Configure Active/Passive HA on AWS Using a Secondary IP
Table of Contents
Expand all | Collapse all
-
- VM-Series Deployments
- VM-Series in High Availability
- Enable Jumbo Frames on the VM-Series Firewall
- Hypervisor Assigned MAC Addresses
- Custom PAN-OS Metrics Published for Monitoring
- Interface Used for Accessing External Services on the VM-Series Firewall
- PacketMMAP and DPDK Driver Support
- Enable NUMA Performance Optimization on the VM-Series
- Enable ZRAM on the VM-Series Firewall
-
- VM-Series Firewall Licensing
- Create a Support Account
- Serial Number and CPU ID Format for the VM-Series Firewall
- Use Panorama-Based Software Firewall License Management
-
- Maximum Limits Based on Tier and Memory
- Activate Credits
- Create a Deployment Profile
- Activate the Deployment Profile
- Manage a Deployment Profile
- Register the VM-Series Firewall (Software NGFW Credits)
- Provision Panorama
- Migrate Panorama to a Software NGFW License
- Transfer Credits
- Renew Your Software NGFW Credits
- Amend and Extend a Credit Pool
- Deactivate License (Software NGFW Credits)
- Delicense Ungracefully Terminated Firewalls
- Set the Number of Licensed vCPUs
- Customize Dataplane Cores
- Migrate a Firewall to a Flexible VM-Series License
-
- Generate Your OAuth Client Credentials
- Manage Deployment Profiles Using the Licensing API
- Create a Deployment Profile Using the Licensing API
- Update a Deployment Profile Using the Licensing API
- Get Serial Numbers Associated with an Authcode Using the API
- Deactivate a VM-Series Firewall Using the API
- What Happens When Licenses Expire?
-
- Supported Deployments on VMware vSphere Hypervisor (ESXi)
-
- Plan the Interfaces for the VM-Series for ESXi
- Provision the VM-Series Firewall on an ESXi Server
- Perform Initial Configuration on the VM-Series on ESXi
- Add Additional Disk Space to the VM-Series Firewall
- Use VMware Tools on the VM-Series Firewall on ESXi and vCloud Air
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Use the VM-Series CLI to Swap the Management Interface on ESXi
-
-
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (North-South)
- Components of the VM-Series Firewall on NSX-T (North-South)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Deploy the VM-Series Firewall
- Direct Traffic to the VM-Series Firewall
- Apply Security Policy to the VM-Series Firewall on NSX-T
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
-
- Components of the VM-Series Firewall on NSX-T (East-West)
- VM-Series Firewall on NSX-T (East-West) Integration
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (East-West)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Add a Service Chain
- Direct Traffic to the VM-Series Firewall
- Apply Security Policies to the VM-Series Firewall on NSX-T (East-West)
- Use vMotion to Move the VM-Series Firewall Between Hosts
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Create Dynamic Address Groups
- Create Dynamic Address Group Membership Criteria
- Generate Steering Policy
- Generate Steering Rules
- Delete a Service Definition from Panorama
- Migrate from VM-Series on NSX-T Operation to Security Centric Deployment
- Extend Security Policy from NSX-V to NSX-T
- Use In-Place Migration to Move Your VM-Series from NSX-V to NSX-T
-
-
- Deployments Supported on AWS
-
- Planning Worksheet for the VM-Series in the AWS VPC
- Launch the VM-Series Firewall on AWS
- Launch the VM-Series Firewall on AWS Outpost
- Create a Custom Amazon Machine Image (AMI)
- Encrypt EBS Volume for the VM-Series Firewall on AWS
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable CloudWatch Monitoring on the VM-Series Firewall
- VM-Series Firewall Startup and Health Logs on AWS
- Simplified Onboarding of VM-Series Firewall on AWS
-
- AWS Shared VPC Monitoring
- Use Case: Secure the EC2 Instances in the AWS Cloud
- Use Case: Use Dynamic Address Groups to Secure New EC2 Instances within the VPC
-
-
- What Components Does the VM-Series Auto Scaling Template for AWS (v2.0) Leverage?
- How Does the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1) Enable Dynamic Scaling?
