Use Migration Coordinator to Move Your VM-Series from NSX-V to NSX-T
Table of Contents
10.0 (EoL)
Expand all | Collapse all
-
- VM-Series Deployments
- VM-Series in High Availability
- Enable Jumbo Frames on the VM-Series Firewall
- Hypervisor Assigned MAC Addresses
- Custom PAN-OS Metrics Published for Monitoring
- Interface Used for Accessing External Services on the VM-Series Firewall
- PacketMMAP and DPDK Driver Support
- Enable ZRAM on the VM-Series Firewall
-
- VM-Series Firewall Licensing
- Create a Support Account
- Serial Number and CPU ID Format for the VM-Series Firewall
- Install a License API Key
- Use Panorama-Based Software Firewall License Management
-
- Maximum Limits Based on Memory
- Activate Credits
- Create a Deployment Profile
- Manage a Deployment Profile
- Register the VM-Series Firewall (Software NGFW Credits)
- Provision Panorama
- Migrate Panorama to a FW-Flex License
- Transfer Credits
- Renew Your Software NGFW Credit License
- Deactivate License (Software NGFW Credits)
- Create and Apply a Subscription-Only Auth Code
- Migrate to a Flexible VM-Series License
- What Happens When Licenses Expire?
-
- Supported Deployments on VMware vSphere Hypervisor (ESXi)
-
- Plan the Interfaces for the VM-Series for ESXi
- Provision the VM-Series Firewall on an ESXi Server
- Perform Initial Configuration on the VM-Series on ESXi
- Add Additional Disk Space to the VM-Series Firewall
- Use VMware Tools on the VM-Series Firewall on ESXi and vCloud Air
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Use the VM-Series CLI to Swap the Management Interface on ESXi
-
-
- VM-Series Firewall for NSX-V Deployment Checklist
- Install the VMware NSX Plugin
- Apply Security Policies to the VM-Series Firewall
- Steer Traffic from Guests that are not Running VMware Tools
- Dynamically Quarantine Infected Guests
- Migrate Operations-Centric Configuration to Security-Centric Configuration
- Add a New Host to Your NSX-V Deployment
- Use Case: Shared Compute Infrastructure and Shared Security Policies
- Use Case: Shared Security Policies on Dedicated Compute Infrastructure
- Dynamic Address Groups—Information Relay from NSX-V Manager to Panorama
-
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (North-South)
- Components of the VM-Series Firewall on NSX-T (North-South)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Deploy the VM-Series Firewall
- Direct Traffic to the VM-Series Firewall
- Apply Security Policy to the VM-Series Firewall on NSX-T
- Use vMotion to Move the VM-Series Firewall Between Hosts
- Extend Security Policy from NSX-V to NSX-T
-
- Components of the VM-Series Firewall on NSX-T (East-West)
- VM-Series Firewall on NSX-T (East-West) Integration
- Supported Deployments of the VM-Series Firewall on VMware NSX-T (East-West)
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Add a Service Chain
- Direct Traffic to the VM-Series Firewall
- Apply Security Policies to the VM-Series Firewall on NSX-T (East-West)
- Use vMotion to Move the VM-Series Firewall Between Hosts
-
- Install the Panorama Plugin for VMware NSX
- Enable Communication Between NSX-T Manager and Panorama
- Create Template Stacks and Device Groups on Panorama
- Configure the Service Definition on Panorama
- Launch the VM-Series Firewall on NSX-T (East-West)
- Create Dynamic Address Groups
- Create Dynamic Address Group Membership Criteria
- Generate Steering Policy
- Generate Steering Rules
- Delete a Service Definition from Panorama
- Migrate from VM-Series on NSX-T Operation to Security Centric Deployment
- Extend Security Policy from NSX-V to NSX-T
- Use In-Place Migration to Move Your VM-Series from NSX-V to NSX-T
- Use Migration Coordinator to Move Your VM-Series from NSX-V to NSX-T
-
-
- Deployments Supported on AWS
-
- Planning Worksheet for the VM-Series in the AWS VPC
- Launch the VM-Series Firewall on AWS
- Launch the VM-Series Firewall on AWS Outpost
- Create a Custom Amazon Machine Image (AMI)
- Encrypt EBS Volume for the VM-Series Firewall on AWS
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable CloudWatch Monitoring on the VM-Series Firewall
-
- Use Case: Secure the EC2 Instances in the AWS Cloud
- Use Case: Use Dynamic Address Groups to Secure New EC2 Instances within the VPC
-
-
- What Components Does the VM-Series Auto Scaling Template for AWS (v2.0) Leverage?
