Control Role-Based Access for Tenant-Level Administrative Users
Table of Contents
Expand All
|
Collapse All
Prisma Access Docs
-
5.2 Preferred and Innovation
- 5.2 Preferred and Innovation
- 5.1 Preferred and Innovation
- 5.0 Preferred and Innovation
- 4.2 Preferred
- 4.1 Preferred
- 4.0 Preferred
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
-
-
-
-
- Allocate Licenses for Prisma Access (Managed by Strata Cloud Manager)
- Plan Service Connections for Prisma Access (Managed by Strata Cloud Manager) and Add-ons
- Add Additional Locations for Prisma Access (Managed by Strata Cloud Manager) and Add-ons
- Enable Available Add-ons for Prisma Access (Managed by Strata Cloud Manager)
- Search for Subscription Details
- Share a License for Prisma Access (Managed by Strata Cloud Manager) and Add-ons
- Increase Subscription Allocation Quantity
-
- Activate a License for Prisma Access (Managed by Strata Cloud Manager) and Prisma SD-WAN Bundle
- Activate and Edit a License for SASE 5G Through Common Services
-
- Prisma Access Onboarding Workflow
-
2.2 Preferred
- 4.0 & Later
- 3.2 Preferred and Innovation
- 3.1 Preferred and Innovation
- 3.0 Preferred and Innovation
- 2.2 Preferred
- Prisma Access China
-
- Prisma Access
- Prisma Access Infrastructure Management
- Releases and Upgrades
- Manage Upgrade Options for the GlobalProtect App
- Notifications and Alerts for Panorama, Cloud Services Plugin, and PAN-OS Dataplane Versions
- Retrieve the IP Addresses for Prisma Access
- Plan for IP Address Changes for Mobile Users, Remote Networks, and Service Connections
- Service IP and Egress IP Address Allocation for Remote Networks
- How to Calculate Remote Network Bandwidth
- Prisma Access APIs
- Use Logging, Routing, and EDL Information to Troubleshoot Your Deployment
-
- Set Up Prisma Access
- Plan the Service Infrastructure and Service Connections
- Configure the Service Infrastructure
- Create a Service Connection to Allow Access to Your Corporate Resources
- Create a Service Connection to Enable Access between Mobile Users and Remote Networks
- Deployment Progress and Status
- How BGP Advertises Mobile User IP Address Pools for Service Connections and Remote Network Connections
- Use Traffic Steering to Forward Internet-Bound Traffic to Service Connections
- Routing Preferences for Service Connection Traffic
- Create a High-Bandwidth Network Using Multiple Service Connections
- List of Prisma Access Locations
-
- Plan To Deploy Prisma Access for Mobile Users
- Secure Mobile Users With GlobalProtect
- Secure Mobile Users with an Explicit Proxy
- Zone Mapping
- Specify IP Address Pools for Mobile Users
- How the GlobalProtect App Selects a Prisma Access Location for Mobile Users
- View Logged In User Information and Log Out Current Users
-