- Plan the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1)
- Customize the Firewall Template Before Launch (v2.0 and v2.1)
- Launch the VM-Series Auto Scaling Template for AWS (v2.0)
- SQS Messaging Between the Application Template and Firewall Template
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.0)
- Modify Administrative Account and Update Stack (v2.0)
-
- Launch the Firewall Template (v2.1)
- Launch the Application Template (v2.1)
- Create a Custom Amazon Machine Image (v2.1)
- VM-Series Auto Scaling Template Cleanup (v2.1)
- SQS Messaging Between the Application Template and Firewall Template (v2.1)
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.1)
- Modify Administrative Account (v2.1)
- Change Scaling Parameters and CloudWatch Metrics (v2.1)
-
-
- KVM Host-Level Performance Tuning for VM-Series
- Intelligent Traffic Offload
-
- Deployments Supported on Azure
- Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
- Simplified Onboarding of VM-Series Firewall on Azure
- Deploy the VM-Series Firewall from the Azure China Marketplace (Solution Template)
- Deploy the VM-Series with the Azure Gateway Load Balancer
- Create a Custom VM-Series Image for Azure
- Deploy the VM-Series Firewall on Azure Stack
- Deploy the VM-Series Firewall on Azure Stack HCI
- Deploy VM-Series on Azure Stack Edge
- Enable Azure Application Insights on the VM-Series Firewall
- Set up Active/Passive HA on Azure
- Use the ARM Template to Deploy the VM-Series Firewall
-
- About the VM-Series Firewall on Google Cloud Platform
- Supported Deployments on Google Cloud Platform
- Prepare to Set Up VM-Series Firewalls on Google Public Cloud
- Create a Custom VM-Series Firewall Image for Google Cloud Platform
-
- Deploy the VM-Series Firewall from Google Cloud Platform Marketplace
- Management Interface Swap for Google Cloud Platform Load Balancing
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable Google Stackdriver Monitoring on the VM Series Firewall
- Enable VM Monitoring to Track VM Changes on Google Cloud Platform (GCP)
- Use Dynamic Address Groups to Secure Instances Within the VPC
- Use Custom Templates or the gcloud CLI to Deploy the VM-Series Firewall
-
- Prepare Your ACI Environment for Integration
-
-
- Create a Virtual Router and Security Zone
- Configure the Network Interfaces
- Configure a Static Default Route
- Create Address Objects for the EPGs
- Create Security Policy Rules
- Create a VLAN Pool and Domain
- Configure an Interface Policy for LLDP and LACP for East-West Traffic
- Establish the Connection Between the Firewall and ACI Fabric
- Create a VRF and Bridge Domain
- Create an L4-L7 Device
- Create a Policy-Based Redirect
- Create and Apply a Service Graph Template
-
- Create a VLAN Pool and External Routed Domain
- Configure an Interface Policy for LLDP and LACP for North-South Traffic
- Create an External Routed Network
- Configure Subnets to Advertise to the External Firewall
- Create an Outbound Contract
- Create an Inbound Web Contract
- Apply Outbound and Inbound Contracts to the EPGs
- Create a Virtual Router and Security Zone for North-South Traffic
- Configure the Network Interfaces
- Configure Route Redistribution and OSPF
- Configure NAT for External Connections
-
-
- Choose a Bootstrap Method
- VM-Series Firewall Bootstrap Workflow
- Bootstrap Package
- Bootstrap Configuration Files
- Generate the VM Auth Key on Panorama
- Create the bootstrap.xml File
- Prepare the Licenses for Bootstrapping
- Prepare the Bootstrap Package
- Bootstrap the VM-Series Firewall on AWS
- Bootstrap the VM-Series Firewall on Azure
- Bootstrap the VM-Series Firewall on Azure Stack HCI
- Bootstrap the VM-Series Firewall on Google Cloud Platform
- Verify Bootstrap Completion
- Bootstrap Errors
Configure Active/Passive HA on AWS Using a Secondary IP
Deploy VM-Series firewall as HA pair with a secondary IP address.
Complete the following procedure to deploy
new VM-Series firewalls as an HA pair with secondary IP addresses.
All VM-Series firewall interfaces must be assigned an
IPv4 address when deployed in a public cloud environment.
- Before you deploy the VM-Series firewalls for you HA pair, ensure the following:
- Refer to the VPC Planning Worksheet to ensure that your VPC is prepared for the VM-Series firewall.
- Secondary IP Move HA requires VM-Series plugin 2.0.1 or later.
