Network Security
Security Profile: AI Security
Table of Contents
Expand All
|
Collapse All
Network Security Docs
Security Profile: AI Security
The page helps you to create an AI security profile in Strata Cloud Manager.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
This page helps you to create an AI security profile and associate this
profile with a security policy to monitor the AI traffic passing through the Prisma AIRS AI Runtime: Network intercept.
An AI security profile protects AI traffic and is only available for Prisma AIRS: Network intercept firewalls.
The AI security profile helps you to configure specific protections to
protect your cloud network architecture. This profile can only be configured from
Strata Cloud Manager and Panorama. See AI Runtime Security: Network intercept for details.
The Prisma AIRS: Network intercept monitors the AI
and non-AI traffic against AI security policy rules and reduces the security risks
that surface during interactions with AI models.
An AI security profile helps you to configure:
- AI application protection with protections like AI URL categorization
- AI model protection to protect your AI models against threats such as prompt injections
- AI data protection to protect against for example; sensitive data leakage to and from AI models
To create an AI security profile:
- Log in to Strata Cloud Manager.Go to Manage > Configuration > NGFW and Prisma Access > Security Services > AI Security.The AI security profile will be available at the folder/snippet/device level for all devices.Select the Configuration Scope as Global or limit it to your AI security profile.Select AI Security and Add Profile.
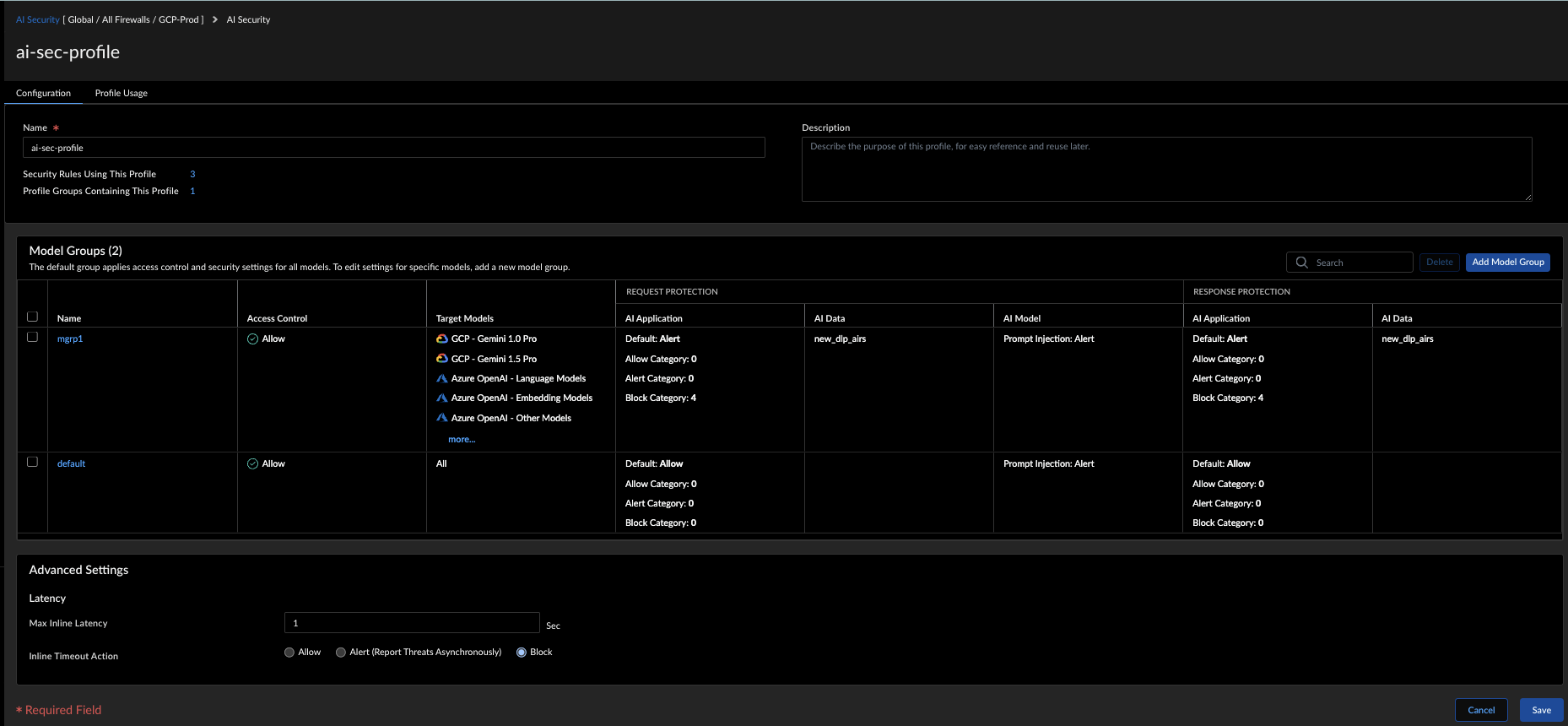
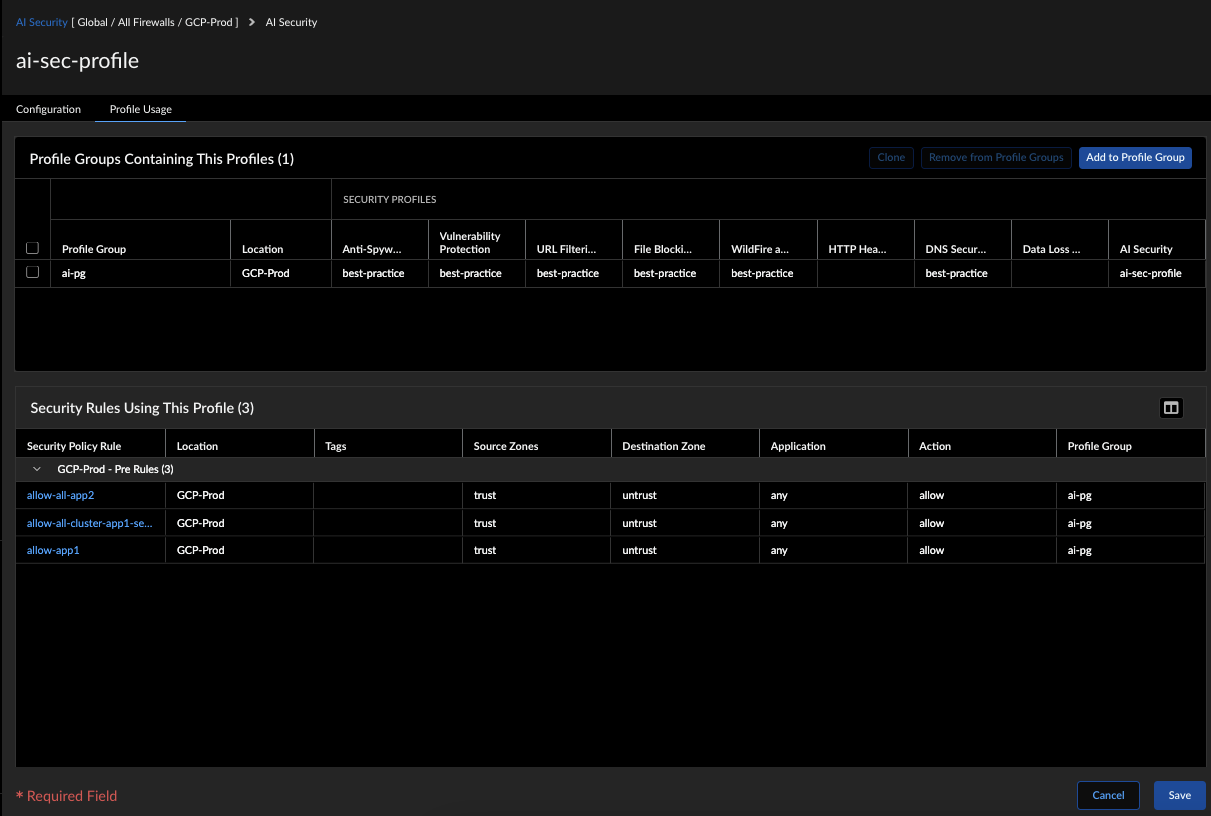
![]() Enter a Name and a Description.Add Model Group for customized protections including AI application protection, AI data protection, and AI model protection. See Create Model Groups for Customized Protections.Set the Max Inline Latency for AI Security detection runtime latency (# milliseconds) for traffic that hits a specific AI security profile.Select Save to create the profile.In the Profile Usage section, you can see the profile groups to which this AI security profile is currently attached. You have the option to add this security profile to additional profile groups, clone a profile group, or remove the security profile from any existing profile group. This section also details the security policy rules associated with the AI security profile.
Enter a Name and a Description.Add Model Group for customized protections including AI application protection, AI data protection, and AI model protection. See Create Model Groups for Customized Protections.Set the Max Inline Latency for AI Security detection runtime latency (# milliseconds) for traffic that hits a specific AI security profile.Select Save to create the profile.In the Profile Usage section, you can see the profile groups to which this AI security profile is currently attached. You have the option to add this security profile to additional profile groups, clone a profile group, or remove the security profile from any existing profile group. This section also details the security policy rules associated with the AI security profile.![]() Next, set up security rules and link the AI security profile to enforce these protections on the traffic.
Next, set up security rules and link the AI security profile to enforce these protections on the traffic.