Upgrade Firewalls When Panorama Is Internet-Connected
Table of Contents
9.1 (EoL)
Expand all | Collapse all
-
- Determine Panorama Log Storage Requirements
-
- Setup Prerequisites for the Panorama Virtual Appliance
- Perform Initial Configuration of the Panorama Virtual Appliance
- Set Up The Panorama Virtual Appliance as a Log Collector
- Set Up the Panorama Virtual Appliance with Local Log Collector
- Set up a Panorama Virtual Appliance in Panorama Mode
- Set up a Panorama Virtual Appliance in Management Only Mode
-
- Preserve Existing Logs When Adding Storage on Panorama Virtual Appliance in Legacy Mode
- Add a Virtual Disk to Panorama on an ESXi Server
- Add a Virtual Disk to Panorama on vCloud Air
- Add a Virtual Disk to Panorama on AWS
- Add a Virtual Disk to Panorama on Azure
- Add a Virtual Disk to Panorama on Google Cloud Platform
- Add a Virtual Disk to Panorama on KVM
- Add a Virtual Disk to Panorama on Hyper-V
- Mount the Panorama ESXi Server to an NFS Datastore
-
- Increase CPUs and Memory for Panorama on an ESXi Server
- Increase CPUs and Memory for Panorama on vCloud Air
- Increase CPUs and Memory for Panorama on AWS
- Increase CPUs and Memory for Panorama on Azure
- Increase CPUs and Memory for Panorama on Google Cloud Platform
- Increase CPUs and Memory for Panorama on KVM
- Increase CPUs and Memory for Panorama on Hyper-V
- Complete the Panorama Virtual Appliance Setup
-
- Convert Your Evaluation Panorama to a Production Panorama with Local Log Collector
- Convert Your Evaluation Panorama to a Production Panorama without Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing with Local Log Collector
- Convert Your Evaluation Panorama to VM-Flex Licensing without Local Log Collector
- Convert Your Production Panorama to an ELA Panorama
-
- Register Panorama
- Activate a Panorama Support License
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is Internet-connected
- Activate/Retrieve a Firewall Management License when the Panorama Virtual Appliance is not Internet-connected
- Activate/Retrieve a Firewall Management License on the M-Series Appliance
- Install the Panorama Device Certificate
-
- Migrate from a Panorama Virtual Appliance to an M-Series Appliance
- Migrate a Panorama Virtual Appliance to a Different Hypervisor
- Migrate from an M-Series Appliance to a Panorama Virtual Appliance
- Migrate from an M-100 Appliance to an M-500 Appliance
- Migrate from an M-100 or M-500 Appliance to an M-200 or M-600 Appliance
-
- Configure an Admin Role Profile
- Configure an Access Domain
-
- Configure a Panorama Administrator Account
- Configure Local or External Authentication for Panorama Administrators
- Configure a Panorama Administrator with Certificate-Based Authentication for the Web Interface
- Configure an Administrator with SSH Key-Based Authentication for the CLI
- Configure RADIUS Authentication for Panorama Administrators
- Configure TACACS+ Authentication for Panorama Administrators
- Configure SAML Authentication for Panorama Administrators
-
- Add a Firewall as a Managed Device
-
- Add a Device Group
- Create a Device Group Hierarchy
- Create Objects for Use in Shared or Device Group Policy
- Revert to Inherited Object Values
- Manage Unused Shared Objects
- Manage Precedence of Inherited Objects
- Move or Clone a Policy Rule or Object to a Different Device Group
- Push a Policy Rule to a Subset of Firewalls
- Manage the Rule Hierarchy
- Manage the Master Key from Panorama
- Redistribute User-ID Information to Managed Firewalls
-
- Plan the Transition to Panorama Management
- Migrate a Firewall to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall to Panorama Management and Push a New Configuration
- Migrate a Firewall HA Pair to Panorama Management and Reuse Existing Configuration
- Migrate a Firewall HA Pair to Panorama Management and Push a New Configuration
- Load a Partial Firewall Configuration into Panorama
- Localize a Panorama Pushed Configuration on a Managed Firewall
-
- Add Standalone WildFire Appliances to Manage with Panorama
