Configure the Cisco ACI Plugin
Table of Contents
9.1 (EoL)
Expand all | Collapse all
-
- VM-Series Deployments
- VM-Series in High Availability
- Enable Jumbo Frames on the VM-Series Firewall
- Hypervisor Assigned MAC Addresses
- Custom PAN-OS Metrics Published for Monitoring
- Interface Used for Accessing External Services on the VM-Series Firewall
- PacketMMAP and DPDK Driver Support
-
- VM-Series Firewall Licensing
- Create a Support Account
- Serial Number and CPU ID Format for the VM-Series Firewall
-
- Activate Credits
- Transfer Credits
- Create a Deployment Profile
- Manage a Deployment Profile
- Provision Panorama
- Migrate Panorama to a Software NGFW License
- Renew Your Software NGFW Credits
- Amend and Extend a Credit Pool
- Deactivate License (Software NGFW Credits)
- Delicense Ungracefully Terminated Firewalls
- Create and Apply a Subscription-Only Auth Code
- Migrate to a Flexible VM-Series License
-
- Generate Your OAuth Client Credentials
- Manage Deployment Profiles Using the Licensing API
- Create a Deployment Profile Using the Licensing API
- Update a Deployment Profile Using the Licensing API
- Get Serial Numbers Associated with an Authcode Using the API
- Deactivate a VM-Series Firewall Using the API
- Use Panorama-Based Software Firewall License Management
- What Happens When Licenses Expire?
- Install a Device Certificate on the VM-Series Firewall
-
- Supported Deployments on VMware vSphere Hypervisor (ESXi)
-
- Plan the Interfaces for the VM-Series for ESXi
- Provision the VM-Series Firewall on an ESXi Server
- Perform Initial Configuration on the VM-Series on ESXi
- Add Additional Disk Space to the VM-Series Firewall
- Use VMware Tools on the VM-Series Firewall on ESXi and vCloud Air
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Use the VM-Series CLI to Swap the Management Interface on ESXi
-
-
- VM-Series Firewall for NSX-V Deployment Checklist
- Install the VMware NSX Plugin
- Apply Security Policies to the VM-Series Firewall
- Steer Traffic from Guests that are not Running VMware Tools
- Add a New Host to Your NSX-V Deployment
- Dynamically Quarantine Infected Guests
- Migrate Operations-Centric Configuration to Security-Centric Configuration
- Use Case: Shared Compute Infrastructure and Shared Security Policies
- Use Case: Shared Security Policies on Dedicated Compute Infrastructure
- Dynamic Address Groups—Information Relay from NSX-V Manager to Panorama
-
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (North-South)
- Components of the VM-Series Firewall on NSX-T (North-South)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Deploy the VM-Series Firewall
- Direct Traffic to the VM-Series Firewall
- Apply Security Policy to the VM-Series Firewall on NSX-T
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
-
- Components of the VM-Series Firewall on NSX-T (East-West)
- VM-Series Firewall on NSX-T (East-West) Integration
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (East-West)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Add a Service Chain
- Direct Traffic to the VM-Series Firewall
- Apply Security Policies to the VM-Series Firewall on NSX-T (East-West)
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
- Use Migration Coordinator to Move Your VM-Series from NSX-V to NSX-T
-
-
- Deployments Supported on AWS
-
- Planning Worksheet for the VM-Series in the AWS VPC
- Launch the VM-Series Firewall on AWS
- Launch the VM-Series Firewall on AWS Outpost
- Create a Custom Amazon Machine Image (AMI)
- Encrypt EBS Volume for the VM-Series Firewall on AWS
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable CloudWatch Monitoring on the VM-Series Firewall
- VM-Series Firewall Startup and Health Logs on AWS
- Use Case: Secure the EC2 Instances in the AWS Cloud
- Use Case: Use Dynamic Address Groups to Secure New EC2 Instances within the VPC
-
-
- What Components Does the VM-Series Auto Scaling Template for AWS (v2.0) Leverage?
- How Does the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1) Enable Dynamic Scaling?