- How Does the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1) Enable Dynamic Scaling?
- Plan the VM-Series Auto Scaling Template for AWS (v2.0 and v2.1)
- Customize the Firewall Template Before Launch (v2.0 and v2.1)
- Launch the VM-Series Auto Scaling Template for AWS (v2.0)
- SQS Messaging Between the Application Template and Firewall Template
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.0)
- Modify Administrative Account and Update Stack (v2.0)
-
- Launch the Firewall Template (v2.1)
- Launch the Application Template (v2.1)
- Create a Custom Amazon Machine Image (v2.1)
- VM-Series Auto Scaling Template Cleanup (v2.1)
- SQS Messaging Between the Application Template and Firewall Template (v2.1)
- Stack Update with VM-Series Auto Scaling Template for AWS (v2.1)
- Modify Administrative Account (v2.1)
- Change Scaling Parameters and CloudWatch Metrics (v2.1)
-
-
- Enable the Use of a SCSI Controller
- Verify PCI-ID for Ordering of Network Interfaces on the VM-Series Firewall
-
- Deployments Supported on Azure
- Deploy the VM-Series Firewall from the Azure Marketplace (Solution Template)
- Deploy the VM-Series Firewall from the Azure China Marketplace (Solution Template)
- Create a Custom VM-Series Image for Azure
- Deploy the VM-Series Firewall on Azure Stack
- Enable Azure Application Insights on the VM-Series Firewall
- Set up Active/Passive HA on Azure
- Use the ARM Template to Deploy the VM-Series Firewall
-
- About the VM-Series Firewall on Google Cloud Platform
- Supported Deployments on Google Cloud Platform
- Prepare to Set Up VM-Series Firewalls on Google Public Cloud
- Create a Custom VM-Series Firewall Image for Google Cloud Platform
-
- Deploy the VM-Series Firewall from Google Cloud Platform Marketplace
- Management Interface Swap for Google Cloud Platform Load Balancing
- Use the VM-Series Firewall CLI to Swap the Management Interface
- Enable Google Stackdriver Monitoring on the VM Series Firewall
- Enable VM Monitoring to Track VM Changes on Google Cloud Platform (GCP)
- Use Dynamic Address Groups to Secure Instances Within the VPC
- Use Custom Templates or the gcloud CLI to Deploy the VM-Series Firewall
-
- Prepare Your ACI Environment for Integration
-
-
- Create a Virtual Router and Security Zone
- Configure the Network Interfaces
- Configure a Static Default Route
- Create Address Objects for the EPGs
- Create Security Policy Rules
- Create a VLAN Pool and Domain
- Configure an Interface Policy for LLDP and LACP for East-West Traffic
- Establish the Connection Between the Firewall and ACI Fabric
- Create a VRF and Bridge Domain
- Create an L4-L7 Device
- Create a Policy-Based Redirect
- Create and Apply a Service Graph Template
-
- Create a VLAN Pool and External Routed Domain
- Configure an Interface Policy for LLDP and LACP for North-South Traffic
- Create an External Routed Network
- Configure Subnets to Advertise to the External Firewall
- Create an Outbound Contract
- Create an Inbound Web Contract
- Apply Outbound and Inbound Contracts to the EPGs
- Create a Virtual Router and Security Zone for North-South Traffic
- Configure the Network Interfaces
- Configure Route Redistribution and OSPF
- Configure NAT for External Connections
-
-
- Choose a Bootstrap Method
- VM-Series Firewall Bootstrap Workflow
- Bootstrap Package
- Bootstrap Configuration Files
- Generate the VM Auth Key on Panorama
- Create the bootstrap.xml File
- Prepare the Licenses for Bootstrapping
- Prepare the Bootstrap Package
- Bootstrap the VM-Series Firewall on AWS
- Bootstrap the VM-Series Firewall on Azure
- Bootstrap the VM-Series Firewall on Google Cloud Platform
- Verify Bootstrap Completion
- Bootstrap Errors
End-of-Life (EoL)
Use Migration Coordinator to Move Your VM-Series from NSX-V to NSX-T
Learn how to perform a maintenance-mode migration to
move your VM-Series firewall deployment from NSX-V to NSX-T.
