Network Security
Policy Object: Traffic Objects
Table of Contents
Expand All
|
Collapse All
Network Security Docs
Policy Object: Traffic Objects
Create traffic objects to specify cloud entities within specific clusters or VPC
endpoints to enforce customized security policy rules.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
This page helps you to create a traffic object with specific cloud assets and map the
traffic object to a zone. Attach the zone to a security policy to enforce the policy
rules on the AI traffic sourced from this zone.
This feature is part of the Prisma AIRS licensing. The AI traffic from the zone is routed
to Prisma AIRS AI Runtime: Network intercept for inspection.
Prerequisite
Configure a Cluster ID in the Kubernetes environment and configure the PAN-CNI
plugin on a Kubernetes cluster to allocate the network interfaces on each pod. To
configure the PAN-CNI plugin for your Kubernetes cluster, you need three YAML files:
`pan-cni-configmap.yaml`, `pan-cni.yaml`, and `pan-cni-multus.yaml`. These files are
essential for setting up and managing the PAN-CNI plugin to secure your Kubernetes
clusters with the CN-Series firewall.
Strata Cloud Manager
Create traffic objects to specify cloud entities within specific clusters or VPC
endpoints to enforce customized security policy rules.
To create a policy object of type
traffic objects:
- Log in to Strata Cloud Manager.Navigate to Manage→ Configuration → NGFW and Prisma Access.From the top menu, select Objects → Traffic Objects.Select Add Traffic Object.
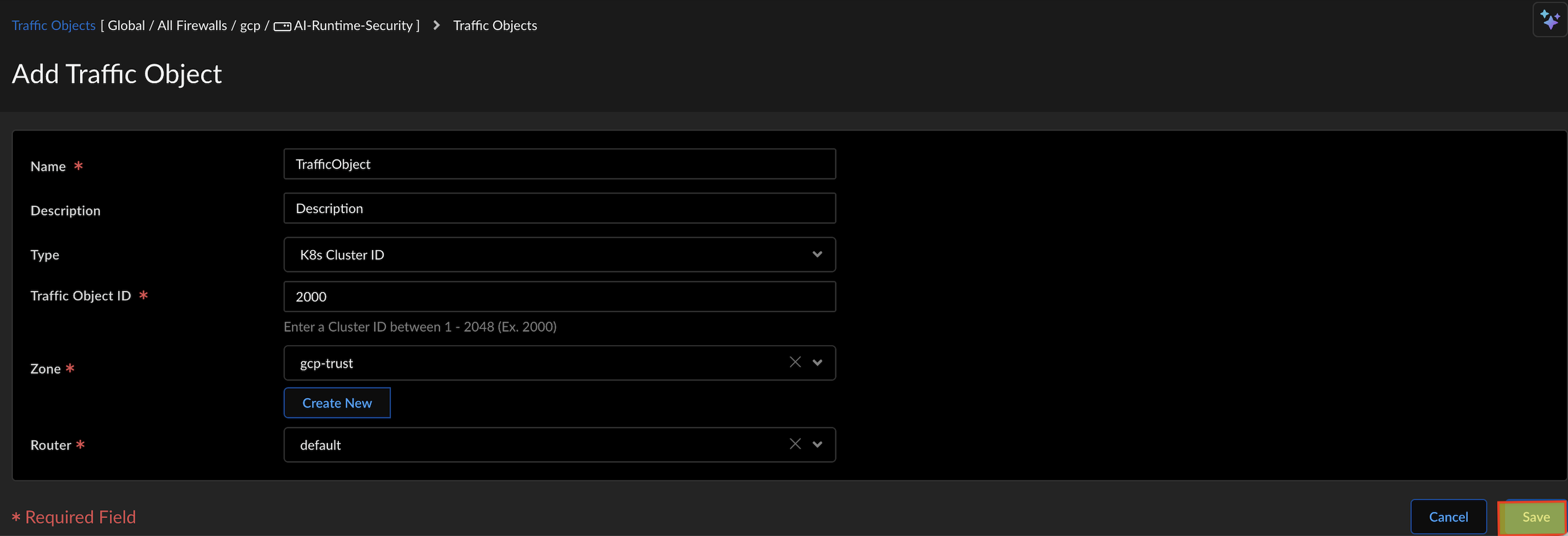
![]() Enter a Name for the Traffic Object.Write a Description.In the Type field, select K8s Cluster ID or VPC Endpoint ID.To get the VPC Endpoint ID, go to the AWS Console and search for VPC. Click on Endpoints, find your endpoint, and copy the ID from the "Endpoint ID" column. Refer to Create and View NGFW Endpoints.In the Traffic Object ID field, enter the K8s Cluster ID or the VPC Endpoint ID.
