Use Dynamic Address Groups in Policy
Table of Contents
End-of-Life (EoL)
Use Dynamic Address Groups in Policy
Dynamic address groups are used in policy.
They allow you to create policy that automatically adapts to changes—adds,
moves, or deletions of servers. It also enables the flexibility
to apply different rules to the same server based on tags that
define its role on the network, the operating system, or the different
kinds of traffic it processes.
A dynamic address group uses
tags as a filtering criteria to determine its members. The filter
uses logical and and or operators. All
IP addresses or address groups that match the filtering criteria
become members of the dynamic address group. Tags can be defined
statically on the firewall and/or registered (dynamically) to the
firewall. The difference between static and dynamic tags is that
static tags are part of the configuration on the firewall, and dynamic
tags are part of the runtime configuration. This implies that a
commit is not required to update dynamic tags; the tags must however
be used by Dynamic Address Groups that are referenced in policy,
and the policy must be committed on the firewall.
To dynamically
register tags, you can use the XML API or the VM Monitoring agent
on the firewall or on the User-ID agent. Each tag is a metadata
element or attribute-value pair that is registered on the firewall
or Panorama. For example, IP1 {tag1, tag2,.....tag32}, where the
IP address and the associated tags are maintained as a list; each
registered IP address can have up to 32 tags such as the operating
system, the datacenter or the virtual switch to which it belongs.
After receiving the API call, the firewall registers the IP address
and associated tags, and automatically updates the membership information
for the dynamic address group(s).
The maximum number of IP
addresses that can be registered for each model is different. Use
the following table for specifics on your model:
Model | Maximum number of
dynamically registered IP addresses |
|---|---|
M-Series and Panorama Virtual Appliances | 500,000 |
| PA-5200 Series, VM-7000 SMC-B Series | 500,000 |
| VM-500, VM-700 | 300,000 |
| PA-3200 Series, VM-300 | 200,000 |
PA-7000 Series | 100,000 |
PA-850, VM-100 | 2,500 |
PA-820, PA-220, VM-50 | 1,000 |
An IP set, such as an IP range or subnet,
is considered as a single registered IP address when counted towards
the maximum number of registered IP addresses supported by each
firewall model.
The following example shows how dynamic
address groups can simplify network security enforcement. The example
workflow shows how to:
- Enable the VM Monitoring agent on the firewall, to monitor the VMware ESX(i) host or vCenter Server and register VM IP addresses and the associated tags.
- Create dynamic address groups and define the tags to filter. In this example, two address groups are created. One that only filters for dynamic tags and another that filters for both static and dynamic tags to populate the members of the group.
- Validate that the members of the dynamic address group are populated on the firewall.
- Use dynamic address groups in policy. This example uses two different security policies:
- A security policy for all Linux servers that are deployed as FTP servers; this rule matches on dynamically registered tags.
- A security policy for all Linux servers that are deployed as web servers; this rule matches on a dynamic address group that uses static and dynamic tags.
- Validate that the members of the dynamic address groups are updated as new FTP or web servers are deployed. This ensure that the security rules are enforced on these new virtual machines too.
- Enable VM Source Monitoring.Create dynamic address groups on the firewall.View the tutorial to see a big picture view of the feature.
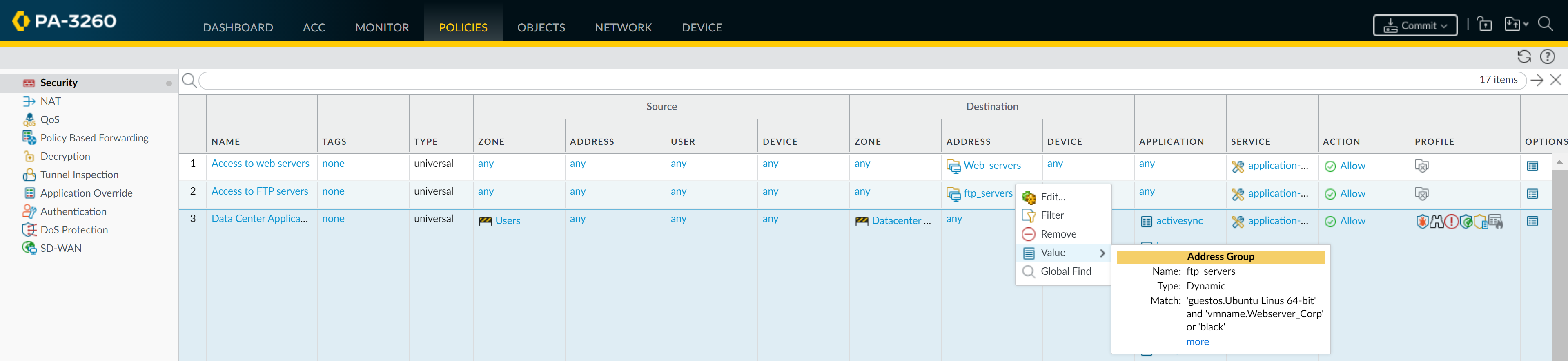
- Log in to the web interface of the firewall.Select ObjectAddress Groups.Click Add and enter a Name and a Description for the address group.Select Type as Dynamic.Define the match criteria. You can select dynamic and static tags as the match criteria to populate the members of the group. Click Add Match Criteria, and select the And or Or operator and select the attributes that you would like to filter for or match against. and then click OK.Click Commit.The match criteria for each dynamic address group in this example is as follows:ftp_server: matches on the guest operating system “Linux 64-bit” and annotated as “ftp” ('guestos.Ubuntu Linux 64-bit' and 'annotation.ftp').web-servers: matches on two criteria—the tag black or if the guest operating system is Linux 64-bit and the name of the server us Web_server_Corp. ('guestos.Ubuntu Linux 64-bit' and 'vmname.WebServer_Corp' or 'black')Use dynamic address groups in policy.View the tutorial.
- Select PoliciesSecurity.Click Add and enter a Name and a Description for the policy.Add the Source Zone to specify the zone from which the traffic originates.Add the Destination Zone at which the traffic is terminating.For the Destination Address, select the Dynamic address group you just created.Specify the action— Allow or Deny—for the traffic, and optionally attach the default security profiles to the rule.Repeats Steps 1 through 6 to create another policy rule.Click Commit.This example shows how to create two policies: one for all access to FTP servers and the other for access to web servers.Validate that the members of the dynamic address group are populated on the firewall.
- Select PoliciesSecurity, and select the rule.Select the drop-down arrow next to the address group link, and select Value. You can also verify that the match criteria is accurate.
![]() Click the more link and verify that the list of registered IP addresses is displayed.Policy will be enforced for all IP addresses that belong to this address group, and are displayed here.If you want to delete all registered IP addresses, use the CLI command debug object registered-ip clear all and then reboot the firewall after clearing the tags.
Click the more link and verify that the list of registered IP addresses is displayed.Policy will be enforced for all IP addresses that belong to this address group, and are displayed here.If you want to delete all registered IP addresses, use the CLI command debug object registered-ip clear all and then reboot the firewall after clearing the tags.