Enterprise DLP
Create a Nested Data Profile
Table of Contents
Expand All
|
Collapse All
Enterprise DLP Docs
Create a Nested Data Profile
Create a single Enterprise Data Loss Prevention (E-DLP) data profile containing multiple data
profiles to simplify management of sensitive data leaving your network.
On May 7, 2025, Palo Alto Networks is introducing new Evidence Storage and Syslog Forwarding service IP
addresses to improve performance and expand availability for these services
globally.
You must allow these new service IP addresses on your network
to avoid disruptions for these services. Review the Enterprise DLP
Release Notes for more
information.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
Or any of the following licenses that include the Enterprise DLP license
|
Enterprise Data Loss Prevention (E-DLP) supports creating a single data profile that contains
multiple nested data profiles. Creating a
single data profile that contains multiple nested data profiles enables you to
consolidate the match criteria to prevent exfiltration of sensitive data to a single
data profile that you can associate with a single Security policy rule. This enables
your data security administrators to simplify the management of sensitive data
leaving your network and reduces the need to manage multiple Security policy rules
and data profiles. Enterprise DLP synchronizes nested data profiles across Panorama, Strata Cloud Manager, and Prisma Browser.
When you create a data profile that contains predefined data profiles and patterns,
be sure to consider the detection types used by the predefined
data patterns because the detection type determines how Enterprise DLP arrives
at a verdict for scanned files.
- Enterprise DLP does not support adding a nested data profile to another nested data profile.
- Enterprise DLP supports adding a data profiles that have only a Primary Rule configured. Enterprise DLP does not support adding data profiles that include both Primary and Secondary Rules to a nested data profile.
- Enterprise DLP supports adding a data profile that includes an advanced detection method to an existing nested data profile if you did not include one when you originally created the data profile.
