Add a Firewall as a Managed Device
Table of Contents
10.0 (EoL)
Expand all | Collapse all
-
- Determine Panorama Log Storage Requirements
-
- Setup Prerequisites for the Panorama Virtual Appliance
- Perform Initial Configuration of the Panorama Virtual Appliance
- Set Up The Panorama Virtual Appliance as a Log Collector
- Set Up the Panorama Virtual Appliance with Local Log Collector
- Set up a Panorama Virtual Appliance in Panorama Mode
- Set up a Panorama Virtual Appliance in Management Only Mode
-
- Preserve Existing Logs When Adding Storage on Panorama Virtual Appliance in Legacy Mode
- Add a Virtual Disk to Panorama on an ESXi Server
- Add a Virtual Disk to Panorama on vCloud Air
- Add a Virtual Disk to Panorama on Alibaba Cloud
- Add a Virtual Disk to Panorama on AWS
- Add a Virtual Disk to Panorama on Azure
- Add a Virtual Disk to Panorama on Google Cloud Platform
- Add a Virtual Disk to Panorama on Hyper-V
- Add a Virtual Disk to Panorama on KVM
- Add a Virtual Disk to Panorama on Oracle Cloud Infrastructure (OCI)
- Mount the Panorama ESXi Server to an NFS Datastore
-
- Increase CPUs and Memory for Panorama on an ESXi Server
- Increase CPUs and Memory for Panorama on vCloud Air
- Increase CPUs and Memory for Panorama on Alibaba Cloud
- Increase CPUs and Memory for Panorama on AWS
- Increase CPUs and Memory for Panorama on Azure
- Increase CPUs and Memory for Panorama on Google Cloud Platform
- Increase CPUs and Memory for Panorama on Hyper-V
- Increase CPUs and Memory for Panorama on KVM
- Increase CPUs and Memory for Panorama on Oracle Cloud Infrastructure (OCI)
- Complete the Panorama Virtual Appliance Setup
-
- Convert Your Evaluation Panorama to a Production Panorama with Local Log Collector
- Convert Your Evaluation Panorama to a Production Panorama without Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing with Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing without Local Log Collector
- Convert Your Production Panorama to an ELA Panorama
-
- Register Panorama
- Activate a Panorama Support License
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is Internet-connected
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is not Internet-connected
- Activate/Retrieve a Firewall Management License on the M-Series Appliance
- Install the Panorama Device Certificate
-
- Panorama, Log Collector, Firewall, and WildFire Version Compatibility
- Install Updates for Panorama in an HA Configuration
- Install Updates for Panorama with an Internet Connection
- Install Updates for Panorama When Not Internet-Connected
- Install Updates Automatically for Panorama without an Internet Connection
- Migrate Panorama Logs to the New Log Format
-
- Migrate from a Panorama Virtual Appliance to an M-Series Appliance
- Migrate a Panorama Virtual Appliance to a Different Hypervisor
- Migrate from an M-Series Appliance to a Panorama Virtual Appliance
- Migrate from an M-100 Appliance to an M-500 Appliance
- Migrate from an M-100 or M-500 Appliance to an M-200 or M-600 Appliance
-
- Configure an Admin Role Profile
- Configure an Access Domain
-
- Configure a Panorama Administrator Account
- Configure Local or External Authentication for Panorama Administrators
- Configure a Panorama Administrator with Certificate-Based Authentication for the Web Interface
- Configure an Administrator with SSH Key-Based Authentication for the CLI
- Configure RADIUS Authentication for Panorama Administrators
- Configure TACACS+ Authentication for Panorama Administrators
- Configure SAML Authentication for Panorama Administrators
-
- Add a Firewall as a Managed Device
-
- Add a Device Group
- Create a Device Group Hierarchy
- Create Objects for Use in Shared or Device Group Policy
- Revert to Inherited Object Values
- Manage Unused Shared Objects
- Manage Precedence of Inherited Objects
- Move or Clone a Policy Rule or Object to a Different Device Group
- Push a Policy Rule to a Subset of Firewalls
- Manage the Rule Hierarchy
- Manage the Master Key from Panorama
- Redistribute Data to Managed Firewalls
-
- Add Standalone WildFire Appliances to Manage with Panorama
- Remove a WildFire Appliance from Panorama Management
-
-
- Configure a Cluster and Add Nodes on Panorama
- Configure General Cluster Settings on Panorama
- Remove a Cluster from Panorama Management
