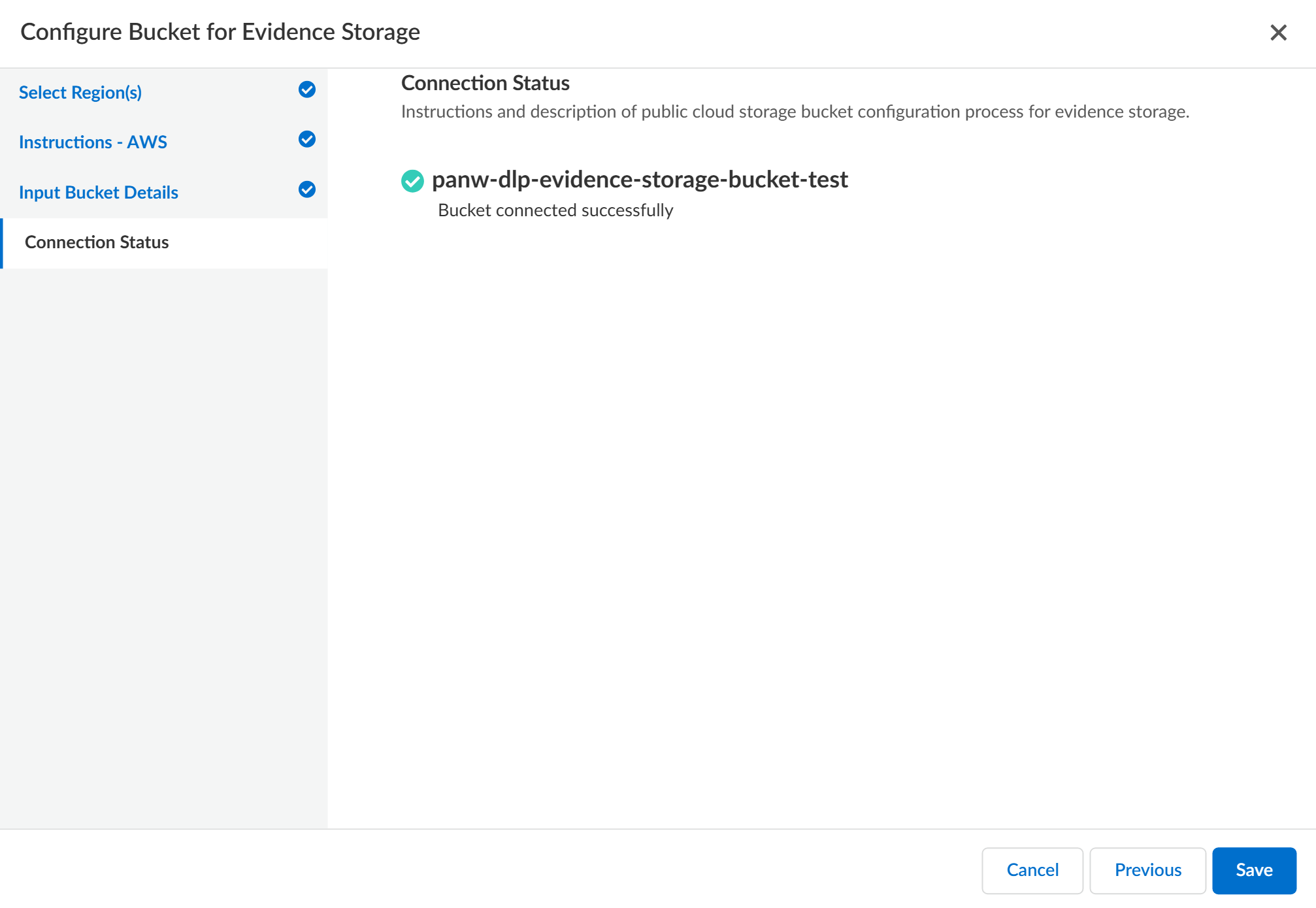
Review the Instructions - AWS and click Next.Select Input Bucket Details.Enter the S3 Bucket Name of the bucket you created.The name you enter here must match the name of the S3 storage bucket on AWS.Enter the Role ARN for the IAM role you created.The IAM Role ARN can be found in the IAM role Permissions. The role ARN is displayed in the Summary.Select the AWS Region where the bucket is located.The region you select here corresponds to the region where you deployed your AWS storage bucket, and not the region where a DLP incident is generated.Connect Enterprise DLP to your S3 storage bucket.![]() Review the Connection Status to verify Enterprise DLP successfully connected to your S3 storage bucket.As part of the setup process, Enterprise DLP uploads a Palo_Alto_Networks_DLP_Connection_Test.txt file to your S3 storage bucket to test and verify connectivity.Save the storage bucket settings if Enterprise DLP successfully connected.Select Previous and edit the bucket connection settings if Enterprise DLP can’t successfully connect to your S3 storage bucket.