- (SaaS Security) Enterprise DLP supports adding a nested data profile to SaaS Security Inline policy recommendations and Internet Access policy rules only.Enterprise DLP does not support adding a nested data profile to data asset policy rules in Data Security.
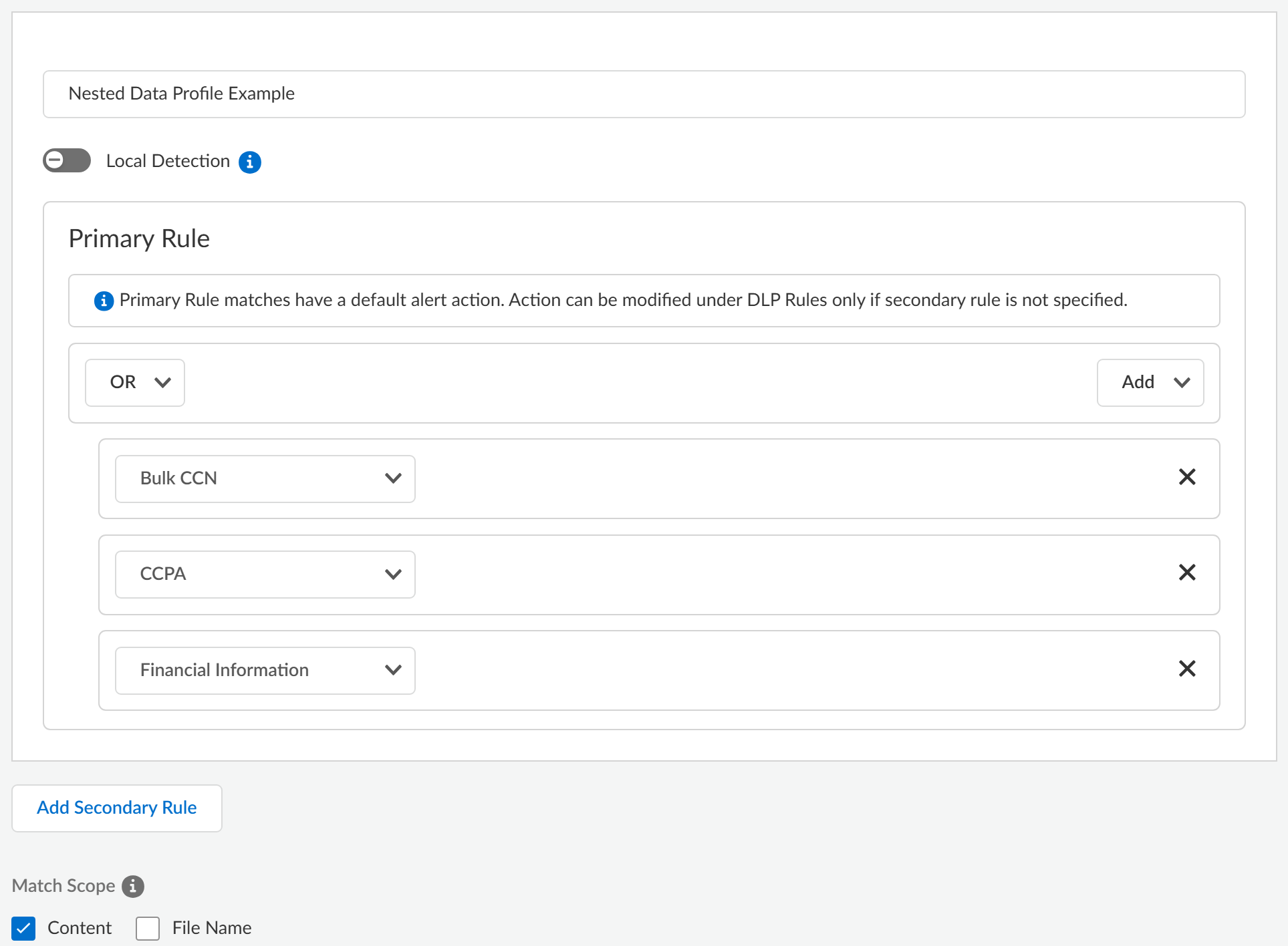
- Log in to Strata Cloud Manager.Select ConfigurationData Loss PreventionData Profiles and Add Data ProfilesCustom Data Profile.You can copy an existing data profile to modify its match criteria while preserving the original. Enterprise DLP names the copied data profile Copy - <name_of_original_data_profile>. You can edit the name as needed.(Prisma Browser) If you copied a Cloud Only data profile, click Convert to Local Supported Profile in the Preview panel to remove all match criteria not supported by local Prisma Browser detection. This converts the data profile into a data profile with Cloud & Local detection coverage.Enter the Data Profile Name.(Prisma Browser) Toggle Local Detection to filter and display only the data profiles supported for local Prisma Browser detection.Required for Prisma Browser users without an active Enterprise DLP license.Configure the Primary Rule for the data profile.Select AddAdd Data Profile to add predefined or custom data profiles. Repeat this step to include additional data profiles.Add the data profile match criteria for allowed traffic to the Primary Rule. Add data profiles for blocked traffic to either Primary Rule or Secondary Rule. Nested data profiles support AND or OR operators.(Optional) Configure a Secondary Rule.Add Data Profile to add predefined or custom data profiles. Repeat this step to include additional data profiles.Enterprise DLP automatically blocks traffic containing sensitive data that matches a Secondary Rule. Add match criteria to the Primary Rule to generate an Alert for allowed traffic.Prisma Browser doesn't support Secondary Rules for data profiles and ignores them.Nested data profiles support only the OR operator.Click Test Run to test and verify the data profile accurately detects the sensitive data you configured it to detect.Review the nested data profile configuration.