- Plan the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1)
- Customize the Firewall Template Before Launch (v2.0 and v2.1)
- Launch the VM-Series Auto Scaling Template for AWS (v2.0)
- SQS Messaging Between the Application Template and Firewall Template
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.0)
- Modify Administrative Account and Update Stack (v2.0)
-
- Launch the Firewall Template (v2.1)
- Launch the Application Template (v2.1)
- Create a Custom Amazon Machine Image (v2.1)
- VM-Series Auto Scaling Template Cleanup (v2.1)
- SQS Messaging Between the Application Template and Firewall Template (v2.1)
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.1)
- Modify Administrative Account (v2.1)
- Change Scaling Parameters and CloudWatch Metrics (v2.1)
-
-
- Enable the Use of a SCSI Controller
- Verify PCI-ID for Ordering of Network Interfaces on the VM-Series Firewall
-
- Deployments Supported on Azure
- Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
- Deploy the VM-Series Firewall from the Azure China Marketplace (Solution Template)
- Deploy the VM-Series Firewall on Azure Stack
- Enable Azure Application Insights on the VM-Series Firewall
- Set up Active/Passive HA on Azure
- Use the ARM Template to Deploy the VM-Series Firewall
-
- About the VM-Series Firewall on Google Cloud Platform
- Supported Deployments on Google Cloud Platform
- Create a Custom VM-Series Firewall Image for Google Cloud Platform
- Prepare to Set Up VM-Series Firewalls on Google Public Cloud
-
- Deploy the VM-Series Firewall from Google Cloud Platform Marketplace
- Management Interface Swap for Google Cloud Platform Load Balancing
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable Google Stackdriver Monitoring on the VM Series Firewall
- Enable VM Monitoring to Track VM Changes on GCP
- Use Dynamic Address Groups to Secure Instances Within the VPC
- Locate VM-Series Firewall Images in the GCP Marketplace
-
- Prepare Your ACI Environment for Integration
-
-
- Create a Virtual Router and Security Zone
- Configure the Network Interfaces
- Configure a Static Default Route
- Create Address Objects for the EPGs
- Create Security Policy Rules
- Create a VLAN Pool and Domain
- Configure an Interface Policy for LLDP and LACP for East-West Traffic
- Establish the Connection Between the Firewall and ACI Fabric
- Create a VRF and Bridge Domain
- Create an L4-L7 Device
- Create a Policy-Based Redirect
- Create and Apply a Service Graph Template
-
- Create a VLAN Pool and External Routed Domain
- Configure an Interface Policy for LLDP and LACP for North-South Traffic
- Create an External Routed Network
- Configure Subnets to Advertise to the External Firewall
- Create an Outbound Contract
- Create an Inbound Web Contract
- Apply Outbound and Inbound Contracts to the EPGs
- Create a Virtual Router and Security Zone for North-South Traffic
- Configure the Network Interfaces
- Configure Route Redistribution and OSPF
- Configure NAT for External Connections
-
-
- Choose a Bootstrap Method
- VM-Series Firewall Bootstrap Workflow
- Bootstrap Package
- Bootstrap Configuration Files
- Generate the VM Auth Key on Panorama
- Create the bootstrap.xml File
- Prepare the Licenses for Bootstrapping
- Prepare the Bootstrap Package
- Bootstrap the VM-Series Firewall on AWS
- Bootstrap the VM-Series Firewall on Azure
- Bootstrap the VM-Series Firewall on Google Cloud Platform
- Verify Bootstrap Completion
- Bootstrap Errors
End-of-Life (EoL)
Configure the Cisco ACI Plugin
Establish a connection between Panorama and the APIC.
After installing the plugin, you must set
the monitoring interval, configure a notify group, and establish
a connection between Panorama and the APIC fabric.
- (Optional) Configure the full-sync interval.
- Log in to the Panorama CLI.
- Enter configure mode.admin@Panorama> configure
- Use the following command to set the full-sync interval.
The default interval is 600 seconds (10 minutes). The range is 600
seconds to 86,400 seconds (one day).admin@Panorama# set plugins cisco full-sync-interval <interval-in-seconds>
- Log in to the Panorama web interface.
