Download PDF
GlobalProtect
Configure the GlobalProtect Portals and Gateways for IoT Devices
Table of Contents
Configure the GlobalProtect Portals and Gateways for IoT Devices
- Review the GlobalProtect for IoT Requirements.Configure your GlobalProtect gateways to support the GlobalProtect app for IoT.
- Complete the prerequisite tasks for setting up a GlobalProtect gateway.
- Create the interfaces (and zones) for the firewall on which you plan to configure each gateway. For gateways that require tunnel connections, you must configure both the physical interface and the virtual tunnel interface. See Create Interfaces and Zones for GlobalProtect.
- Set up the gateway server certificates and SSL/TLS service profile required for the GlobalProtect app to establish an SSL connection with the gateway. See Enable SSL Between GlobalProtect Components.
- Define the authentication profiles and/or certificate profiles that will be used to authenticate GlobalProtect users. See GlobalProtect User Authentication.
Install a GlobalProtect subscription for each gateway that supports the GlobalProtect app for IoT. If you use Prisma Access, a GlobalProtect subscription is not required.Customize a gateway configuration for your IoT devices:When you configure a gateway, you can specify client authentication settings that apply specifically to IoT. For example, you can configure Windows and macOS endpoints to use two-factor authentication and require IoT devices to use certificate-based authentication.You can also configure supported network and client settings—such as specific IP pools, access routes, and split tunneling—for IoT devices.- Select NetworkGlobalProtectGateways and then select or Add a gateway configuration.
- Add a Client Authentication configuration for IoT devices:
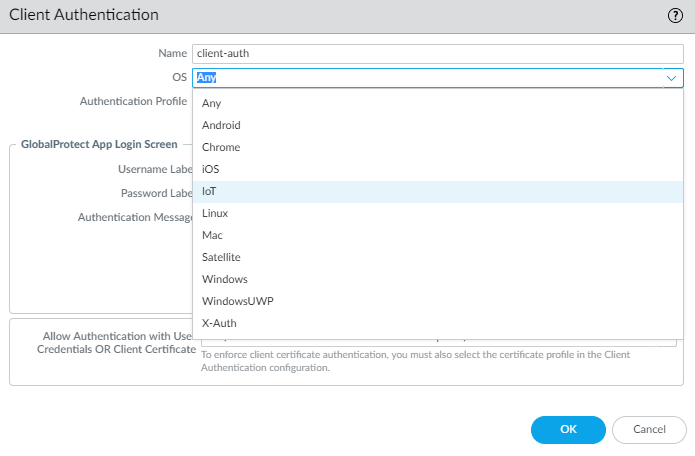
- Select Authentication and Add a new Client Authentication configuration.
- Enter a Name to identify the Client Authentication configuration, set OS to IoT, specify the Authentication Profile to use for authenticating users on this gateway. Choose a profile that enables client certificate authentication.
![]()
- Click OK.
- To configure specific client settings that apply to only IoT endpoints, configure a new Client Settings configuration:
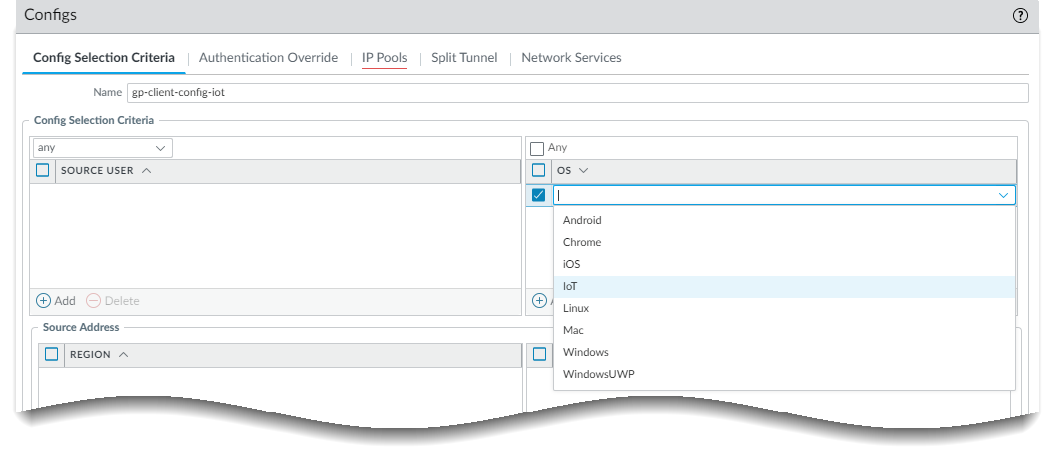
- Select Agent and Add a new Client Settings configuration.
- Configure the Client Authentication settings as desired.
- Select User/User Group and then Add an OS, and select IoT.
![]()
- Click OK.
- Click OK.
- Commit the configuration.
Configure the portal to support the GlobalProtect app for IoT devices.To support IoT devices, you must configure one or more gateways to which the GlobalProtect app can connect and then configure the portal and app settings. The portal sends configuration information and information about the available gateways to the app. After receiving the configuration from the GlobalProtect portal, the app discovers the gateways listed in the client configuration and selects the best gateway. Use the following workflow to configure the GlobalProtect portal to support the GlobalProtect app for IoT devices.- If you have not already done so, complete the prerequisite tasks for setting up a GlobalProtect portal.
- Create the interfaces (and zones) for the firewall where you plan to configure the portal. See Create Interfaces and Zones for GlobalProtect.
- Set up the portal server certificate, gateway server certificate, SSL/TLS service profiles, and, optionally, any client certificates to deploy to end users to enable SSL/TLS connections for the GlobalProtect™ services. See Enable SSL Between GlobalProtect Components.
- Define the optional authentication profiles and certificate profiles that the portal can use to authenticate GlobalProtect users. See GlobalProtect User Authentication.
Define client settings for IoT devices to authenticate to the portal.- Select NetworkGlobalProtectPortals and then select a portal configuration.
- Configure Client Authentication settings that apply to IoT devices when users access the portal:
- Select Authentication and then Add a new Client Authentication configuration.
- Enter a Name to identify the Client Authentication configuration, set OS to IoT, specify the Authentication Profile to use for authenticating users on this portal. Choose a profile that enables client certificate authentication.
Customize an agent configuration for IoT devices.Whether you modify an existing configuration or create a new one depends on your environment. For example, if you use OS-specific gateways or want to collect host information that is specific to IoT devices, consider creating a new agent configuration.For information about supported features, refer to the Palo Alto Networks Compatibility Matrix for a list of features supported by OS for IoT devices.- Define a GlobalProtect Agent Configuration:
- Select Agent and select an existing or Add a new portal agent configuration.
- Configure the Authentication settings for IoT devices.
- Select User/User Group and then add an OS and select IoT.
- Specify the external gateways to which users with this configuration can connect.
- (Optional) Select App and customize the applicable portal settings for the GlobalProtect app for IoT. The GlobalProtect app discards any settings that do not apply for IoT. For a list of supported features by operating system, refer to the Palo Alto Networks Compatibility Matrix for a list of features supported by OS for IoT devices.
- Click OK twice.
- Commit the configuration.
Enforce Policies on IoT devices (ObjectsGlobalProtectHIP Objects).You can now create HIP objects using Host Info that is specific to IoT devices and use it for match conditions in any HIP profiles. You can then use a HIP profile as a match condition in a policy rule to enforce the corresponding security policy.- Select GeneralHost InfoOS.
- Select ContainsIoT.
- Click OK.
- Create additional HIP objects as needed.
Install and set up the GlobalProtect app for IoT.Use the provided instructions for the operating system of your IoT device.