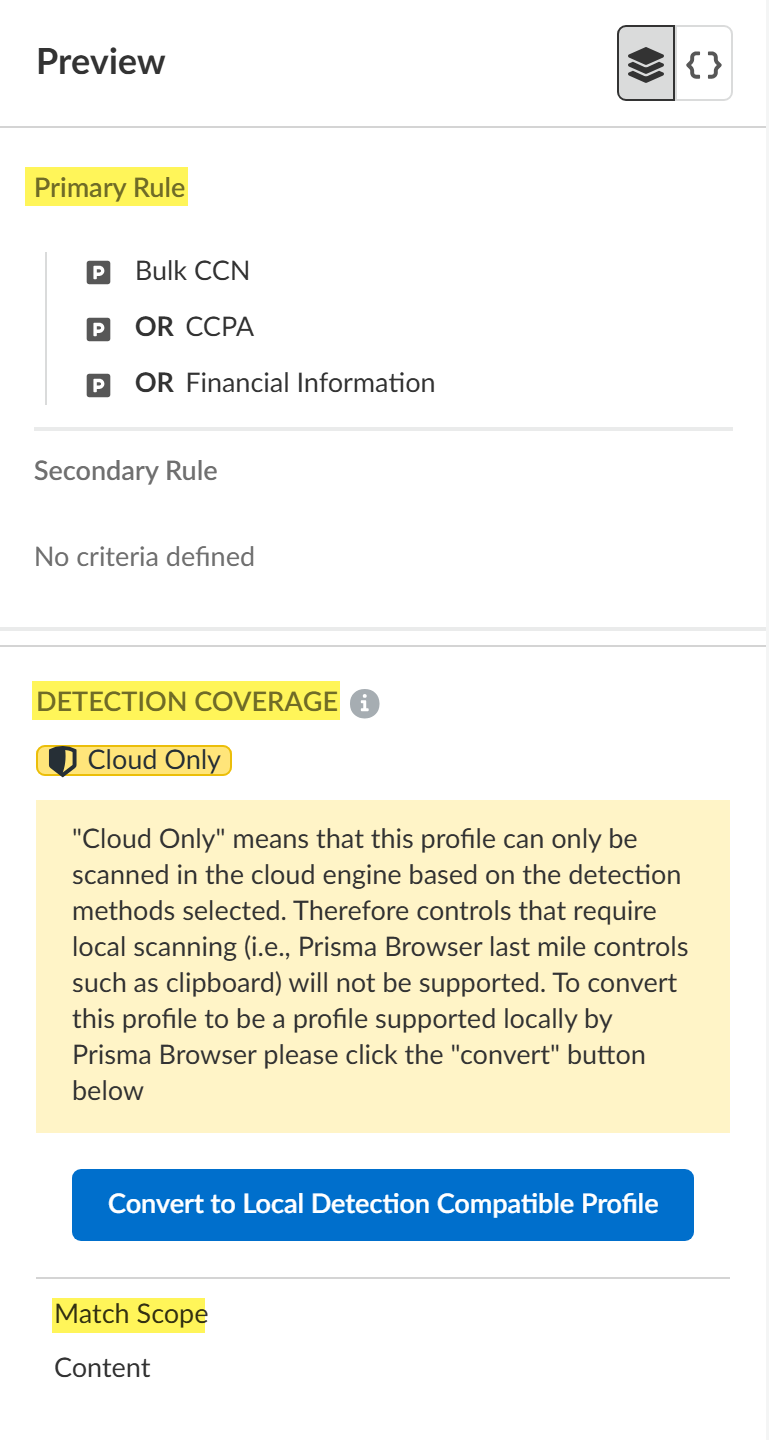
![]() Use the Preview to view of your Primary and Secondary Rule configuration, the Detection Coverage (Cloud & Local or Cloud Only), and the Match Scope.
Use the Preview to view of your Primary and Secondary Rule configuration, the Detection Coverage (Cloud & Local or Cloud Only), and the Match Scope.- Example of No Local Detection SupportA data profile with Cloud Only detection coverage includes cloud-assisted detection method which makes the data profile not compatible local Prisma Browser detection.Click Convert to Local Detection Compatible Profile to remove any cloud-assisted detection methods not compatible with local Prisma Browser detection. This converts the data profile into a data profile with Cloud & Local detection coverage.