Enter a Name for the Traffic Object.Write a Description.In the Type field, select K8s Cluster ID or VPC Endpoint ID.To get the VPC Endpoint ID, go to the AWS Console and search for VPC. Click on Endpoints, find your endpoint, and copy the ID from the "Endpoint ID" column. Refer to Create and View NGFW Endpoints.In the Traffic Object ID field, enter the K8s Cluster ID or the VPC Endpoint ID.- If the type is K8s Cluster ID, the traffic object ID values can be between 1-2048.
- If the type is VPC Endpoint ID, the Traffic Object ID format is:vpc-xxxxxxxxxxxxxxxxx (with 17 alphanumeric characters)
- Select the existing ingress Zone for the traffic object or create a new zone.Select the Router. Refer to the section on how to configure a Logical Router.Select Save to create the traffic object.This creates a sub-interface using the zone and the Traffic Object ID, and we map the sub-interface to the zone. This zone defines granular security policies on the cloud assets within a zone.Ensure that the traffic object is attached to a zone within the security policy. You can associate traffic objects with either a new zone and attach it to a security policy or with an existing zone that is already part of a security policy.
Panorama
Create traffic objects to specify cloud entities within specific clusters or VPC endpoints to enforce customized security policy rules.This page helps you to create a traffic object with specific cloud assets and map the traffic object to a zone. Attach the zone to a security policy to enforce the policy rules on the AI traffic sourced from this zone. To create a policy object of type traffic objects:- Log in to the Panorama Web Interface.Navigate to Network Traffic Objects.Select Add.
