Advanced WildFire Powered by Precision AI™
Forward Files for Advanced WildFire Analysis (Cloud Management)
Table of Contents
Forward Files for Advanced WildFire Analysis (Cloud Management)
If you’re using Panorama to manage Prisma Access:
Toggle over to the PAN-OS tab
and follow the guidance there.
If you’re using Prisma Access Cloud Management, continue here.
- Review the Advanced WildFire cloud to which you forward samples to.Select ConfigurationNGFW and Prisma AccessSecurity ServicesWildFire and AntivirusGeneral Settings and edit the General Settings based on your WildFire cloud deployment (public, government, private, or hybrid).The WildFire U.S. Government Cloud is only available to U.S. Federal agencies as an optional analysis environment.Add the WildFire Cloud URL for the cloud environment to forward samples to for analysis.Advanced WildFire Public Cloud options:The regional WildFire cloud location for sample processing might differ from their respective Prisma Access Compute location. For more details on how the Prisma Access Compute locations maps to the WildFire public cloud, refer to: Prisma Access Privacy Datasheet.
- Enter the WildFire Public Cloud URL:
- United States: wildfire.paloaltonetworks.com
- Europe: eu.wildfire.paloaltonetworks.com
- Japan: jp.wildfire.paloaltonetworks.com
- Singapore: sg.wildfire.paloaltonetworks.com
- United Kingdom: uk.wildfire.paloaltonetworks.com
- Canada: ca.wildfire.paloaltonetworks.com
- Australia: au.wildfire.paloaltonetworks.com
- Germany: de.wildfire.paloaltonetworks.com
- India: in.wildfire.paloaltonetworks.com
- Switzerland: ch.wildfire.paloaltonetworks.com
- Poland: pl.wildfire.paloaltonetworks.com
- Indonesia: id.wildfire.paloaltonetworks.com
- Taiwan: tw.wildfire.paloaltonetworks.com
- France: fr.wildfire.paloaltonetworks.com
- Qatar: qatar.wildfire.paloaltonetworks.com
- South Korea: kr.wildfire.paloaltonetworks.com
- South Africa: za.wildfire.paloaltonetworks.com
- Israel: il.wildfire.paloaltonetworks.com
- Saudi Arabia: sa.wildfire.paloaltonetworks.com
- Italy: it.wildfire.paloaltonetworks.com
- Spain: es.wildfire.paloaltonetworks.com
- Brazil: br.wildfire.paloaltonetworks.com
Make sure the WildFire Private Cloud field is clear.WildFire FedRAMP Cloud options:- Enter the WildFire FedRAMP Cloud URL:
- U.S. Government Cloud: wildfire.gov.paloaltonetworks.com
- Advanced WildFire Government Cloud: gov-cloud.wildfire.paloaltonetworks.com
- Advanced WildFire Public Sector Cloud: pubsec-cloud.wildfire.paloaltonetworks.com
Make sure the WildFire Private Cloud field is clear.Enable Prisma Access to forward decrypted SSL traffic for Advanced WildFire analysis by selecting Allow Forwarding of Decrypted Content. Decrypted traffic is evaluated against security policy rules; if it matches the WildFire analysis profile attached to the security rule, the decrypted traffic is forwarded for analysis before it is re-encrypted.Forwarding decrypted SSL traffic for analysis is an Advanced WildFire Best Practice.Define the size limits for samples that Prisma Access forwards for analysis.It is a Advanced WildFire Best Practice to set the file forwarding values to the default setting.Configure submission log settings.- Select Report Benign Files to allow logging for files that receive a verdict of benign.Select Report Grayware Files to allow logging for files that receive a verdict of grayware.When finished, Save your changes.Define traffic to forward for analysis.
- Select ConfigurationNGFW and Prisma AccessSecurity ServicesWildFire and Antivirus, and then Add Profile. Provide a Name and Description for the profile.Add Rule to define traffic to be forwarded for analysis and give the rule a descriptive Name, such as local-PDF-analysis.Define the profile rule to match to unknown traffic and to forward samples for analysis based on:
- Direction of Traffic—Forward files for analysis based the transmission direction of the file (Upload, Download, or Upload and Download). For example, select Upload and Download to forward all unknown PDFs for analysis, regardless of the transmission direction.
- Applications—Forward files for analysis based on the application in use.
- File Types—Forward files for analysis based on file types, including links contained in email messages. For example, select PDF to forward unknown PDFs detected by the firewall for analysis.
- Select the destination for traffic to be forwarded for Analysis.
- Select Public Cloud so that all traffic matched to the rule is forwarded to the Advanced WildFire public cloud for analysis.
- Select Private Cloud so that all traffic matched to the rule is forwarded to the WildFire appliance for analysis.
- Save the WildFire analysis forwarding rule when finished.
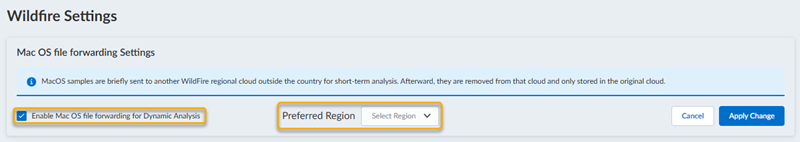
Save the WildFire and Antivirus security profile.(Optional) Enable MacOS (Dynamic Analysis) forwarding support. The file size limits as well as any forwarding profile rules are inherited from the file type MacOSX.![]()
- Select ConfigurationWildFire Setting.
- Enable Mac OS file forwarding for Dynamic Analysis and select the Preferred Region, whereby suspicious MacOS samples are sent for MacOS dynamic analysis.MacOS dynamic analysis forwarding support is available only in select WildFire cloud regions. If your configured WildFire public cloud region does not support MacOS dynamic analysis, the sample is temporarily sent to the region designated for MacOS dynamic analysis, during which the file is analyzed and subsequently deleted. The sample analysis results are then sent to your configured WildFire public cloud region for access.The following WildFire public cloud regions are available:
- United States (US)
- European Union (EU)
- Japan (JP)
- Singapore (SG)
- Apply Change to save the configuration.
Enable the WildFire and Antivirus Security Profile.Traffic allowed by the security policy rule is evaluated against the attached WildFire analysis profile; Prisma Access forwards traffic matched to the profile for WildFire analysis.Push configuration changes.(Optional) Enable Advanced WildFire Inline MLChoose what to do next...- Verify WildFire Submissions to confirm that the firewall is successfully forwarding files for analysis.
- Monitor WildFire Activity to assess alerts and details reported for malware.