- Use Explicit Proxy to Secure Public Apps and GlobalProtect or a Third-Party VPN to Secure Private Apps
- Prisma Access with On-Premises Gateways
-
- Set Equal Gateway Priorities for On-Premises and Prisma Access Gateways
- Set a Higher Gateway Priority for an On-Premises Gateway
- Set Higher Priorities for Multiple On-Premises Gateways
- Configure Priorities for Prisma Access and On-Premises Gateways
- Allow Mobile Users to Manually Select Specific Prisma Access Gateways
- DNS Resolution for Mobile Users—GlobalProtect and Remote Network Deployments
- IPv6 Support for Private App Access
- Sinkhole IPv6 Traffic In Mobile Users—GlobalProtect Deployments
- Identification and Quarantine of Compromised Devices With Prisma Access
- Support for Gzip Encoding in Clientless VPN
- Report Website Access Issues
-
- Plan to Deploy Remote Networks
- Onboard and Configure Remote Networks
-
- Remote Network Locations with Overlapping Subnets
- Remote Network Locations with WAN Link
- Use Predefined IPSec Templates to Onboard Service and Remote Network Connections
- Onboard Remote Networks with Configuration Import
- Configure Quality of Service in Prisma Access
- Create a High-Bandwidth Network for a Remote Site
- Provide Secure Inbound Access to Remote Network Locations
-
- Multitenancy Overview
- Multitenancy Configuration Overview
- Enable Multitenancy and Migrate the First Tenant
- Add Tenants to Prisma Access
- Delete a Tenant
- Create a Tenant-Level Administrative User
- Control Role-Based Access for Tenant-Level Administrative Users
- Sort Logs by Device Group ID for External Logging
- Visibility and Monitoring Features in the Prisma Access App
-
- Integrate Prisma Access With Other Palo Alto Networks Apps
- Integrate Third-Party Enterprise Browser with Explicit Proxy
- Integrate Third-Party NDRs with Prisma Access
- Juniper Mist Integration for SASE Health
-
-
- Connect your Mobile Users in Mainland China to Prisma Access Overview
- Configure Prisma Access for Mobile Users in China
- Configure Real-Name Registration and Create the VPCs in Alibaba Cloud
- Attach the CEN and Specify the Bandwidth
- Create Linux Instances in the Alibaba Cloud VPCs
- Configure the Router Instances
- Onboard the GlobalProtect Gateway and Configure the Prisma Access Portal
-
-
-
- INC_MU_APP_EXPERIENCE_UNREACHABLE_ ALL_PA_LOCATIONS
- INC_MU_APP_EXPERIENCE_UNREACHABLE_ PER_PA_LOCATION
- INC_RN_APP_EXPERIENCE_UNREACHABLE_ ALL_PA_LOCATIONS
- INC_RN_APP_EXPERIENCE_UNREACHABLE_ ONE_PA_LOCATION
- INC_CIE_AGENT_DISCONNECT
- INC_CIE_DIRECTORY_DISCONNECT
- INC_GLOBALPROTECT_GW_USER_AUTH_ TIMEOUT_FAILURES_COUNT_EXCEEDED_ ABOVE_BASELINE_ALL_PA_LOCATIONS
- INC_GLOBALPROTECT_GW_USER_AUTH_ TIMEOUT_FAILURES_COUNT_EXCEEDED_ ABOVE_BASELINE_PER_PA_LOCATION
- INC_GLOBALPROTECT_PORTAL_AUTH_ TIMEOUT_FAILURES_COUNT_EXCEEDED_ ABOVE_BASELINE_ALL_PA_LOCATIONS