- You must add the firewalls as managed devices on Panorama and create Device Groups so that you can configure Panorama to notify these groups with the VM information it retrieves. Device groups can include VM-Series firewalls or virtual systems on the hardware firewalls.
- Enable monitoring, set the monitoring interval, and enable
bypass proxy.
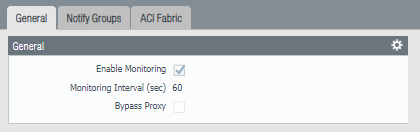
- Select PanoramaCisco ACISetupGeneral.
- Select Enable Monitoring. This enables monitoring for all clusters in your deployment.
- Set the Monitoring Interval in seconds. The monitoring interval is how often Panorama retrieves updated network information from the APIC. The default value is 60 seconds and the range is 60 seconds to 86,400 seconds (one day).
- (Optional) Select Bypass Proxy to Bypass proxy server settings, configured on Panorama under PanoramaSetupServicesProxy Server, for communication between Panorama and the APIC. This allows Panorama to communicate directly with the APIC while maintaining proxied communication for other services.
![]()
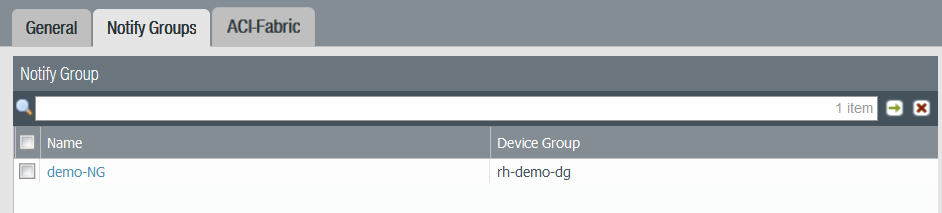
- Create a notify group.
- Select PanoramaCisco ACISetupNotify Groups.
- Click Add.
- Enter a descriptive Name for your notify group.
- Select the device groups in your ACI deployment.
![]()
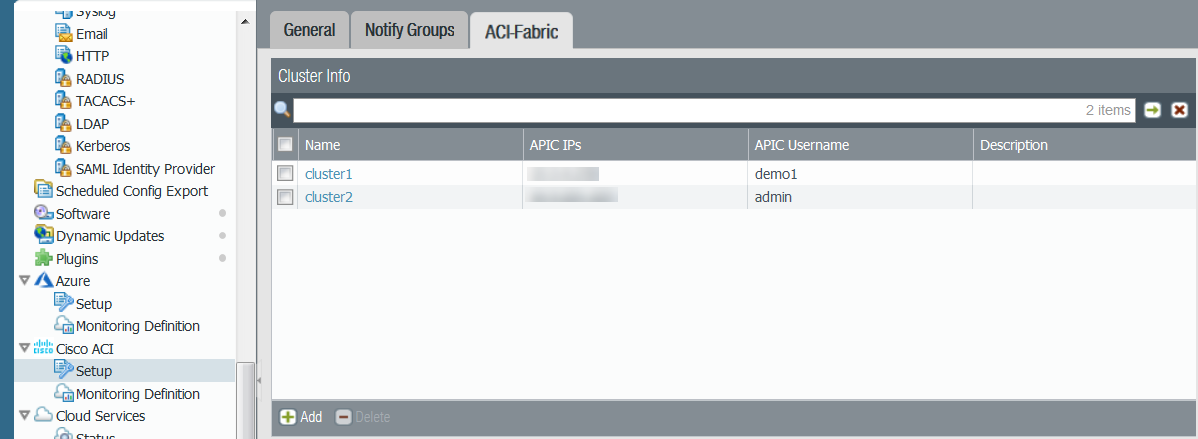
- Add ACI fabric information.
- Select PanoramaCisco ACISetupACI Fabric.
- Enter a descriptive Name for your cluster.
- Enter the IP address or FQDN for each APIC in the
cluster as a comma-separated list.When using FQDN, do not include https:// in the URL.
