Next-Generation Firewall
Dynamic IPv6 Addressing on the Management Interface
Table of Contents
Expand All
|
Collapse All
Next-Generation Firewall Docs
-
-
-
-
-
-
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 11.0 (EoL)
- PAN-OS 10.2
- PAN-OS 10.1
- PAN-OS 10.0 (EoL)
- PAN-OS 9.1 (EoL)
- PAN-OS 9.0 (EoL)
- PAN-OS 8.1 (EoL)
-
- PAN-OS 12.1
- PAN-OS 11.2
- PAN-OS 11.1
- PAN-OS 10.2
- PAN-OS 10.1
Dynamic IPv6 Addressing on the Management Interface
Learn about the management interface receiving its dynamic IPv6 address using either
stateful DHCPv6 or SLAAC with stateless DHCPv6.
| Where Can I Use This? | What Do I Need? |
|---|---|
|
The management (MGT) interface on the NGFW supports dynamic IPv6 address assignment.
Configuring the management interface for
dynamic IPv6 address assignment (rather than a static address) makes it
easier to insert and manage the firewall in an IPv6 network.
You have two types of addressing to choose from: stateful or stateless. On the network
segment, you control the router where you set flags to indicate that the MGT interface
will be one of the following:
- A stateful DHCPv6 client, which receives its IPv6 address, prefix length, and other configuration from a DHCPv6 server.
- An IPv6 stateless address autoconfiguration (SLAAC) client, which autogenerates its IPv6 address. A stateless IPv6 address avoids a DHCPv6 server having to store dynamic state information about clients; such avoidance is helpful in environments with a large number of endpoints.
The firewall uses Neighbor Discovery Protocol (NDP) to send a Router Solicitation to all
routers on the link. The flags in the Router Advertisement (RA) that the sole router (or
preferred router) on the link sends to the firewall control whether the firewall will
use SLAAC or stateful DHCPv6 to get a dynamic address for the MGT interface.
However, the current situation is that when the Autonomous (A) flag is set in the RA
message, the firewall chooses both a DHCPv6 address and a SLAC address. Ideally, the
firewall should choose only the SLAAC address and shouldn't send a DHCPv6 Solicit
message. As a result of this known issue, if there is a DHCPv6 server on the segment and
it can assign an IPv6 address, the firewall prefers DHCPv6 address assignment over
SLAAC.
The following example illustrates stateful DHCPv6 address assignment.
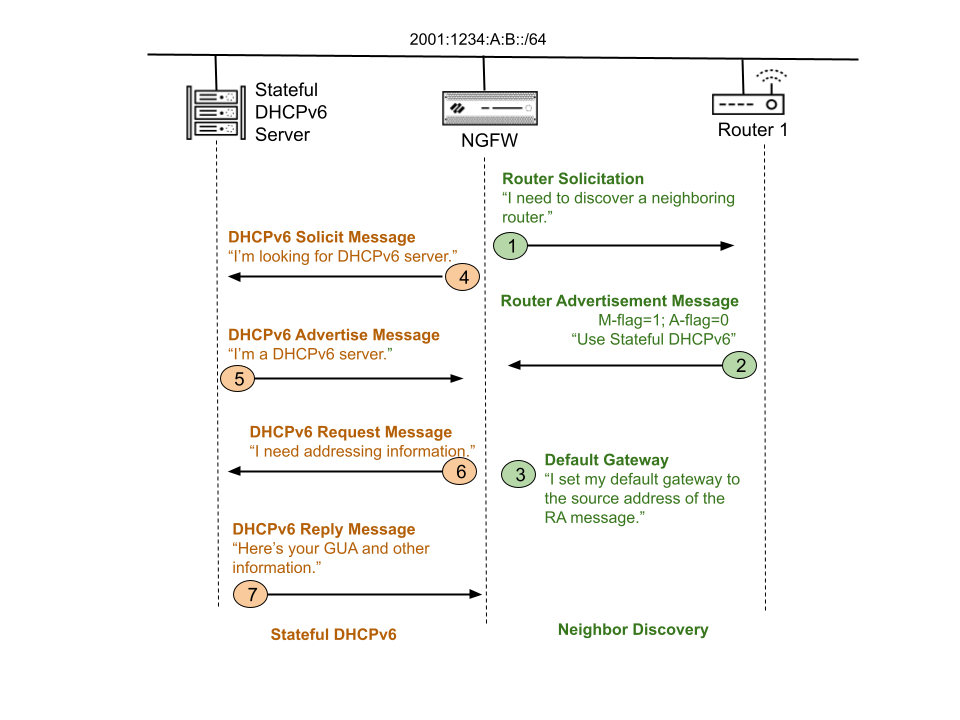
In the example topology, the firewall is connected to a router acting as the default
gateway. The firewall is an IPv6 SLAAC/DHCPv6 client connected to a DHCPv6 server. After
you enable IPv6 on the MGT interface, select Dynamic address type and Dynamic default
gateway type, and commit, the following process occurs.
