GlobalProtect
Endpoint Traffic Policy Enforcement
Table of Contents
Expand All
|
Collapse All
GlobalProtect Docs
-
10.1 & Later
- 10.1 & Later
- 9.1 (EoL)
-
- How Does the App Know Which Certificate to Supply?
- Set Up Cloud Identity Engine Authentication
- Configure GlobalProtect to Facilitate Multi-Factor Authentication Notifications
- Enable Delivery of VSAs to a RADIUS Server
- Enable Group Mapping
-
-
- GlobalProtect App Minimum Hardware Requirements
- Download the GlobalProtect App Software Package for Hosting on the Portal
- Host App Updates on the Portal
- Host App Updates on a Web Server
- Test the App Installation
- Download and Install the GlobalProtect Mobile App
- View and Collect GlobalProtect App Logs
-
-
- Deploy App Settings in the Windows Registry
- Deploy App Settings from Msiexec
- Deploy Scripts Using the Windows Registry
- Deploy Scripts Using Msiexec
- Deploy Connect Before Logon Settings in the Windows Registry
- Deploy GlobalProtect Credential Provider Settings in the Windows Registry
- SSO Wrapping for Third-Party Credential Providers on Windows Endpoints
- Enable SSO Wrapping for Third-Party Credentials with the Windows Registry
- Enable SSO Wrapping for Third-Party Credentials with the Windows Installer
- Deploy App Settings to Linux Endpoints
- GlobalProtect Processes to be Whitelisted on EDR Deployments
-
-
- Mobile Device Management Overview
- Set Up the MDM Integration With GlobalProtect
- Qualified MDM Vendors
-
-
- Set Up the Microsoft Intune Environment for Android Endpoints
- Deploy the GlobalProtect App on Android Endpoints Using Microsoft Intune
- Create an App Configuration on Android Endpoints Using Microsoft Intune
- Configure Lockdown Mode for Always On Connect Method on Android Endpoints Using Microsoft Intune
-
- Deploy the GlobalProtect Mobile App Using Microsoft Intune
- Configure an Always On VPN Configuration for iOS Endpoints Using Microsoft Intune
- Configure a User-Initiated Remote Access VPN Configuration for iOS Endpoints Using Microsoft Intune
- Configure a Per-App VPN Configuration for iOS Endpoints Using Microsoft Intune
-
-
-
- Create a Smart Computer Group for GlobalProtect App Deployment
- Create a Single Configuration Profile for the GlobalProtect App for macOS
- Deploy the GlobalProtect Mobile App for macOS Using Jamf Pro
-
- Enable GlobalProtect System Extensions on macOS Endpoints Using Jamf Pro
- Enable GlobalProtect Network Extensions on macOS Big Sur Endpoints Using Jamf Pro
- Add a Configuration Profile for the GlobalProtect Enforcer by Using Jamf Pro 10.26.0
- Verify Configuration Profiles Deployed by Jamf Pro
- Remove System Extensions on macOS Monterey Endpoints Using Jamf Pro
- Non-Removable System Extensions on macOS Sequoia Endpoints Using Jamf Pro
- Uninstall the GlobalProtect Mobile App Using Jamf Pro
-
- Configure HIP-Based Policy Enforcement
- Configure HIP Exceptions for Patch Management
- Collect Application and Process Data From Endpoints
- Redistribute HIP Reports
-
- Identification and Quarantine of Compromised Devices Overview and License Requirements
- View Quarantined Device Information
- Manually Add and Delete Devices From the Quarantine List
- Automatically Quarantine a Device
- Use GlobalProtect and Security Policies to Block Access to Quarantined Devices
- Redistribute Device Quarantine Information from Panorama
- Troubleshoot HIP Issues
-
-
- Enable and Verify FIPS-CC Mode on Windows Endpoints
- Enable and Verify FIPS-CC Mode on macOS Endpoints
- Enable and Verify FIPS-CC Mode Using Workspace ONE on iOS Endpoints
- Enable FIPS Mode on Linux EndPoints with Ubuntu or RHEL
- Enable and Verify FIPS-CC Mode Using Microsoft Intune on Android Endpoints
