View Policy Rule Usage
Table of Contents
End-of-Life (EoL)
View Policy Rule Usage
View the policy rule hit count data of managed firewalls
to monitor rule usage so you can validate rules and keep your rule
base organized.
View the number of times a Security, NAT,
QoS, policy-based forwarding (PBF), Decryption, Tunnel Inspection,
Application Override, Authentication, or DoS protection rule matches
traffic to help keep your firewall policies up to date as your environment
and security needs change. To prevent attackers from exploiting over-provisioned
access, such as when a server is decommissioned or when you no longer
need temporary access to a service, use the policy rule hit count
data to identify and remove unused rules.
Policy rule usage
data enables you to validate rule additions and rule changes and
to monitor the time frame when a rule was used. For example, when
you migrate port-based rules to app-based rules, you create an app-based
rule above the port-based rule and check for any traffic that matches
the port-based rule. After migration, the hit count data helps you
determine whether it is safe to remove the port-based rule by confirming
whether traffic is matching the app-based rule instead of the port-based
rule. The policy rule hit count helps you determine whether a rule
is effective for access enforcement.
You can reset the rule
hit count data to validate an existing rule or to gauge rule usage
within a specified period of time. Policy rule hit count data is
not stored on the firewall or Panorama so that data is no longer available
after you reset (clear) the hit count.
After filtering your
policy rulebase, administrators can take action to delete, disable,
enable, and tag policy rules directly from the policy optimizer.
For example, you can filter for unused rules and then tag them for review
to determine whether they can be safely deleted or kept in the rulebase.
By enabling administrators to take action directly from the policy
optimizer, you reduce the management overhead required to further assist
in simplifying your rule lifecycle management and ensure that your
firewalls are not over-provisioned.
The rule hit count
data is not synchronized across firewalls in a high availability
(HA) deployment so you need to log in to each firewall to view the
policy rule hit count data for each firewall or use Panorama to
view information on the HA firewall peers.
Policy
rule usage data is also useful when using Security Policy Rule Optimization to determine
which rules to migrate or clean up first.
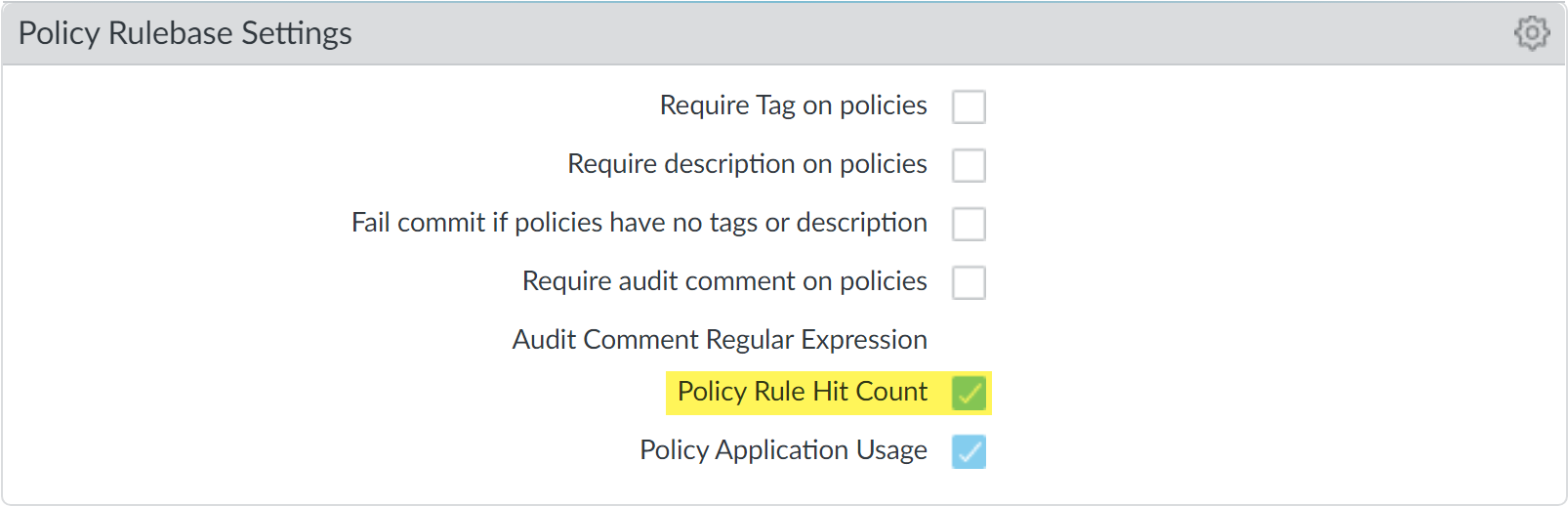
- Launch the Web Interface.Verify that Policy Rule Hit Count is enabled.
- Navigate to Policy Rulebase Settings (DeviceSetup Management).Verify that Policy Rule Hit Count is enabled.