- Default gateway assignment occurs using a Router Solicitation (RS) and a Router
Advertisement (RA) (right side of graphic).Hosts set their default gateway based on the source address of the only (or the preferred) router attached to the link. The firewall uses Neighbor Discovery Protocol (NDP) to send an RS to all routers on the link. If only one router is attached to the link, the firewall uses the source address of that router's ICMPv6 RA messages as its default gateway address. If the firewall receives RAs from multiple routers attached to the link, the firewall uses the source address of the RA message that has the highest default router preference (low, medium, or high) as its default gateway address.In response to the RS, the flags in the RA that the router sends to the firewall indicate whether the firewall will use SLAAC or stateful DHCPv6 to get a dynamic address for the management interface, as follows:
- An Autonomous (A) flag set to 1 tells the firewall to autogenerate a Global Unicast Address (GUA) using SLAAC. The firewall uses the prefix from the prefix options in the RA message, along with the EUI-64 Interface ID of the MGT interface, to create a GUA for the MGT interface. The Interface ID is created from the MAC address of the management interface. (If the flag is set to 0, autoconfiguration isn't allowed on the segment.)
- An Other Configuration (O) flag set to 1 tells the firewall that it can
get a DNS server list and a domain name from a stateless DHCPv6 server
(but not addressing information). Usually the O flag works with SLAAC
autoconfiguration and both the A flag and O flag are set to 1.Currently, there is a known issue with the O flag (stateless DHCPv6), which isn't supported in this release.
- A Managed (M) flag set to 1 tells the firewall to get its IPv6 network
parameters (such as its global address, DNS, and a domain name) from a
stateful DHCPv6 server. The firewall contacts a DHCPv6 server to request
a GUA and the other information. Typically this means that SLAAC
autoaddressing isn't allowed on the segment and both the A flag and O
flag are set to 0.Currently, there is a known issue that the firewall sends a DHCPv6 Solicit message even when the M flag isn't set.
The following steps correspond to callouts in the graphic.- Step 1—The firewall sends an RS to the well-known multicast address for all routers (FF02::2).
- Step 2—In response, Router 1 generates an RA with the M-flag set to 1 and the A-flag set to 0, indicating to the firewall that SLAAC isn't allowed on the segment and it must use stateful DHCPv6 for addressing and other configuration.
- Step 3—Upon receipt of the RA, the firewall sets the source IPv6 address of Router 1 as its default gateway. Because the A-flag is set to 0, the firewall does not perform SLAAC.
- Dynamic address assignment occurs using DHCPv6 (left side of the graphic).
- Step 4—Based on the M-flag set to 1 in the RA, the firewall sends a DHCPv6 Solicit message to the well-known multicast address for all DHCPv6 agents (FF01::1:2), searching for a DHCPv6 server.
- Step 5—Upon receipt of the Solicit message, the server unicasts a DHCPv6 Advertise message to the link-local address of the firewall.
- Step 6—The firewall knows DHCPv6 service is available and sends a Request for addressing information.
- Step 7—Upon receipt of the Request, the server sends a DHCPv6 Reply containing the GUA and all other information available to assign. (The DNS information is taken from the DHCPv4 server, not the DHCPv6 server.)
- The firewall performs Duplicate Address Detection (DAD) on the GUA it receives to confirm the GUA is unique. If DAD determines that the IPv6 address is a duplicate (whether a SLAAC, DHCPv6, or even a link-local address), the IPv6 address is not seen in the interface.
Alternatively, you could configure Router 1 to use IPv6 SLAAC (not shown in the graphic)
for dynamic address assignment. In this case, Router 1 sends an RA with the A-flag set
to 1, indicating the firewall must create its GUA using SLAAC. You can configure the
Prefix options in the RA message along with the A-flag. The firewall uses the prefix
coming from the prefix options of the RA (which is 2001:1234:A:B::/64 in the example
topology) in addition to the EUI-64 Interface ID to create one or more GUAs. The
Interface ID can be created based on the MAC address of the MGT interface (EUI-64).
Configuring the MGT interface as a DHCPv6 client involves requesting a Non-Temporary or
Temporary Address, the Rapid Commit option, the type of DHCPv6 Unique ID type, and
specifying a static or dynamic default gateway address.