- FIPS-CC Security Functions
- Resolve FIPS-CC Mode Issues
-
-
- Remote Access VPN (Authentication Profile)
- Remote Access VPN (Certificate Profile)
- Remote Access VPN with Two-Factor Authentication
- GlobalProtect Always On VPN Configuration
- Remote Access VPN with Pre-Logon
- User-Initiated Pre-Logon Connection
- GlobalProtect Multiple Gateway Configuration
- GlobalProtect for Internal HIP Checking and User-Based Access
- Mixed Internal and External Gateway Configuration
- Captive Portal and Enforce GlobalProtect for Network Access
- GlobalProtect on Windows 365 Cloud PC
-
- About GlobalProtect Cipher Selection
- Cipher Exchange Between the GlobalProtect App and Gateway
-
- Reference: GlobalProtect App Cryptographic Functions
-
- Reference: TLS Ciphers Supported by GlobalProtect Apps on macOS Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on Windows Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on Android 6.0.1 Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on iOS 10.2.1 Endpoints
- Reference: TLS Ciphers Supported by GlobalProtect Apps on Chromebooks
- Ciphers Used to Set Up IPsec Tunnels
- SSL APIs
-
- View a Graphical Display of GlobalProtect User Activity in PAN-OS
- View All GlobalProtect Logs on a Dedicated Page in PAN-OS
- Event Descriptions for the GlobalProtect Logs in PAN-OS
- Filter GlobalProtect Logs for Gateway Latency in PAN-OS
- Restrict Access to GlobalProtect Logs in PAN-OS
- Forward GlobalProtect Logs to an External Service in PAN-OS
- Configure Custom Reports for GlobalProtect in PAN-OS
-
6.3
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
-
- Download and Install the GlobalProtect App for Windows
- Use Connect Before Logon
- Use Single Sign-On for Smart Card Authentication
- Use the GlobalProtect App for Windows
- Report an Issue From the GlobalProtect App for Windows
- Disconnect the GlobalProtect App for Windows
- Uninstall the GlobalProtect App for Windows
- Fix a Microsoft Installer Conflict
-
- Download and Install the GlobalProtect App for macOS
- Use the GlobalProtect App for macOS
- Report an Issue From the GlobalProtect App for macOS
- Disconnect the GlobalProtect App for macOS
- Uninstall the GlobalProtect App for macOS
- Remove the GlobalProtect Enforcer Kernel Extension
- Enable the GlobalProtect App for macOS to Use Client Certificates for Authentication
-
6.0
- 6.1
- 6.0
- 5.1
-
- Redesigned GlobalProtect App User Interface for Windows and macOS
- Endpoint Traffic Policy Enforcement
- Improved Connectivity Experience for the GlobalProtect App for Android and iOS
- Security Policy Enforcement for Inactive GlobalProtect Sessions
- Single Sign-On (SSO) Using Smart Card Authentication
- Delivery Optimization Support for Windows
- Improved Authentication Experience for the GlobalProtect App for Windows and macOS
- SAML Authentication with Cloud Authentication Service
- No Direct Access to Local Network Support for Linux
-
6.3
- 6.3
- 6.2
- 6.1
- 6.0
- 5.1
Endpoint Traffic Policy Enforcement
Learn how to prevent users from bypassing GlobalProtect using the physical
adapter.
Software Support: Starting with GlobalProtect™
app 6.0 with Content Release version 8450-6909 or later.
OS
Support: Windows 10, ARM64-Based Windows 10, macOS 11 and later
releases, and ARM-Based macOS 11 and later releases
With the
Endpoint Traffic Policy Enforcement feature, GlobalProtect now provides
added security to protect your remote workforce. By enforcing endpoint traffic
policy on the GlobalProtect endpoint, you can now perform the following
functions:
- Block malicious inbound connections outside of the VPN tunnel to guard against data exfiltration.