Complete the following procedure to migrate
your VM-Series firewall configuration from NSX-V to NSX-T using
the VMware Migration Coordinator tool in
NSX-T. This tool is designed run in-place on the same hardware that
is running NSX-V. By migrating your configuration, you can reuse
policy and dynamic address groups already configured on Panorama.
This procedure refers to information and processes published in VMware documentation as
well as steps specific to PAN.
This procedure supports operations-centric
NSX-V deployments only. An operations-centric deployment
means that your policy rules for redirecting traffic to the VM-Series
firewall were created in NSX-V Manager, not Panorama.
This
procedure requires NSX-T Manager 3.1.0 or later.
It is recommended that plan for security
downtime while performing this migration.
- Before you begin, complete the following preparatory
tasks.
- Enable DRS on the cluster to be migrated.
- VMs should be deployed on shared storage and not a local datastore.
- Prepare NSX-T Manager for migration.
- Log in to the NSX-T Manager CLI via SSH.
- Execute the following command to enable NSX Migration
Coordinator. start service migration-coordinatorThis will now appear in the NSX-T Manager user interface under SystemMigrate.
- SSH in to the NSX-T Manager CLI as root or as admin.
- Execute the following command.st e
- Navigate ovf_validation.properties under /config.vmware/auth/
and make the following change.THIRD_PARTY_OVFS_VALIDATION_FLAG=2
- Execute the following command.service cm-inventory restart
- Install the Panorama Plugin for VMware NSX 3.2.0 or later. See the Panorama Plugin for VMware NSX 3.2.0 Release Notes before upgrading.
- Enable Communication Between NSX-T Manager and Panorama.
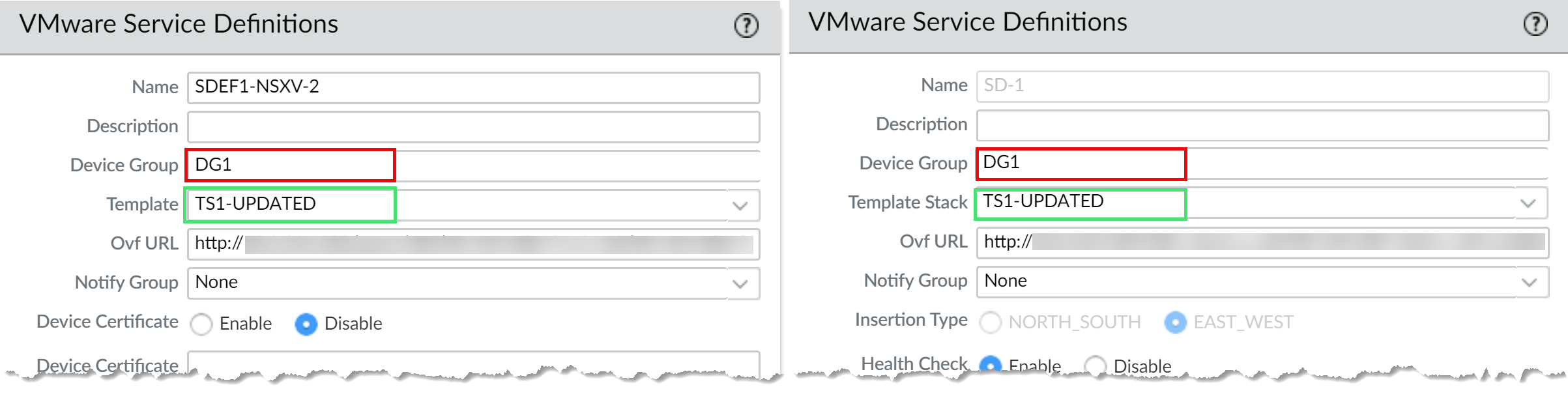
- Configure an NSX-T
service definition for each NSX-V service definition in your
deployment. Do not create new device groups; instead use
your existing NSX-V device groups. Using the existing device groups
allows you to apply the same security policy rules used on NSX-V
to the VM-Series firewalls deployed on NSX-T. If you have policy
that reference a particular zone, add the same template stack from
your NSX-V service definition to your NSX-T service definition.