Review the Connection Status to verify Enterprise DLP successfully connected to your S3 storage bucket.As part of the setup process, Enterprise DLP uploads a Palo_Alto_Networks_DLP_Connection_Test.txt file to your S3 storage bucket to test and verify connectivity.Save the storage bucket settings if Enterprise DLP successfully connected.Select Previous and edit the bucket connection settings if Enterprise DLP can’t successfully connect to your S3 storage bucket.![]() Enable Sensitive Files for your enforcement points.You can enable evidence storage of sensitive files for Prisma Access, NGFW, and Endpoint DLP. Enable evidence storage when prompted to confirm.
Enable Sensitive Files for your enforcement points.You can enable evidence storage of sensitive files for Prisma Access, NGFW, and Endpoint DLP. Enable evidence storage when prompted to confirm.Set up Evidence Storage on Strata Cloud Manager Using AWS KMS
Create an S3 storage bucket on AWS using the AWS Key Management Service (KMS) to store files that match your Enterprise Data Loss Prevention (E-DLP) data profiles on Strata Cloud Manager.- Review the setup prerequisites for Enterprise DLP and enable the required ports, full qualified domain names (FQDN), and IP addresses on your network.Create a public S3 storage bucket to store files scanned by Enterprise DLP.
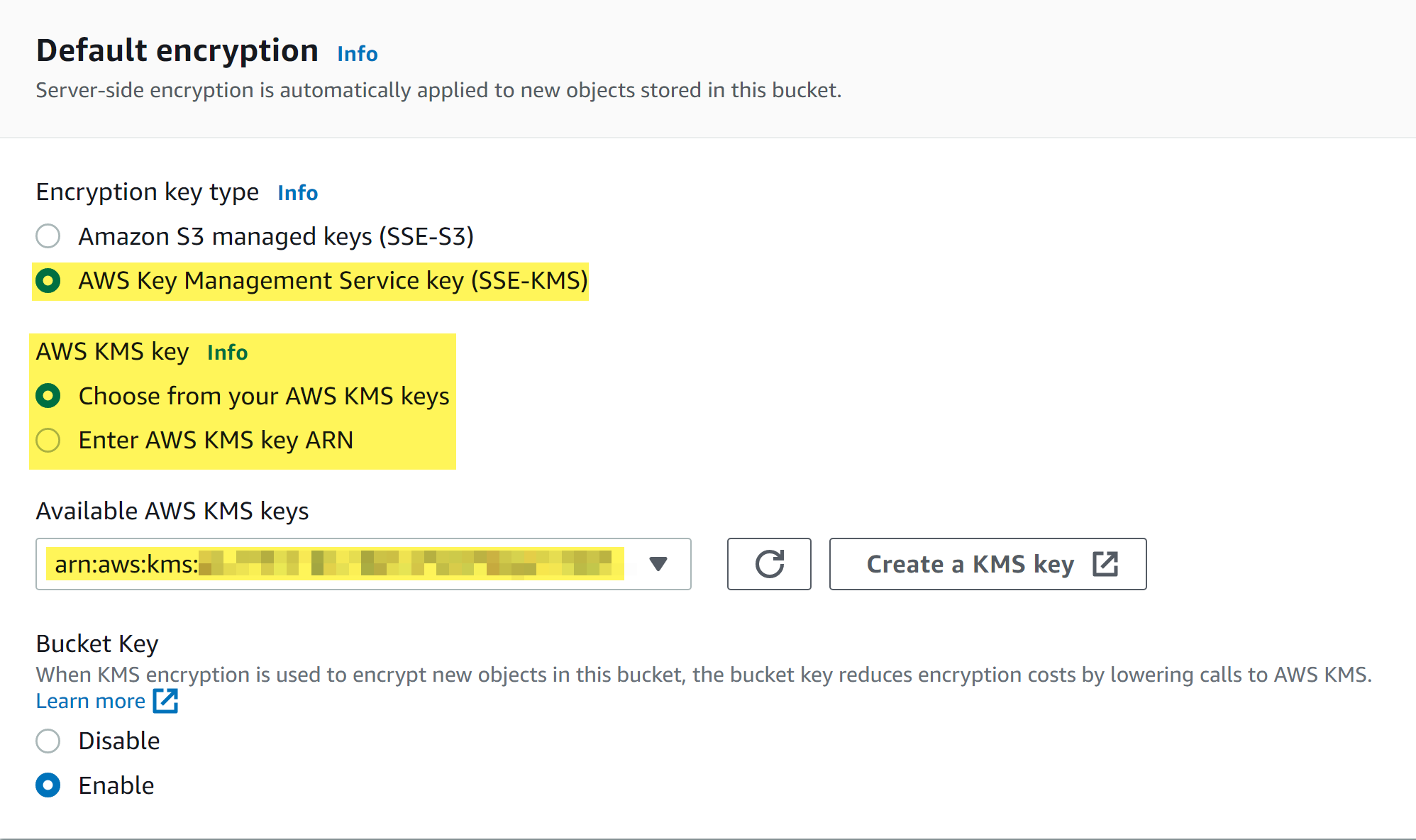
- Log in to the Amazon AWS console.Select ServicesStorageS3Buckets and Create bucket.Enter a descriptive Bucket name.Select the AWS Region for the S3 storage bucket.In the Default encryption section, select AWS Key Management Service (SSE-KMS) as the Encryption key type.To specify the AWS KMS key, you can Choose from your AWS KMS keys or you can Enter AWS key ARN.You can Create a KMS Key if one does not already exist. Refer to AWS Documentation for more information on creating a new KMS key.