- Deploy both HA peers in the same AWS availability zone.Starting with VM-Series plugin 2.0.3, you can deploy the HA peers in different availability zones. Although this type of deployment is not recommended, it is supported.
- Create an IAM role and assign the role to the VM-Series firewalls when you deploy the instances.
- The active and passive firewalls must have at least four interfaces each—a management interface, an HA2 interface, an untrust interface, and a trust interface. Additionally, the trust and untrust interfaces on the active firewall must assigned a secondary IP address.The management interface must be used as the HA1 interface.
- Verify that the network and security components are defined suitably.
- Enable communication to the internet from the management interface (at least udp/53 and tcp/443). The default VPC includes an internet gateway, and if you install the VM-Series firewall in the default subnet it has access to the internet.
- Create subnets. Subnets are segments of the IP address range assigned to the VPC in which you can launch the EC2 instances. The VM-Series firewall must belong to the public subnet so that it can be configured to access the internet.
- Create a data security group that includes the firewall data interfaces. Additionally, configure the security to allow all traffic (0.0.0.0/0), so security is enforced by the firewalls. This is required to maintain existing sessions during failover.
- Add routes to the route table for a private subnet to ensure that traffic can be routed across subnets and security groups in the VPC, as applicable.
- If you are bootstrapping the firewall, create the necessary S3 bucket containing the required bootstrap files.
Deploy the VM-Series Firewall on AWS.- If your VM-Series firewalls do not have the VM-Series plugin 2.0.1 or later installed, upgrade the plugin before continuing.Configure ethernet 1/1 as the HA2 interface on each HA peer.
- Open the Amazon EC2 console.
- Select Network Interface and then choose then select your network interface.
- Select ActionsManage IP Addresses.
- Leave the field blank to allow AWS to assign an IP address dynamically or enter an IP address within the subnet range for the VM-Series firewall.
- Click Yes and Update.
- Select ActionsChange Source/Dest. Check and select Disable.
- Repeat this process on the second (to be passive) HA peer.
Add a secondary IP address to your dataplane interfaces on the first (to be active) HA peer.- Select Network Interface and then choose then select your network interface.
- Select ActionsManage IP AddressesIPv4 AddressesAssign new IP.
- Leave the field blank to allow AWS to assign an IP address dynamically or enter an IP address within the subnet range for the VM-Series firewall.
- Click Yes and Update.
Associate an Elastic (public) IP address on the primary instance with the untrust interface of the active peer.- Select Elastic IPs and then choose the Elastic IP address to associate.
- Select ActionsAssociate Elastic IP.
- Under Resource Type, select Network Interface.
- Chose the network interface with which to associate the Elastic IP address.
- Click Associate.
For outbound traffic inspection, add an entry to the subnet route table that sets the next hop as the firewall trust interface.- Select VPCRoute Tables.
- Choose your subnet route table.
- Select ActionsEdit routesAdd route.
- Enter the Destination CIDR Block or IP address.
- For Target, enter the network interface of the firewall trust interface.
- Click Save routes.
To use AWS Ingress Routing, create a route table and associate the internet gateway to it. Then add an entry with the next hop set as the active firewall untrust interface.- Select Route TablesCreate route table.
- (Optional) Enter a descriptive Name tag for your route table.
- Click Create.
- Click your route table and select ActionsEdit edge associations.
- Select Internet gateways and choose your VPC internet gateway.
- Click Save.
- Click your route table and select ActionsEdit routes.
- For the Target, select Network Interface and choose the untrust interface of the active firewall.
- Click Save routes.
Configure the interfaces on the firewall. You must configure the HA2 data link and at least two Layer 3 interfaces for your untrust and trust interfaces. Complete this workflow on the first HA peer and then repeat the steps on the second HA peer.- Log in to the firewall web interface.Select NetworkInterfacesEthernet and click on your untrust interface. In this example, the HA2 interface is 1/1, the trust interface is ethernet 1/2, and the untrust interface is ethernet 1/3.Click the link for ethernet 1/1 and configure as follows:
- Interface Type: HA
Click the link for ethernet 1/2 and configure as follows:- Interface Type: Layer3
- On the Config tab, assign the interface to the default router.
- On the Config tab, expand the Security Zone drop-down and select New Zone. Define a new zone, for example trust-zone, and then click OK.