- INC_GLOBALPROTECT_PORTAL_AUTH_ TIMEOUT_FAILURES_COUNT_EXCEEDED_ ABOVE_BASELINE_PER_PA_LOCATION
- INC_MU_AUTH_SERVER_UNREACHABLE_ALL_ PA_LOCATIONS
- INC_MU_AUTH_SERVER_UNREACHABLE_PER_ PA_LOCATION
- INC_MU_DNS_SERVER_UNREACHABLE_ALL_ PA_LOCATIONS
- INC_MU_DNS_SERVER_UNREACHABLE_ PER_PA_LOCATION
- INC_PORTAL_CLIENTLESS_VPN_AUTH_ TIMEOUT_FAILURES_COUNT_EXCEEDED_ ABOVE_BASELINE_ALL_PA_LOCATIONS
- INC_PORTAL_CLIENTLESS_VPN_AUTH_ TIMEOUT_FAILURES_COUNT_EXCEEDED_ ABOVE_BASELINE_PER_PA_LOCATION
- INC_RN_AUTH_SERVER_UNREACHABLE_ALL_ PA_LOCATIONS
- INC_RN_AUTH_SERVER_UNREACHABLE_PER_ PA_LOCATION
- INC_RN_DNS_SERVER_UNREACHABLE_ALL_ PA_LOCATIONS
- INC_RN_DNS_SERVER_UNREACHABLE_PER_ PA_LOCATION
- INC_RN_ECMP_TUNNEL_RTT_EXCEEDED_ BASELINE
- INC_RN_PRIMARY_WAN_TUNNEL_RTT_ EXCEEDED_BASELINE
- INC_RN_SECONDARY_TUNNEL_DOWN
- INC_RN_SECONDARY_WAN_TUNNEL_RTT_ EXCEEDED_BASELINE
- INC_RN_SITE_CAPACITY_PREDICTION
- INC_SC_PRIMARY_WAN_TUNNEL_RTT_ EXCEEDED_BASELINE
- INC_SC_SECONDARY_WAN_TUNNEL_RTT_ EXCEEDED_BASELINE
- INC_SC_SITE_CAPACITY_PREDICTION
-
- INC_CERTIFICATE_EXPIRY
- INC_GP_CLIENT_VERSION_UNSUPPORTED
- INC_MU_IP_POOL_BLOCK_UTILIZATION_ EXCEEDED_CAPACITY
- INC_MU_IP_POOL_BLOCK_UTILIZATION_ EXCEEDED_THRESHOLD
- INC_PA_INFRA_DEGRADATION
- INC_PA_SERVICE_DEGRADATION_PA_LOCATION
- INC_PA_SERVICE_DEGRADATION_RN_ SITE_CONNECTIVITY
- INC_PA_SERVICE_DEGRADATION_SC_ CONNECTIVITY
- INC_RN_ECMP_BGP_DOWN
- INC_RN_ECMP_BGP_FLAP
- INC_RN_ECMP_PROXY_TUNNEL_DOWN
- INC_RN_ECMP_PROXY_TUNNEL_FLAP
- INC_RN_ECMP_TUNNEL_DOWN
- INC_RN_ECMP_TUNNEL_FLAP
- INC_RN_PRIMARY_WAN_BGP_FLAP
- INC_RN_PRIMARY_WAN_PROXY_TUNNEL_DOWN
- INC_RN_PRIMARY_WAN_PROXY_TUNNEL_FLAP
- INC_RN_PRIMARY_WAN_TUNNEL_DOWN
- INC_RN_PRIMARY_WAN_TUNNEL_FLAP
- INC_RN_SECONDARY_WAN_BGP_DOWN
- INC_RN_SECONDARY_WAN_BGP_FLAP
- INC_RN_SECONDARY_WAN_PROXY_TUNNEL_DOWN
- INC_RN_SECONDARY_WAN_PROXY_TUNNEL_FLAP
- INC_RN_SECONDARY_WAN_TUNNEL_DOWN
- INC_RN_SECONDARY_WAN_TUNNEL_FLAP
- INC_RN_SITE_DOWN
- INC_RN_SITE_LONG_DURATION_CAPACITY_ EXCEEDED_THRESHOLD
- INC_RN_SITE_LONG_DURATION_EXCEEDED_ CAPACITY
- INC_RN_SPN_LONG_DURATION_CAPACITY_EXCEEDED _THRESHOLD
- INC_RN_SPN_LONG_DURATION_EXCEEDED_ CAPACITY
- INC_SC_PRIMARY_WAN_BGP_DOWN
- INC_SC_PRIMARY_WAN_BGP_FLAP
- INC_SC_PRIMARY_WAN_PROXY_TUNNEL_DOWN
- INC_SC_PRIMARY_WAN_PROXY_TUNNEL_FLAP
- INC_SC_PRIMARY_WAN_TUNNEL_DOWN
- INC_SC_PRIMARY_WAN_TUNNEL_FLAP
- INC_SC_SECONDARY_WAN_BGP_DOWN
- INC_SC_SECONDARY_WAN_BGP_FLAP
- INC_SC_SECONDARY_WAN_PROXY_TUNNEL_DOWN
- INC_SC_SECONDARY_WAN_PROXY_TUNNEL_FLAP
- INC_SC_SECONDARY_WAN_TUNNEL_DOWN
- INC_SC_SECONDARY_WAN_TUNNEL_FLAP
- INC_SC_SITE_DOWN
- INC_SC_SITE_LONG_DURATION_CAPACITY_ EXCEEDED_THRESHOLD
- INC_SC_SITE_LONG_DURATION_EXCEEDED_ CAPACITY
- INC_ZTNA_CONNECTOR_APP_STATUS_DOWN
- INC_ZTNA_CONNECTOR_APP_STATUS_DOWN_PARTIAL
- INC_ZTNA_CONNECTOR_CPU_HIGH