- Configure Appliance-to-Appliance Encryption Using Predefined Certificates Centrally on Panorama
- Configure Appliance-to-Appliance Encryption Using Custom Certificates Centrally on Panorama
- View WildFire Cluster Status Using Panorama
- Upgrade a Cluster Centrally on Panorama with an Internet Connection
- Upgrade a Cluster Centrally on Panorama without an Internet Connection
-
-
- Manage Licenses on Firewalls Using Panorama
-
- Supported Updates
- Schedule a Content Update Using Panorama
- Upgrade Log Collectors When Panorama Is Internet-Connected
- Upgrade Log Collectors When Panorama Is Not Internet-Connected
- Upgrade Firewalls When Panorama Is Internet-Connected
- Upgrade Firewalls When Panorama Is Not Internet-Connected
- Upgrade a ZTP Firewall
- Revert Content Updates from Panorama
-
- Preview, Validate, or Commit Configuration Changes
- Enable Automated Commit Recovery
- Compare Changes in Panorama Configurations
- Manage Locks for Restricting Configuration Changes
- Add Custom Logos to Panorama
- Use the Panorama Task Manager
- Reboot or Shut Down Panorama
- Configure Panorama Password Profiles and Complexity
-
-
- Verify Panorama Port Usage
- Resolve Zero Log Storage for a Collector Group
- Replace a Failed Disk on an M-Series Appliance
- Replace the Virtual Disk on an ESXi Server
- Replace the Virtual Disk on vCloud Air
- Migrate Logs to a New M-Series Appliance in Log Collector Mode
- Migrate Logs to a New M-Series Appliance in Panorama Mode
- Migrate Logs to a New M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Logs to the Same M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Log Collectors after Failure/RMA of Non-HA Panorama
- Regenerate Metadata for M-Series Appliance RAID Pairs
- View Log Query Jobs
- Troubleshoot Commit Failures
- Troubleshoot Registration or Serial Number Errors
- Troubleshoot Reporting Errors
- Troubleshoot Device Management License Errors
- Troubleshoot Automatically Reverted Firewall Configurations
- Complete Content Update When Panorama HA Peer is Down
- View Task Success or Failure Status
- Downgrade from Panorama 10.0
End-of-Life (EoL)
Add a Firewall as a Managed Device
To use Panorama for managing your firewalls,
you need to enable a connection between the firewall and Panorama.
A successful connection requires that you enter the Panorama IP
address on each firewall that Panorama will manage and to also enter
the serial number of each firewall on Panorama. When you add a firewall
as a managed device, you can associate the new firewall with a device
group, template stack, collector group, and Log Collector during
the initial deployment. Additionally, you have the option to automatically
push the configuration to your newly added firewall when the firewall
first connects to Panorama, which ensures that firewalls are immediately
configured and ready to secure your network.
You can
only bulk import single vsys firewalls to be managed by Panorama.
The
firewall uses the Panorama management server IP address to set up
an SSL connection to register with Panorama. Panorama and the firewall
authenticate each other using 2,048-bit certificates and AES-256
encrypted SSL connections for configuration management and log collection.
Prepare Panorama and each firewall as follows:
- Configure the firewall to communicate with Panorama.Repeat this step for each firewall Panorama will manage.
- Perform initial configuration on the firewall so that it is accessible and can communicate with Panorama over the network.
- Configure each data interface you plan to use on the firewall and attach it to a security zone so that you can push configuration and policy from Panorama.
- Add the Panorama IP address to the firewall.
- Select DeviceSetupManagement and edit the Panorama Settings.
- Enter the Panorama IP address in the first field.Panorama issues a single IP address for device management, log collection, reporting, and dynamic updates. Enter the external, Internet-bound IP address to ensure Panorama can successfully access existing and new managed devices and Log Collectors. If an internal Panorama IP address is configured, you may be unable to manage some devices. For example, if you Install Panorama on AWS and enter the internal IP address, Panorama is unable to manage devices or Log Collectors outside of the AWS security group.