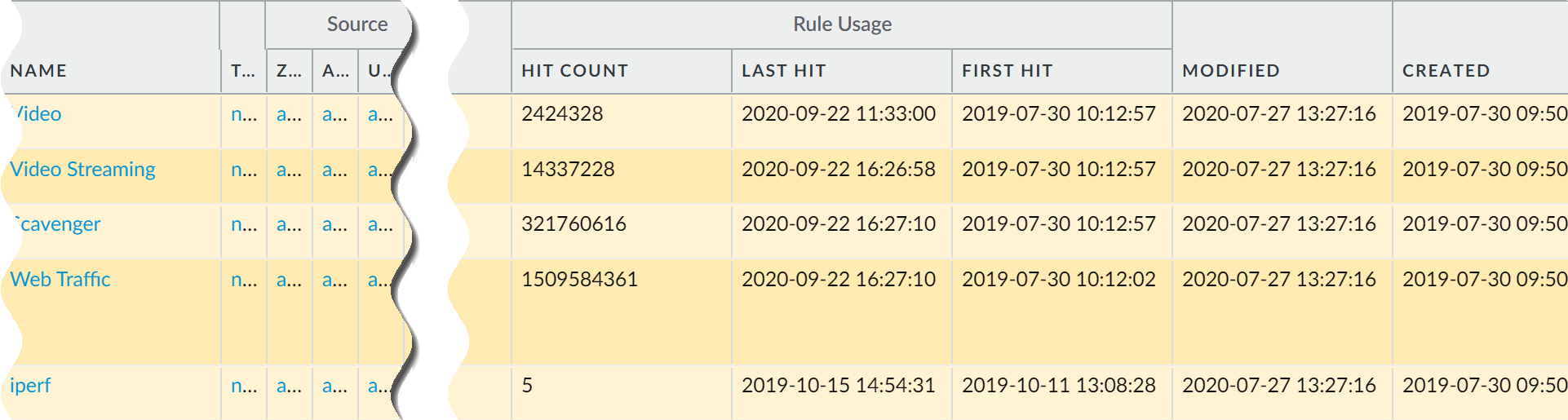
![]() Select Policies.View the policy rule usage for each policy rule:
Select Policies.View the policy rule usage for each policy rule:- Hit Count—The number of times traffic matched the criteria you defined in the policy rule. Persists through reboot, dataplane restarts, and upgrades unless you manually reset or rename the rule.
- Last Hit—The most recent timestamp for when traffic matched the rule.
- First Hit—The first instance when traffic was matched to this rule.
- Modified—The date and time the policy rule was last modified.
- Created—The date and time the policy rule was created.If the rule was created when Panorama was running PAN-OS 8.1 and the Policy Rule Hit Count setting is enabled, the First Hit date and time is used as the Created date and time on upgrade to PAN-OS 9.0. If the rule was created in PAN-OS 8.1 when the Policy Rule Hit Count setting was disabled or if the rule was created when Panorama was running PAN-OS 8.0 or an earlier release, the Created date for the rule will be the date and time you successfully upgraded Panorama to PAN-OS 9.0
![]() In the Policy Optimizer dialog, view the Rule Usage filter.Filter rules in the selected rulebase.Use the rule usage filter to evaluate the rule usage within a specified period of time. For example, filter the selected rulebase for Unused rules within the last 30 days. You can also evaluate rule usage with other rule attributes, such as the Created and Modified dates, which enables you to filter for the correct set of rules to review. You can use this data to help manage your rule lifecycle and to determine if a rule needs to be removed to reduce your network attack surface.
In the Policy Optimizer dialog, view the Rule Usage filter.Filter rules in the selected rulebase.Use the rule usage filter to evaluate the rule usage within a specified period of time. For example, filter the selected rulebase for Unused rules within the last 30 days. You can also evaluate rule usage with other rule attributes, such as the Created and Modified dates, which enables you to filter for the correct set of rules to review. You can use this data to help manage your rule lifecycle and to determine if a rule needs to be removed to reduce your network attack surface.- Select the Timeframe you want to filter on or specify a Custom time frame.Select the rule Usage on which to filter.(Optional) If you have reset the rule usage data for any rules, check for Exclude rules reset during the last <number of days> days and decide when to exclude a rule based on the number of days you specify since the rule was reset. Only rules that were reset before your specified number of days are included in the filtered results.
![]() (Optional) Specify search filters based on rule data
(Optional) Specify search filters based on rule data- Hover your cursor over the column header and Columns.
- Add any additional columns you want to display or use for filter.
![]()
- Hover your cursor over the column data that you would like to filter on Filter. For data that contain dates, select whether to filter using This date, This date or earlier, or This date or later.
- Apply Filter ().
![]()
![]()
Take action on one or more unused policy rules.- Select one or more unused policy rules.Perform one of the following actions:
- Delete—Delete one or more selected policy rules.
- Enable—Enable one or more selected policy rules when disabled.
- Disable—Disable one or more selected policy rules.
- Tag—Apply one or more group tags to one or more selected policy rules. The group tag must already exist in order to tag policy rule.
- Untag—Remove one or more group tags from one or more selected policy rules.
Commit your changes.