Prisma Access
GlobalProtect in Proxy Mode (Strata Cloud Manager)
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
- 6.1 Preferred and Innovation
- 6.0 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
-
-
- 4.0 & Later
- Prisma Access China
-
-
GlobalProtect in Proxy Mode (Strata Cloud Manager)
Configure GlobalProtect in Proxy mode.
- Enable the agent-based proxy functionality for mobile users on Prisma Access.
- Enable Explicit Proxy.
- Select Configuration NGFW and Prisma AccessConfiguration ScopePrisma AccessMobile Users and click Explicit Proxy Setup.
- In the Infrastructure Settings area, click Setup Proxy Settings and specify an Explicit Proxy URL.
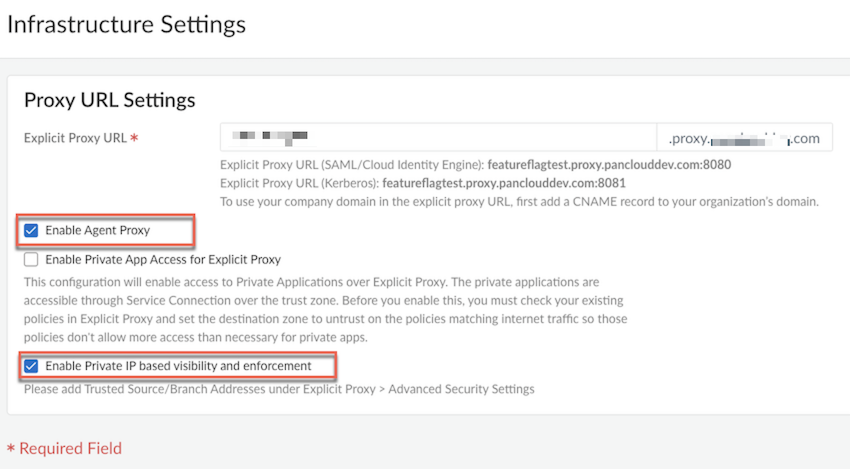
Enable Agent Proxy , and optionally Enable Private IP based visibility and enforcement, and Save.![]() Choose the Prisma Access locations where you want to support mobile users.For the best user experience, if you're limiting the number of locations, choose locations that are closest to your end users. If a location isn't available in the country where your mobile users reside, choose a location that’s closest to the mobile users.Create a Forwarding Profile to define the traffic you want to send through Explicit Proxy. While configuring the forwarding profile, bypass *.prismaaccess.com and *.gpcloudservice.com domains.
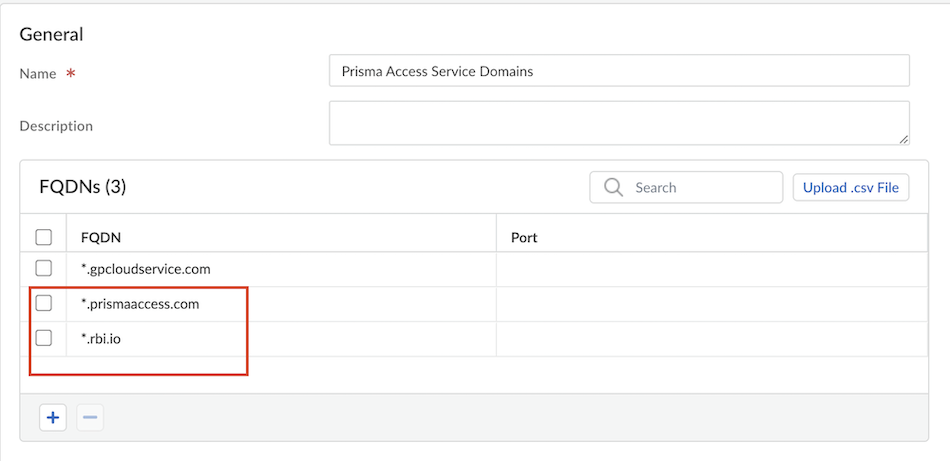
Choose the Prisma Access locations where you want to support mobile users.For the best user experience, if you're limiting the number of locations, choose locations that are closest to your end users. If a location isn't available in the country where your mobile users reside, choose a location that’s closest to the mobile users.Create a Forwarding Profile to define the traffic you want to send through Explicit Proxy. While configuring the forwarding profile, bypass *.prismaaccess.com and *.gpcloudservice.com domains.![]() Attach the Forwarding Profile to your GlobalProtect app configuration.Select Configuration NGFW and Prisma AccessConfiguration ScopePrisma AccessExplicit ProxyAdvanced Security Settings Authentication Settings and add the domains you need to bypass.All requests to the proxy undergo authentication. However, if you're passing IdP flows through the proxy, then you need to bypass them for the authentication to be successful.In this example, we are bypassing the GlobalProtect portal and Okta, but please customize these to the IdPs that you use.