- (Optional) If you have set up a high availability (HA) pair in Panorama, enter the IP address of the secondary Panorama in the second field.
- Click OK.
- Select Commit and Commit your changes.
- Add one or more firewalls to Panorama.
- Add one or more firewalls.
- Add a new managed device (PanoramaManaged DevicesSummary).
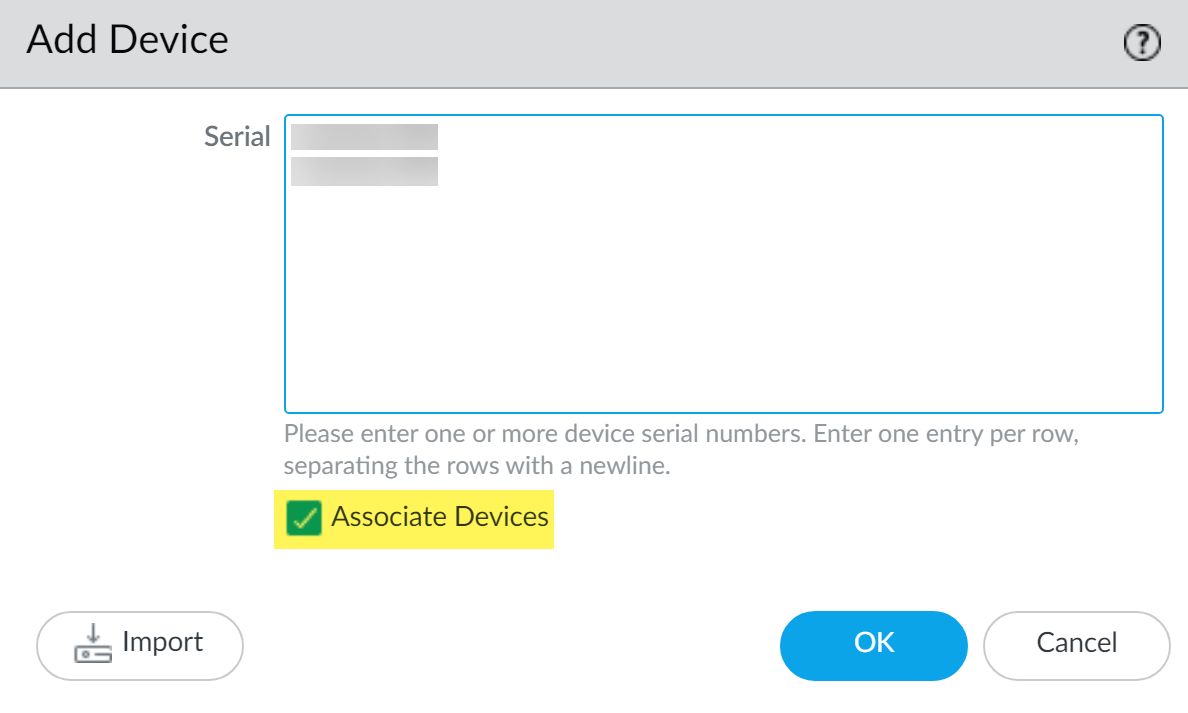
- Enter the firewall Serial number. If you are adding multiple firewalls, enter each serial number on a separate line. If you want to associate the new firewalls with a device group, template stack, collector group, or Log Collector for the initial deployment, continue to the next step. To manually assign each firewall, click OK and continue to Step 3.
- Select the Associate Devices check box and click OK.