- Configure Basic WildFire Appliance Settings on Panorama
- Remove a WildFire Appliance from Panorama Management
-
-
- Configure a Cluster and Add Nodes on Panorama
- Configure General Cluster Settings on Panorama
- Remove a Cluster from Panorama Management
- Configure Appliance-to-Appliance Encryption Using Predefined Certificates Centrally on Panorama
- Configure Appliance-to-Appliance Encryption Using Custom Certificates Centrally on Panorama
- View WildFire Cluster Status Using Panorama
- Upgrade a Cluster Centrally on Panorama with an Internet Connection
- Upgrade a Cluster Centrally on Panorama without an Internet Connection
-
-
- Manage Licenses on Firewalls Using Panorama
-
- Supported Updates
- Schedule a Content Update Using Panorama
- Upgrade Log Collectors When Panorama Is Internet-Connected
- Upgrade Log Collectors When Panorama Is Not Internet-Connected
- Upgrade Firewalls When Panorama Is Internet-Connected
- Upgrade Firewalls When Panorama Is Not Internet-Connected
- Upgrade a ZTP Firewall
- Revert Content Updates from Panorama
-
- Preview, Validate, or Commit Configuration Changes
- Enable Automated Commit Recovery
- Compare Changes in Panorama Configurations
- Manage Locks for Restricting Configuration Changes
- Add Custom Logos to Panorama
- Use the Panorama Task Manager
- Reboot or Shut Down Panorama
- Configure Panorama Password Profiles and Complexity
-
-
- Verify Panorama Port Usage
- Resolve Zero Log Storage for a Collector Group
- Replace a Failed Disk on an M-Series Appliance
- Replace the Virtual Disk on an ESXi Server
- Replace the Virtual Disk on vCloud Air
- Migrate Logs to a New M-Series Appliance in Log Collector Mode
- Migrate Logs to a New M-Series Appliance in Panorama Mode
- Migrate Logs to a New M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Logs to the Same M-Series Appliance Model in Panorama Mode in High Availability
- Migrate Log Collectors after Failure/RMA of Non-HA Panorama
- Regenerate Metadata for M-Series Appliance RAID Pairs
- Troubleshoot Registration or Serial Number Errors
- Troubleshoot Reporting Errors
- Troubleshoot Device Management License Errors
- Troubleshoot Automatically Reverted Firewall Configurations
- Complete Content Update When Panorama HA Peer is Down
- View Task Success or Failure Status
- Restore an Expired Device Certificate
- Downgrade from Panorama 9.1
End-of-Life (EoL)
Upgrade Firewalls When Panorama Is Internet-Connected
Procedure to upgrade managed firewalls when Panorama
is Internet connected.
Review the PAN-OS 9.1 Release Notes and
then use the following procedure to upgrade firewalls that you manage
with Panorama. This procedure applies to standalone firewalls and
firewalls deployed in a high availability (HA) configuration.
If Panorama is unable to connect directly
to the updates server, follow the Upgrade
Firewalls When Panorama Is Not Internet-Connected procedure
so that you can manually download images to Panorama and then distribute
the images to firewalls.
Before you can upgrade firewalls
from Panorama, you must:
- Make sure Panorama is running the same or a later PAN-OS version than you are upgrading to. Before upgrading managed firewalls to PAN-OS 9.1, you must Install Content and Software Updates for Panorama and Deploy Upgrades to Firewalls, Log Collectors, and WildFire Appliances Using Panorama to upgrade Panorama and Log Collectors to PAN-OS 9.1.
- Ensure that firewalls are connected to a reliable power source. A loss of power during an upgrade can make a firewall unusable.
- Save
a backup of the current configuration file on each managed firewall
you plan to upgrade.Although the firewall automatically creates a configuration backup, it is a best practice to create and externally store a backup before you upgrade.
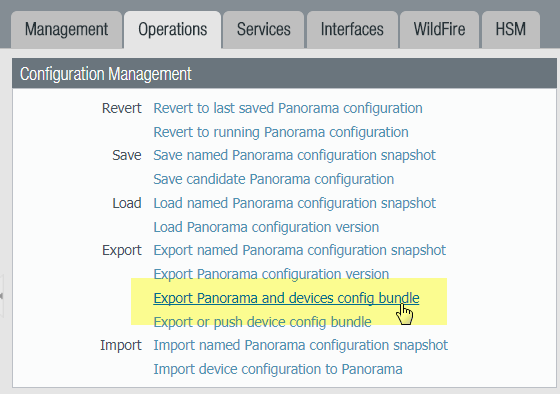
- From the Panorama web interface, select PanoramaSetupOperations and
click Export Panorama and devices config bundle to generate
and export the latest configuration backup of Panorama and of each
managed appliance.