- INC_ZTNA_CONNECTOR_MEMORY_HIGH
- INC_ZTNA_CONNECTOR_TUNNEL_DOWN
-
- AL_CIE_AGENT_DISCONNECT
- AL_CIE_DIRECTORY_DISCONNECT
- AL_MU_IP_POOL_CAPACITY
- AL_MU_IP_POOL_USAGE
- AL_RN_ECMP_BGP_DOWN
- AL_RN_ECMP_BGP_FLAP
- AL_RN_PRIMARY_WAN_BGP_DOWN
- AL_RN_PRIMARY_WAN_BGP_FLAP
- AL_RN_PRIMARY_WAN_TUNNEL_DOWN
- AL_RN_PRIMARY_WAN_TUNNEL_FLAP
- AL_RN_SECONDARY_WAN_BGP_DOWN
- AL_RN_SECONDARY_WAN_BGP_FLAP
- AL_RN_SECONDARY_WAN_TUNNEL_DOWN
- AL_RN_SECONDARY_WAN_TUNNEL_FLAP
- AL_RN_SITE_DOWN
- AL_RN_SITE_LONG_DURATION_CAPACITY_ EXCEEDED_THRESHOLD
- AL_RN_SITE_LONG_DURATION_EXCEEDED_ CAPACITY
- AL_RN_SPN_LONG_DURATION_CAPACITY_ EXCEEDED_THRESHOLD
- AL_SC_PRIMARY_WAN_BGP_DOWN
- AL_SC_PRIMARY_WAN_BGP_FLAP
- AL_SC_PRIMARY_WAN_TUNNEL_DOWN
- AL_SC_PRIMARY_WAN_TUNNEL_FLAP
- AL_SC_SECONDARY_WAN_BGP_DOWN
- AL_SC_SECONDARY_WAN_BGP_FLAP
- AL_SC_SECONDARY_WAN_TUNNEL_DOWN
- AL_SC_SECONDARY_WAN_TUNNEL_FLAP
- AL_SC_SITE_DOWN
- AL_SC_SITE_LONG_DURATION_CAPACITY_ EXCEEDED_THRESHOLD
- AL_SC_SITE_LONG_DURATION_EXCEEDED_CAPACITY
- AL_ZTNA_CONNECTOR_APP_STATUS_DOWN
- AL_ZTNA_CONNECTOR_APP_STATUS_DOWN_PARTIAL
- AL_ZTNA_CONNECTOR_CPU_HIGH
- AL_ZTNA_CONNECTOR_MEMORY_HIGH
- AL_ZTNA_CONNECTOR_TUNNEL_DOWN
- New Features in Incidents and Alerts
- Known Issues
Control Role-Based Access for Tenant-Level Administrative Users
If you manage a multitenant deployment, you
can use role-based access control (RBAC) to create tenant-level
administrative users.
To modify RBAC-level access for
tenant-level administrative users in Panorama, you create a tenant-level
administrative user, use an Admin Role Profile with
a Role of Device Group and Template,
and Enable, Disable,
or give Read Only access to areas of the
Panorama Web UI. Use this method to manage
access to all Panorama components for tenant-level users, with the
exception of access to the Cloud Services plugin where you manage
Prisma Access.
If you want to restrict a tenant-level user
from configuring the Prisma Access components in Panorama, you cannot
use Admin Roles. To disallow users from configuring Prisma Access-specific
configuration tasks, you must
prevent the user from
accessing the Cloud Services plugin
, which also prevents
them from viewing it. Using this method, you can create an administrative
user for a security professional who has permissions to make changes
to security policies and push those changes to Panorama, but cannot
view or make any changes to Prisma Access configuration.You
can either enable or disable access to the Cloud Services plugin
for a user, but you cannot give a user read-only access; if a user
has access to view the Cloud Services plugin, the user can also
make configuration changes to its components, including Prisma Access.
The
following table shows sample tenant-level administrative roles and
the steps you perform to create those roles.