![]()
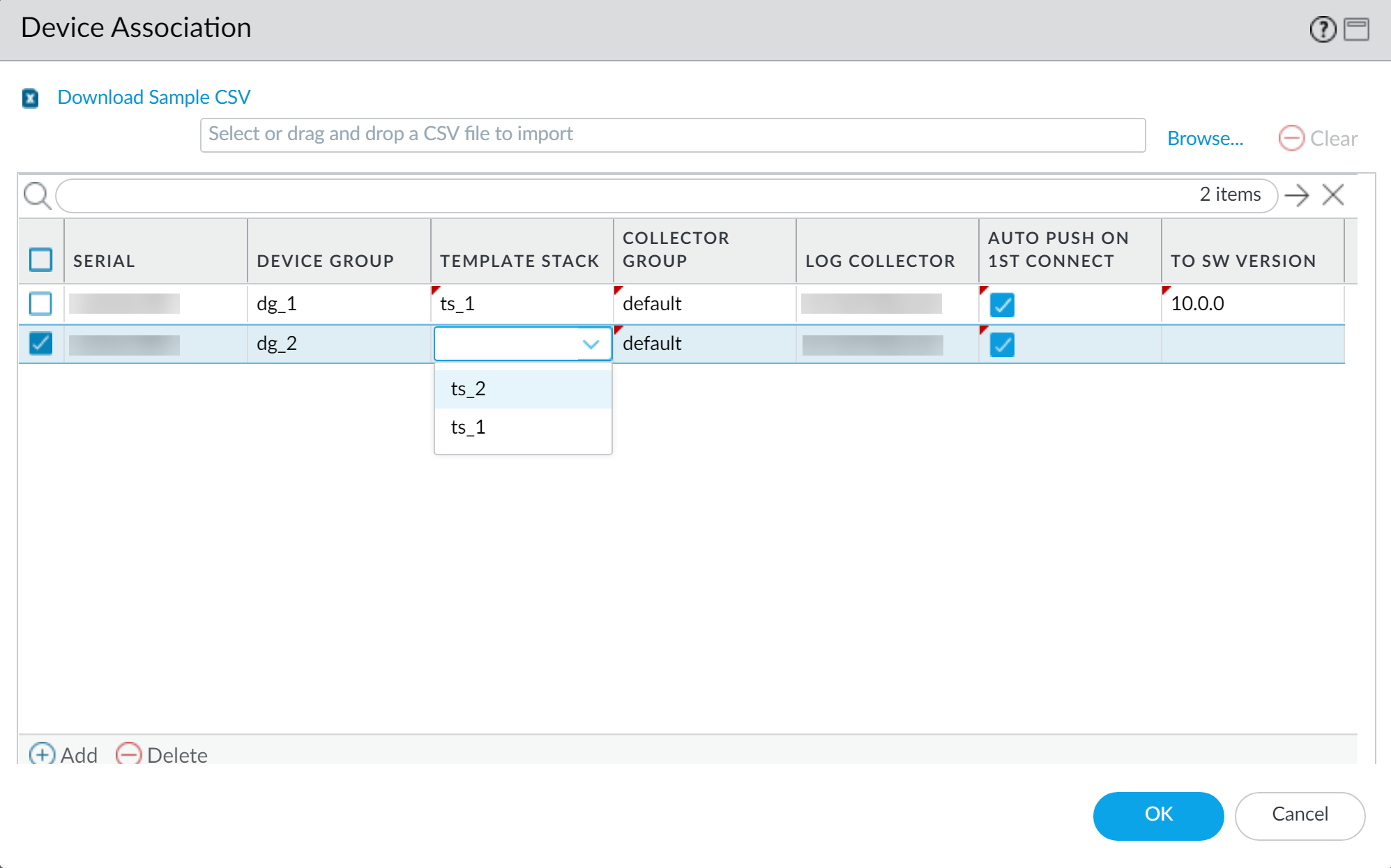
- Assign the Device Group, Template Stack, Collector Group, and Log Collector as needed from the drop-down for each column.
- Enable Auto Push on 1st connect check box to automatically push the device group and template stack configuration to the new devices when they successfully connect to Panorama.The Auto Push on 1st Connect option is supported only on firewalls running PAN-OS 8.1 or later releases. The commit all job executes from Panorama to managed devices running PAN-OS 8.1 and later releases.
- (Optional) Select a PAN-OS release version in the To SW Version column to begin automatically upgrading the managed firewall to the specified PAN-OS release version upon successful connection to Panorama.To upgrade a managed firewall to a target PAN-OS release on first connection, you must install the minimum content release version required for that PAN-OS release before adding the firewall as a managed device. To do this, you must register the firewall, activate the support license, and install the content update before adding the firewall to Panorama management.Leave this column empty if you do not want to automatically upgrade the managed firewall.