- Restrict any applications from bypassing the GlobalProtect tunnel by binding their connections directly to the physical adapter on the remote endpoint.
- Prevent end users from tampering with the routing table to bypass the GlobalProtect tunnel.
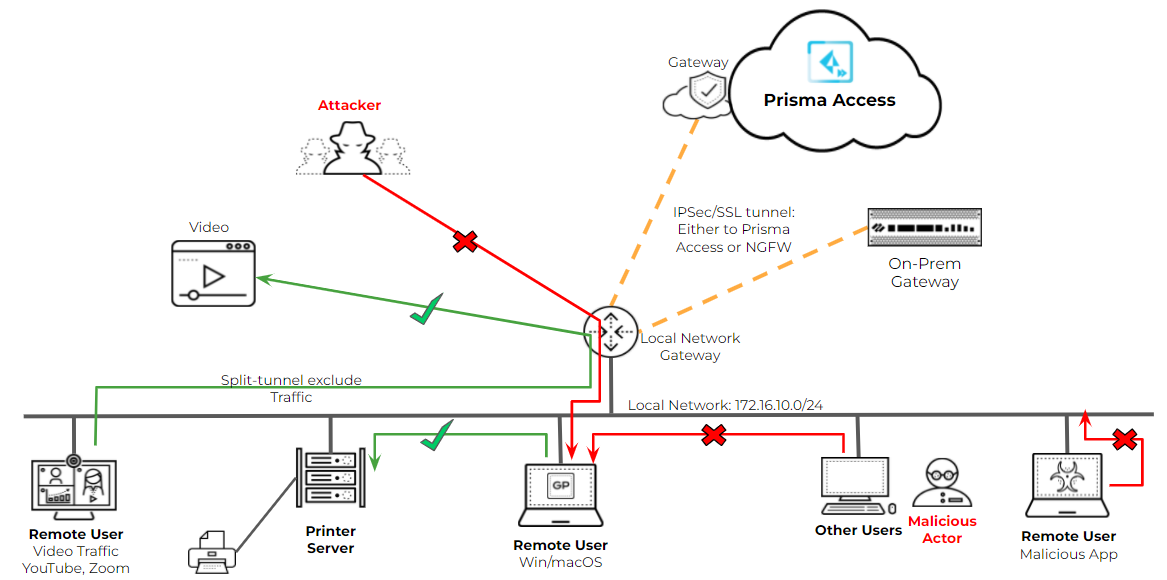
The following diagram
illustrates the scenarios for enforcing endpoint traffic policy
to block malicious inbound connections and to prevent bypassing
the IPSec or SSL tunnel that GlobalProtect builds to Prisma Access
or to a gateway on the NGFW:
- The attacker can attempt to have malicious inbound connections to the remote endpoint.
- A malicious actor can attempt to perform an act within the same local network as the remote GlobalProtect endpoint.
- An application can attempt to bind the connection directly to the physical adapter on the remote user's endpoint.
Configure Endpoint Traffic Enforcement
Configure endpoint
traffic policy enforcement to block malicious inbound connections
using the physical adapter on the remote endpoint and prevent users
from accessing unauthorized applications or resources after the
GlobalProtect tunnel is established.
- Enable Endpoint Traffic
Policy Enforcement.
- Launch the Web Interface.
- Select NetworkGlobalProtectPortals<portal-config> Agent<agent-config> AppEndpoint Traffic Policy Enforcement.
