Install the Device Certificate for a Managed Firewall
Table of Contents
9.1 (EoL)
Expand all | Collapse all
-
- Determine Panorama Log Storage Requirements
-
- Setup Prerequisites for the Panorama Virtual Appliance
- Perform Initial Configuration of the Panorama Virtual Appliance
- Set Up The Panorama Virtual Appliance as a Log Collector
- Set Up the Panorama Virtual Appliance with Local Log Collector
- Set up a Panorama Virtual Appliance in Panorama Mode
- Set up a Panorama Virtual Appliance in Management Only Mode
-
- Preserve Existing Logs When Adding Storage on Panorama Virtual Appliance in Legacy Mode
- Add a Virtual Disk to Panorama on an ESXi Server
- Add a Virtual Disk to Panorama on vCloud Air
- Add a Virtual Disk to Panorama on AWS
- Add a Virtual Disk to Panorama on Azure
- Add a Virtual Disk to Panorama on Google Cloud Platform
- Add a Virtual Disk to Panorama on KVM
- Add a Virtual Disk to Panorama on Hyper-V
- Mount the Panorama ESXi Server to an NFS Datastore
-
- Increase CPUs and Memory for Panorama on an ESXi Server
- Increase CPUs and Memory for Panorama on vCloud Air
- Increase CPUs and Memory for Panorama on AWS
- Increase CPUs and Memory for Panorama on Azure
- Increase CPUs and Memory for Panorama on Google Cloud Platform
- Increase CPUs and Memory for Panorama on KVM
- Increase CPUs and Memory for Panorama on Hyper-V
- Complete the Panorama Virtual Appliance Setup
-
- Convert Your Evaluation Panorama to a Production Panorama with Local Log Collector
- Convert Your Evaluation Panorama to a Production Panorama without Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing with Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing without Local Log Collector
- Convert Your Production Panorama to an ELA Panorama
-
- Register Panorama
- Activate a Panorama Support License
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is Internet-connected
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is not Internet-connected
- Activate/Retrieve a Firewall Management License on the M-Series Appliance
- Install the Panorama Device Certificate
-
- Migrate from a Panorama Virtual Appliance to an M-Series Appliance
- Migrate a Panorama Virtual Appliance to a Different Hypervisor
- Migrate from an M-Series Appliance to a Panorama Virtual Appliance
- Migrate from an M-100 Appliance to an M-500 Appliance
- Migrate from an M-100 or M-500 Appliance to an M-200 or M-600 Appliance
-
- Configure an Admin Role Profile
- Configure an Access Domain
-
- Configure a Panorama Administrator Account
- Configure Local or External Authentication for Panorama Administrators
- Configure a Panorama Administrator with Certificate-Based Authentication for the Web Interface
- Configure an Administrator with SSH Key-Based Authentication for the CLI
- Configure RADIUS Authentication for Panorama Administrators
- Configure TACACS+ Authentication for Panorama Administrators
- Configure SAML Authentication for Panorama Administrators
-
- Add a Firewall as a Managed Device
-
- Add a Device Group
- Create a Device Group Hierarchy
- Create Objects for Use in Shared or Device Group Policy
- Revert to Inherited Object Values
- Manage Unused Shared Objects
- Manage Precedence of Inherited Objects
- Move or Clone a Policy Rule or Object to a Different Device Group
- Push a Policy Rule to a Subset of Firewalls
- Manage the Rule Hierarchy
- Manage the Master Key from Panorama
- Redistribute User-ID Information to Managed Firewalls
-
- Plan the Transition to Panorama Management
- Migrate a Firewall to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall to Panorama Management and Push a New Configuration
- Migrate a Firewall HA Pair to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall HA Pair to Panorama Management and Push a New Configuration
- Load a Partial Firewall Configuration into Panorama
- Localize a Panorama Pushed Configuration on a Managed Firewall
-
- Add Standalone WildFire Appliances to Manage with Panorama
- Configure Basic WildFire Appliance Settings on Panorama
- Remove a WildFire Appliance from Panorama Management
-
-
- Configure a Cluster and Add Nodes on Panorama
- Configure General Cluster Settings on Panorama
- Remove a Cluster from Panorama Management
- Configure Appliance-to-Appliance Encryption Using Predefined Certificates Centrally on Panorama
- Configure Appliance-to-Appliance Encryption Using Custom Certificates Centrally on Panorama
- View WildFire Cluster Status Using Panorama
- Upgrade a Cluster Centrally on Panorama with an Internet Connection
- Upgrade a Cluster Centrally on Panorama without an Internet Connection
-
-
- Manage Licenses on Firewalls Using Panorama
-
- Supported Updates