Additionally, if your device group references a particular template,
ensure that you select the template stack that includes the template
referenced in the device group.
![]()
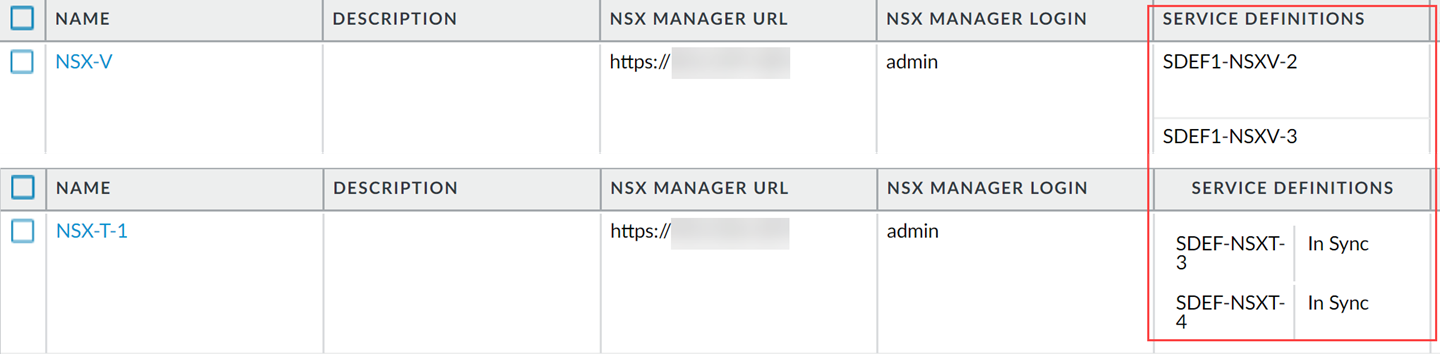
- Configure an NSX-T service manager and associate the
NSX-T service definitions to the service manager.
![]()
- Verify that your NSX-T configuration is present on NSX-T
Manager.
- Log in to NSX-T Manager.
- Select SystemService DeploymentsCatalog.
- Confirm that your NSX-T service definition is listed.
- Select SecurityNetwork Introspection SettingsService Profiles.
- Confirm that your zones associated with your NSX-T template are listed.
Steps 8 through 11 detail the migration workflow to be executed on the migration coordinator tool on NSX-T Manager. For more information, refer to VMware migration documentation for more information. - Import the NSX-V configuration to NSX-T.
- Uninstall the service instance from NSX-V.This step will result in traffic disruption.
- Log in to your vSphere client.
- Select Installation and UpgradeService Deployment.
- Select your service deployment.
- Click Delete.
- Click Delete to confirm.
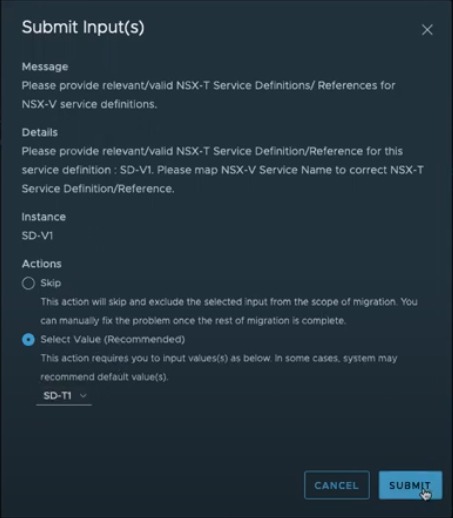
- Resolve Configuration issues
on NSX-T Manager. While resolving configuration issues, you must
take specific actions to migrate your VM-Series firewall configuration.