- Select one of the following endpoint traffic policy
enforcement options:
Option Description No Specifies that the Endpoint Traffic Policy Enforcement feature is disabled and that this feature is not applied. This is the default option.TCP/UDP Traffic Based on Tunnel IP Address Type Enables endpoint traffic policy enforcement for TCP/UDP traffic. This feature is enabled for traffic based on the tunnel IP address type. If the tunnel is IPv4, this feature applies only to IPv4 traffic. If the tunnel is IPv6, this features applies only to IPv6 traffic.All TCP/UDP Traffic Enables endpoint traffic policy enforcement for all TCP/UDP traffic regardless of the tunnel IP address type. If the tunnel IP address type is IPv4, endpoint traffic policy enforcement applies to all TCP/UDP (IPv4 or IPv6) traffic. If the tunnel IP address type is IPv6, endpoint traffic policy enforcement applies to all TCP/UDP (IPv4 or IPv6) traffic.All Traffic Enables endpoint traffic policy enforcement for all TCP, UDP, ICMP, and all other protocols regardless of the tunnel IP address type.
- Save the configuration.
- Click OK twice.
- Commit the configuration.
- Verify the endpoint traffic policy enforcement configuration.You can verify the endpoint traffic policy enforcement option in the GlobalProtect service (PanGPS) log file.The following example shows the entry in the PanGPS log file:<traffic-enforcement>tcp-udp-with-tunnel-address-type</traffic-enforcement>To verify that the feature is working as expected generate a packet capture on both the physical adapter and the GlobalProtect adapter from the client machine while connected to GlobalProtect and then try to access any websites or resources to verify that the traffic is being enforced as expected based on your configuration.
Endpoint Traffic Enforcement with No Direct Access to Local Network
You can use Endpoint
Traffic Policy Enforcement in conjunction with No Direct Access
to Local Network Support to control access to the local network.
The following table shows the traffic behavior and interaction between the
features.
IPv4 and IPv6 Traffic | Endpoint Traffic Policy Enforcement
Enabled No Direct Access to Local Network is Disabled | Endpoint Traffic Policy Enforcement
Enabled No Direct Access to Local Network is Enabled | ||
|---|---|---|---|---|
Before the tunnel is established | After the tunnel is established | Before the tunnel is established | After the tunnel is established | |
New Incoming Traffic | Traffic is allowed on the local subnet through
the physical adapter. | Local subnet traffic is excluded. Return
traffic from the local subnet will not be dropped on the non-tunnel interface. | Traffic is allowed on the local subnet through
the physical adapter. | Return traffic is dropped on the physical adapter
unless split tunneling is configured to exclude traffic based on
the following conditions:
|
New Outgoing Traffic | Traffic is allowed on the local subnet through
the physical adapter. | Traffic is sent through the VPN tunnel unless
the destination IP address matches the following exclusions for
split tunnel:
| Traffic is allowed on the local subnet through
the physical adapter. | Traffic is sent through the VPN tunnel unless the
destination IP address matches the following exclusions for split tunnel:
|
Existing Traffic | Traffic is allowed on the local subnet through
the physical adapter. | Traffic is terminated unless the destination
IP address matches the following exclusions for split tunnel:
| Traffic is allowed on the local subnet through
the physical adapter. | Traffic is terminated unless the destination
IP address matches the following exclusions for split tunnel:
|
1 The destination domains will not
work for existing connections that started before establishing the
GlobalProtect connection because GlobalProtect does not have visibility
that is associated with the DNS. However, this traffic behavior will
work for existing connections across GlobalProtect reconnections
because GlobalProtect can monitor the DNS during the reconnect interval.
Endpoint Traffic Policy Enforcement Use Cases
Endpoint Traffic
Policy Enforcement supports the following use cases:
Prevent All Traffic from Bypassing the Tunnel
No traffic can
bypass the tunnel after establishing incoming or outgoing connections.
When the No Direct Access to Local Networks feature is enabled in
conjunction with the Endpoint Traffic Policy Enforcement feature
being enabled, mobile users are unable to access proxies and local
resources (such as local printers) directly when traffic is going
through the VPN tunnel for inspection and policy enforcement while
enabled on GlobalProtect.
