Define the Satellite Configurations
Table of Contents
End-of-Life (EoL)
Define the Satellite Configurations
When a GlobalProtect satellite connects and
successfully authenticates to the GlobalProtect portal, the portal
delivers a satellite configuration, which specifies what gateways
the satellite can connect to. If all your satellites will use the
same gateway and certificate configurations, you can create a single
satellite configuration to deliver to all satellites upon successful
authentication. However, if you require different satellite configurations—for
example if you want one group of satellites to connect to one gateway
and another group of satellites to connect to a different gateway—you
can create a separate satellite configuration for each. The portal
will then use the enrollment username/group name or the serial number
of the satellite to determine which satellite configuration to deploy.
As with security rule evaluation, the portal looks for a match starting
from the top of the list. When it finds a match, it delivers the
corresponding configuration to the satellite.
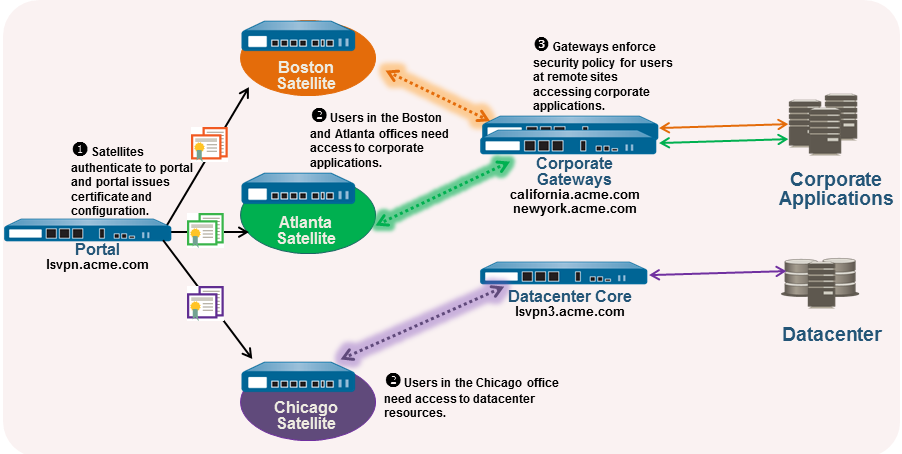
For example,
the following figure shows a network in which some branch offices
require VPN access to the corporate applications protected by your
perimeter firewalls and another site needs VPN access to the data
center.
Use
the following procedure to create one or more satellite configurations.
- Add a satellite configuration.The satellite configuration specifies the GlobalProtect LSVPN configuration settings to deploy to the connecting satellites. You must define at least one satellite configuration.
- Select NetworkGlobalProtectPortals and select the portal configuration for which you want to add a satellite configuration and then select the Satellite tab.In the Satellite section, click Add.Enter a Name for the configuration.If you plan to create multiple configurations, make sure the name you define for each is descriptive enough to allow you to distinguish them.To change how often a satellite should check the portal for configuration updates specify a value in the Configuration Refresh Interval (hours) field (range is 1-48; default is 24).Specify the satellites to which to deploy this configuration.The portal uses the Enrollment User/User Group settings and/or Devices serial numbers to match a satellite to a configuration. Therefore, if you have multiple configurations, be sure to order them properly. As soon as the portal finds a match, it will deliver the configuration. Therefore, more specific configurations must precede more general ones. See Step 5 for instructions on ordering the list of satellite configurations.Specify the match criteria for the satellite configuration as follows:
- To restrict this configuration to satellites with specific serial numbers, select the Devices tab, click Add, and enter serial number (you do not need to enter the satellite hostname; it will be automatically added when the satellite connects). Repeat this step for each satellite you want to receive this configuration.
- Select the Enrollment User/User Group tab, click Add, and then select the user or group you want to receive this configuration. Satellites that do not match on serial number will be required to authenticate as a user specified here (either an individual user or group member).
Before you can restrict the configuration to specific groups, you must Map Users to Groups.Specify the gateways that satellites with this configuration can establish VPN tunnels with.Routes published by the gateway are installed on the satellite as static routes. The metric for the static route is 10x the routing priority. If you have more than one gateway, make sure to also set the routing priority to ensure that routes advertised by backup gateways have higher metrics compared to the same routes advertised by primary gateways. For example, if you set the routing priority for the primary gateway and backup gateway to 1 and 10 respectively, the satellite will use 10 as the metric for the primary gateway and 100 as the metric for the backup gateway.- On the Gateways tab, click Add.Enter a descriptive Name for the gateway. The name you enter here should match the name you defined when you configured the gateway and should be descriptive enough identify the location of the gateway.Enter the FQDN or IP address of the interface where the gateway is configured in the Gateways field. The address you specify must exactly match the Common Name (CN) in the gateway server certificate.(Optional) If you are adding two or more gateways to the configuration, the Routing Priority helps the satellite pick the preferred gateway. Enter a value in the range of 1-25, with lower numbers having the higher priority (that is, the gateway the satellite will connect to if all gateways are available). The satellite will multiply the routing priority by 10 to determine the routing metric.Save the satellite configuration.
- Click OK to save the satellite configuration.If you want to add another satellite configuration, repeat the previous steps.Arrange the satellite configurations so that the proper configuration is deployed to each satellite.
- To move a satellite configuration up on the list of configurations, select the configuration and click Move Up.
- To move a satellite configuration down on the list of configurations, select the configuration and click Move Down.
Specify the certificates required to enable satellites to participate in the LSVPN.- In the Trusted Root CA field, click Add and then select the CA certificate used to issue the gateway server certificates. The portal will deploy the root CA certificate you add here to all satellites as part of the configuration to enable the satellite to establish an SSL connection with the gateways. As a best practice, all of your gateways should use the same issuer.Select the method of Client Certificate distribution:
- To store the client certificates on the portal—select Local and select the Root CA certificate that the portal will use to issue client certificates to satellites upon successfully authenticating them from the Issuing Certificate drop-down.
If the root CA certificate used to issue your gateway server certificates is not on the portal, you can Import it now. See Enable SSL Between GlobalProtect LSVPN Components for details on how to import a root CA certificate.- To enable the portal to act as a SCEP client to dynamically request and issue client certificates—select SCEP and then select the SCEP profile used to generate CSRs to your SCEP server.
If the you have not yet set up the portal to act as a SCEP client, you can add a New SCEP profile now. See Deploy Client Certificates to the GlobalProtect Satellites Using SCEP for details.Save the portal configuration.- Click OK to save the settings and close the GlobalProtect Portal Configuration dialog.Commit your changes.