- Click OK to add the devices.
![]()
- Bulk import multiple firewalls using a comma-separated values (CSV) file.
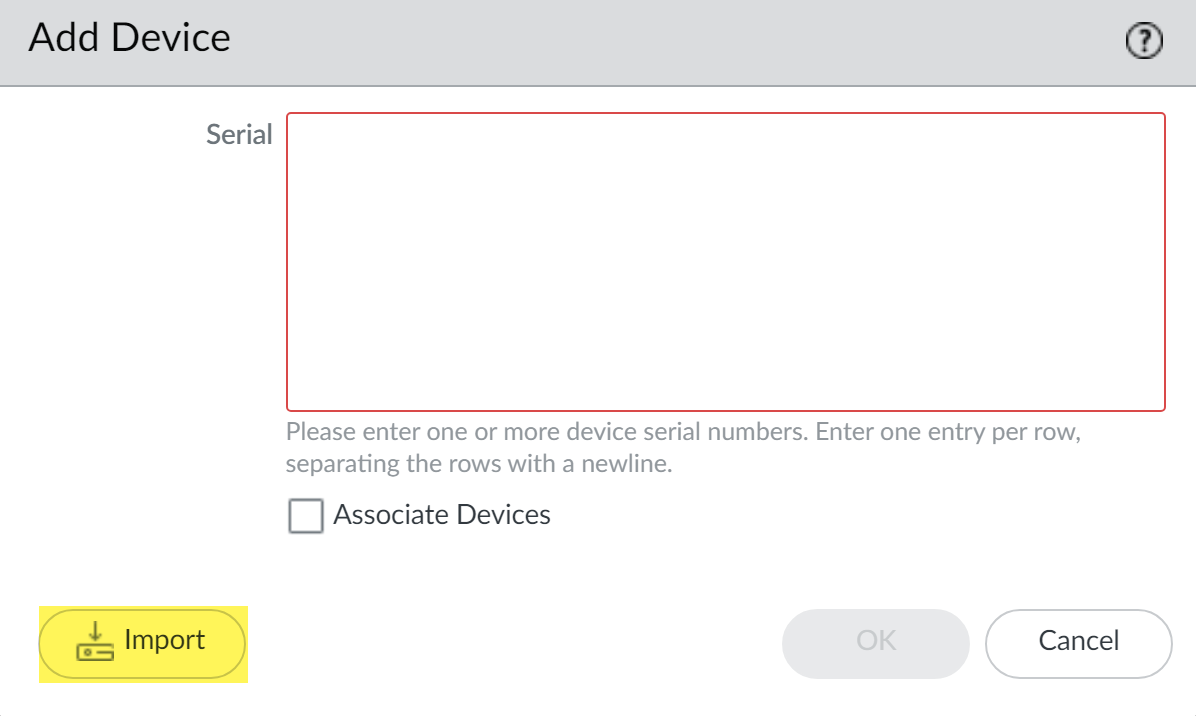
- Add a new managed device (PanoramaManaged DevicesSummary).
- Click Import.