- Schedule a Content Update Using Panorama
- Upgrade Log Collectors When Panorama Is Internet-Connected
- Upgrade Log Collectors When Panorama Is Not Internet-Connected
- Upgrade Firewalls When Panorama Is Internet-Connected
- Upgrade Firewalls When Panorama Is Not Internet-Connected
- Upgrade a ZTP Firewall
- Revert Content Updates from Panorama
-
- Preview, Validate, or Commit Configuration Changes
- Enable Automated Commit Recovery
- Compare Changes in Panorama Configurations
- Manage Locks for Restricting Configuration Changes
- Add Custom Logos to Panorama
- Use the Panorama Task Manager
- Reboot or Shut Down Panorama
- Configure Panorama Password Profiles and Complexity
-
-
- Verify Panorama Port Usage
- Resolve Zero Log Storage for a Collector Group
- Replace a Failed Disk on an M-Series Appliance
- Replace the Virtual Disk on an ESXi Server
- Replace the Virtual Disk on vCloud Air
- Migrate Logs to a New M-Series Appliance in Log Collector Mode
- Migrate Logs to a New M-Series Appliance in Panorama Mode
- Migrate Logs to a New M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Logs to the Same M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Log Collectors after Failure/RMA of Non-HA Panorama
- Regenerate Metadata for M-Series Appliance RAID Pairs
- Troubleshoot Registration or Serial Number Errors
- Troubleshoot Reporting Errors
- Troubleshoot Device Management License Errors
- Troubleshoot Automatically Reverted Firewall Configurations
- Complete Content Update When Panorama HA Peer is Down
- View Task Success or Failure Status
- Restore an Expired Device Certificate
- Downgrade from Panorama 9.1
End-of-Life (EoL)
Install the Device Certificate for a Managed Firewall
Install the device certificate for managed firewalls
from the Panorama™ management server.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
|
Select and install the device certificate for managed firewalls from the Panorama
management server to use one or more cloud services. You only need to install a
device certificate once. The device certificate has a 90-day lifetime. The firewall
re-installs the device certificate 15 days before the certificate expires. In the
event the firewall is unable to reinstall the device certificate on its own, you may
need to manually restore an expired device certificate.
To successfully install the device certificate on a firewall, the firewall must have
outbound internet access and the following Fully Qualified Domain Names (FQDN) and
ports must be allowed on your network in order to reach to the CSP. Additionally,
the managed firewall must belong to the same CSP account as Panorama in order to
generate the One Time Password (OTP) used to install the device certificate.
|
FQDN
|
Ports
|
|---|---|
|
TCP 80
|
|
TCP 443
|
|
TCP 444 and TCP 443
|
- Log in to the Panorama Web Interface as a Superuser.A Panorama admin with Superuser access privileges is required to generate OTP Request Token and apply the OTP used to install the device certificate on a managed firewall.
- (Best Practices) Configure the Network Time Protocol (NTP) server for
Panorama.An NTP server is required validate the device certification expiration date, ensure the device certificate does not expire early or become invalid.
- Select PanoramaSetupServices.
- Select NTP and enter the hostname or IP address of the Primary NTP Server.
- (Optional) Enter a the hostname or IP address of the Secondary NTP Server.
- (Optional) To authenticate time updates from the NTP
server(s), for Authentication Type, select one of
the following for each server.
-
None (default)—Disables NTP authentication.
-
Symmetric Key—Firewall uses symmetric key exchange (shared secrets) to authenticate time updates.
-
Key ID—Enter the Key ID (1-65534)
-
Algorithm—Select the algorithm to use in NTP authentication (MDS or SHA1)
-
-
- Click OK to save your configuration changes.
- Select Commit and Commit to Panorama.
- Configure the Network Time Protocol (NTP) server.An NTP server is required validate the device certification expiration date, ensure the device certificate does not expire early or become invalid.
- Select DeviceSetupServices and select the Template.
- Select one of the following depending on your platform:
- For multi-virtual system platforms, select Global and edit the Services section.
-
For single virtual system platforms, edit the Services section.
- Select NTP and enter the hostname or IP address of the Primary NTP Server.
- (Optional) Enter a the hostname or IP address of the Secondary NTP Server.
- (Optional) To authenticate time updates from the NTP
server(s), for Authentication Type, select one of
the following for each server.