![]() Create bucket.Obtain the ARN for the S3 storage bucket.After creating the S3 storage bucket, you're redirected back to the Buckets page. Search for and click the storage bucket you created.Click Properties. The storage bucket ARN is displayed in the Bucket overview.Enable the AWS KMS setting for the storage bucket and locate the trust relationship and access policy JSONs provided by Palo Alto Networks.
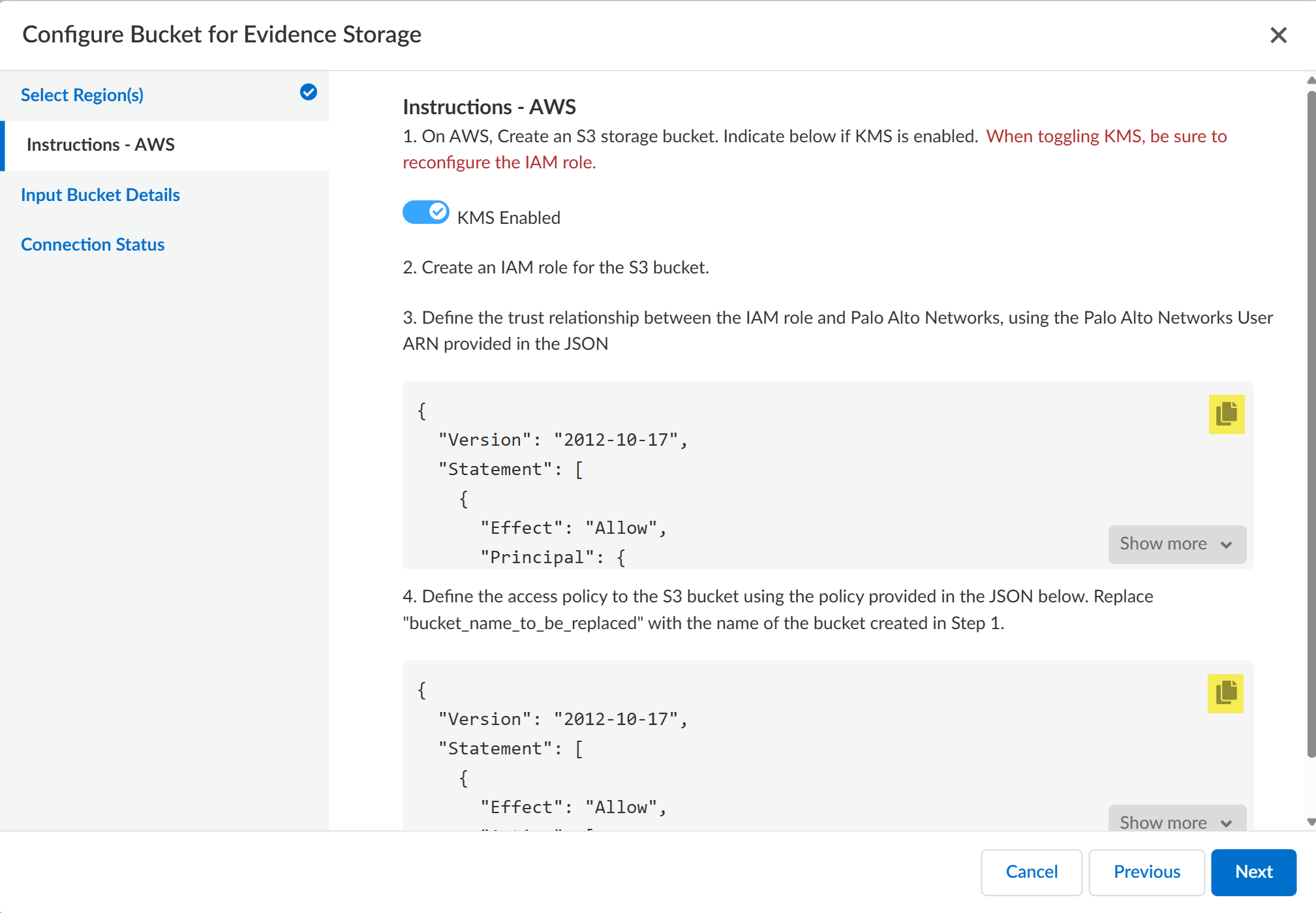
Create bucket.Obtain the ARN for the S3 storage bucket.After creating the S3 storage bucket, you're redirected back to the Buckets page. Search for and click the storage bucket you created.Click Properties. The storage bucket ARN is displayed in the Bucket overview.Enable the AWS KMS setting for the storage bucket and locate the trust relationship and access policy JSONs provided by Palo Alto Networks.- Log in to Strata Cloud Manager.Select ConfigurationData Loss PreventionSettingsSensitive Data.In Evidence Storage, select Configure BucketAWS as the Public Storage Bucket.Toggle KMS Enabled enable an S3 storage bucket using AWS KMS.In Instructions - AWS, locate the trust relationship and access policy JSON provided to define the trust relationship and access policy between the IAM role and Palo Alto Networks.The first JSON provided is the trust relationship and the second is the access policy. Highlighted are the copy buttons that you will use later on to create the IAM role for the S3 storage bucket.Leave the Configure Bucket for Evidence Storage display open and continue to create the IAM role for the S3 storage bucket in a separate browser window.
![]() Create the IAM role for the S3 storage bucket.This role is required to allow Enterprise DLP to write to the S3 storage bucket.
