Advanced WildFire Powered by Precision AI™
View WildFire Logs and Analysis Reports
Table of Contents
View WildFire Logs and Analysis Reports
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
WildFire logs contain information on samples (files
and email links) uploaded to the WildFire cloud for analysis. It
includes artifacts, which are properties, activities, or behaviors
associated with the logged event, such as the application type or
the IP address of an attacker as well as WildFire-specific qualities,
such as high-level analysis results including categorization of
the sample as malware, phishing, grayware, or benign and details sample
information. Reviewing the WildFire Submissions logs can also indicate
whether a user in your networks downloaded a suspicious file. The WildFire
analysis report displays detailed sample information, as well as
information on targeted users, email header information (if enabled),
the application that delivered the file, and all URLs involved in
the command-and-control activity of the file. It informs you if
the file is malicious, if it modified registry keys, read/wrote
into files, created new files, opened network communication channels,
caused application crashes, spawned processes, downloaded files,
or exhibited other malicious behavior.
WildFire logs are displayed as WildFire submissions logs on NGFW firewalls, while on Cloud
Management platforms, you must first configure log forwarding to upload relevant logs to
Strata Logging Service, which will then show the WildFire logs as threat logs
(type WildFire).
View WildFire Logs and Analysis Reports (Cloud Management)
If you’re using Panorama to manage Prisma Access,, you can follow the process
below to access content in Prisma Access or toggle over to the PAN-OS
tab and follow the guidance there.
- Use the credentials associated with your Palo Alto Networks support account and log in to the Strata Cloud Manager application on the hub.For more information on using Activity, refer to the Log Viewer.Filter threat logs to display your WildFire sample submissions in Prisma Access.
- Select Log Viewer.Change the log type to be searched to Threat.Create a search filter using the WildFire subtype used to indicate a WildFire sample submission using the query builder. For example, you can use sub_type.value = 'wildfire' to view your WildFire logs. Adjust the search criteria as necessary for your search, including additional query parameters (such as the severity level and action) along with a date range.To view the WildFire analysis report, you must log in to the WildFire portal and use the hash value or file name to retrieve the report file. For more information, refer to View Reports on the WildFire Portal.
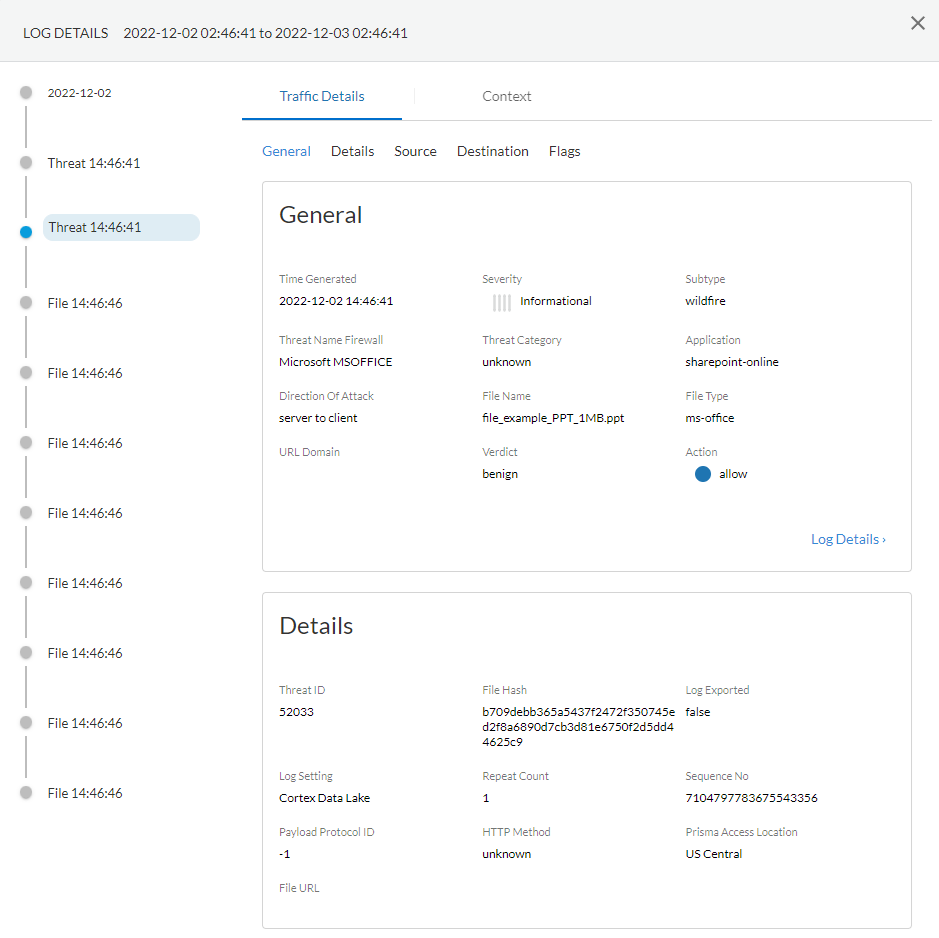
![]() Run the query after you have finished assembling your filter.Select a log entry from the results to view the log details.The threat log Subtype is displayed in the General pane along with other information about the sample. Other relevant details about the threat are displayed in their corresponding windows.