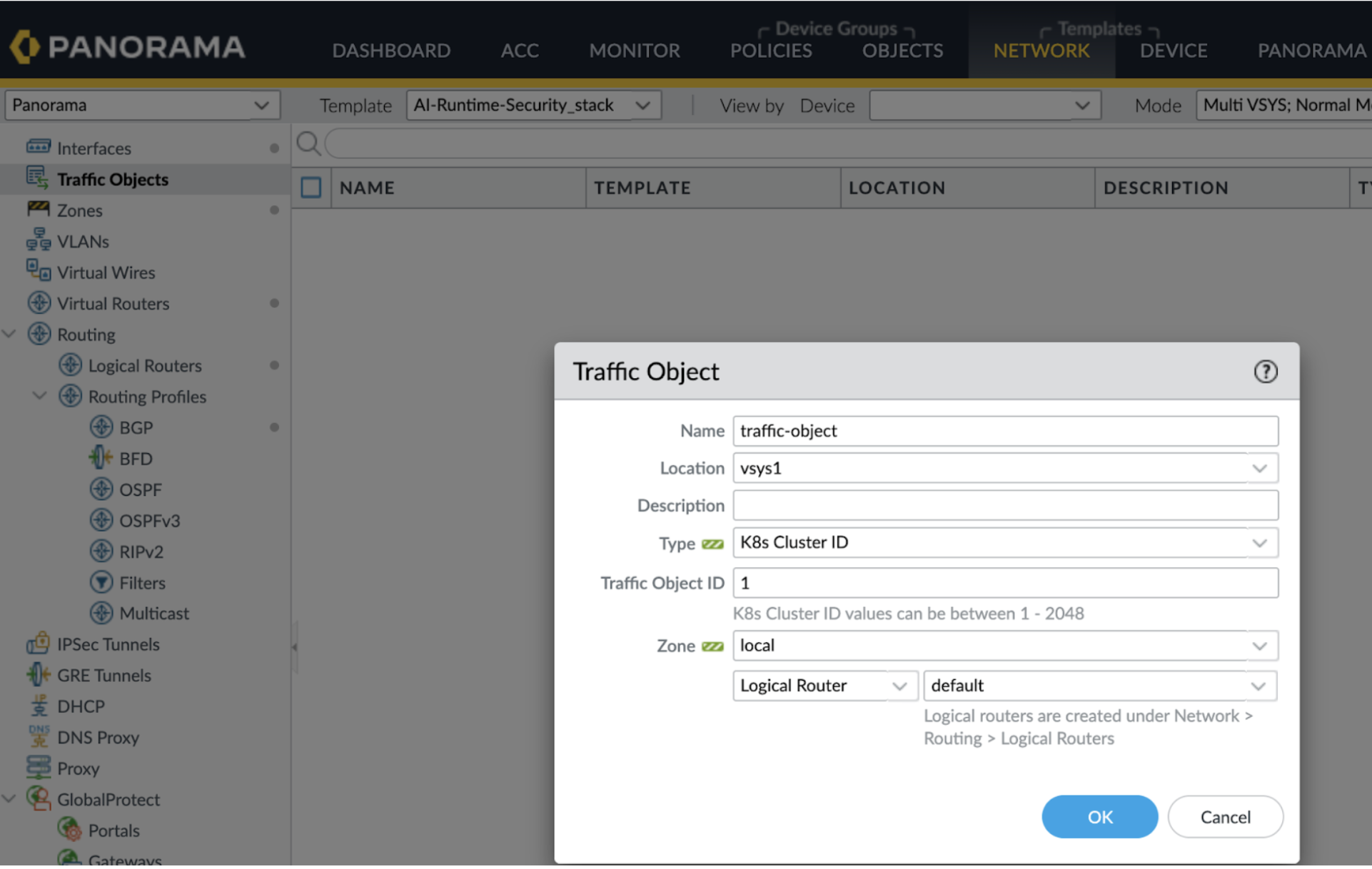
![]() Enter a Name for the Traffic Object.In the Location field, select your virtual systems.Write a Description.In the Type field, select K8s Cluster ID or VPC Endpoint ID.To get the VPC Endpoint ID, go to the AWS Console and search for VPC. Click on Endpoints, find your endpoint, and copy the ID from the "Endpoint ID" column. Refer to Create and View NGFW Endpoints.In the Traffic Object ID field, enter the K8s Cluster ID or the VPC Endpoint ID.
Enter a Name for the Traffic Object.In the Location field, select your virtual systems.Write a Description.In the Type field, select K8s Cluster ID or VPC Endpoint ID.To get the VPC Endpoint ID, go to the AWS Console and search for VPC. Click on Endpoints, find your endpoint, and copy the ID from the "Endpoint ID" column. Refer to Create and View NGFW Endpoints.In the Traffic Object ID field, enter the K8s Cluster ID or the VPC Endpoint ID.- If the type is K8s Cluster ID, the traffic object ID values can be between 1-2048.
- If the type is VPC Endpoint ID, the Traffic Object ID format is:vpc-xxxxxxxxxxxxxxxxx (with 17 alphanumeric characters)
- Select the existing ingress Zone for the traffic object or create a new zone.Select the Logical Router from the list or create a new Logical Router under Network Routing Logical Routers.You don’t have to configure the Virtual router, as advanced routing is enabled by defaultSelect OK to create the traffic object.