- Enable No direct access to local network ( AgentClient Settings <client-setting-config>Split TunnelAccess Route).
- Set Endpoint Traffic Policy Enforcement to All Traffic.
Exclude High Bandwidth Consuming Domains While Preventing Local Subnet Traffic
By enabling the
No Direct Access to Local Networks feature in conjunction with the
Endpoint Traffic Policy Enforcement you can exclude high bandwidth
consuming domains from the tunnel while blocking local subnet traffic.
In this use case, mobile users cannot access proxies and local resources
(such as local printers) directly when traffic is going through
the VPN tunnel for inspection and policy enforcement while connected
to GlobalProtect. By excluding split tunnel traffic based on the
domain, all traffic for that specific domain is sent directly to
the physical adapter on the endpoint without inspection.
- Enable No direct access to local network ( AgentClient Settings <client-setting-config>Split TunnelAccess Route).
- Configure split tunneling to exclude high-bandwidth traffic such as video from the tunnel.
- Set Endpoint Traffic Policy Enforcement to All Traffic.
Allow Local Traffic While Preventing Traffic on the Physical Adapter
Traffic is sent
over the VPN tunnel and end users can access local resources (such
as printers) directly. When the No Direct Access to Local Network
Support feature is disabled in conjunction with the Endpoint Traffic
Policy Enforcement feature being enabled, mobile users are able
to access proxies and local resources (such as local printers) directly
when all traffic is going through the VPN tunnel for inspection
and policy enforcement while connected to GlobalProtect. If a malicious
actor attempts to perform an act within the same local network as
the remote GlobalProtect endpoint, malicious incoming connections
can be sent directly to the physical adapter on the mobile user’s
endpoint.
- Disable No direct access to local network ( AgentClient Settings <client-setting-config>Split TunnelAccess Route).
- Set Endpoint Traffic Policy Enforcement to All Traffic.
Exclude High Bandwidth Consuming Domains and Allow Access to Local Resources While Preventing Traffic on the Physical Adapter
High bandwidth
consuming domains are excluded but end users can access local resources
(such as local printers) directly and some traffic is sent through
the VPN tunnel. When the No Direct Access to Local Network Support feature
is disabled in conjunction with the Endpoint Traffic Policy Enforcement
feature being either enabled or disabled, mobile users are able
to access proxies and local resources (such as local printers) directly
when traffic to the corporate network is going through the VPN tunnel
for inspection and policy enforcement while enabled on GlobalProtect.
- Disable No direct access to local network ( AgentClient Settings <client-setting-config>Split TunnelAccess Route).
- Configure split tunneling to exclude high bandwidth consuming domains and applications, such as video.
- Set Endpoint Traffic Policy Enforcement to prevent All TCP/UDP Traffic, TCP/UDP Traffic Based on Tunnel IP Address Type, or All Traffic on the physical adapter.
Feature Limitations
The following limitations
apply:
- ICMP requests are not supported for domain- or app-based split tunneling or for enforcing endpoint traffic policy.
- You cannot exclude split tunnel traffic based on server-side applications for incoming connections.
- TCP handshake packets are bypassed. Some TCP ACK packets with no data might be seen in the packet capture (pcap) data.
- Exclusions for destination domains might not work for new incoming connections without the DNS query or DNS response because GlobalProtect will not know the IP address of the destination domain.
- (macOS only) Exclusions for applications will not work for new incoming connections and existing connections.
- (macOS only) Traffic is allowed on TCP ports 53 and 5353.
- (Windows only) DHCP traffic (UDP remote port 67) and DNS (UDP remote port 53) is allowed.
- The feature cannot be used for bridge-mode networking or for Layer 2 controls. You can prohibit the use of bridge mode for Virtual Machine applications on your endpoints to workaround this limitation or use standard Layer 3 networking with NAT.