![]()
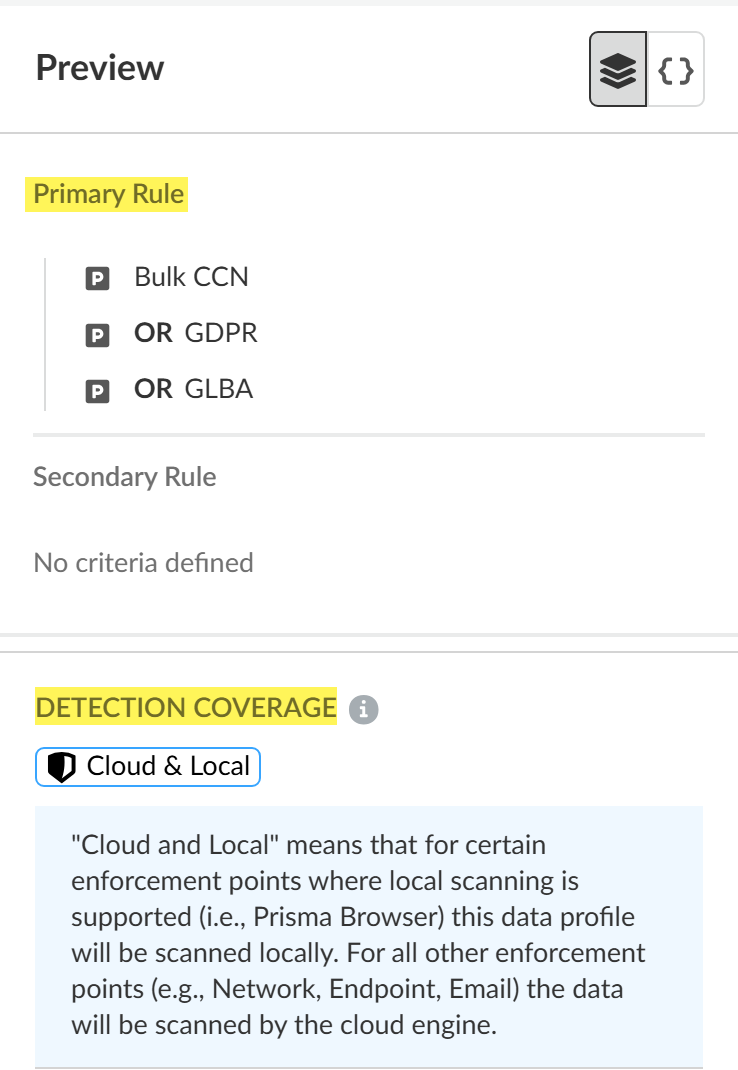
- Example of Local Detection SupportA data profile with Cloud & Local detection coverage includes only the detection methods that are compatible with local Prisma Browser detection.
![]()
![]()
Verify that the data profile you created.- Strata Cloud Manager—Log in to Strata Cloud Manager and select ConfigurationData Loss PreventionData Profiles and search for the data profile you created.
- PanoramaSee Update a Data Profile for more information on which data profile settings are editable on Panorama for a data profile created on Strata Cloud Manager.If the data profile has both Primary and Secondary Patterns, changing the data profile Action on Panorama deletes all Secondary Pattern match criteria.
- Select the data profile created on Strata Cloud Manager.
- Set the data profile Action to Block traffic that matches the data profile match criteria.
- Select CommitCommit to Panorama and Commit.
- Click OK.
- Select CommitPush to Devices and Edit Selections.
- Select Device Groups and Include Device and Network Templates.
- Push your configuration changes to your managed firewalls that are using Enterprise DLP.
Save the data profile.Modify the DLP rule or add the data profile to a Data Control Rule.- NGFW and Prisma Access Tenants—Modify a DLP rule to define the type of traffic to inspect, the impacted file types and apps, the action Enterprise DLP takes when sensitive data is detected, log severity, and more for the data profile match criteria. Enterprise DLP automatically creates a DLP rule with an identical name as the data profile from which it was created.
- Prisma Browser—Create or edit a Data Control rule to prevent exfiltration of sensitive data for specific apps, website classifications, or URLs.