GlobalProtect
Use the GlobalProtect App for Android
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
- 10.1 & Later
- 9.1 (EoL)
-
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
-
- 6.1
- 6.0
- 5.1
-
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
Use the GlobalProtect App for Android
Learn how to navigate and use the GlobalProtect App for
Android version 6.0.
The first time you launch the GlobalProtect
app for Android, you will be prompted to read and acknowledge a
disclosure about the information that may be collected by the app.
After that, the way you proceed depends on how your administrator
has configured the app. In some cases, you will automatically be
logged in to GlobalProtect and connected to your corporate network
after acknowledging the disclosure. Or, your administrator may have
configured the app to require you to enter the GlobalProtect portal
address and/or supply your domain credentials to authenticate to
GlobalProtect.
- On-Demand (Remote Access VPN) connection experience:When your GlobalProtect administrator configures GlobalProtect with the On-Demand connect method, you must launch the GlobalProtect app to initiate the connection manually. After the connection initiates, you can TAP TO CONNECT to establish the GlobalProtect connection. If your administrator enables GlobalProtect to save your user credentials, the connection establishes without requiring further user interaction. Otherwise you will need to enter your credentials to connect to GlobalProtect and access your organization’s resources.
![]()
- Always On connection experience:When your GlobalProtect administrator configures GlobalProtect with the Always On connect method, the connection initiates automatically. Depending on whether your administrator configures the GlobalProtect app to save your user credentials, you can establish the GlobalProtect connection without launching the app. If your administrator enables GlobalProtect to save your credentials, the connection establishes automatically without requiring any user interaction. Otherwise you will need to enter your credentials to connect.
![]()
- Install the GlobalProtect app for Android and then launch the app.The first time you connect using the GlobalProtect app for Android, read the disclosure about the information GlobalProtect may collect or access on your device and then click OK to acknowledge and dismiss the message.
![]() If prompted, enter the following information:The information you need to supply depends on how your administrator has configured the app.
If prompted, enter the following information:The information you need to supply depends on how your administrator has configured the app.- Enter the GlobalProtect portal address.
![]()
- (Optional) Depending on the connection mode, tap Connect to initiate the connection.
- (Optional) If your endpoint is unable to verify the identity of the GlobalProtect portal using the portal server certificate, the Cannot Verify Server Identity message appears. If you trust the certificate, tap Continue to proceed with the connection.
- (Optional) If prompted, enter your Username and Password and then SIGN IN.If your administrator has allowed you to use biometric (fingerprint) information to sign in, you need to first sign-in with a username and password; you can then use biometric information to sign in.
![]()
- When the Connection request message appears, tap OK to allow GlobalProtect to set up a VPN connection on your endpoint.
![]()
- (Optional) If you are using multi-factor authentication, enter the GlobalProtect verification Code that is sent to your endpoint after you sign in, and then tap Continue.
- (Optional) If your administrator configures the GlobalProtect app to display a welcome message, the welcome message appears upon successful connection. Tap outside of the welcome message to proceed to the home screen.
![]()
- (Optional) If there are notifications on your app, the Notifications dialog appears upon successful connection. Close the Notifications dialog to proceed to the home screen.
![]()
- When the home screen appears, verify that your connection has established successfully. If the connection is successful, the home screen displays the CONNECTED state.
![]()
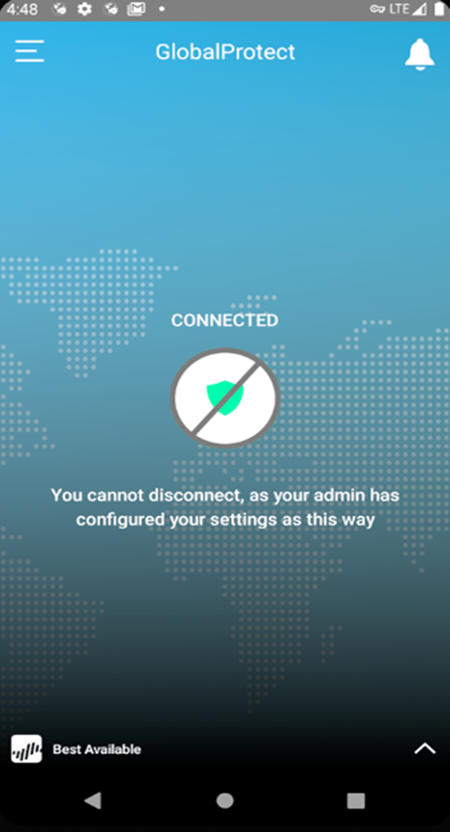
- (Optional) If your administrator has configured GlobalProtect with the Always On connect method, the connection initiates automatically. The home screen displays CONNECTED state.
![]() With the Always On connect method, the home screen displays CONNECTED state with a disconnect message to prevent you from disconnecting when you try to tap the Connect icon.
With the Always On connect method, the home screen displays CONNECTED state with a disconnect message to prevent you from disconnecting when you try to tap the Connect icon.![]()
- (Optional) By default, the endpoint automatically connects to the Best Available gateway based on the configuration that the administrator defines and the response times of the available gateways. To connect to a different gateway, tap the gateway drop-down at the bottom of the home screen, and then select a gateway from the list (external gateways only).
View information about your GlobalProtect connection.After you establish the GlobalProtect connection, launch the GlobalProtect app. Tap the settings icon to open the settings menu. From the settings menu, tap SETTINGS to view information about your connection, including the Portal address and connection Status.![]()
- If you want to connect to a different GlobalProtect portal, tap the Portal address. When prompted, enter a new portal address and then tap CONNECT.
![]()
- If you are connected to an external gateway, tap the connection Status to view additional details about your connection (including the network SSID and gateway IP address/FQDN).
![]()
(Optional) Change your saved password.If your GlobalProtect administrator configures the GlobalProtect portal app to save your user credentials, you will not need to enter them every time you connect. When your password expires or a RADIUS or AD administrator requires a password change at the next login, you can update your password on the app. This feature is enabled only when you are authenticated with a RADIUS server using the Protected Extensible Authentication Protocol Microsoft Challenge Handshake Authentication Protocol version 2 (PEAP-MSCHAPv2).- Launch the GlobalProtect app.From the home screen, TAP TO CONNECT.(Optional) If prompted, enter your old Username and Password, and then SIGN IN.When the GlobalProtect app prompts you to Update Password, enter your Current Password followed by your New Password.Retype Password to confirm your new password.SIGN IN to reconnect to GlobalProtect with your new password.(Optional) Disconnect from GlobalProtect.If your administrator configures GlobalProtect with the On-Demand connect method, you can TAP TO DISCONNECT from the home screen.
![]()