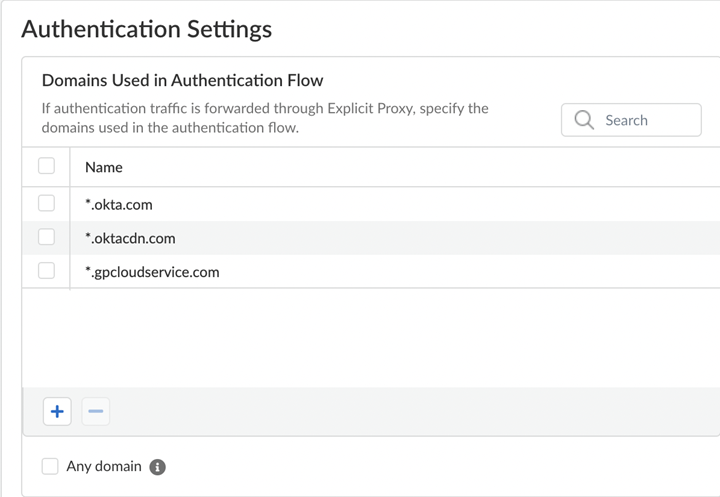
Attach the Forwarding Profile to your GlobalProtect app configuration.Select Configuration NGFW and Prisma AccessConfiguration ScopePrisma AccessExplicit ProxyAdvanced Security Settings Authentication Settings and add the domains you need to bypass.All requests to the proxy undergo authentication. However, if you're passing IdP flows through the proxy, then you need to bypass them for the authentication to be successful.In this example, we are bypassing the GlobalProtect portal and Okta, but please customize these to the IdPs that you use.![]() Set up the GlobalProtect portal, authentication, and configure Proxy mode for the GlobalProtect app.
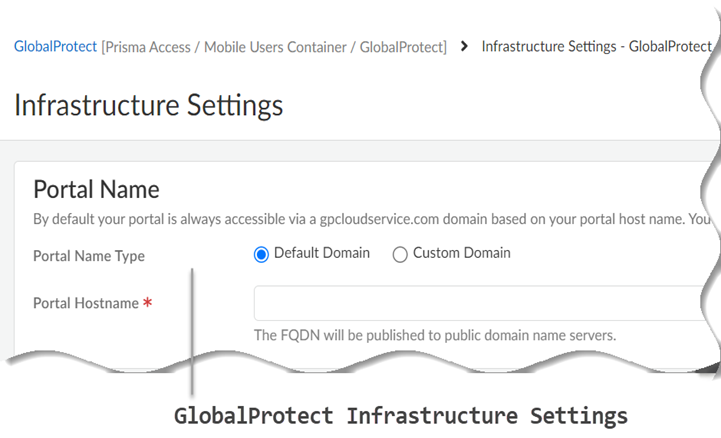
Set up the GlobalProtect portal, authentication, and configure Proxy mode for the GlobalProtect app.- Select Configuration NGFW and Prisma AccessConfiguration ScopePrisma AccessGlobalProtectInfrastructureInfrastructure Settings and specify the Portal Name.
![]()
- Default Domain—If you select this option, your portal hostname uses the default domain name: .gpcloudservice.com. In this case, simply enter a Portal Hostname to append to the default domain name. Prisma Access for Users will automatically create the necessary certificates and publish the hostname to public DNS servers.
- Custom Domain—You can also customize the portal address if you want the domain in the portal hostname to match your company domain name (for example, myportal.mydomain.com).
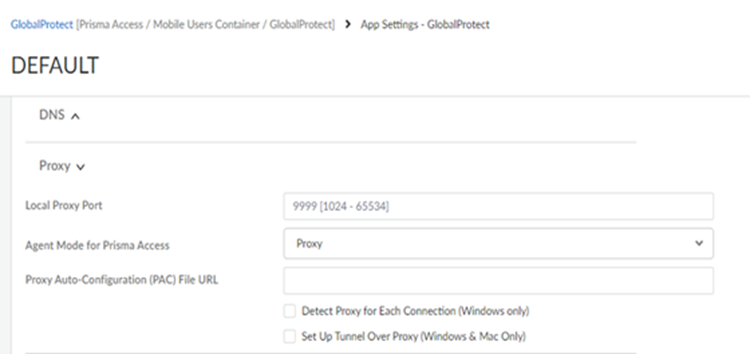
Enable mobile users to authenticate to Prisma Access.Enable GlobalProtect proxy mode for Prisma Access in the GlobalProtect app settings to send internet traffic to the agent-based proxy.The GlobalProtect connect method does not apply in proxy mode as it's always on.- Select ConfigurationNGFW and Prisma AccessConfiguration ScopePrisma AccessGlobalProtect.
- On the GlobalProtect App tab, click Default to customize the app settings or Add App Settings add a new configuration.
- Click Show Advanced Options and in the App Configuration section.
- Set Agent Mode for Prisma Access to Proxy to instruct the GlobalProtect app to send the internet traffic to the Explicit Proxy on Prisma Access.
- (Optional) Configure the local proxy port. The port range is 1024 to 65534 and the default port is 9999. If the default port isn't available, GlobalProtect will try 10 other ports in the range of 9999 to 10009 and use the port that is available. You can also pick your own port number within the range.
