AI Access Security
Tag GenAI Apps in the Application Config
Table of Contents
Expand All
|
Collapse All
AI Access Security Docs
Tag GenAI Apps in the Application Config
Apply tags to the application to reflect whether a GenAI app is approved within your
organization from the Application config in Strata Cloud Manager.
- Log in to Strata Cloud Manager.Associate the predefined Application-Tagging snippet with appropriate Configuration Scope to support tag-based policy enforcement.Obtain the child App-IDs you want to tag.You can obtain the child App-IDs for a GenAI app using one of the following ways.
- Use the AI Access Security Insights dashboard to discover risks posed by GenAI apps. AI Access Security Insights shows you the detected child App-IDs used across your organization.
- Review the list of supported GenAI apps.
- Use Applipedia to search for the child App-IDs of supported GenAI apps delivered through a dynamic content update.Applipedia only displays App-IDs for apps delivered through a dynamic content, and doesn't display apps delivered through App-ID Cloud Engine (ACE).
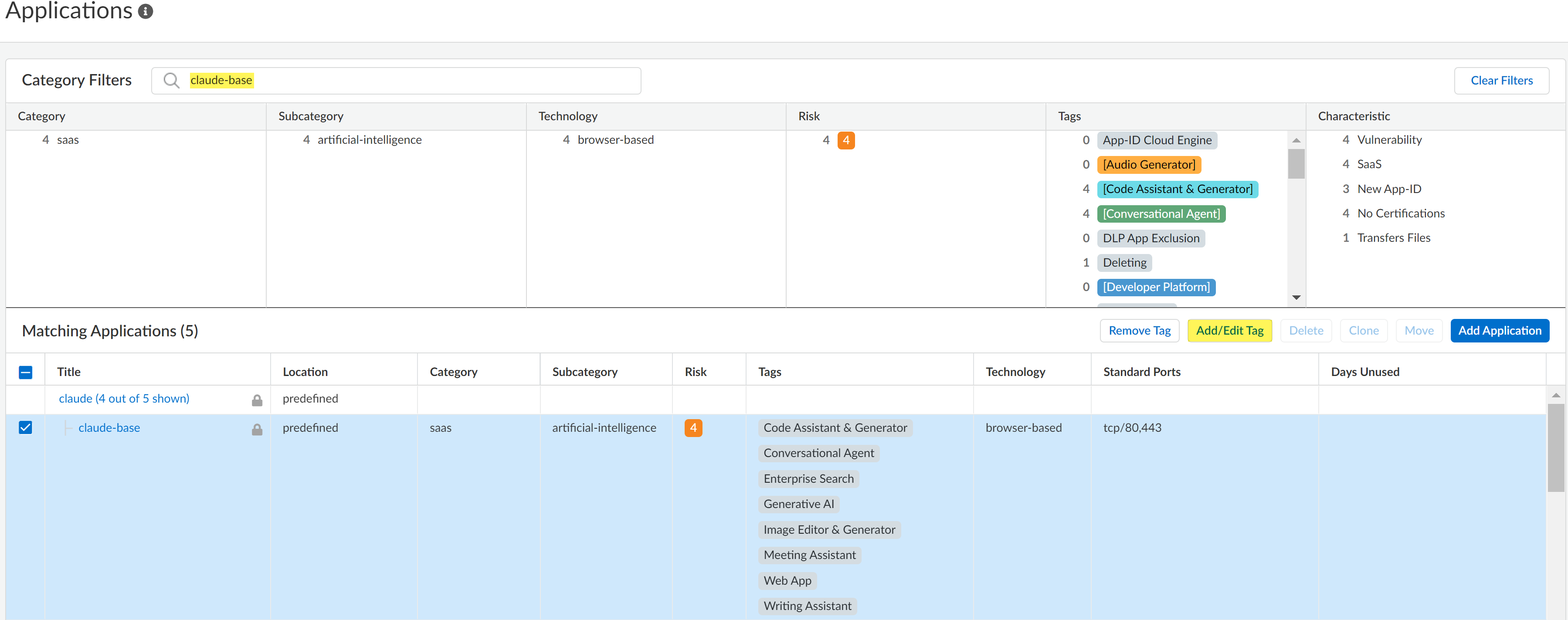
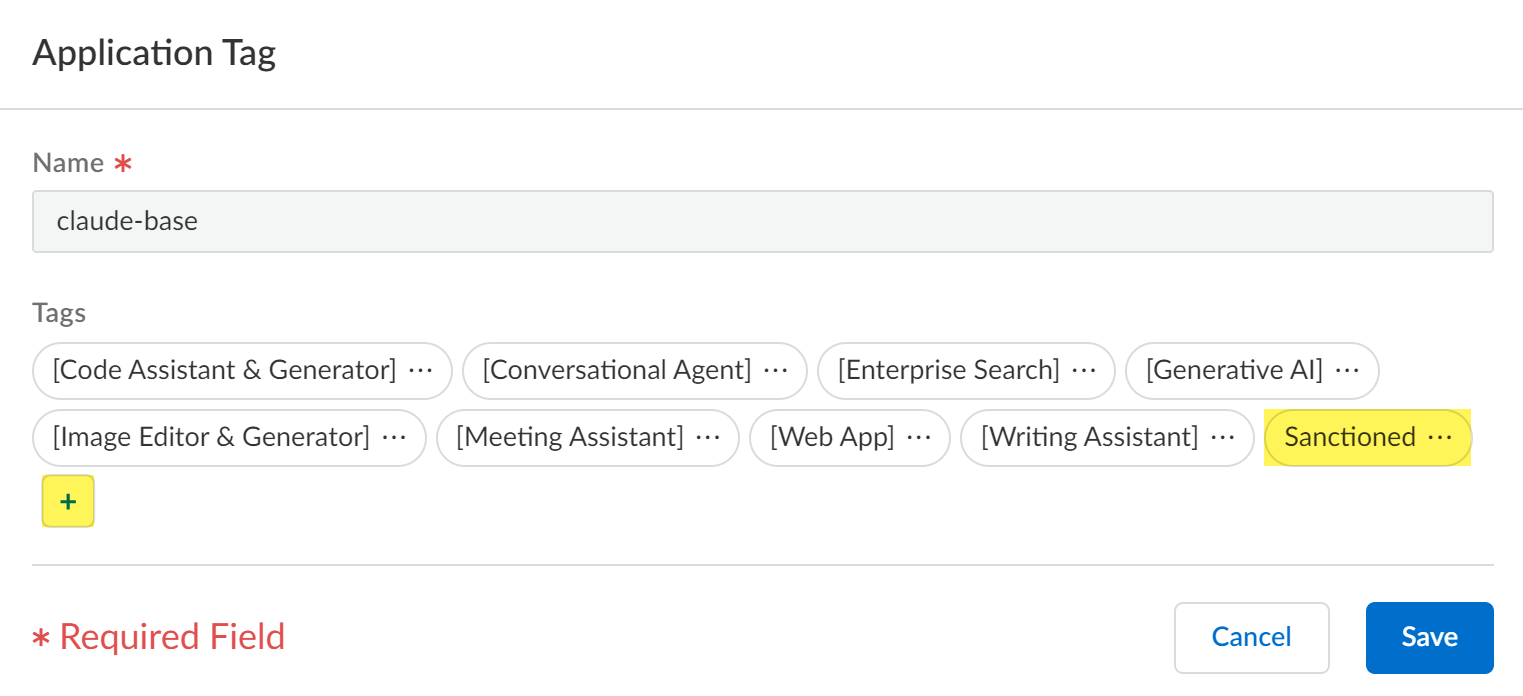