Create the IAM role for the S3 storage bucket.This role is required to allow Enterprise DLP to write to the S3 storage bucket.- Log in to the Amazon AWS console.Select ServicesSecurity, Identity, and ComplianceIAMAccess managementRoles and Create role.Select Custom trust policy.For the Trusted entity type, select Custom trust policy.Return to Strata Cloud Manager and copy the trust relationship JSON.In the Amazon AWS console, paste the trust relationship JSON into the Custom trust policy to configure the trust policy.
![]() Click Next.In Add permissions, select Create policyJSON.A new window is automatically opened in your browser to create the new access policy.Return to Strata Cloud Manager and copy the access policy JSON.In the Amazon AWS console, paste the access policy JSON into the Policy editor.Add the bucket ARN for the S3 storage bucket you created.Throughout the JSON, you must replace all instances of bucket_name_to_be_replaced with the S3 storage bucket ARN you created.
Click Next.In Add permissions, select Create policyJSON.A new window is automatically opened in your browser to create the new access policy.Return to Strata Cloud Manager and copy the access policy JSON.In the Amazon AWS console, paste the access policy JSON into the Policy editor.Add the bucket ARN for the S3 storage bucket you created.Throughout the JSON, you must replace all instances of bucket_name_to_be_replaced with the S3 storage bucket ARN you created.![]() Add the AWS KMS key ARN.The AWS KMS ARN you add here must be the same AWS KMS Key ARN you provided when you created the S3 storage bucket.
Add the AWS KMS key ARN.The AWS KMS ARN you add here must be the same AWS KMS Key ARN you provided when you created the S3 storage bucket.![]() Click Next.Enter a Policy name and Create policy.Return to the browser window where you're creating the IAM role,Search for and select the access policy you created.