- (Optional) Configure PAC Auto-Configuration (PAC) File URL if you want to push the new PAC URL for the proxy settings to the endpoint. The PAC URL pushes to the endpoint once the user connects. When the user disconnects the GlobalProtect app, the endpoint proxy configurations are automatically disabled and reverting to the previous settings.
- (Optional) Enable Allow User to Rediscover Network if you want the user to check the portal for any new settings.
- (Optional) Configure GlobalProtect App Config Refresh Interval (hours). By default, the GlobalProtect client refreshes the cached portal configuration every 24 hours. You can change the refresh interval based on your business requirements.
- Disable Set Up Tunnel Over Proxy (Windows & Mac Only).
![]() Enable Always-On internet security by configuring the following settings on the Configuration NGFW and Prisma AccessConfiguration ScopePrisma AccessGlobalProtectGlobalProtect AppAdd App Settings page:
Enable Always-On internet security by configuring the following settings on the Configuration NGFW and Prisma AccessConfiguration ScopePrisma AccessGlobalProtectGlobalProtect AppAdd App Settings page:- Set Disable GlobalProtect to Disallow, Allow with Passcode, or Allow with Ticket.
- Disable Allow user to Sign Out from GlobalProtect App.
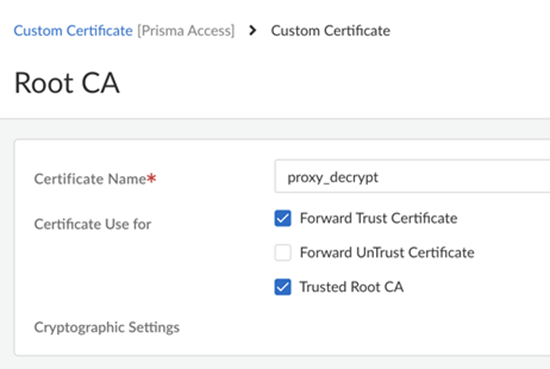
Configure decryption for Explicit Proxy traffic.- Select ConfigurationNGFW and Prisma AccessSecurity ServicesDecryption.
- If you enable decryption, make sure you set up the
decryption certificate as a trusted root CA.
![]()
Configure Security policy rules for Explicit Proxy traffic.- Select ConfigurationNGFW and Prisma AccessSecurity ServicesSecurity Policy.
- Follow the Internet Gateway Security Policy Best Practices.
(Optional) Configure the GlobalProtect app in proxy mode in a no default route network.- (Optional) Host a PAC file internally and add the Prisma Access Explicit Proxy FQDN as a proxy in the PAC file, or host the PAC file in a Forwarding Profile and add routes in your network for PAC service IP addresses.
- In the PAC file, forward the IdP URL and Prisma Access portal URL to Explicit Proxy.
- On Explicit Proxy, exclude the IdP and portal URL from the authentication settings. Add the IdP and portal URL to the domain used in the authentication flows.
- Set up routes to the Explicit Proxy FQDN or IP addresses on perimeter devices to allow users to access the internet via the Explicit Proxy.
- (Optional) Add DNS records to resolve the Prisma Access Explicit Proxy FQDN to an internal IP address if users can’t resolve public domains in the branch network and add destination NAT for the internal IP address to the Explicit Proxy FQDN or IP address.
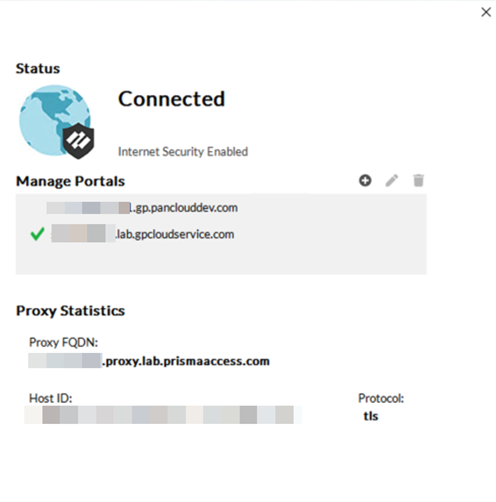
Click Save and Push Config to GlobalProtect and Explicit Proxy.Verify and troubleshoot the agent proxy deployment.- Verify the information about your network connection on the GlobalProtect app Connections tab under Settings.
- Open the GlobalProtect app.
- Select Settings to open the GlobalProtect Settings panel, and then select Connections.
![]() View and collect the GlobalProtect logs.View the PanGPS log to verify the proxy mode configuration on the GlobalProtect portal.You can verify that Proxy mode is configured by looking for the following event in the PanGPS log:OnProxyAgentMode: proxy only modeTo view GlobalProtect logs in Prisma Access, select Incidents & AlertsLog Viewer and:
View and collect the GlobalProtect logs.View the PanGPS log to verify the proxy mode configuration on the GlobalProtect portal.You can verify that Proxy mode is configured by looking for the following event in the PanGPS log:OnProxyAgentMode: proxy only modeTo view GlobalProtect logs in Prisma Access, select Incidents & AlertsLog Viewer and:- GlobalProtect, for authentication logs
- Traffic and Decryption for user access logs