Select ConfigurationNGFW and Prisma AccessObjectsApplicationApplications.In the Configuration Scope, select the Application-Tagging snippet.If you are tagging an App-ID delivered through App-ID Cloud Engine (ACE), then all NGFW or Prisma Access tenants associated with the selected folder must be configured to receive App-ID updates from ACE.ACE is enabled by default for a NGFW or Prisma Access tenant when they have an active SaaS Security Inline or AI Access Security license. You can also manually enable ACE for your NGFW.The configuration push fails if you tag an App-ID delivered from ACE and at least one NGFW or Prisma Access tenant associated with the selected folder isn't configured to receive App-IDs from ACE.For this reason, Palo Alto Networks doesn't recommend selecting the Global Configuration Scope.In the Category Filters search field, enter the App-ID you want to tag and select it.You can only tag one App-ID at a time.Add/Edit Tag.![]() Click + to apply a predefined Sanctioned or Tolerated application tag.In this example, the claude-base App-ID is tagged with the Sanctioned tag.An app is assumed as Unsanctioned in the absence of the Sanctioned or Tolerated tags if tagging from Applications.If you want to change the app tag from Sanctioned or Tolerated to Unsanctioned, you need to remove the existing tag. You can't manually tag an app as Unsanctioned from Applications.Save.
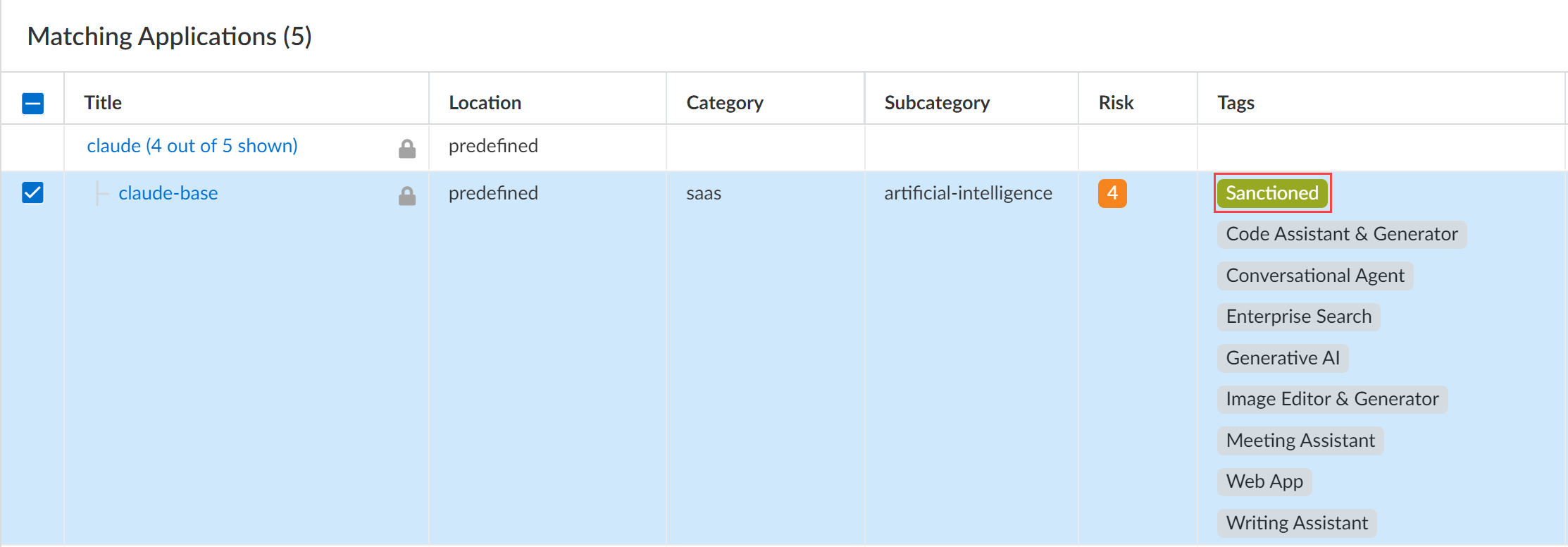
Click + to apply a predefined Sanctioned or Tolerated application tag.In this example, the claude-base App-ID is tagged with the Sanctioned tag.An app is assumed as Unsanctioned in the absence of the Sanctioned or Tolerated tags if tagging from Applications.If you want to change the app tag from Sanctioned or Tolerated to Unsanctioned, you need to remove the existing tag. You can't manually tag an app as Unsanctioned from Applications.Save.![]() Review the values in the Tag column to verify you successfully applied the application tag.
Review the values in the Tag column to verify you successfully applied the application tag.![]() Click Overview.Push Config and Push your configuration changes.
Click Overview.Push Config and Push your configuration changes.