- On the IPv4 tab, select DHCP Client.
- Check Enable.
- On the untrust interface, check Automatically create default route pointing to default gateway provided by server. This option tells the firewall to create a static route to a default gateway.
- Repeat these steps for ethernet 1/3.
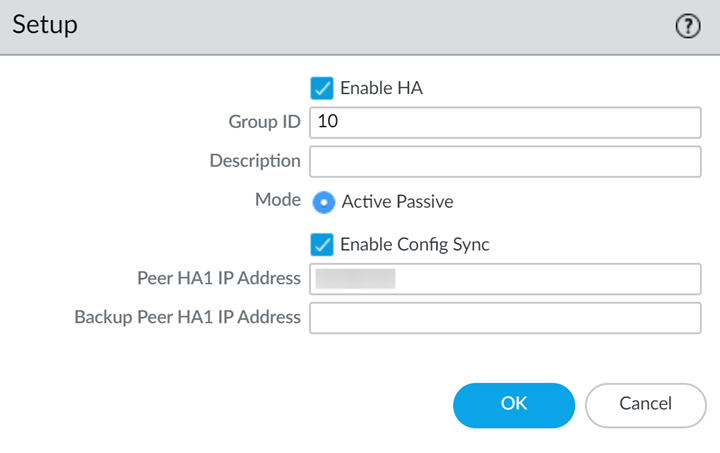
Repeat the above steps on the passive peer.Enable HA.- Select DeviceHigh AvailabilityGeneral.Edit the Setup settings.Enter the private IP address of the passive peer in the Peer HA1 IP address field.Click OK.
![]() Edit the Election Settings to specify a particular firewall to be the active peer. Enter a lower numerical Device Priority value on the active firewall. If both firewalls have the same Device Priority value, the firewall with the lowest MAC value on the HA1 control becomes the active firewall.Enabling preemption is not recommended.Click OK.Commit your changes.Repeat the above steps on the passive peer.Set up the Control Link (HA1) to use the management port.
Edit the Election Settings to specify a particular firewall to be the active peer. Enter a lower numerical Device Priority value on the active firewall. If both firewalls have the same Device Priority value, the firewall with the lowest MAC value on the HA1 control becomes the active firewall.Enabling preemption is not recommended.Click OK.Commit your changes.Repeat the above steps on the passive peer.Set up the Control Link (HA1) to use the management port.- Select DeviceHigh AvailabilityGeneral, and edit the Control Link (HA1) section.
![]() (Optional) Select Encryption Enabled, for secure HA communication between the peers. To enable encryption, you must export the HA key from a device and import it into the peer device.
(Optional) Select Encryption Enabled, for secure HA communication between the peers. To enable encryption, you must export the HA key from a device and import it into the peer device.- Select DeviceCertificate ManagementCertificates.
- Select Export HA key. Save the HA key to a network location that the peer device can access.
- On the peer device, navigate to DeviceCertificate ManagementCertificates, and select Import HA key to browse to the location that you saved the key and import it in to the peer device.