Run the query after you have finished assembling your filter.Select a log entry from the results to view the log details.The threat log Subtype is displayed in the General pane along with other information about the sample. Other relevant details about the threat are displayed in their corresponding windows.![]()
View WildFire Logs and Analysis Reports (PAN-OS & Panorama)
Samples that firewalls submit for WildFire analysis are displayed as entries in the WildFire Submissions log on the firewall web interface. For each WildFire entry, you can open an expanded log view which displays log details and the WildFire analysis report for the sample.Mozilla Firefox users: The WildFire Analysis Report displays correctly only in Firefox v54 and earlier releases. If you experience issues viewing the report, consider using a different web browser such as Google Chrome. Alternatively, you can download and open the PDF version or view the report through the WildFire portal.- Forward Files for Advanced WildFire Analysis.Configure WildFire Submissions Log Settings.To view samples submitted by a firewall to a WildFire public, private, or hybrid cloud, select MonitorLogsWildFire Submissions. When WildFire analysis of a sample is complete, the results are sent back to the firewall that submitted the sample and are accessible in the WildFire Submissions logs. The submission logs include details about a given sample, including the following information:
- The Verdict column indicates whether the sample is benign, malicious, phishing, or grayware.
- The Action column indicates whether the firewall allowed or blocked the sample.
- The Severity column indicates how much of a threat a sample poses to an organization using the following values: critical, high, medium, low, and informational.The values for the following severity levels are determined by a combination of verdict and action values.
- Low—Grayware samples with the action set to allow.
- High—Malicious samples with the action set to allow.
- Informational:
- Benign samples with the action set to allow.
- Samples with any verdict with the action set to block.
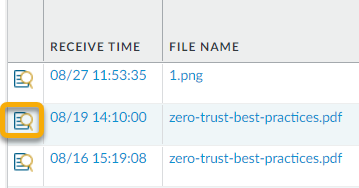
![]() For any entry, select the Log Details icon to open a detailed log view for each entry:
For any entry, select the Log Details icon to open a detailed log view for each entry:![]() The detailed log view displays Log Info and the WildFire Analysis Report for the entry. If the firewall has packet captures (PCAPs) enabled, the sample PCAPs are also displayed.
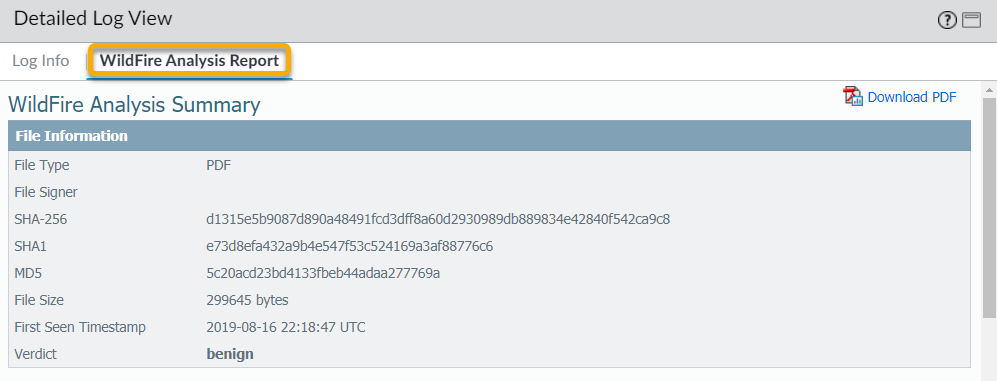
The detailed log view displays Log Info and the WildFire Analysis Report for the entry. If the firewall has packet captures (PCAPs) enabled, the sample PCAPs are also displayed.![]() For all samples, the WildFire analysis report displays file and session details. For malware samples, the WildFire analysis report is extended to include details on the file attributes and behavior that indicated the file was malicious.
For all samples, the WildFire analysis report displays file and session details. For malware samples, the WildFire analysis report is extended to include details on the file attributes and behavior that indicated the file was malicious.![]() (Optional) Download PDF of the WildFire Analysis Report.
(Optional) Download PDF of the WildFire Analysis Report.