![]()
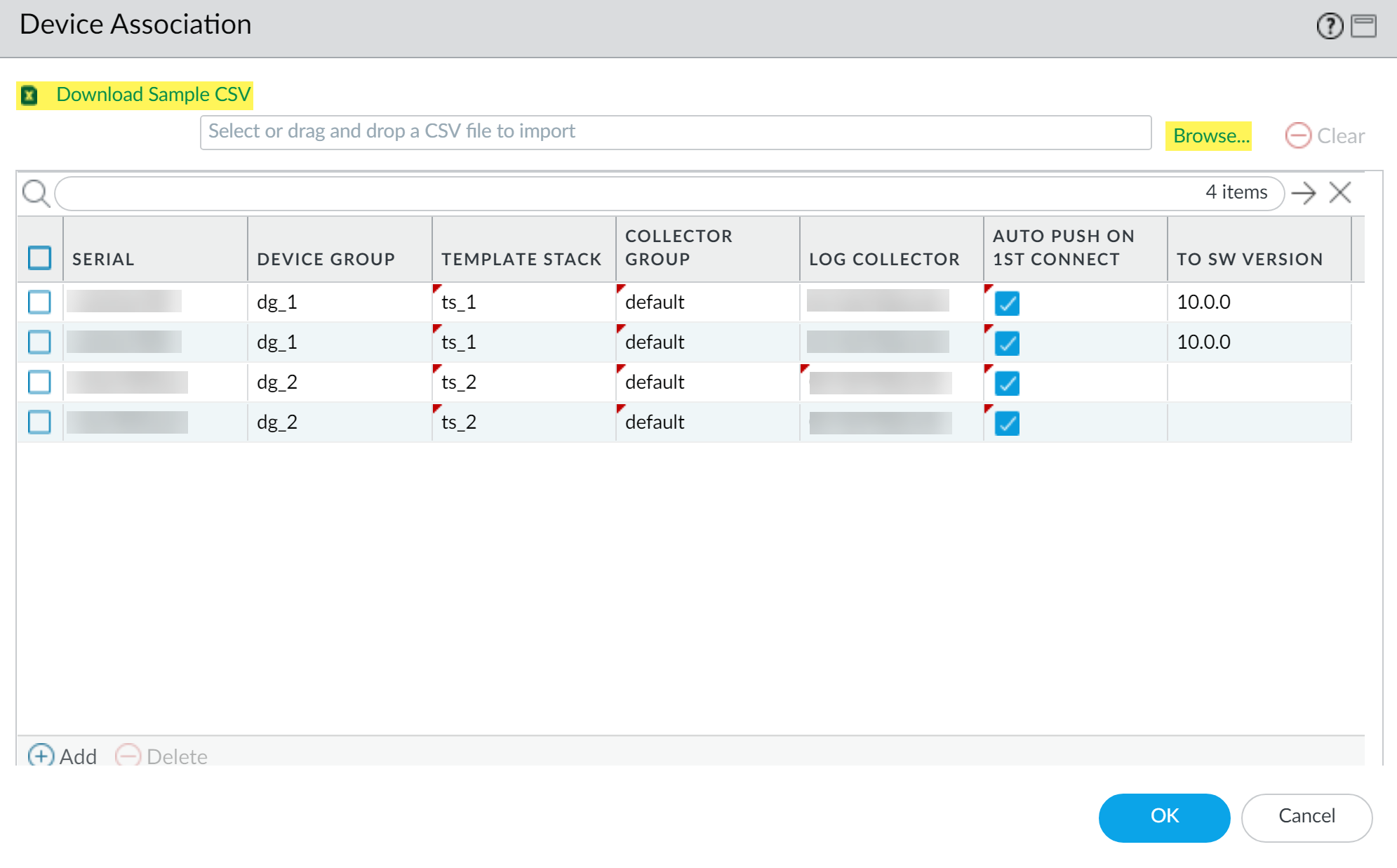
- Download Sample CSV and edit the downloaded CSV file with the firewalls you are adding. You can choose to assign the firewalls to a device group, template stack, Collector Group, and Log Collector from the CSV or enter only the firewall serial numbers and assign them from the web interface. Save the CSV after you finish editing it.
- Browse and select the CSV file you edited in the previous step.
- If not already assigned in the CSV, assign the firewalls a Device Group, Template Stack, Collector Group, and Log Collector as needed from the drop-down for each column.
- If not already enabled in the CSV, enable Auto Push on 1st connect check box to automatically push the device group and template stack configuration to the new devices when they successfully connect to Panorama.
- (Optional) Select a PAN-OS release version in the To SW Version column to begin automatically upgrading the managed firewall to the specified PAN-OS release version upon successful connection to Panorama.Leave this column empty if you do not want to automatically upgrade the managed firewall.
- Click OK to add the devices.
![]()
- (Optional)
Add a Tag. Tags make it easier for you to
find a firewall from a large list; they help you to dynamically
filter and refine the list of firewalls in your display. For example,
if you add a tag called branch office, you can filter for all branch
office firewalls across your network.
- Select each firewall and click Tag.
- Click Add, enter a string of up to 31 characters (no empty spaces), and click OK.