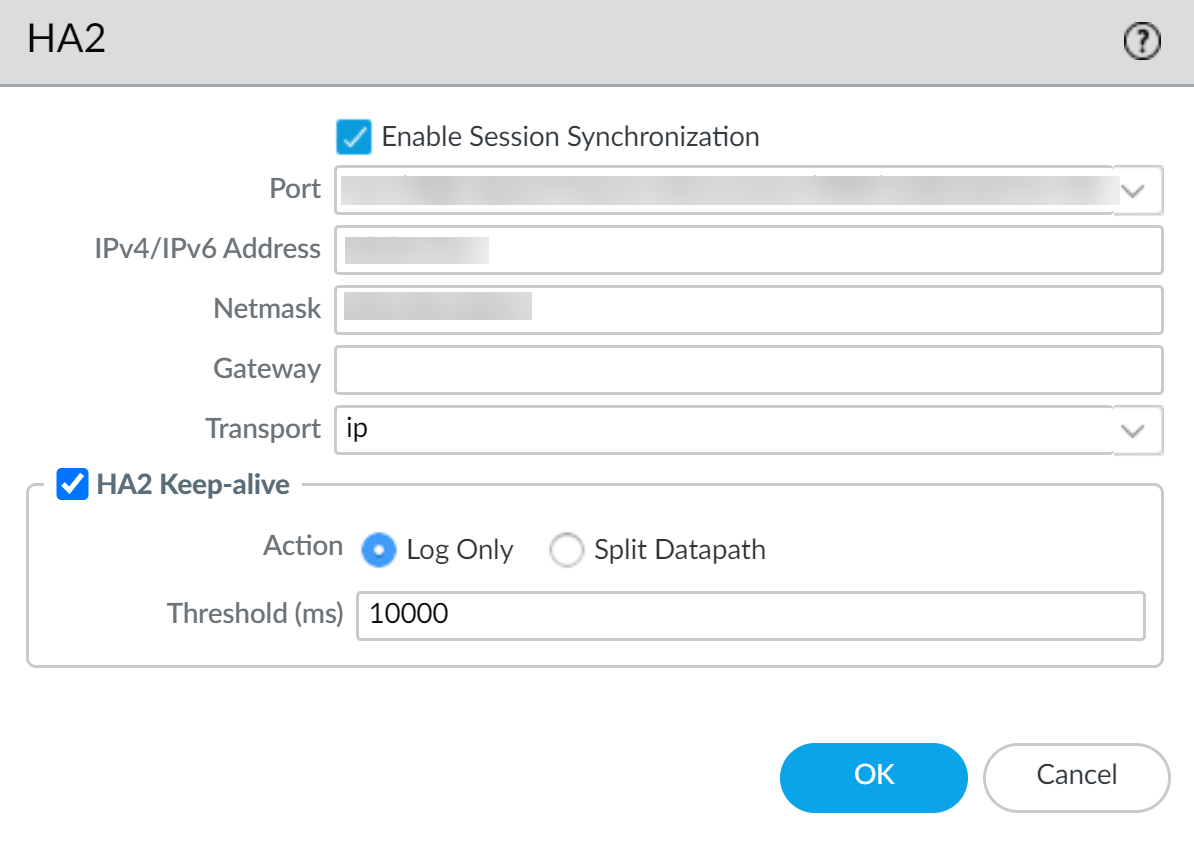
Set up the Data Link (HA2) to use ethernet1/1.- Select DeviceHigh AvailabilityGeneral, edit the Data Link (HA2) section.Select Port ethernet1/1.Enter the IP address for ethernet1/1. This IP address must be the same that assigned to the ENI on the EC2 Dashboard.Enter the Netmask.Enter a Gateway IP address if the HA1 interfaces are on separate subnets.Select IP or UDP for Transport. Use IP if you need Layer 3 transport (IP protocol number 99). Use UDP if you want the firewall to calculate the checksum on the entire packet rather than just the header, as in the IP option (UDP port 29281).
![]() (Optional) Modify the Threshold for HA2 Keep-alive packets. By default, HA2 Keep-alive is enabled for monitoring the HA2 data link between the peers. If a failure occurs and this threshold (default is 10000 ms) is exceeded, the defined action will occur. A critical system log message is generated when an HA2 keep-alive failure occurs.You can configure the HA2 keep-alive option on both devices, or just one device in the HA pair. If you enable this option on one device, only that device will send the keep-alive messages.After your finish configuring HA on both firewalls, verify that the firewalls are paired in active/passive HA.
(Optional) Modify the Threshold for HA2 Keep-alive packets. By default, HA2 Keep-alive is enabled for monitoring the HA2 data link between the peers. If a failure occurs and this threshold (default is 10000 ms) is exceeded, the defined action will occur. A critical system log message is generated when an HA2 keep-alive failure occurs.You can configure the HA2 keep-alive option on both devices, or just one device in the HA pair. If you enable this option on one device, only that device will send the keep-alive messages.After your finish configuring HA on both firewalls, verify that the firewalls are paired in active/passive HA.- Access the Dashboard on both firewalls and view the High Availability widget.On the active HA peer, click Sync to peer.Confirm that the firewalls are paired and synced.
- On the passive firewall: the state of the local firewall should display Passive and the Running Config should show as Synchronized.
- On the active firewall: the state of the local firewall should display Active and the Running Config should show as Synchronized.
From the firewall command line interface, execute the following commands:- To verify failover readiness:show plugins vm_series aws ha state
- To show secondary IP mapping:show plugins vm_series aws ha ips