-
None (default)—Disables NTP authentication.
-
Symmetric Key—Firewall uses symmetric key exchange (shared secrets) to authenticate time updates.
-
Key ID—Enter the Key ID (1-65534)
-
Algorithm—Select the algorithm to use in NTP authentication (MDS or SHA1)
-
-
- Click OK to save your configuration changes.
- Select Commit and Commit and Push your configuration changes to your managed firewalls.
- Generate the OTP Request Token on Panorama.The OTP Request Token generated on Panorama is used to generate the OTP required to install the device certificate on a managed firewall.
- Select PanoramaManaged DevicesSummary.
- Select one or more managed firewalls.
- Select Request OTP From CSPCustom selected devices.
- Copy the entire output in the OTP Request Token field.
- Generate the One Time Password (OTP) for managed firewalls. OTP lifetime is 60 minutes and expires if not used within the 60 minute lifetime.Firewall may only attempt to retrieve the OTP from the CSP one time. If the firewall fails for any reason to fetch the OTP, the OTP expires and you must generate a new OTP.
- Log in to the Customer Support Portal with a user role that has permission to generate an OTP.
- Select ProductsDevice Certificates and Generate OTP.
- For the Device Type, select Generate OTP for Panorama managed firewalls and click Next.
- Paste the OTP request you copied in the previous step and Generate OTP.
- Click Done and wait a few minutes for the OTP to successfully generate.
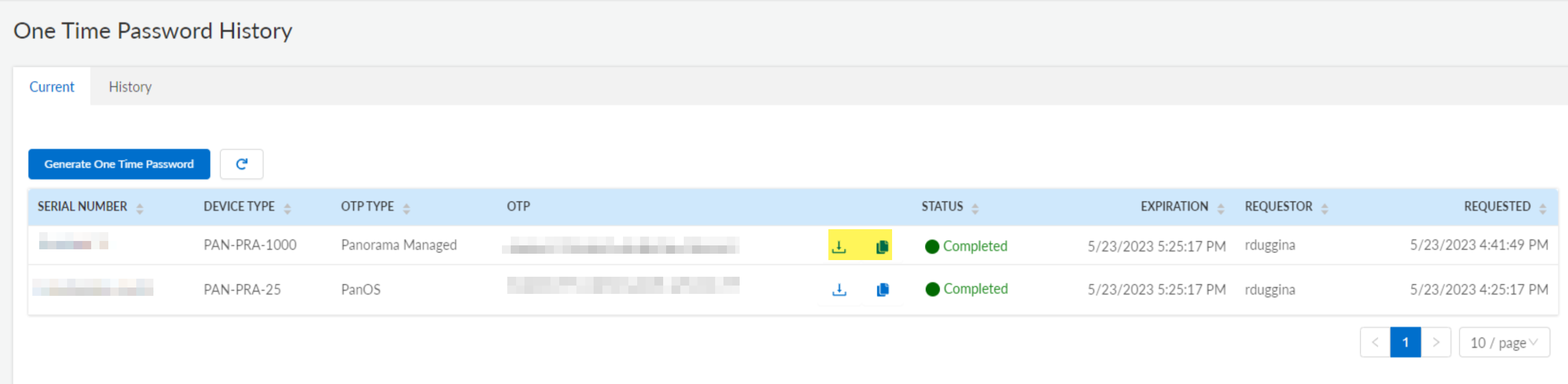
- View OTP History.
- In the Current One Time Password History, copy or download the OTP
- Copy to Clipboard or
Download the OTP.
![]()
- Install the device certificate on managed firewalls.Managed firewalls must have an outbound internet connection to successfully install the device certificate. After you upload the OTP from Panorama, each managed firewall connects to the Palo Alto Networks CSP to install the device certificate.
- Log in to the Panorama web interface as a Superuser user.
- Select PanoramaManaged DevicesSummary and Upload OTP.
- Paste the OTP you generated and Upload.You must still copy and paste the OTP generated from the Palo Alto Networks CSP even if you downloaded the OTP in the previous step. Uploading the file containing the OTP is not supported.
- (WildFire and Advanced WildFire) Log in to the firewall CLI and refresh
the firewall settings to establish a connection to the Advanced WildFire cloud
with the updated device certificate.Repeat this step for each managed firewall with an activate WildFire or Advanced WildFire subscription that is actively communicating with the Advanced WildFire cloud service.admin>request wildfire registration channel public
- Verify that the Device Certificate column displays as Valid and that the Device Certificate Expiry Date displays an expiration date.