![]()
- Save the exported file to a location external to the firewall. You can use this backup to restore the configuration if you have problems with the upgrade.
- From the Panorama web interface, select PanoramaSetupOperations and
click Export Panorama and devices config bundle to generate
and export the latest configuration backup of Panorama and of each
managed appliance.
- Update the content release version on the firewalls you
plan to upgrade.Refer to the Release Notes for the minimum content release version required for PAN-OS 9.1. Make sure to follow the Best Practices for Application and Threat Updates when deploying content updates to Panorama and managed firewalls.
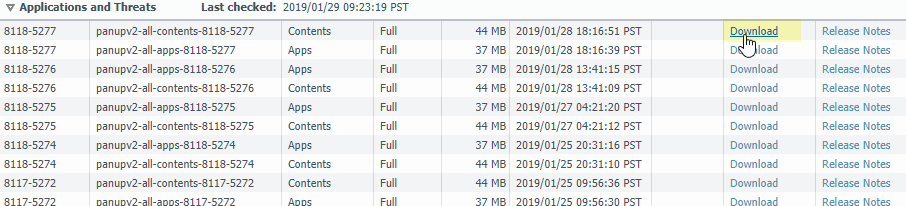
- Select PanoramaDevice DeploymentDynamic Updates and Check
Now for the latest updates. If an update is available,
the Action column displays a Download link.
![]()
- If not already installed, Download the latest content release version.
- Click Install, select the firewalls
on which you want to install the update, and click OK.
If you are upgrading HA firewalls, you must update content on both
peers.
![]() By default, you can upload a maximum of two software or content updates of each type to a Panorama appliance and if you download a third update of the same type, Panorama will delete the update for the earliest version of that type. If you need to upload more than two software updates or content updates of a single type, use the setmax-num-images count <number> CLI command to increase the maximum.
By default, you can upload a maximum of two software or content updates of each type to a Panorama appliance and if you download a third update of the same type, Panorama will delete the update for the earliest version of that type. If you need to upload more than two software updates or content updates of a single type, use the setmax-num-images count <number> CLI command to increase the maximum.
- Select PanoramaDevice DeploymentDynamic Updates and Check
Now for the latest updates. If an update is available,
the Action column displays a Download link.
- Determine the Upgrade Path to PAN-OS
9.1.You cannot skip installation of any feature release versions in the path from the currently running PAN-OS version to PAN-OS 9.1.0. Review the known issues and changes to default behavior in the Release Notes and upgrade/downgrade considerations in the New Features Guide for each release through which you pass as part of your upgrade path.If upgrading more than one firewall, streamline the process by determining upgrade paths for all firewalls before you start downloading images.
- (HA firewall upgrades only) If you will be upgrading
firewalls that are part of an HA pair, disable preemption. You need
only disable this setting on one firewall in each HA pair.
- Log in to the firewall web interface of one of the firewall HA peers.
- Select DeviceHigh Availability and edit the Election Settings.
- If enabled, disable (clear) the Preemptive setting
and click OK.
![]()
- Commit your change. Make sure the commit is successful before you proceed with the upgrade.
- (HA firewall upgrades only) Suspend the primary HA peer to force a
failover.(Active/passive firewalls) For firewalls in an active/passive HA configuration, suspend and upgrade the active HA peer first.(Active/active firewalls) For firewalls in an active/active HA configuration, suspend and upgrade the active-primary HA peer first.
- Log in to the firewall web interface of active primary firewall HA peer.
- Select DeviceHigh AvailabilityOperational Commands and Suspend local device for high availability.
- In the bottom-right corner, verify that the state is
suspended.The resulting failover should cause the secondary passive HA peer to transition to active state.The resulting failover verifies that HA failover is functioning properly before you upgrade.
- Download
the target PAN-OS 9.1. release image.
- Select PanoramaDevice DeploymentSoftware and Check Now for the latest release versions.
- Download the firewall-specific
file (or files) for the release version to which you are upgrading.
You must download a separate installation file for each firewall
model (or firewall series) that you intend to upgrade.For example, to upgrade your PA-220 and PA-5250 firewalls to PAN-OS 9.1.0, download the PanOS_220-9.1.0, PanOS_3000-9.1.0, and PanOS_5200-9.1.0 images. After you successfully download an image, the Action column changes to Install for that image.
- Install
the PAN-OS 9.1 software update on the firewalls.