- Enter your APIC username.
- Enter and confirm your APIC password.
- Click OK.
![]()
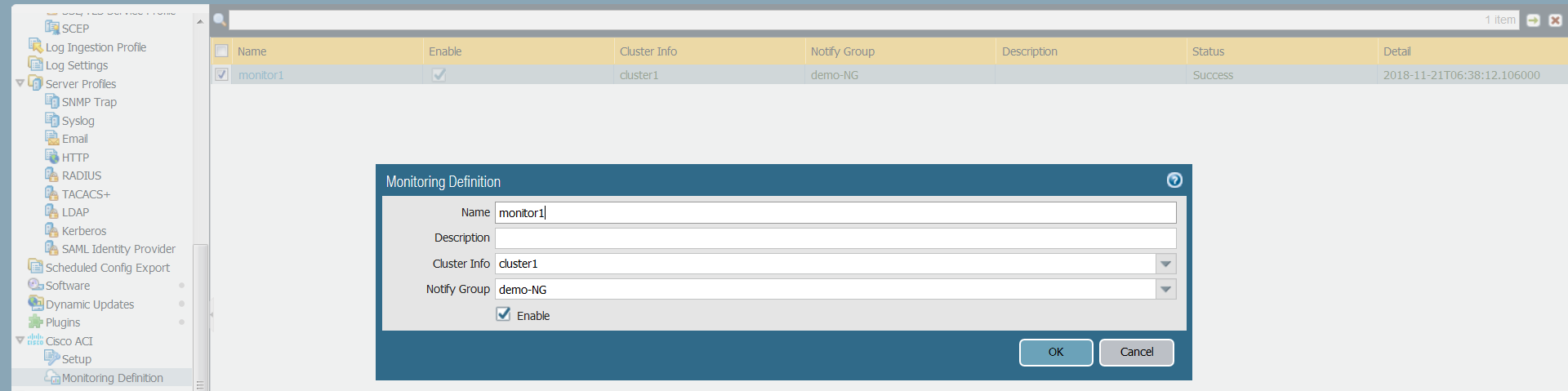
- Configure the Monitoring Definition.
- Select PanoramaCisco ACIMonitoring Definition and click Add.
- Enter a descriptive Name and optionally a description to identify the Cisco ACI cluster for which you use this definition.
- Select the Cluster Info and Notify Group.
- Click OK.
![]()
- Commit your changes.
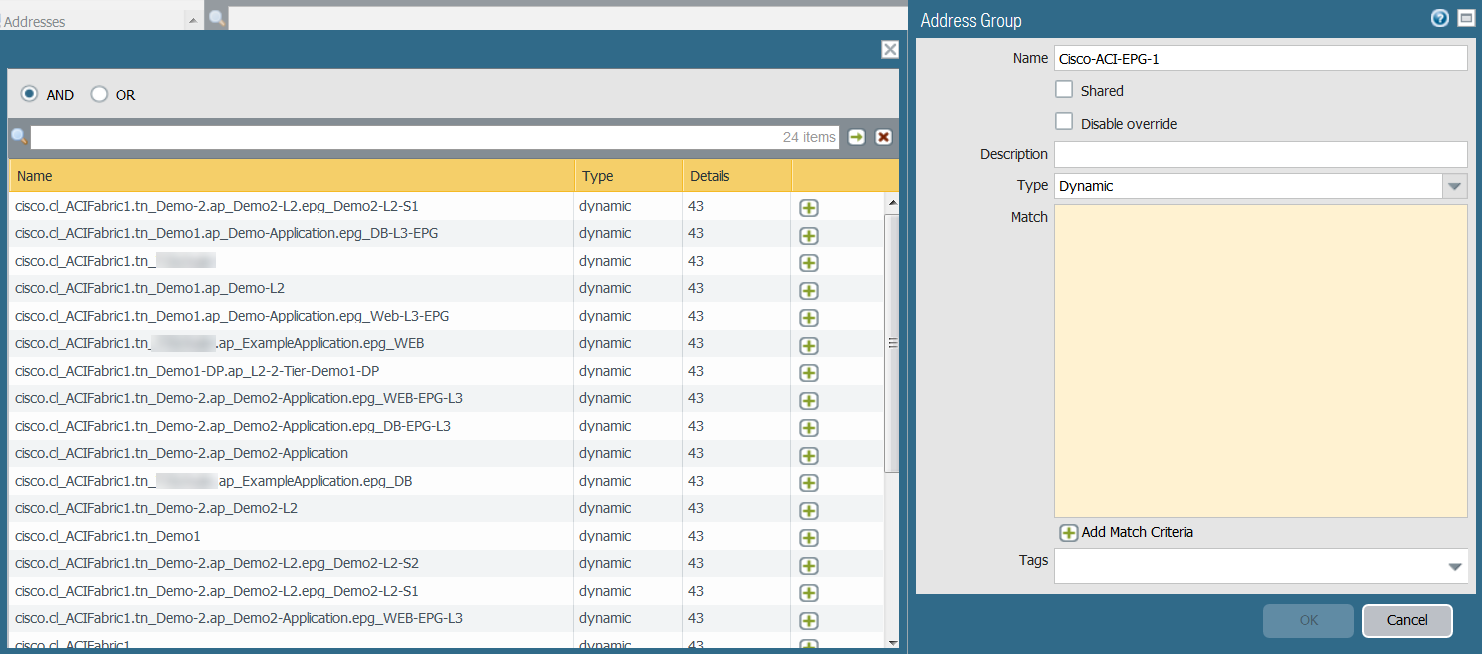
- Verify that you can view the EPG information on Panorama,
and define the match criteria for Dynamic Address Groups.Some browser extensions may block API calls between Panorama and the APIC which prevents Panorama from receiving match criteria. If Panorama displays no match criteria and you are using browser extensions, disable the extensions and Synchronize Dynamic Objects to populate the tags available to Panorama.Panorama does not immediately process new monitoring definitions and populate the match criteria available to dynamic address. You should wait for the duration of your configured monitoring interval before verifying that EPG information.
![]()
- Verify that addresses in your EPGs are added to dynamic
address groups.
- Select PanoramaObjectsAddress Groups.
- Click More in the Addresses
column of a dynamic address group. Panorama displays a list of IP addresses added to that dynamic address group based on the match criteria you specified.
- Use dynamic address groups in policy.
- Select PoliciesSecurity.
- Click Add and enter a Name and a Description for the policy.
- Add the Source Zone to specify the zone from which the traffic originates.
- Add the Destination Zone at which the traffic is terminating.
- For the Destination Address, select the Dynamic address group you just created.