- If your deployment is using custom certificates for authentication between Panorama and managed devices, deploy the custom client device certificate. For more information, see Set Up Authentication Using Custom Certificates and Add New Client Devices.
- Select CommitCommit to Panorama and Commit your changes.
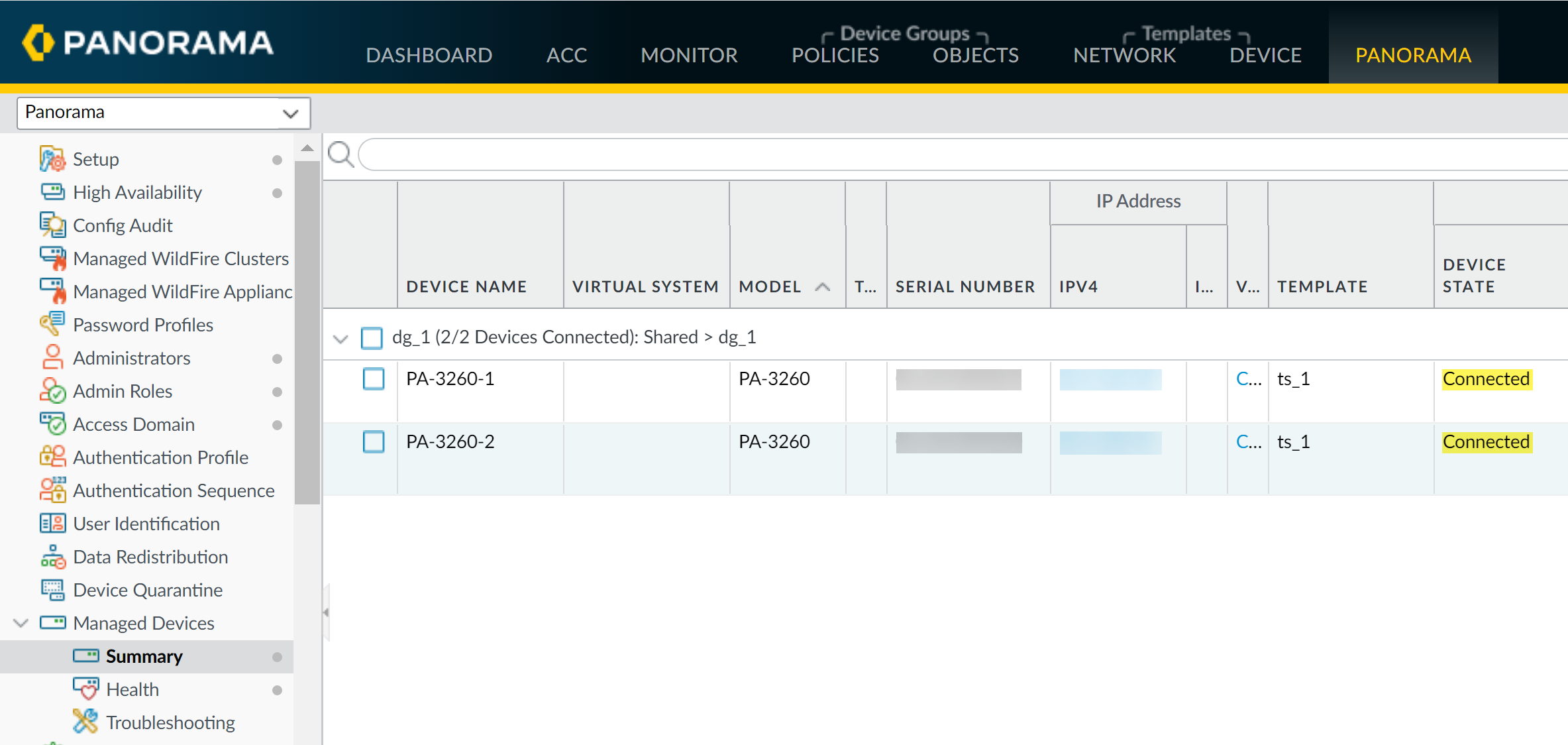
- Verify
that the firewall is connected to Panorama.
- Click PanoramaManaged DevicesSummary.
- Verify that the Device State for
the new device shows as Connected.
![]()