- Click Install in the Action column that corresponds to the firewall models you want to upgrade. For example, if you want to upgrade your PA-220 firewalls, click Install in the row that corresponds to PanOS_220-9.1.0.
- In the Deploy Software file dialog, select all firewalls that you want to upgrade. To reduce downtime, select only one peer in each HA pair. For active/passive pairs, select the passive peer; for active/active pairs, select the active-secondary peer.
- (HA firewall upgrades only) Make sure Group HA Peers is not selected.
- Select Reboot device after install.
- To begin the upgrade, click OK.
- After the installation completes successfully, reboot
using one of the following methods:
- If you are prompted to reboot, click Yes.
- If you are not prompted to reboot, select DeviceSetupOperations and Reboot Device.
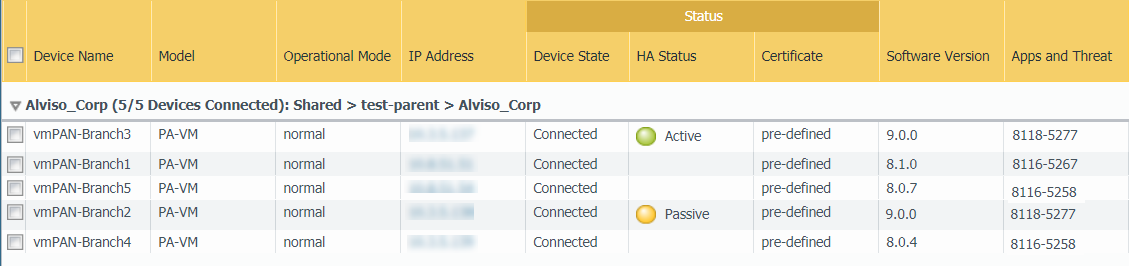
- After the firewalls finish rebooting, select PanoramaManaged Devices and verify the Software Version is 9.1.0 for the firewalls you upgraded. Also verify that the HA status of any passive firewalls you upgraded is still passive.
- (HA firewall upgrades only) Restore HA functionality to the primary HA
peer.
- Log in to the firewall web interface of suspended primary firewall HA peer.
- Select DeviceHigh AvailabilityOperational Commands and Make local device functional for high availability.
- In the bottom-right corner, verify that the state is Passive. For firewalls in an active/active configuration, verify that the state is Active.
- Wait for the HA peer running configuration to synchronize.In the Dashboard, monitor the Running Config status in the High Availability widget.
- (HA firewall upgrades only) Suspend the secondary HA peer to force a
failover back to the primary HA peer.
- Log in to the firewall web interface of active secondary firewall HA peer.
- Select DeviceHigh AvailabilityOperational Commands and Suspend local device for high availability.
- In the bottom-right corner, verify that the state is
suspended.The resulting failover should cause the primary passive HA peer to transition to active state.The resulting failover verifies that HA failover is functioning properly before you upgrade.
- (HA firewall upgrades only) Upgrade the second HA peer in each HA
pair.
- In the Panorma web interface, select PanoramaDevice DeploymentSoftware.
- Click Install in the Action column that corresponds to the firewall models of the HA pairs you are upgrading.
- In the Deploy Software file dialog, select all firewalls that you want to upgrade. This time, select only the peers of the HA firewalls you just upgraded.
- Make sure Group HA Peers is not selected.
- Select Reboot device after install.
- To begin the upgrade, click OK.
- After the installation completes successfully, reboot using one of the
following methods:
-
If you are prompted to reboot, click Yes.
-
If you are not prompted to reboot, select DeviceSetupOperations and Reboot Device.
-
- (HA firewall upgrades only) Restore HA functionality to the secondary
HA peer.
- Log in to the firewall web interface of suspended secondary firewall HA peer.
- Select DeviceHigh AvailabilityOperational Commands and Make local device functional for high availability.
- In the bottom-right corner, verify that the state is Passive. For firewalls in an active/active configuration, verify that the state is Active.
- Wait for the HA peer running configuration to synchronize.In the Dashboard, monitor the Running Config status in the High Availability widget.
- Verify the software and content release version running
on each managed firewall.
- On Panorama, select PanoramaManaged Devices.
- Locate the firewalls and review the content and software
versions in the table.For HA firewalls, you can also verify that the HA Status of each peer is as expected.
![]()
- (HA firewall upgrades only)If you disabled preemption on one of your HA firewalls before you upgraded, then edit the Election Settings (DeviceHigh Availability) and re-enable the Preemptive setting for that firewall and then Commit the change.