- Specify the action— Allow or Deny—for the traffic, and optionally attach the default security profiles to the rule.
- Repeats Steps 1 through 6 to create another policy rule.
- Click Commit.See Use Dynamic Address Groups in Policy for more information.
- You can update the dynamic objects from the APIC at any
time by synchronizing dynamic objects. Synchronizing dynamic objects
enables you to maintain context on changes in the virtual environment
and allows you to enable applications by automatically updating
the Dynamic Address Groups used in policy rules.
- Select PanoramaCisco ACIMonitoring Definition.
- Click Synchronize Dynamic Objects.
On HA failover, the newly active Panorama attempts to reconnect to the APIC and retrieve tags for all monitoring definitions. If there is an error with reconnecting even one monitoring definition, Panorama generates a system log messageUnable to process subscriptions after HA switch-over; user-intervention required.
When you see this error, you must log in to Panorama and fix the issue, for example remove an invalid APIC IP or provide valid credentials, and commit your changes to enable Panorama to reconnect and retrieve the tags for all monitoring definitions. Even when Panorama is disconnected from the APIC, the firewalls have the list of all tags that had been retrieved before failover, and can continue to enforce policy on that list of IP addresses. If you perform a commit before resolving the failover error, the newly active Panorama will not push any IP-to-tag mapping information and clearing the mapping information from the firewalls. As a best practice, to monitor this issue, configure action-oriented log forwarding to an HTTPS destination from Panorama so that you can take immediate action.