In most cases, you can accept the recommendations presented by NSX-T
Manager.
- When resolving service insertion configuration,
verify that you selected the correct service definition that you
previously configured on Panorama for the VM-Series on NSX-T.
![]()
- Continue resolving the remaining configuration.
- Before moving to Migrate Configuration, you will be asked to provide a transport zone for the service insertion.
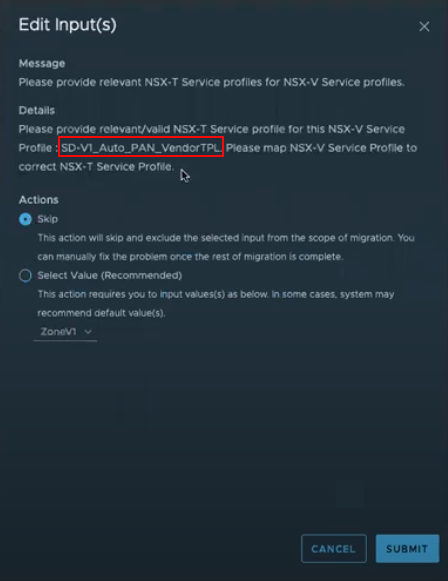
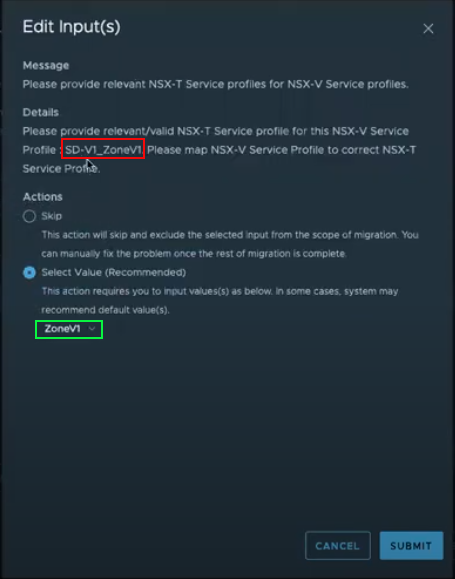
- Map the service profiles on NSX-V to the corresponding
service profiles on NSX-T.
- Auto_PAN_VendorTPL can be skipped.
![]()
- Map the NSX-T service profile to the corresponding NSX-V service profile.
![]()
- When resolving service insertion configuration,
verify that you selected the correct service definition that you
previously configured on Panorama for the VM-Series on NSX-T.
- Migrate the configuration.
- Verify that your configuration has been migrated successfully.
- Select InventoryGroups to verify that your IP sets and security groups are present. You can click on the security group name to see that the correct IP address are a part of the security group.
- Select SecurityNetwork Introspection SettingsService Segment to confirm that a service segment has been created.
- Select SecurityNetwork Introspection SettingsService Chains to confirm that a service chain has been created. Click the Profiles link in the Forward Path and Reverse Path columns to view your service profile.
- Select SecurityNetwork Introspection (E-W) to confirm that a traffic redirection rule has been created to direct traffic to the service profile of the VM-Series firewall.
- If applicable, modify and migrate edges.
- Configure and migrate your hosts.
- Add the NSX-T tags to you existing dynamic address groups.
- Select PanoramaObjectsAddress Groups.
- Click on the name of an existing NSX-V dynamic address group.
- Click Add Match Criteria to display the tags from NSX-V and NSX-T.
- Add the NSX-T tag to the dynamic address groups. If you choose not to remove the NSX-V tags, be sure to use the OR operator between the tags.
- When you have added all the necessary tags, click OK.
- Commit your changes.
- Launch the VM-Series Firewall on NSX-T (East-West). You do not need to create a new service segment; instead select the service segment created during migration.