Click Next.Enter a Policy name and Create policy.Return to the browser window where you're creating the IAM role,Search for and select the access policy you created.![]() Click Next.Enter a descriptive Role name for the IAM role.Review the IAM role trust relationship and access policy.Create role.Log in to Strata Cloud Manager.Access to evidence storage settings and files on Strata Cloud Manager is allowed only for an account administrator or app administrator role with Enterprise DLP read and write privileges. This ensures that only the appropriate users have access to report data and evidence.(Email DLP only) Select ConfigurationSaaS SecuritySettingsEmail DLP Settings and enable Evidence Storage for Email DLP.You must enable the evidence storage service for Email DLP so Enterprise DLP can forward evidence files to your storage buckets. Enterprise DLP won't forward evidence files for Email DLP traffic matches if you don't enable this setting.Configure the S3 storage bucket for evidence file storage.
Click Next.Enter a descriptive Role name for the IAM role.Review the IAM role trust relationship and access policy.Create role.Log in to Strata Cloud Manager.Access to evidence storage settings and files on Strata Cloud Manager is allowed only for an account administrator or app administrator role with Enterprise DLP read and write privileges. This ensures that only the appropriate users have access to report data and evidence.(Email DLP only) Select ConfigurationSaaS SecuritySettingsEmail DLP Settings and enable Evidence Storage for Email DLP.You must enable the evidence storage service for Email DLP so Enterprise DLP can forward evidence files to your storage buckets. Enterprise DLP won't forward evidence files for Email DLP traffic matches if you don't enable this setting.Configure the S3 storage bucket for evidence file storage.- Select ConfigurationData Loss PreventionSettingsSensitive Data and select Configure Regional BucketAWS.Select the Region(s) from which you want to forward evidence files to the storage bucket.This setting specifies the regions where DLP incidents are generated. When DLP incidents are generated in the regions you select here, Enterprise DLP forwards the incident evidence to the storage bucket.
![]() Review the Instructions - AWS and click Next.Select Input Bucket Details.Enter the S3 Bucket Name of the bucket you created.The name you enter in Strata Cloud Manager must match the name of the S3 storage bucket on AWS.Enter the Role ARN for the IAM role you created.The IAM Role ARN can be found in the IAM role Permissions. The role ARN is displayed in the Summary.Select the AWS Region where the bucket is located.The region you select here corresponds to the region where you deployed your AWS storage bucket, and not the region where a DLP incident is generated.Connect Enterprise DLP to your S3 storage bucket.
Review the Instructions - AWS and click Next.Select Input Bucket Details.Enter the S3 Bucket Name of the bucket you created.The name you enter in Strata Cloud Manager must match the name of the S3 storage bucket on AWS.Enter the Role ARN for the IAM role you created.The IAM Role ARN can be found in the IAM role Permissions. The role ARN is displayed in the Summary.Select the AWS Region where the bucket is located.The region you select here corresponds to the region where you deployed your AWS storage bucket, and not the region where a DLP incident is generated.Connect Enterprise DLP to your S3 storage bucket.![]() Review the Connection Status to verify Enterprise DLP successfully connected to your S3 storage bucket.As part of the setup process, Enterprise DLP uploads a Palo_Alto_Networks_DLP_Connection_Test.txt file to your S3 storage bucket to test and verify connectivity.Save the storage bucket settings if Enterprise DLP successfully connected.Select Previous and edit the bucket connection settings if Enterprise DLP can’t successfully connect to your S3 storage bucket.
Review the Connection Status to verify Enterprise DLP successfully connected to your S3 storage bucket.As part of the setup process, Enterprise DLP uploads a Palo_Alto_Networks_DLP_Connection_Test.txt file to your S3 storage bucket to test and verify connectivity.Save the storage bucket settings if Enterprise DLP successfully connected.Select Previous and edit the bucket connection settings if Enterprise DLP can’t successfully connect to your S3 storage bucket.![]() Enable Sensitive Files for your enforcement points.You can enable evidence storage of sensitive files for Prisma Access, NGFW, and Endpoint DLP. Enable evidence storage when prompted to confirm.
Enable Sensitive Files for your enforcement points.You can enable evidence storage of sensitive files for Prisma Access, NGFW, and Endpoint DLP. Enable evidence storage when prompted to confirm.