Add an Identity Federation Through Common Services
Table of Contents
Expand all | Collapse all
- Get Started with Common Services: Identity & Access
-
- Add an Identity Federation
- Manually Configure a SAML Identity Provider
- Upload SAML Identity Provider Metadata
- Get the URL of a SAML Identity Provider
- Clone SAML Identity Provider Configuration
- Add or Delete an Identity Federation Owner
- Configure Palo Alto Networks as a Service Provider
- Delete an Identity Federation
- Map a Tenant for Authorization
- Update Tenant Mapping for Authorization
- PAN Resource Name Mapping Properties
- Manage Single Tenant Transition to Multitenant
- Release Updates
Add an Identity Federation Through Common Services
Learn how to add an identity federation through the Common Services.
Common Services enables you to integrate
with a third party identity provider (IDP) to allow access to the
platform, rather than adding users directly to the platform itself.
Identity Federation enables users of different enterprises or domains to use the same digital
identity to access all their applications. Technologies for identity federation
often include Security Assertion Markup Language (SAML), OAuth, OpenID, and more.
Common Services supports SAML and the following IDPs:
- Okta
- Azure
- Ping
- Onelogin
- SecureAuth
- Google Workspace
- Microsoft Active Directory Federation Service (AD FS)
- Any other IDPs that follow the SAML standard
You can add and verify an identity federation from Common ServicesIdentity & AccessIdentity Federations.
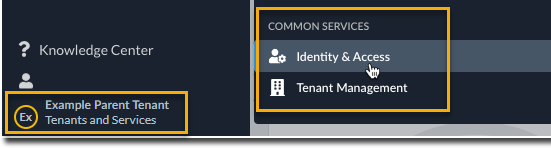
- Use one of the various ways to access Common ServicesIdentity & Access.Select Identity & Access. Only one way is shown here.
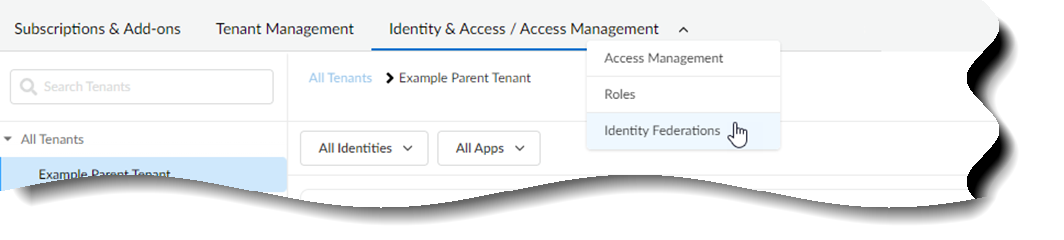
![]() Select Identity & Access/Access ManagementIdentity FederationsAdd Identity Federation to add an identity federation.
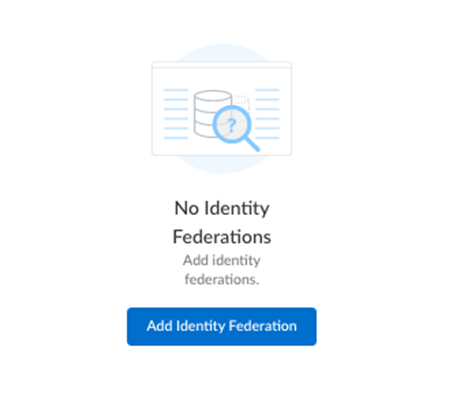
Select Identity & Access/Access ManagementIdentity FederationsAdd Identity Federation to add an identity federation.![]()
![]() Add the Domain information for your enterprise. The character limit is 50. Special characters are not allowed, with the exception of “-” and “.”Select Next.Follow the Instructions for Verification to add a DNS record within your domain name provider.
Add the Domain information for your enterprise. The character limit is 50. Special characters are not allowed, with the exception of “-” and “.”Select Next.Follow the Instructions for Verification to add a DNS record within your domain name provider.- Copy the TXT record from the Common Services.
- Select Finish.
- Go to your domain provider’s console and paste the TXT record, so that Palo Alto Networks can verify that you are an owner of the domain. The console details look similar to the following, but all providers are slightly different.
![]()
- (Optional) In the domain provider’s console, revise your identity provider’s time to live (TTL) setting if you need a faster refresh rate. The TTL setting impacts, for example, how long it takes to verify ownership of the identity federation.
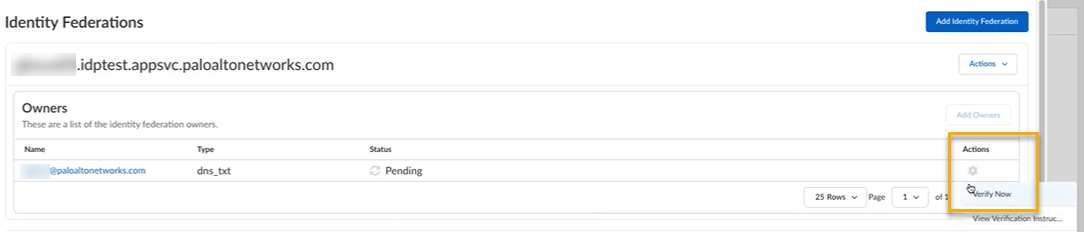
In Common Services, select Verify Now to verify ownership of the identity federation.![]() (Optional) Add additional owners to manage the identity federation.Configure a Security Assertion Markup Language (SAML) provider in one of the following ways:
(Optional) Add additional owners to manage the identity federation.Configure a Security Assertion Markup Language (SAML) provider in one of the following ways: