Manage the Master Key from Panorama
Table of Contents
11.1 & Later
Expand all | Collapse all
-
- Determine Panorama Log Storage Requirements
-
- Setup Prerequisites for the Panorama Virtual Appliance
- Perform Initial Configuration of the Panorama Virtual Appliance
- Set Up The Panorama Virtual Appliance as a Log Collector
- Set Up the Panorama Virtual Appliance with Local Log Collector
- Set up a Panorama Virtual Appliance in Panorama Mode
- Set up a Panorama Virtual Appliance in Management Only Mode
-
- Add a Virtual Disk to Panorama on an ESXi Server
- Add a Virtual Disk to Panorama on vCloud Air
- Add a Virtual Disk to Panorama on Alibaba Cloud
- Add a Virtual Disk to Panorama on AWS
- Add a Virtual Disk to Panorama on Azure
- Add a Virtual Disk to Panorama on Google Cloud Platform
- Add a Virtual Disk to Panorama on KVM
- Add a Virtual Disk to Panorama on Hyper-V
- Add a Virtual Disk to Panorama on Oracle Cloud Infrastructure (OCI)
-
- Increase CPUs and Memory for Panorama on an ESXi Server
- Increase CPUs and Memory for Panorama on vCloud Air
- Increase CPUs and Memory for Panorama on Alibaba Cloud
- Increase CPUs and Memory for Panorama on AWS
- Increase CPUs and Memory for Panorama on Azure
- Increase CPUs and Memory for Panorama on Google Cloud Platform
- Increase CPUs and Memory for Panorama on KVM
- Increase CPUs and Memory for Panorama on Hyper-V
- Increase the CPUs and Memory for Panorama on Oracle Cloud Infrastructure (OCI)
- Complete the Panorama Virtual Appliance Setup
-
- Convert Your Evaluation Panorama to a Production Panorama with Local Log Collector
- Convert Your Evaluation Panorama to a Production Panorama without Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing with Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing without Local Log Collector
- Convert Your Production Panorama to an ELA Panorama
-
- Register Panorama
- Activate a Panorama Support License
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is Internet-connected
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is not Internet-connected
- Activate/Retrieve a Firewall Management License on the M-Series Appliance
- Install the Panorama Device Certificate
- Install the Device Certificate for a Dedicated Log Collector
-
- Prepare Panorama for Migration - Checklist and Prerequisites
- Migrate Panorama SC3 Certificates During Appliance Migration
- Migrate from a Panorama Virtual Appliance to an M-Series Appliance
- Migrate a Panorama Virtual Appliance to a Different Hypervisor
- Migrate from an M-Series Appliance to a Panorama Virtual Appliance
- Migrate from an M-500 Appliance to an M-700 Appliance
- Migrate from an M-600 Appliance to an M-700 Appliance
-
- Configure an Admin Role Profile
- Configure an Admin Role Profile for Selective Push to Managed Firewalls
- Configure an Access Domain
-
- Configure a Panorama Administrator Account
- Configure Local or External Authentication for Panorama Administrators
- Configure a Panorama Administrator with Certificate-Based Authentication for the Web Interface
- Configure an Administrator with SSH Key-Based Authentication for the CLI
- Configure RADIUS Authentication for Panorama Administrators
- Configure TACACS+ Authentication for Panorama Administrators
- Configure SAML Authentication for Panorama Administrators
- Enable SCP Uploads for an Administrator
- Configure Tracking of Administrator Activity
-
- Add a Firewall as a Managed Device
- Change Between Panorama Management and Cloud Management
-
- Add a Device Group
- Move a Firewall to a Different Device Group
- Create a Device Group Hierarchy
- Create Objects for Use in Shared or Device Group Policy
- Revert to Inherited Object Values
- Manage Unused Shared Objects
- Manage Precedence of Inherited Objects
- Move or Clone a Policy Rule or Object to a Different Device Group
- Push a Policy Rule to a Subset of Firewalls
- Device Group Push to a Multi-VSYS Firewall
- Manage the Rule Hierarchy
- Manage the Master Key from Panorama
- Schedule a Configuration Push to Managed Firewalls
- Redistribute Data to Managed Firewalls
-
- Plan the Transition to Panorama Management
- Migrate a Firewall to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall to Panorama Management and Push a New Configuration
- Migrate a Firewall HA Pair to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall HA Pair to Panorama Management and Push a New Configuration
- Load a Partial Firewall Configuration into Panorama
- Localize a Panorama Pushed Configuration on a Managed Firewall
-
- Configure a Managed Collector
- Monitor Managed Collector Health Status
- Configure Log Forwarding to Panorama
- Configure Syslog Forwarding to External Destinations
- Forward Logs to Strata Logging Service
- Verify Log Forwarding to Panorama
- Modify Log Forwarding and Buffering Defaults
- Configure Log Forwarding from Panorama to External Destinations
-
- Add Standalone WildFire Appliances to Manage with Panorama
- Remove a WildFire Appliance from Panorama Management
-
-
- Configure a Cluster and Add Nodes on Panorama
- Configure General Cluster Settings on Panorama
- Remove a Cluster from Panorama Management
- Configure Appliance-to-Appliance Encryption Using Predefined Certificates Centrally on Panorama
- Configure Appliance-to-Appliance Encryption Using Custom Certificates Centrally on Panorama
- View WildFire Cluster Status Using Panorama
-
-
- Preview, Validate, or Commit Configuration Changes
- Commit Selective Configuration Changes for Managed Devices
- Push Selective Configuration Changes to Managed Devices
- Enable Automated Commit Recovery
- Compare Changes in Panorama Configurations
- Manage Locks for Restricting Configuration Changes
- Add Custom Logos to Panorama
- Use the Panorama Task Manager
- Reboot or Shut Down Panorama
- Configure Panorama Password Profiles and Complexity
-
-
- Verify Panorama Port Usage
- Resolve Zero Log Storage for a Collector Group
- Replace a Failed Disk on an M-Series Appliance
- Replace the Virtual Disk on an ESXi Server
- Replace the Virtual Disk on vCloud Air
- Migrate Logs to a New M-Series Appliance in Log Collector Mode
- Migrate Logs to a New M-Series Appliance in Panorama Mode
- Migrate Logs to a New M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Logs to the Same M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Log Collectors after Failure/RMA of Non-HA Panorama
- Regenerate Metadata for M-Series Appliance RAID Pairs
- View Log Query Jobs
- Troubleshoot Registration or Serial Number Errors
- Troubleshoot Reporting Errors
- Troubleshoot Device Management License Errors
- Troubleshoot Automatically Reverted Firewall Configurations
- View Task Success or Failure Status
- Generate a Stats Dump File for a Managed Firewall
- Recover Managed Device Connectivity to Panorama
- Restore an Expired Device Certificate
Manage the Master Key from Panorama
Deploy new, or renew expiring master keys, to firewalls,
log collectors, and WF-500 appliances from the Panorama™ management
server.
Panorama, firewalls, Log Collectors, and WF-500
appliances use a master key to encrypt sensitive elements in the
configuration and they have a default master key they use to encrypt
passwords and configuration elements. As part of a standard security
practice, you should replace the default master key and change the
key on each individual firewall, Log Collector, WildFire appliance,
and Panorama before it expires.
To strengthen your security
posture, configuring a unique master key for Panorama and for each
managed firewall. By configuring unique master keys, you can ensure that
a compromised master key does not compromise the configuration encryption of
your entire deployment. Unique master keys are supported only for
Panorama and managed firewalls. Log Collectors and WildFire appliances
must share the same master key as Panorama. For Panorama or managed
firewalls in a high availability (HA) configuration, you must deploy
the same master key for both HA peers as the master key is not synchronized
across HA peers.
The default encryption algorithm that the master key uses to encrypt data is
AES-256-CBC—the same algorithm that the master key used prior to PAN-OS 10.0.
AES-256-CBC is the default encryption level because when you manage firewalls with
Panorama, the managed firewalls may be on different PAN-OS releases, and firewalls
on PAN-OS releases earlier than PAN-OS 10.0 do not support AES-256-GCM. This is why
Panorama must use the lowest level of encryption that its managed devices can use.
For example, if some managed devices run PAN-OS 10.0 and some run earlier versions,
Panorama must use AES-256-CBC. However, if all managed devices run PAN-OS 10.0 or
later, then Panorama and all of its managed devices can use AES-256-GCM.
Palo Alto Networks recommends using AES 256-GCM level 2 for master key
encryption.
Configuring a unique master key also eases
the operational burden of updating your master keys. By configuring
a unique master key for a managed firewall, you can update each
master key individually without the need to coordinate changing
the master key across a large number of managed firewalls.
When a master key expires, you must enter
the current master key in order to configure a new master key.
Be
sure to keep track of the master key you deploy to your managed
firewalls, Log Collectors, and WildFire appliances because master
keys cannot be recovered. you must reset to factory default if you
cannot provide the current master key when it expires.
- Log in to the Panorama Web Interface.(Best Practice) Select Commit and Commit and Push any pending configuration changes.Panorama must re-encrypt data using the new master key. To ensure all configuration elements are encrypted with the new master key, you should commit all pending changes before deploying the new master key.Configure a unique master key for a managed firewall.
- (HA only) Disable Config Sync for managed firewalls.This step is required before deploying a new master key to a firewall HA pair
- Select DeviceHigh AvailabilityGeneral and select the Template containing the managed firewall HA configuration.
- Edit the HA Pair Settings Setup.
- Disable (clear) Enable Config Sync and click OK.
- Commit and Commit and Push your configuration changes.
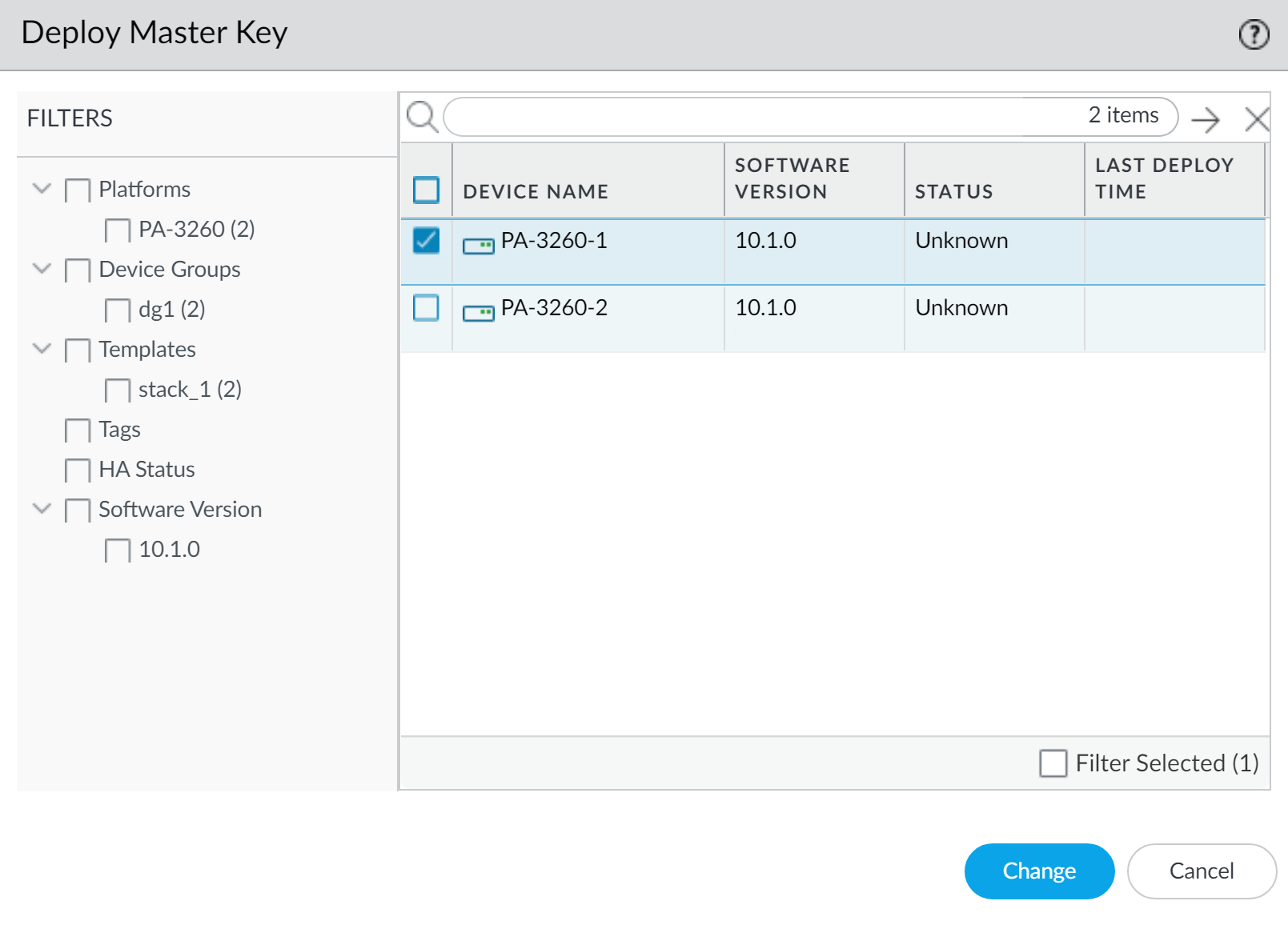
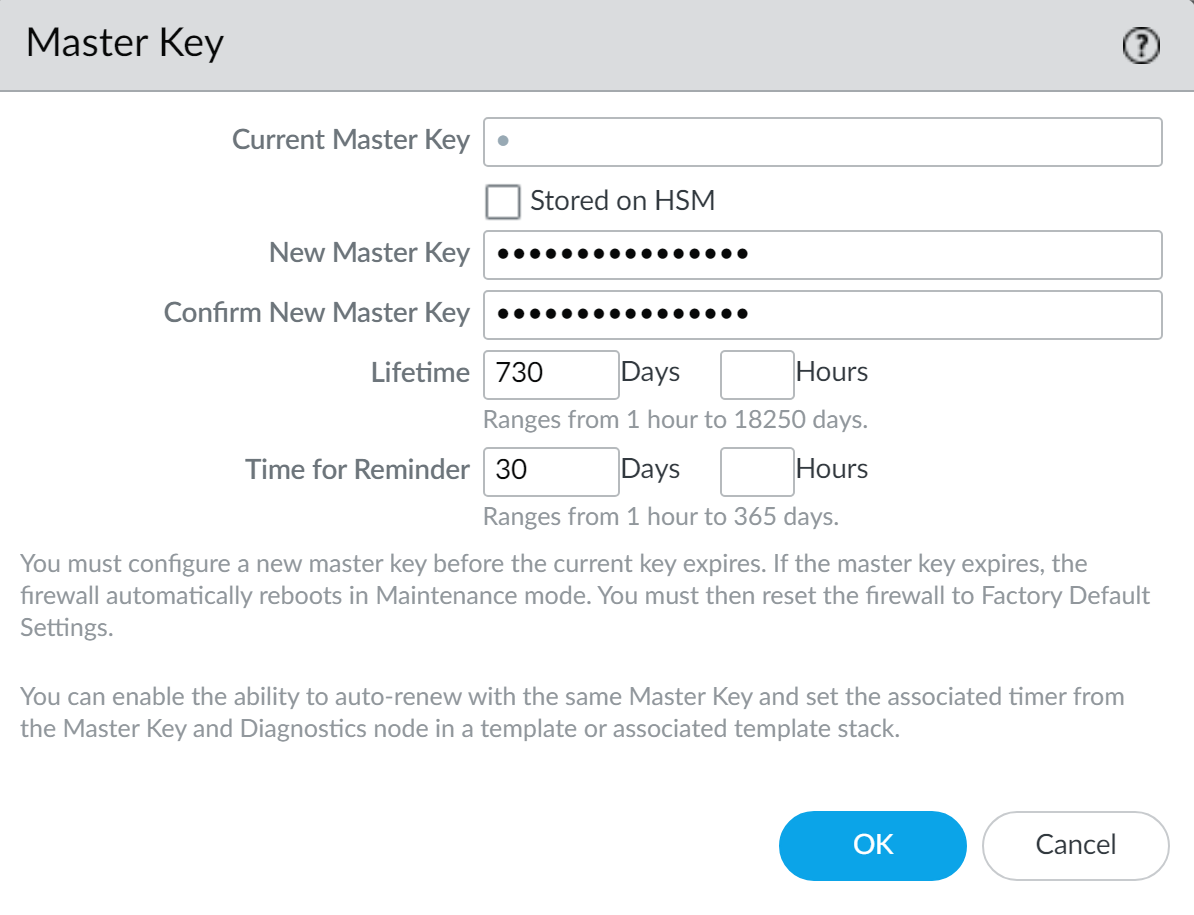
Select PanoramaManaged DevicesSummary and Deploy Master Key.Select a managed firewall and Change the master key.If you want to deploy a unique master key for a specific set of managed firewalls, you can select those specific managed firewalls as well.![]() Configure the master key:
Configure the master key:- If renewing a master key, enter the Current Master Key. If you are replacing the default master key with a new master key, do not specify a Current Master Key.
- (Optional) Enable (check) Stored on HSM if the master key is encrypted on a Hardware Security Module (HSM).
- Specify the New Master Key and Confirm Master Key.
- Configure the master key Lifetime and Time for Reminder.
- Click OK.The new master key is automatically pushed to your managed firewalls after you click OK. Proceed only if you are certain you are ready to change the master key for your managed firewalls.
![]() Verify that the master key was deployed successfully to all selected managed firewalls.A System log generates when you deploy a new master key from Panorama.(Optional) Configure the master key to automatically renew for your managed firewalls.Configure this setting to automatically renew the master key deployed on the managed firewalls associated with the selected template. Otherwise, the master key expires per the configured master key lifetime and you must deploy a new master key.
Verify that the master key was deployed successfully to all selected managed firewalls.A System log generates when you deploy a new master key from Panorama.(Optional) Configure the master key to automatically renew for your managed firewalls.Configure this setting to automatically renew the master key deployed on the managed firewalls associated with the selected template. Otherwise, the master key expires per the configured master key lifetime and you must deploy a new master key.- Select DeviceMaster Key and Diagnostic and select the Template containing the target managed firewalls.
- Edit the Master Key settings and configure the Auto Renew With Same Master Key setting.
- Click OK.
- Commit and Commit and Push your configuration changes.
Configure the master key on Panorama.- (HA only) Disable the HA configuration for Panorama.This step is required to successfully change the master for both Panorama HA peers. You are unable to commit configuration changes on the secondary HA peer when Panorama is in an HA configuration.
- Select PanoramaHigh AvailabilityGeneral and edit the HA Setup.
- Disable (uncheck) Enable HA and click OK.
- Commit and Commit to Panorama.
Select PanoramaMaster Key and Diagnostics and configure the master key.- If renewing a master key, enter the Current Master Key. If you are replacing the default master key with a new master key, o not specify a Current Master Key.
- Configure the New Master Key and Confirm Master Key.
- Configure the master key Lifetime and Time for Reminder.
- Click OK.The new master key is automatically committed to Panorama after you click OK. Proceed only if you are certain you are ready to change the master key on Panorama.
(Optional) Configure the Panorama master key to automatically renew.Configure this setting to automatically renew the master key deployed on Panorama. Otherwise, the master key expires per the configured master key lifetime and you must deploy a new master key.- Select PanoramaMaster Key and Diagnostic and edit the Master Key setting.
- Configure the Auto Renew With Same Master Key setting.
- Click OK.
Select CommitCommit to Panorama and Commit your changes.(HA only) Repeat this step to configure an identical master key on the secondary HA peer.You must manually configure an identical master key on the primary and secondary HA peers when Panorama is in an HA configuration. The master key is not synchronized between the primary and secondary HA peers.Deploy the master key to Log Collectors.The master key configured for your Log Collectors must be identical to the master key configured for Panorama.- Select PanoramaManaged Collectors and Deploy Master Key.Select all devices and Change the master key.Configure the master key:
- If renewing a master key, enter the Current Master Key. If you are replacing the default master key with a new master key, do not specify a Current Master Key.
- Specify the New Master Key and Confirm Master Key.
- Configure the master key Lifetime and Time for Reminder.
- Click OK.The new master key is automatically pushed to your Log Collectors after you click OK. Proceed only if you are certain you are ready to change the master key for your Log Collectors.
Verify that the master key was deployed successfully to all selected devices.A System log generates when you deploy a new master key from Panorama.Deploy the master key to managed WildFire appliances.The master key configured your WildFire appliances must be identical to the master key configured for Panorama.- Select PanoramaManaged WildFire Appliances and Deploy Master Key.Select all devices and Change the master key.Configure the master key:
- If renewing a master key, enter the Current Master Key. If you are replacing the default master key with a new master key, do not specify a Current Master Key.
- Specify the New Master Key and Confirm Master Key.
- Configure the master key Lifetime and Time for Reminder.
- Click OK.The new master key is automatically pushed to your WildFire appliances after you click OK. Proceed only if you are certain you are ready to change the master key for your WildFire appliances.
Verify that the master key was deployed successfully to all selected devices.A System log generates when you deploy a new master key from Panorama.(HA Panorama only) Reconfigure the Panorama HA configuration.Repeat this step for both the primary and secondary Panorama HA peers.- Select PanoramaHigh AvailabilityGeneral and edit the HA Setup.Enable (check) Enable HA and click OK.Commit and Commit to Panorama.(HA Firewalls only) Enable config sync for managed firewalls.
- Select DeviceHigh AvailabilityGeneral and select the Template containing the managed firewall HA configuration.Edit the HA Pair Settings Setup.Enable (check) Enable Config Sync and click OK.Commit and Commit and Push your configuration changes.