| Sample Tenant-Level Configuration | Configuration Task |
|---|---|
Create a networking-focused user who:
| Create a tenant-level
administrative user, enabling Save and Commit permissions
in the Admin Role Profile, and disabling
or making Read Only any permissions that
you don’t want the tenant-level administrative user to have. |
Create a security-focused user who:
| To prevent a tenant-level administrative user
from viewing or accessing the plugin, remove plugin access
for a tenant-level administrator . For all other Panorama-related
permissions, change the Admin Role permissions for the user. |
Create a hybrid user who:
| This configuration is not possible. You
cannot make the Cloud Services plugin read-only. You can only provide
access to admin users to view it and use it to make configuration
changes, or disallow them from viewing it. |
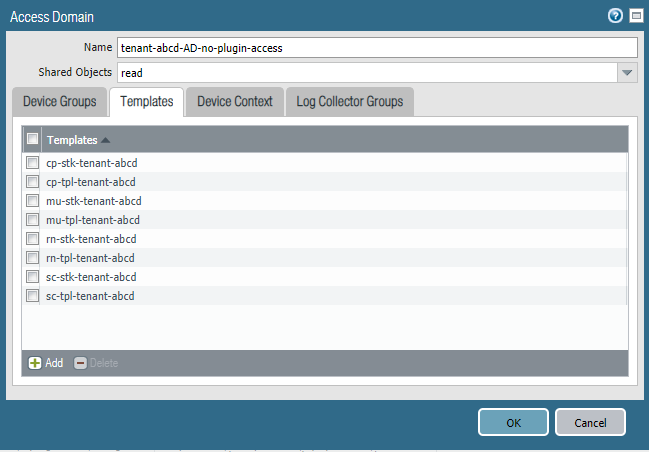
Remove Plugin Access for a Tenant-Level Administrative User
In normal multitenant configurations, you
use access domains Add Tenants to Prisma Access and associate
each access domain with a tenant. To prevent a tenant-level administrative
user from viewing or making configuration changes to Prisma Access,
you create an access domain, but you do not associate it with a
tenant.
Because you associated the access domain to the device
groups and template stacks for the tenant, the tenant-level administrative
user has RBAC access at the tenant level and is able to perform
configuration for that tenant only. Because you did not associate
the access domain with a tenant in Prisma Access, the access domain
is unable to view the Cloud Services plugin, which provides access
to Prisma Access. In this way, you create a user who can perform
tenant-level configuration tasks without being able to access, view,
or make configuration changes to Prisma Access.
To remove
Prisma Access access for an administrative-level user, complete
the following task.
This task assumes that you have Add Tenants to Prisma Access templates,
template stacks, and device groups for the tenant; you’ll be associating
them to the tenant-level administrative user.
- Create an administrative role with a type of Device Group and Template.
- Select PanoramaAdmin Roles.
- Add an Admin Role Profile with a Role of Device Group and Template.
- Click OK.You can create a single Admin Role Profile and share it across multiple tenants.

- Specify the Device Groups and Templates associated with the tenant.If you created any device groups that are children or grandchildren of other device groups under the Shared parent device group, select only the device group at the lowest hierarchical level (child or grandchild); do not select the parent or you will have errors on commit.


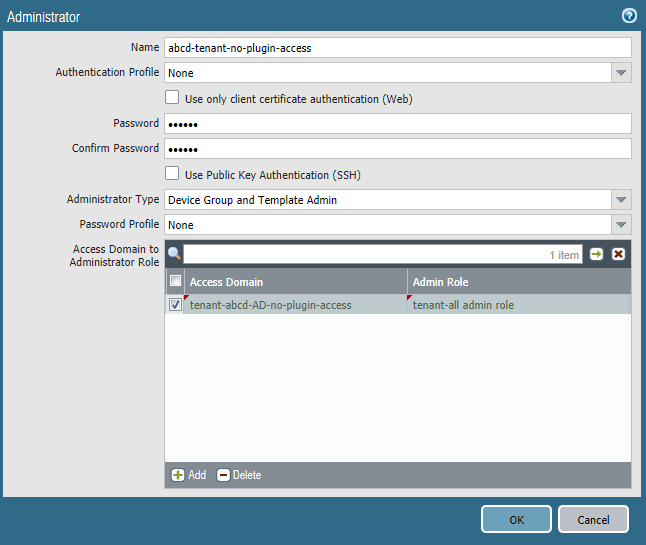
- Create and configure an Administrator for the tenant-level administrative user, specifying the Access Domain you just created.
- Select PanoramaAdministrators.
- Add an Administrator.
- Enter and confirm a Password for the new Administrator.
- Specify an Administrator Type of Device Group and Template Admin.
- Specify the Access Domain that is associated with the device groups for that tenant.
- Specify the Admin Role that you created in Step1for the tenant.When you complete this example, the abcd-tenant-no-plugin-access Administrative user will have permissions based on what you defined in the Admin Role profile, but will not be able to view or configure the Cloud Services plugin (including Prisma Access). Note, however, that they will not be able to push any changes that they make to the cloud.

- Select CommitCommit to Panorama and Commit your changes.